5 Key Cybersecurity Threats for 2020

Cybersecurity threats have become remarkably common and they continue to gain traction with the progressions in technology. Cybercriminals are continuously adopting newer technologies, enhancing their coordination and becoming more sophisticated. Through cybercrimes, employees’ and customers’ personally identifiable information (PII) gets compromised and used in illegal schemes somewhere else. Through large-scale data breaches, legitimate data is vulnerable to identity thefts and frauds.
According to a study by Cybersecurity Ventures, cybercrimes will cost the world $6 trillion a year by 2021. In the last few years, cybercrimes have been in the news a lot with tech giants like Google, Facebook, Twitter, and mobile companies becoming a victim of data and security breaches. This is why when it comes to cybercrimes, it’s not a question of ‘if’, it’s a question of ‘when’ it will happen.
Watch Out for These Cyber Security Threats in 2020
This article details five key cyber threats that enterprises need to take seriously and should watch out for in 2020.
Social Engineering Attacks
Social engineering is a method of tricking people so that they give you their information. It is also a way to exploit their weakness, or negligence, to figure out that information. Phishing attacks are a type of social engineering attack. In a phishing attack, the attacker generates a fraudulent email, text or website in order to dupe a victim into giving out sensitive information. Phishing attacks are considered to be the most frequently used approach to get into a corporation’s network these days. Through these attacks, login credentials for work, passwords to online accounts, credit card info, date of birth, etc. are stolen by the attacker.
Only 3 percent of malware tries to exploit an exclusively technical flaw and the other 97 percent target users through social engineering according to KnowBe4. Phishing strategies are now becoming remarkably common as they are cheap, effective and easy to pull off. A report by Small Business Trends reports 1 in every 99 emails is a phishing attack. And this counts for 4.8 emails per employee in a five-day work week. Close to 30% of phishing emails make it past default security.
Social engineering attacks are specifically designed to deceive your employees into granting access to systems or divulging information that helps attackers gain that access through low-, or often no-tech means. Social engineering attacks can come in many forms — by phone, email, snail mail, in person or through social media. So, it’s important that you train your employees to be wary.
IoT-Based Attacks
Almost everything these days is connected with the internet but a lot of these smart devices don’t have strong security installed. This makes it easy for attackers to hijack these devices to infiltrate business networks. An IoT attack is any cyberattack that leverages a victim’s use of internet-connected smart devices like Wi-Fi-connected speakers, appliances, alarm clocks, etc to sneak malware onto a network. In the workplace, everything from smart thermostats and videoconferencing technologies to stock monitors and smart vending machines are all examples of IoT technologies.
IoT is continuously gaining traction and according to Gartner, by 2020 more than 20.4 billion IoT devices will exist. Connected devices are easier for customer use and the majority of businesses use them to save money. More connected devices imply greater risk which subsequently makes IoT networks more vulnerable to cyber invasions. Once controlled by hackers, IoT devices can then used to overload networks, create havoc or close down essential equipment for financial gain. The very things that make IoT so common and easy to use are the same reasons for their vulnerability.
Ransomware Attacks
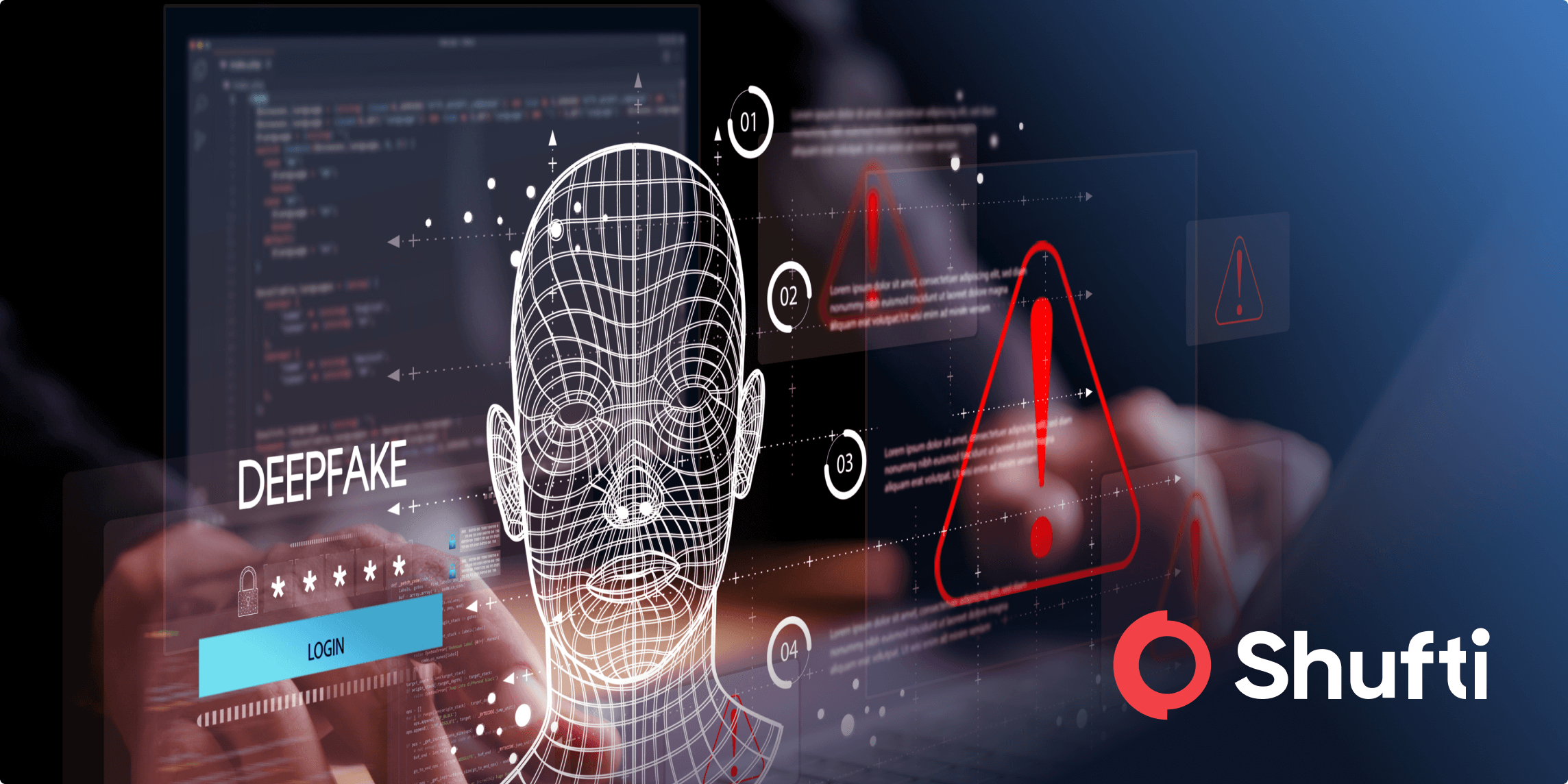
Ransomware attacks are becoming extremely common in the past few years. These are a type of malicious software designed to block access to a computer system until a specific sum of money is paid. This type of attack is triggered by an employee clicking on a link in a phishing email that is harmful and then clicking the link that ignites the malware.
It is highly imperative for enterprises to maintain the privacy of their customers and keep their confidential data secure. In general, ransomware attacks targeting individuals are on the decline over the last year. As reported by ITPro Today, within businesses the rate of ransomware detections rose from 2.8 million in the first quarter of 2018 to 9.5 million in the first quarter of 2019. That’s nearly a 340% increase in detections. It is already on track to hit $11.5 billion in damages for 2019.
A reason why businesses are the victims of ransomware attacks more than private individuals is that they have more motivation to pay for ransoms compared to people. The threat of ransomware is ever increasing and it’s going to be no different in 2020. Businesses are vulnerable to encryption malware making its way into their systems and destroying their data.
Internal Threats
One of the most damaging cybersecurity threats faced by any business is through its own employees. As employees have inside access to the business’s happening, it makes them capable of inflicting great harm if they choose to abuse their access rights for personal gains. Employees may unknowingly allow their user accounts to be jeopardized by attackers or download harmful malware onto their systems.
The reason why internal threats are one of the biggest cybersecurity threats to pay attention to is because of the magnitude of risks they pose. Internal security breaches happen about 2500 times every day in US Business and 19% of employees state that they have been involved in a security breach at work.
How can We Avoid Internal Threats?
- Internal threats can be avoided by including such procedures in your security policy that prevents and detects misuse. The security policy should also have guidelines for conducting insider misuse investigations.
- Background checks are extremely important to avoid internal attacks. They save the company a lot of cost and time and ensures the security of the company.
- Make sure you have access to your employees’ desktops and systems. Through the utilization of a few services, you can remain on top of all the systems of your company which eventually enables you to make your systems secure.
- Another beneficial way is to observe employees directly. This can be done through security cameras or keystroke logging.
State-sponsored Attacks
It isn’t just hackers looking to make a profit through attacks and cyber threats, cyberattacks are becoming common on the government level as well. Entire nations are using their cyber skills to infiltrate other governments in order to perform attacks on critical infrastructure. State-sponsored attacks will continue to expand its scope in the year 2020 with attacks on critical infrastructure as a particular concern.
The majority of these attacks target government-run systems and infrastructure but private sector organizations are also at risk. According to a report from Thomson Reuters Labs, state-sponsored cyberattacks are constantly emerging and pose a significant risk to private enterprises. This will increase the challenges to those sectors of the business world that provide convenient targets for settling geopolitical grievances.