Verify Customers
Build Trust Across the
Shufti creates digital trust at every stage with fast, accurate identity verification and fraud prevention. Built for global scale and strict compliance.
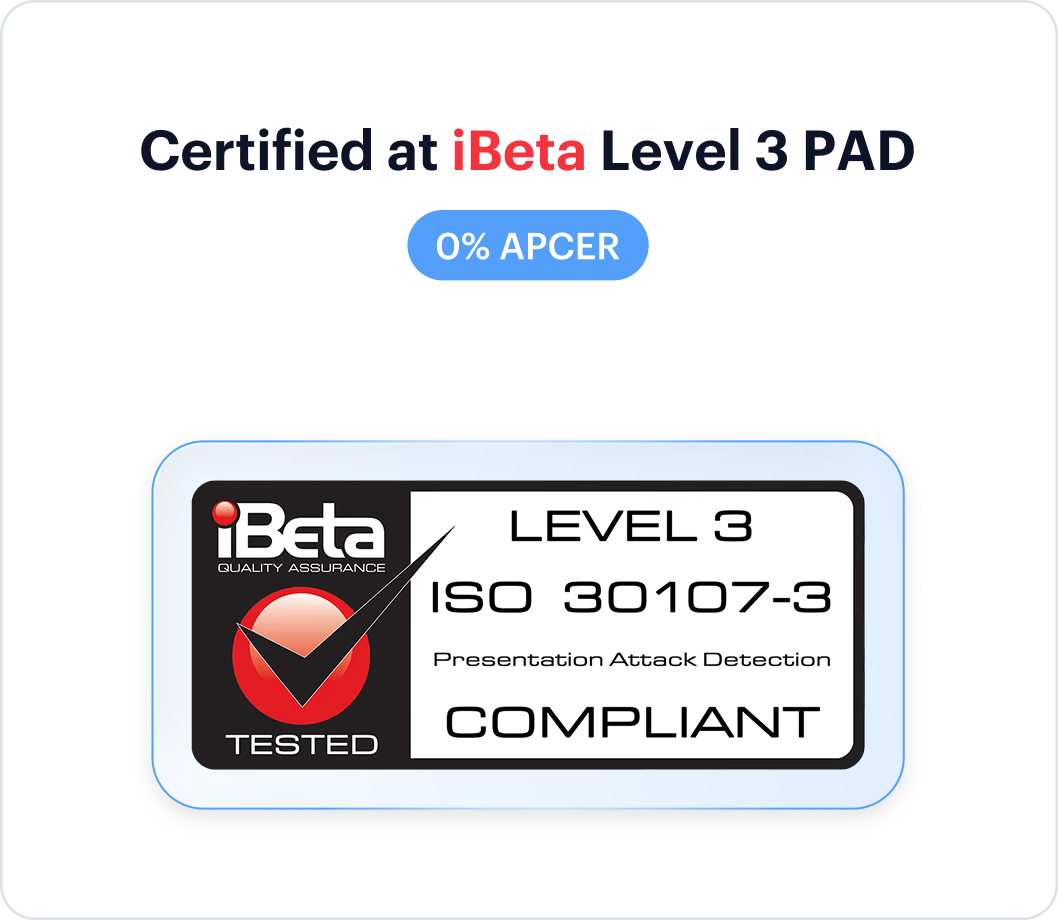
Try NowEurope’s First iBeta Level 3 Certified Liveness Provider
G2
Summer 2026
Independent Validation
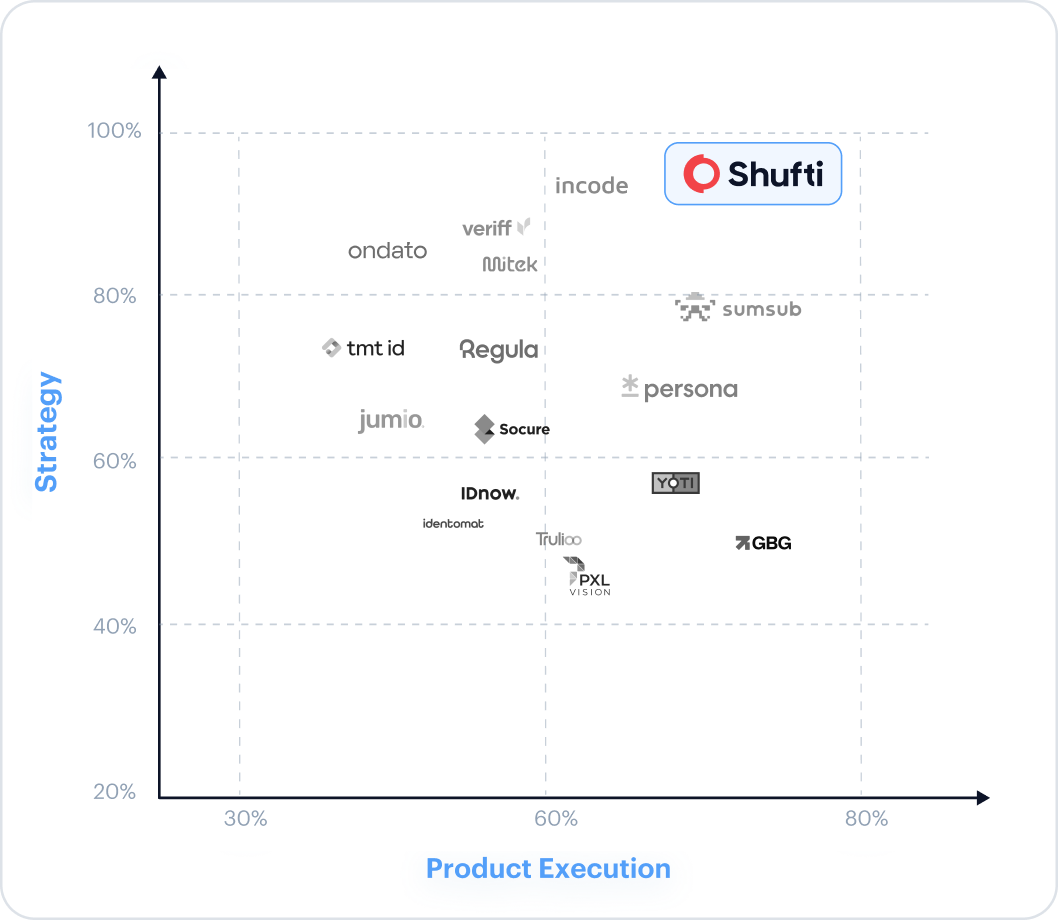
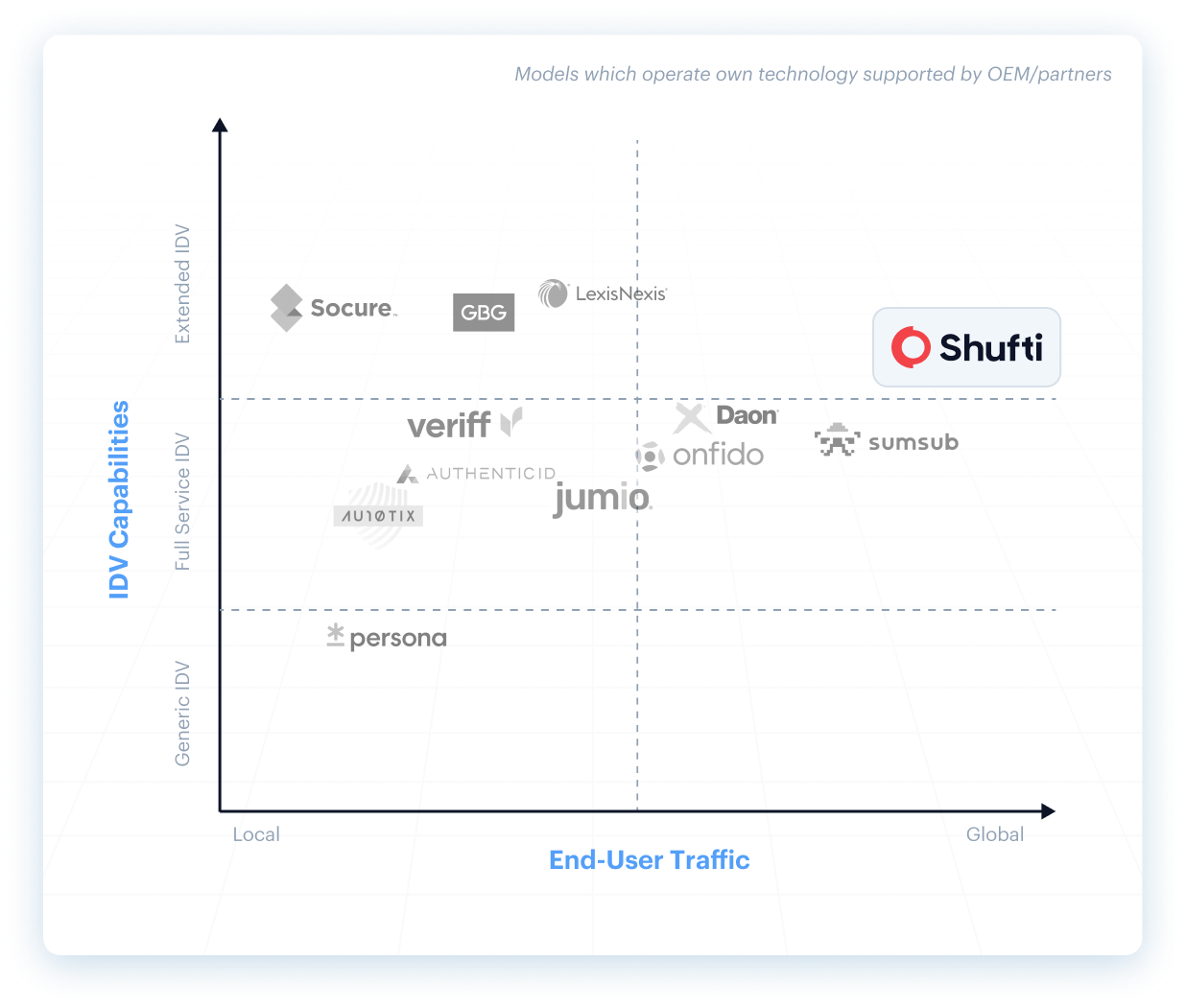
Shufti's Recognition Across Independent Evaluations

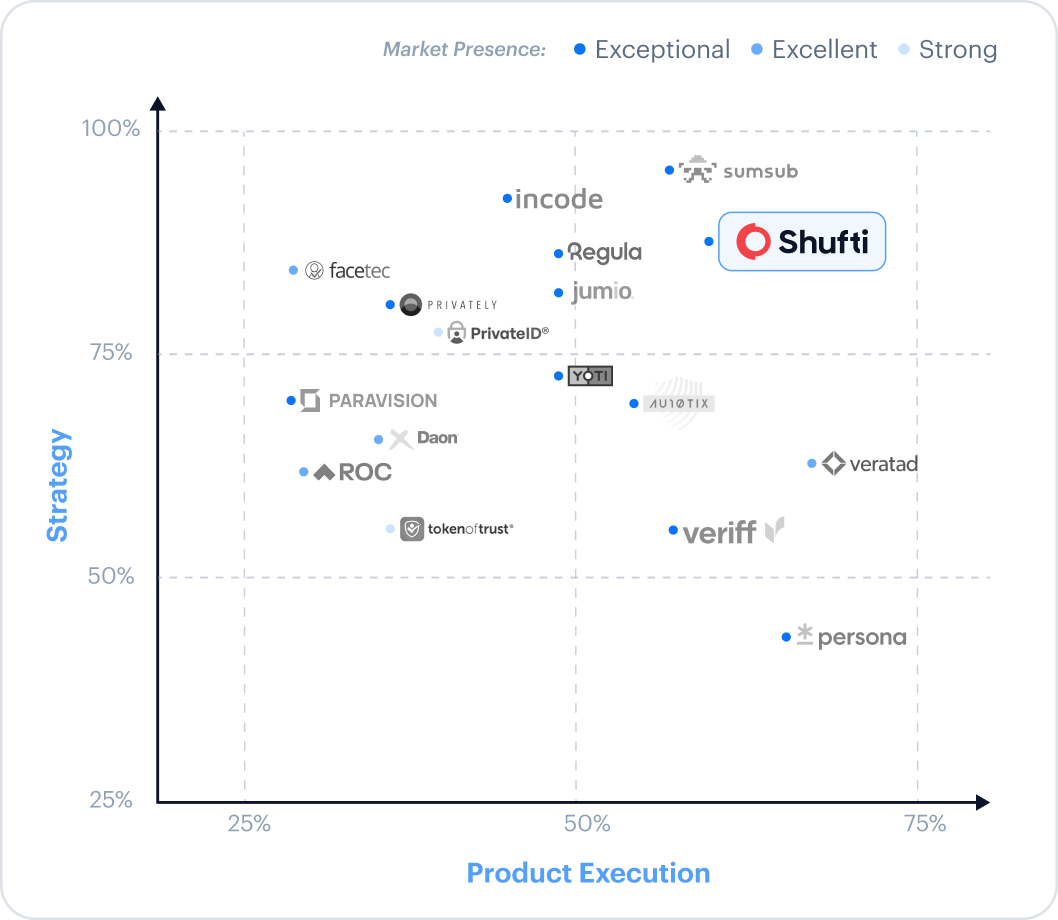
Ranked Exceptional in the Liminal Index 2026 for age estimation
View Report
Differentiated by Gartner on document diversity and country coverage

Certified at iBeta Level 3 PAD with 0% APCER
Read Blog
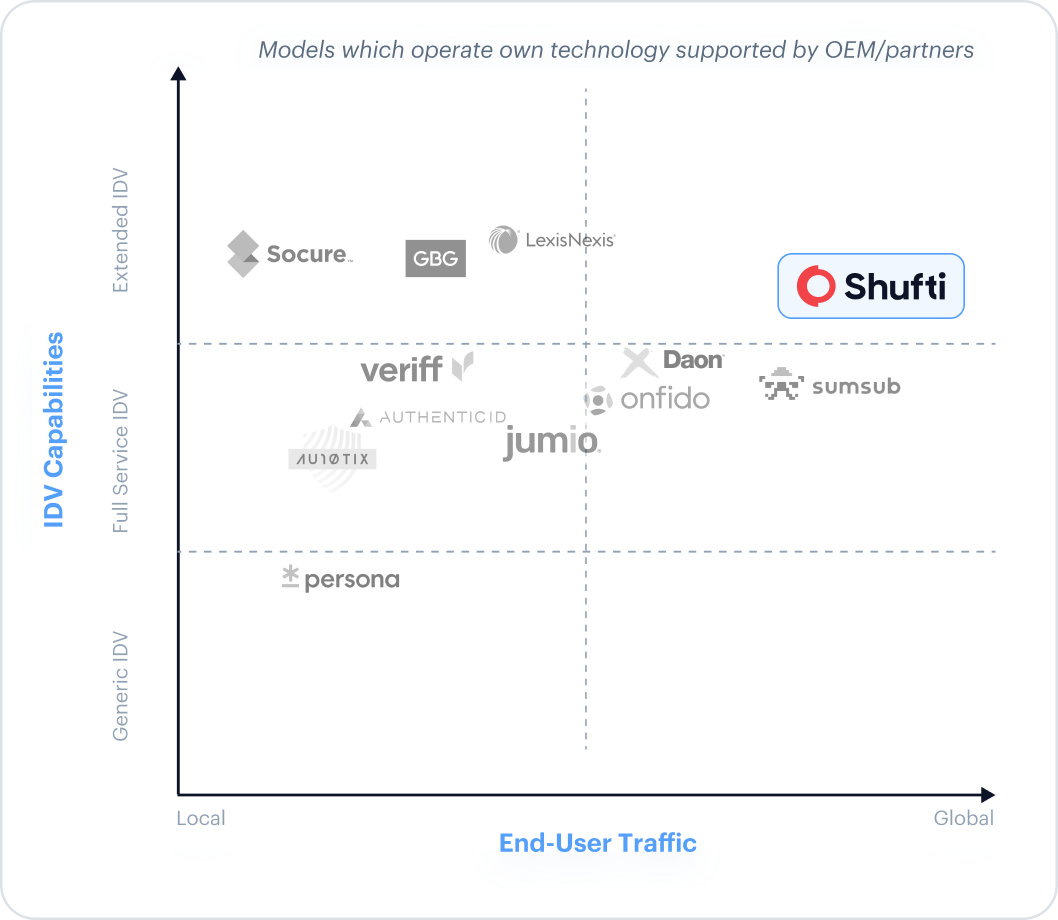
Broadest global reach in the 2025 KuppingerCole Extended IDV report
Download Report
Ranked Top 5 in the DHS RIVR 2025 for identity validation
Read Blog
Ranked Exceptional for age verification by Liminal Index 2026
View Report
Recognised as a Leader across four G2 Summer 2026 reports
View ReportThe Challenges Shufti Solves
Global Identity Verification
Onboard users anywhere, instantly with secure, AI-powered verification flows that keep genuine customers moving with minimal friction.

Identity Lifecycle Management
Secure the full customer journey with continuous identity assurance, re-verify when risk changes and monitor signals without disrupting real users.

Smart Fraud Prevention
Stop fraud before it starts with adaptive AI that detects deepfakes, synthetic IDs, and account takeovers as patterns evolve.

Compliance Assured
Meet global regulations confidently by automating KYC, KYB, KYI, and AML with accurate screening and clear audit trails across markets.
Trust, built-in. From first verification to every future interaction
One Platform. Full Identity Lifecycle
User Verification
Onboard and authenticate legitimate users in seconds
Business Onboarding
Perform global KYB and due diligence with confidence
Authentication
Detect and block fraud at every touchpoint
monitoring & Compliance
Proactively manage risk and maintain regulatory compliance
User Verification
Onboard and authenticate legitimate users in seconds.
Face Verification
Confirm user identity and prevent spoofing with advanced 3D liveness detection and face verification.
Address Verification
Instantly confirm a user's address from utility bills, bank statements, and other documents against global database.
Document Verification
Instantly verify government-issued identity documents from over 230 countries and territories.
Age Verification
Reliably verify user age to meet regulatory requirements and protect your platform.
VideoIdent
Conduct real-time, agent-led identity verification through live video interviews for high-assurance KYC.
eIDV
Confirm user details against trusted government and financial data sources for added confidence.
Business Onboarding
Perform global KYB and due diligence with confidence
Business Verification
Automate the verification of business entities by checking data from global corporate registries.
Due Diligence
Streamline your enhanced due diligence process with customizable risk assessment and data collection.
Authentication
Detect and block fraud at every touchpoint.
monitoring & Compliance
Proactively manage risk and maintain regulatory compliance with continuous user and transaction monitoring.
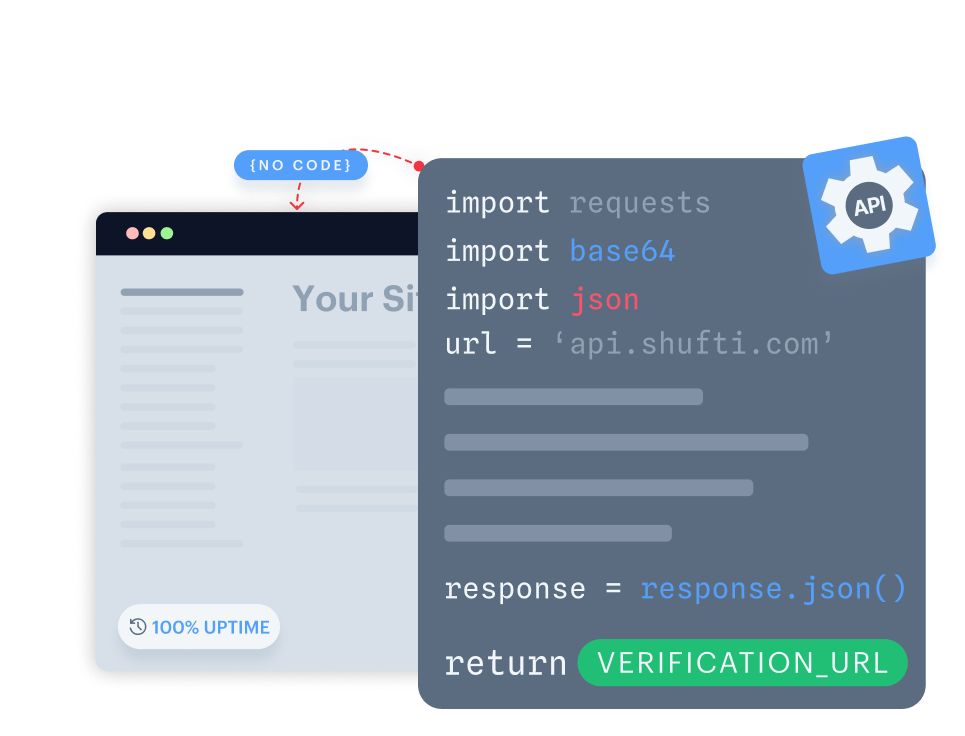
Single platform that adapts automatically & deploys anywhere
Why Leading Enterprises Trust Shufti
Complete, Proprietary
Technology
100% in-house identity stack
KYB
KYC
DOCUMENT
AML
Face Verification
No aggregators. No third-party dependencies. Full control, accuracy, and accountability.
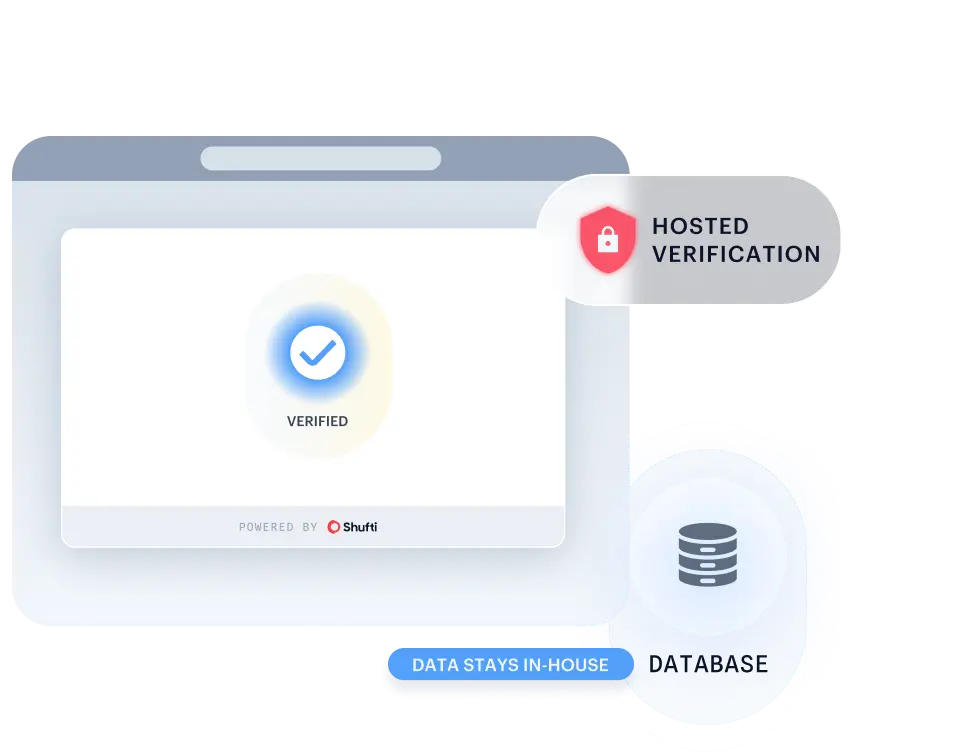
You Control Your Data
Full deployment flexibility on-premise, private cloud, or SaaS. Our full-stack ownership gives you the power to effortlessly comply with any data residency laws.
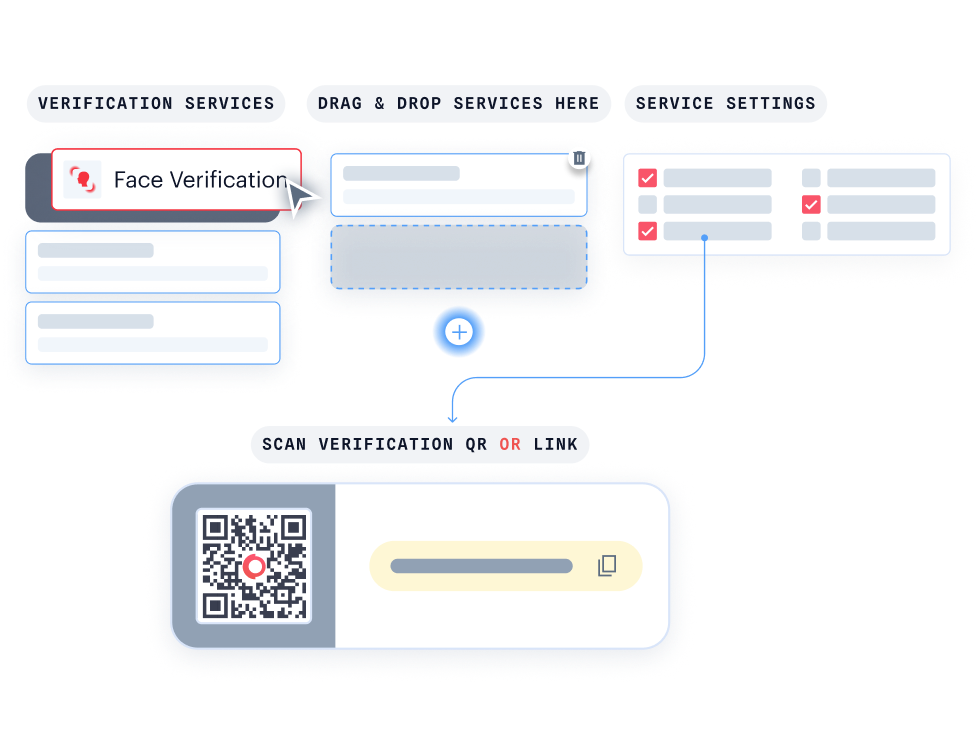
Customised Workflows
Stop forcing your business into a box. We build bespoke verification flows around your specific logic and complex global needs. Consider it done, with 24/7/365 enterprise support.
Scale Globally via Shufti AI
Don't just verify, scale! Shufti AI, trained on 10,000+ global documents, uses zero-shot learning to master new formats in minutes. Your global onboarding never stops.