ID Verification Trends to Curb Online Frauds

Automated Identity Verification Can Play a Significant Role in Fraud Management
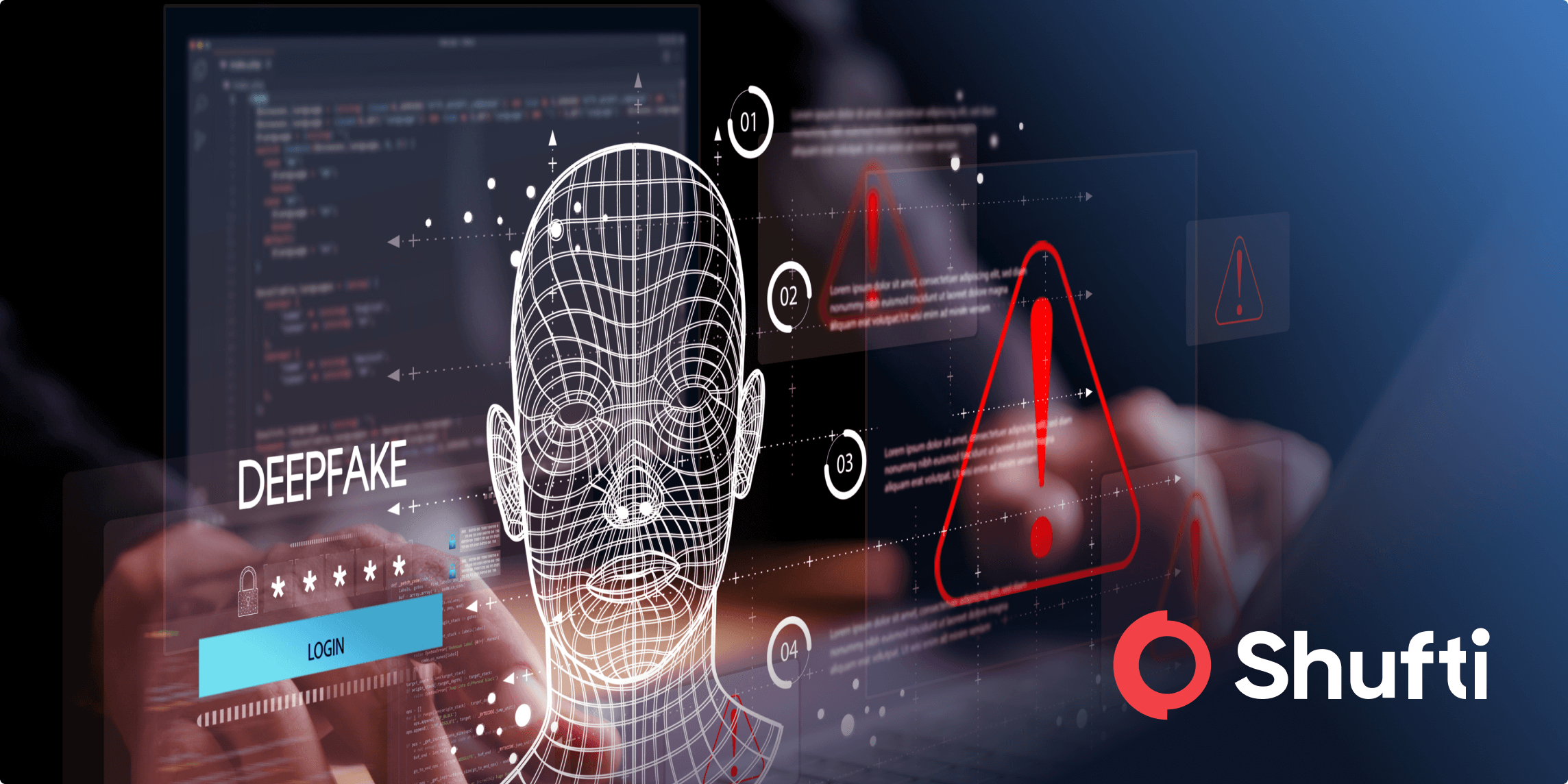
Fraud management plays an important role in preventing internet frauds and scams. Systems for online ID verification are contributing significantly towards fraud prevention. The previous year was an uphill battle against online frauds with nearly 1 billion personal identity records stolen during the year. With significant incidents of data breaches including the Marriott data breach, Amazon’s merchant fraud and Atlanta’s SamSam Ransomware infection. The landscape for cybersecurity and fraud protection, therefore, has to keep on evolving with time.
As cybersecurity threats continue to become more sophisticated in nature, both customers and employees expect the technological landscape to develop solutions that can tackle them effectively. Identity and Access Management (IAM) systems have to improve continually to keep fraudulent activities at bay. Effective IAM is being used by businesses to achieve a number of outcomes including the management of identities, verification of users, and the management of access to applications and APIs (Application Programming Interface).
The future of identity verification systems depends on the amount and types of online frauds that take place. To date, cybercrimes and frauds show no signs of slowing down. Which is why the future of online ID verification continues to evolve and advance. The trends that the identity verification landscape that can be expected over time include;
Evolving Methods for Identity Authentication
Identity proofing or authentication has been a requirement where people have to be physically present to verify themselves and their identities. Financial institutions, banks, government agencies and retail merchants have always required physical proof of identity from a customer or user. But ever since the e-commerce market has gained its place in the industry, it is becoming harder for businesses to identify fraud. The age of the internet has made products and services more accessible than ever before. So why should the methods for identity authentication remain far behind?
As advanced technological solutions powered by artificial intelligence (AI) and machine learning, gain their place in the market, new methods for identity proofing have also emerged in the market. These solutions and systems are only expected to grow over the next few years. They are also expected to change the way people share their identities online or otherwise.
As the need for physical interactions, while conducting transactions decreases, alternatives are being developed for ID verification. The need for verification systems like knowledge-based authentication (KBA) is diminishing as they have proved to be vulnerable. Thus verification measures need to be developed that establish a better connection between authorities and the private sector businesses.

Passwordless Authentication Methods
Creating and remembering unique passwords has always been difficult for online users. Over a decade ago, Bill Gates analysed that password-based authentications will, over time, become obsolete. Sure enough, it seems that passwords alone are not enough to thwart cybercriminals. Moreover, the types of online activity also determine the kind of security a particular action requires. Fraudsters do not pay bills or order small, insignificant things online. Identity authentication measures are expected to evolve in as much that passwordless authentication will be used for trivial and low-risk activities.
Companies like VEON, Microsoft, Accenture and Capgemini have managed t develop advanced systems for identity and access management that use cloud automation and passwordless mobile sign-on that can cope with the challenges of identity theft and cybersecurity.
Behavioural Analytics and Machine Learning
As the applications of AI and machine learning technology become vast and widespread, systems for identity verification have also transformed to provide better and more information to businesses about their customers. Companies are increasingly collecting and using customer data to draw insights for marketing campaigns, improve customer services and fight fraud. Behavioural analytics use complex machine learning algorithms to analyse a customer’s purchase behaviour. Such systems rely on vast quantities of data. They use transactional data to detect suspicious activities. Drawing on a users’ past behaviour, the system is able to determine if a transaction is fraudulent. If suspicious activity is detected on a customer’s account, it reported to the company, who then takes the appropriate action against it.
Biometric Verifications Become More Common
Online businesses and financial institutions are increasingly making use of multi-factor or multi-layered authentication systems. As smartphones, these days have made online facial recognition a mainstream technology, facial biometrics are becoming the standard of online ID verification for companies. Just as the fingerprint authentication method took off, the face recognition ID verification method will be adopted by many businesses over the next few years.
Every company does not have the resources and technology to implement automated ID verification systems. Shufti is an ID verification service that provides real-time verification results for document verifications, facial recognition as well as AML screening checks. It offers comprehensive fraud protection services through a complete KYC package.