Account Takeover Frauds – Impact, Causes, and Prevention

Living in the era of technology, the world is rapidly moving towards digitization. From banking institutions to shopping stores, every organization is shifting its operations online. Going digital is no doubt providing a competitive edge to organizations to meet customer demands. On the other hand, the online presence has raised serious concerns for both individuals and businesses by exposing digital information to cybercriminals. As a result, there has been a significant increase in digital fraud, specifically account takeover (ATO) fraud.
What is account takeover fraud?
Account takeover (ATO) fraud is the type of identity fraud that involves unauthorized criminal access to a user’s account to use it for some type of personal and financial gain. The increased presence of people on the internet and involvement in activities like online shopping and banking and convenient funds transfer has opened new opportunities for criminals looking to make extra cash.
ATO fraud can involve the exploitation of multiple types of online accounts, including online banking, eCommerce, mobile, and social media accounts. Generally, cybercriminals and fraudsters lookout for the accounts from which they can steal money and gain monetary advantages. For instance, targeting bank accounts for fund transfer to own account or eCommerce accounts to make fraudulent purchases. Also, the imposters can take over social media accounts and request money from the family and friends of the victims.
Ecommerce platforms are the most profitable for criminals due to frictionless payment systems. In e-commerce sites, due to instant purchase functionality, all the billing information is stored in the user account that makes it convenient for the customers to make purchases. But it also makes it handy for criminals to simply change the shipping address and start making a purchase, once they discover the login credentials.
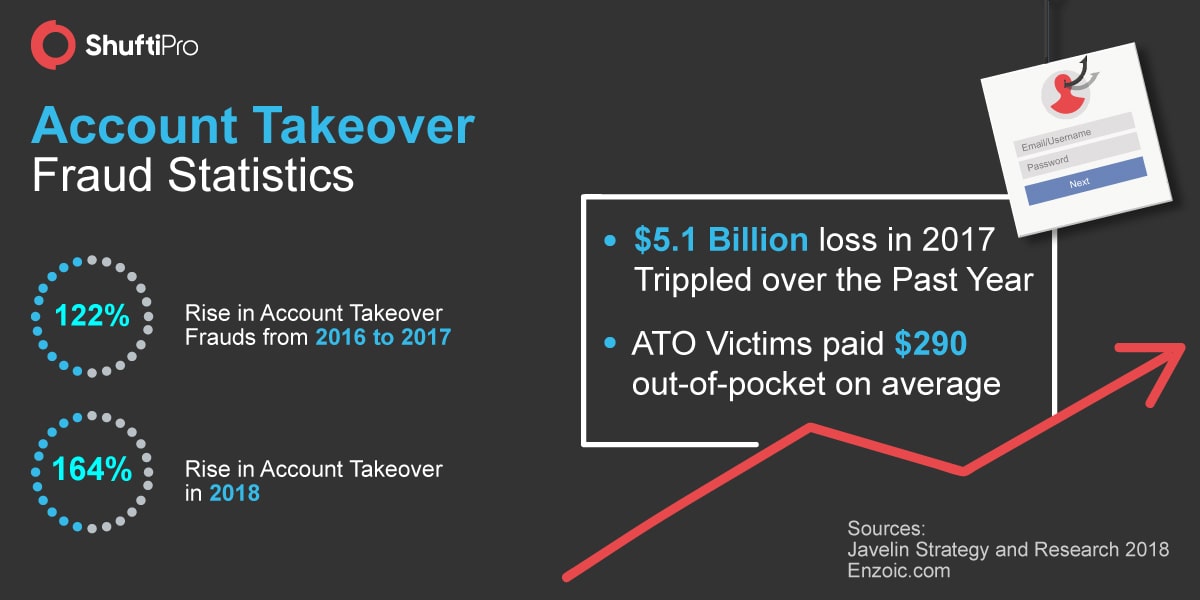
Impact of ATO Frauds
Account takeover fraud rates have been on the rise for the last few years. Every year the individuals and businesses incur huge losses due to ATO frauds. Mostly customers are the ones who endure monetary losses. In addition, in most cases, they not only lose time in resolving fraud but also suffer a damaged reputation and relationships, for example, in the case of social media account take over. Businesses, however, suffer losses in the form of chargebacks and bruised reputation.
Last year in May, KREM2 reported a case ATO fraud in which the victim, “Allie Raye” wasn’t aware of the fraud until she started receiving shipping notices and orders from Amazon. Even after discovering it, it was very difficult for her to stop the fraudulent orders – that included several gift cards. It took her around three weeks to regain hold of her account and all this while she lost $1,640 in fraudulent purchases. In that case, the Amazon had to suffer the actual loss by ultimately refunding Raye the whole amount.
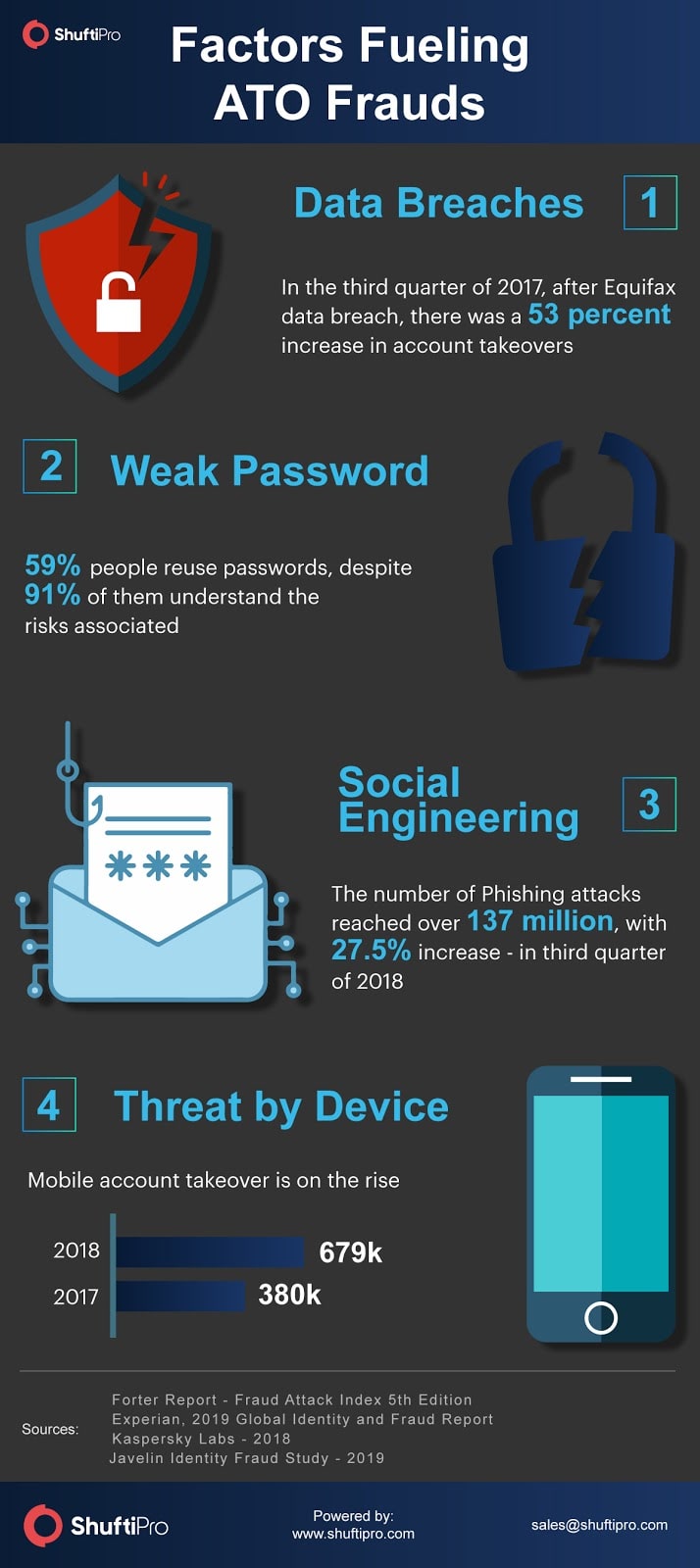
Factors fueling ATO frauds
Account takeover fraud is a serious concern not only for the individuals but businesses as well. The technological innovations have made the fraudsters more sophisticated in accessing users’ information. There are multiple factors that are fueling ATO frauds, some of them are:
-
Data Breaches
One of the main driving factors behind account takeover frauds is the increasing trend of data breaches. The purpose of a data breach is to access the records of the customers containing their information – for example, usernames, passwords, account numbers, and card numbers, etc. The list obtained from the breach is sold in the black market where the numbers of cybercriminals are readily looking for users’ data.
When the username and password of an account are known, hackers try the same combination on multiple online platforms through various automated tools – known as credential stuffing. According to Perimeterx Research, there is an 8% success chance of these attacks. Moreover, if criminals have access to the username and email address they can use multiple attacks, for instance, brute force, to guess the passwords.
-
Weak Password Practice and Inefficient Authentication
More online presence of individuals means more accounts. It means users have to remember all the usernames and passwords for different accounts. The difficulty memorizing them encourages the users to set the same passwords for multiple accounts. This is a very common yet highly risky practice. It is found that 21% of people use passwords that are 10 years old and at least 71% reuse their passwords. This weak password practice exposes users to cybercriminals. Through brute force attacks and credential stuffing, they can easily take hold of users’ credentials and accounts.
Most of the organizations still rely on the binary authentication method i.e. using username and password. Anyone having access to those credentials can easily log in to the account and do whatever they want. This is one of the main reasons for account takeover.
-
Social Engineering Tactics
The advent of technology has significantly provided fraudsters and imposters with advanced social engineering tactics; phishing is one of them. Through phishing attacks, cybercriminals are accessing user credentials by tricking the users. There are multiple ways through which these attacks can occur – including through email, text message or even over the phone. However, the purpose is the same, i.e, trying to get the users to hand over their information.
An example of such an attack is receiving an email that persuades you to click the link and prompt the login page to enter your credentials which are stolen by criminals.
-
Threat by Device
Another factor that is driving the ATO fraud threat is through smart devices – mobiles and mobile applications are prime targets of cybercriminals for ATO fraud. One of the major reasons for this is the technology lag. Regardless of advanced tools designed to protect users on web browsers, those tools don’t work for mobile apps at the same time. According to Rippleshot’s State of Card Fraud 2018 report, mobile phones are becoming increasingly vulnerable targets of ATO frauds and would rise in the future as well.
How to prevent ATO frauds?
-
Identity verification at the time of onboarding
No doubt ATO fraud is the major concern for the businesses especially for e-commerce, however, they can be prevented using proper user verification at the time of onboarding. Sometimes after committing the ATO fraud, the fraudsters use that information of the user to create another account. Through digital identity verification services, businesses can ensure the identity of real users and hinder the fraudster from creating fake accounts – i.e. committing identity theft.
-
Identity Authentication
The main factor that fuels ATO frauds, is the lack of proper authentication checks. In this world of no trust, stealing someone’s credentials is no more a difficult task. By applying the social engineering phenomenon, the fraudsters can trick users to provide their information. If online businesses follow proper and advanced authentication services like 2-Factor Authentication and Biometric verification through Face verification, then the account takeover frauds can be prevented.
The users who fail to verify and authenticate their identity can be hindered from accessing the account in real-time.
-
Monitoring Payments
ATO frauds are done to gain monetary benefits mostly. The frictionless mobile and online payments are no doubt enhancing the user experience, but at the same time, it is grabbing the attention of cybercriminals. Whenever the imposters take over the account, let’s say bank account, the first thing they do is transfer money to their account.
Due to a lack of payment monitoring or authentication before processing transactions, the cybercriminals are successful in making fraudulent payments. Monitoring the payment every single time when a user request a transaction can combat fraudsters in real-time.
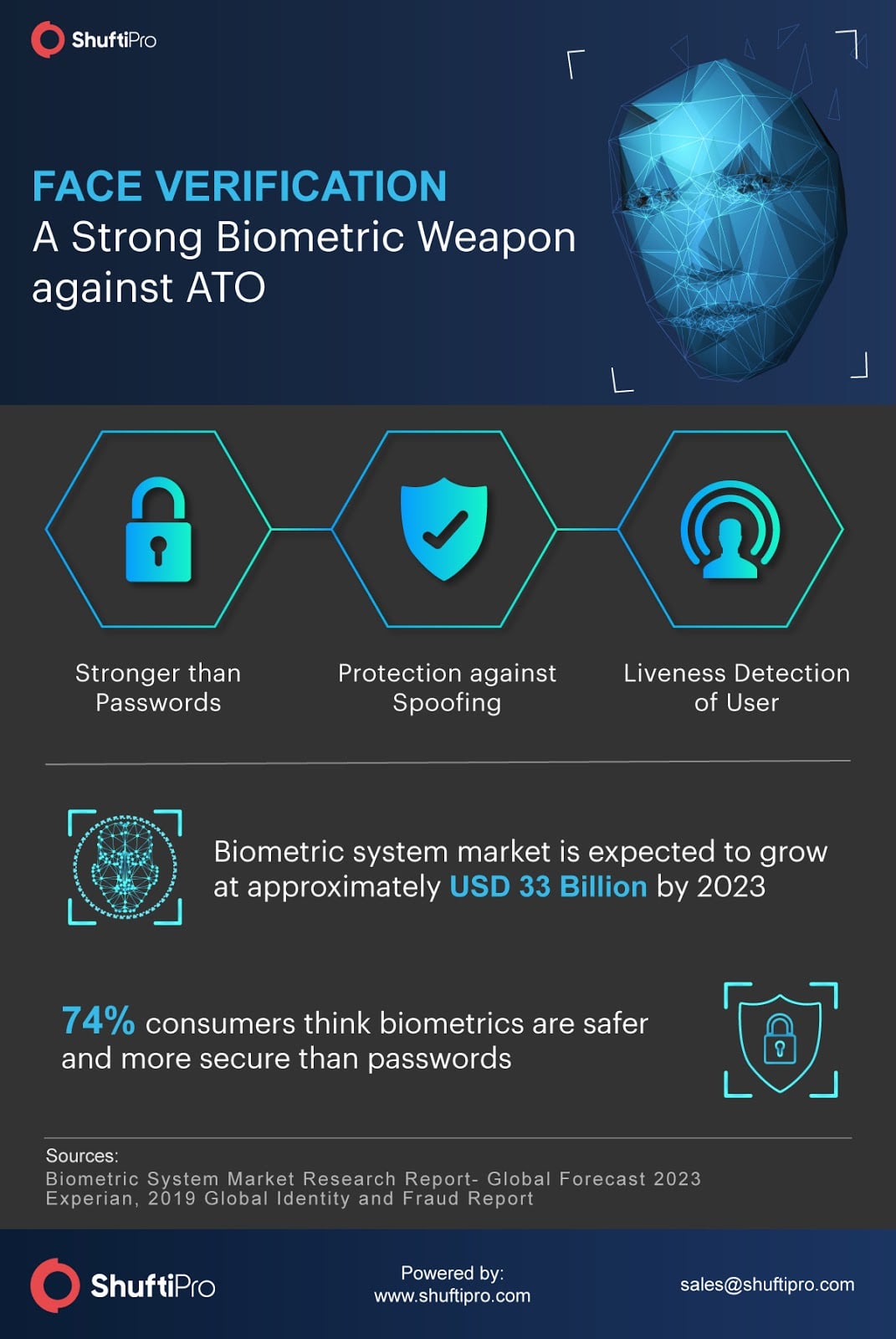
Face Verification – A Strong Weapon against ATO frauds
Face verification is the advanced form of biometric verification powered by artificial intelligence and machine learning algorithms. The traditional verification and authentication check have failed to prevent the fraudsters from accessing the users’ data and personally identifiable information (PII). Integrating face verification API with the existing platforms can identify the fraudsters beforehand who may try to enter the system through spoofing measures.