Transaction Screening vs. Transaction Monitoring in 2025: Key Differences, New Regulations & Shufti Insights
In 2025 the stakes for anti‑money laundering (AML) compliance have never been higher. Financial institutions face an evolving threat landscape—AI‑driven fraud rings, instant‑payment rails, and record AML fines expected to exceed US $6 billion this year. Meanwhile, regulators on both sides of the Atlantic have tightened the rules: the EU Anti‑Money Laundering Authority (AMLA) starts direct supervision, FinCEN has overhauled beneficial‑ownership reporting, and the UK’s Economic Crime and Corporate Transparency Act (ECCTA) introduces a new corporate offence of failure to prevent fraud from 1 September 2025.
Against this backdrop, understanding the distinction between transaction screening and transaction monitoring is critical. While both aim to detect illicit activity, the when, how and why differ—affecting everything from onboarding risk assessment to Suspicious Activity Report (SAR) volumes.
Quick Definitions
| Term | Purpose | Timing | Typical Data Points |
| Transaction Screening | Identify prohibited or high‑risk counterparties by checking names, wallet addresses and payment fields against sanctions, PEP and adverse‑media lists. | Pre‑ or real‑time (before settlement). | Beneficiary/payor name, IBAN, BIC, crypto wallet, jurisdiction codes. |
| Transaction Monitoring | Detect unusual behaviour across a customer’s transaction history to flag potential money laundering, fraud or terrorist financing. | Post‑event or near real‑time (continuous). | Amount, frequency, geolocation, velocity, device fingerprints, behavioural biometrics. |
2025 trend: Instant‑payment rails (e.g., SEPA Instant, FedNow) compress settlement windows from hours to seconds. Screening and monitoring engines must now deliver risk decisions in < 300 ms to avoid false declines that frustrate customers.
Why Both Matter More in 2025
The 2025 compliance environment is defined by speed, transparency and accountability. Payments settle in seconds, regulators expect near‑real‑time oversight, and consumers demand friction‑free experiences. Transaction screening and monitoring therefore serve as twin safety nets—screening blocks known bad actors at the point of entry, while monitoring uncovers hidden patterns that evolve over time.
1. Regulatory Upheaval
Increasingly, supervisors are converging on a data‑first, proactive posture.
- AMLA launches (EU) – From January 2025, AMLA co‑ordinates and directly supervises high‑risk cross‑border institutions. Firms must submit granular transaction data through new EUCLID‑2 APIs and be prepared for joint examinations alongside national competent authorities.
- FinCEN interim rule (US) – March 2025 guidance removes domestic beneficial‑ownership filings but tightens thresholds for foreign entities. Financial institutions handling cross‑border payments must now monitor for indirect ownership chains that fall below 25 % but exceed US $10 million annual throughput.
- ECCTA (UK) – The corporate offence of failure to prevent fraud (effective 1 September 2025) extends liability to senior managers if transaction‑monitoring controls are weak. Prosecutors will look for evidence of risk assessments, scenario testing and model validation.
2. Enforcement & Fines
With global AML penalties projected at US $6 billion in 2025 (up 20 % YoY), fines are increasingly tied to inadequate data‑governance frameworks. The EU issued €1.4 billion in penalties in H1 2025 alone—42 % linked to sanction‑screening failures. Repeat offenders face licence restrictions and personal accountability for directors.
3. Emerging Threat Vectors
Criminals exploit technology at pace:
- Crypto mixing services account for an estimated 12 % of illicit flows (vs 8 % in 2023). Sophisticated mixers now chain‑hop across blockchains within milliseconds, demanding deeper analytics.
- Instant‑credit push‑payment fraud has surged 67 % YoY as faster‑payments schemes expand. Fraudsters leverage social‑engineering scripts and synthetic IDs, necessitating behavioural monitoring that looks beyond static KYC data.
Shufti Analytics Spotlight
Shufti continuously analyses billions of datapoints to surface actionable intelligence. Below is a snapshot of key findings from 110 million transactions processed between July 2024 and June 2025.
Before diving into the numbers, remember that analytics are only as powerful as the feedback loops that refine them. Each alert fed back into Shufti’s Dynamic Risk Engine 2.0 helps sharpen thresholds and minimise customer friction.
- False‑positive reduction: AI‑assisted screening cut false positives by 52 %, saving compliance teams ~2,400 analyst hours per bank, per year. The model combines fuzzy‑logic name matching with contextual indicators such as device reputation and transaction velocity.
- SAR uplift: Intelligent monitoring surfaced 29 % more genuinely suspicious cases versus legacy, rule‑only systems. Crucially, overall SAR filings remained flat—indicating higher‑quality alerts, not increased noise.
- Real‑time crypto risk scoring: Blockchain analytics flagged 1.3 million risky wallet interactions, preventing over US $920 million in potential illicit flows. The engine scores wallets on chain‑behaviour, mixer proximity and darknet‑market exposure in < 200 ms.
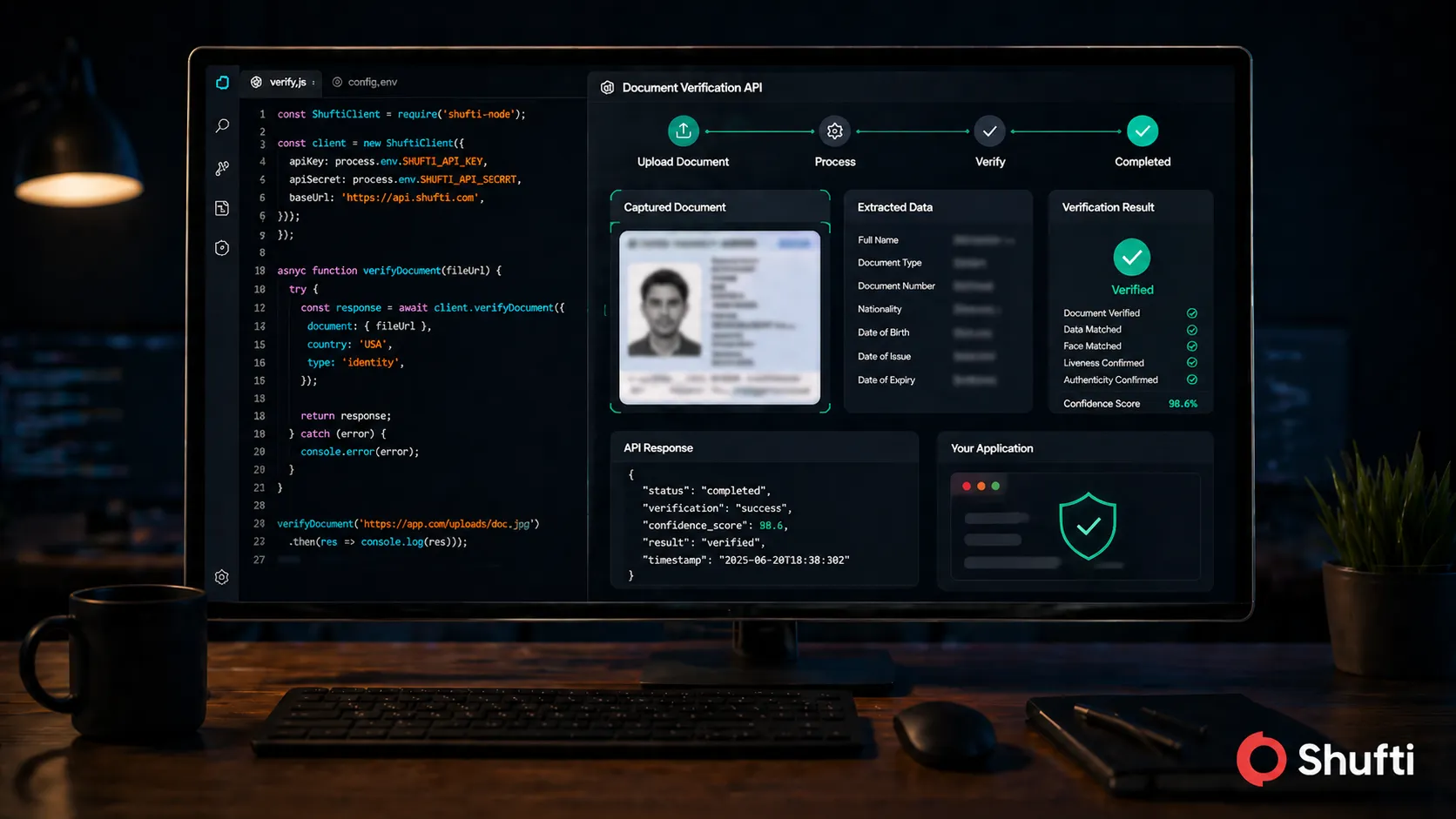
Product note: Shufti’s Dynamic Risk Engine 2.0 (released May 2025) fuses behaviour analytics, device intelligence and sanctions ontology mapping to score each transaction in milliseconds—even during peak traffic.
Compliance Checklist for 2025
A robust AML framework requires more than ticking boxes; each control must work in concert. Use the checklist below as a roadmap for 2025 readiness.
Centralise Sanctions Data – Aggregate over 1,700 watchlists (OFAC, UN, EU, UK, AMLA) into a single, deduplicated feed refreshed hourly. Centralisation ensures consistent decisions across business units and reduces maintenance overhead.
Integrate Real‑Time Monitoring – Synchronise screening engines with transaction‑monitoring triggers so that an alert generated at screening (e.g., sanctioned beneficiary) cascades into downstream monitoring scenarios (e.g., velocity checks). This eliminates duplicate alerts and provides holistic risk scoring.
Update Policies – Align internal AML manuals with AMLA supervisory guidelines and FinCEN/ECCTA amendments. Document how regulatory changes impact thresholds, escalation paths and reporting timelines. Regulators increasingly request policy‑to‑process traceability.
Test & Tune Models – Conduct quarterly model‑risk assessments. Stress‑test AI thresholds against synthetic fraud scenarios and document explainability in line with the EU AI Act. Maintain version control so you can roll back if drift degrades performance.
Train Staff – Deliver scenario‑based simulations focusing on instant‑payments fraud and crypto‑mixer typologies. Reinforce red‑flag indicators, SAR drafting best practices and escalation protocols. Well‑trained analysts are your last line of defence.
FAQ (2025 Edition)
Q1. Do I need separate systems for screening and monitoring?
A: Not necessarily. Integrated platforms can provide both capabilities, but you must still configure distinct rule sets because screening (static data) and monitoring (behavioural data) serve different regulatory obligations.
Q2. How will AMLA supervision change my day‑to‑day compliance?
A: Expect stricter reporting timelines (10 days for material breaches), direct data calls and potential joint examinations with your national competent authority.
Q3. Does the FinCEN interim rule mean fewer BOI obligations?
A: Only for U.S.‑incorporated entities. Foreign companies with a U.S. nexus now face more granular reporting and enhanced monitoring of cross‑border payments.
Q4. What’s the impact of the UK’s ECCTA fraud offence?
A: Firms must demonstrate ‘reasonable procedures’—including robust transaction monitoring—to prevent fraud or risk unlimited fines and director disqualification.
Q5. How can I reduce false positives without missing real threats?
A: Combine fuzzy‑logic matching with contextual data (e.g., geolocation, device ID) and machine‑learning feedback loops—an approach proven to cut false alerts by over 50 % in controlled deployments.
Conclusion
The convergence of tighter regulations, instant‑payment ecosystems and sophisticated criminal techniques means that both transaction screening and transaction monitoring are indispensable pillars of AML compliance in 2025. Screening keeps bad actors out at the gateway; monitoring detects evolving risks over the customer lifecycle.
By harnessing Shufti’s real‑time analytics, AI‑driven risk scoring and global watchlist coverage, compliance teams can meet regulatory expectations while enhancing operational efficiency.
Ultimately, a proactive, data‑led approach anchored in accurate screening and intelligent monitoring remains the most effective defence against financial crime in an increasingly complex world.
Sources:
1- EU Regulation 2023/1113 establishing the Anti‑Money Laundering Authority (AMLA). Official Journal of the European Union, 15 January 2025.
2- Financial Crimes Enforcement Network (FinCEN). “Beneficial Ownership Reporting Requirements for Foreign Entities.” Interim Final Rule, 18 March 2025.
3- UK Government. Economic Crime and Corporate Transparency Act 2023 (Commencement No. 2) Regulations 2025.
4- FATF. “Detecting and Preventing Money Laundering in Instant Payment Systems.” April 2025.
5- Shufti. “Global Transaction Risk Report 2024‑2025”, internal analytics dataset, July 2025.

 Explore Now
Explore Now