Face Verification
Face Verification Software for Secure Identity Verification
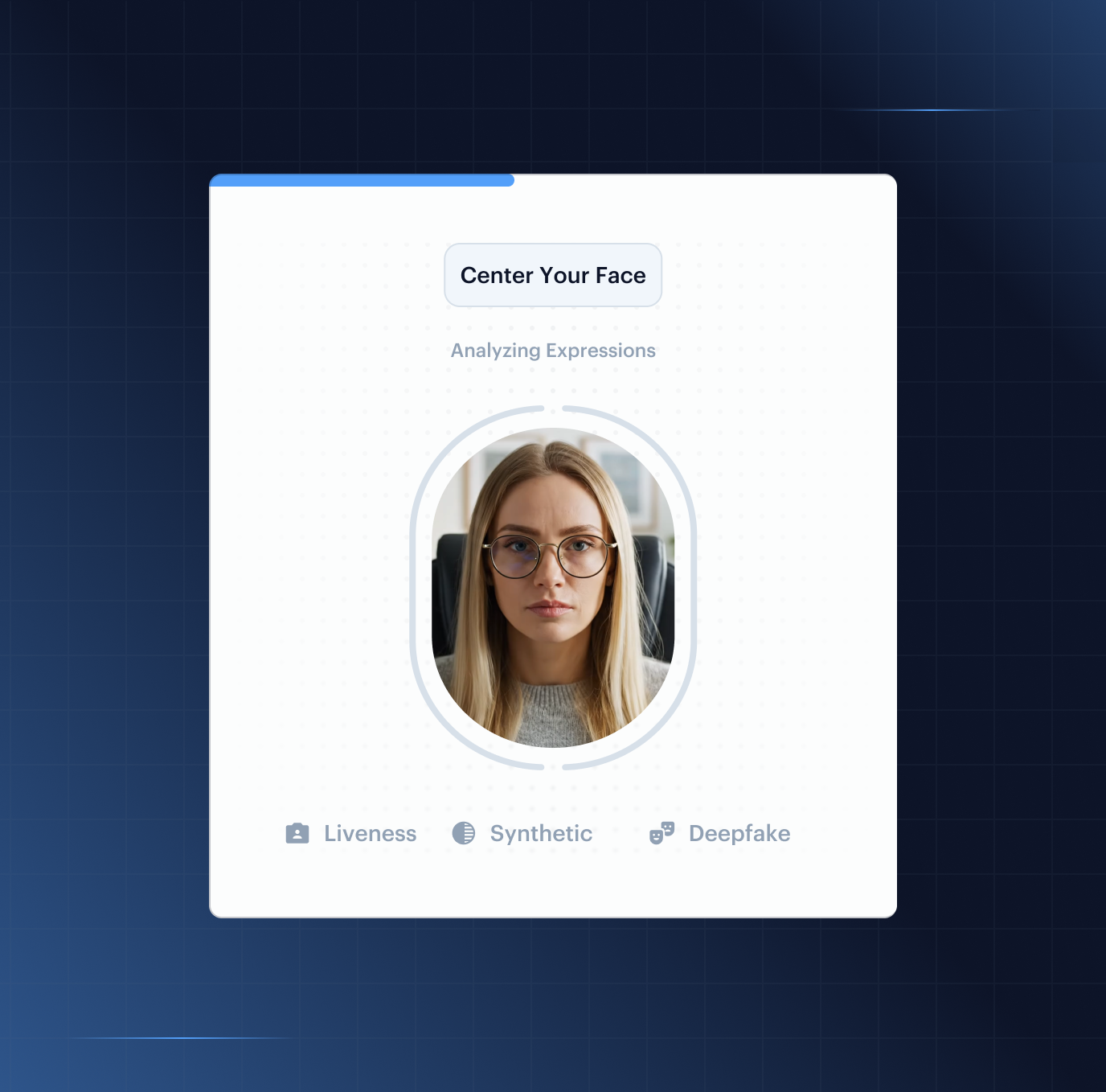
Stop sophisticated spoofing before it compromises your platform. By applying layered liveness and advanced frequency-domain forensics, Shufti face verification proves you are dealing with a live human instead of a deepfake, printed mask, or injected video stream.
Independently Validated Results
Face Verification System for Advance Fraud Prevention
Detection That Keeps Pace With New Fraud
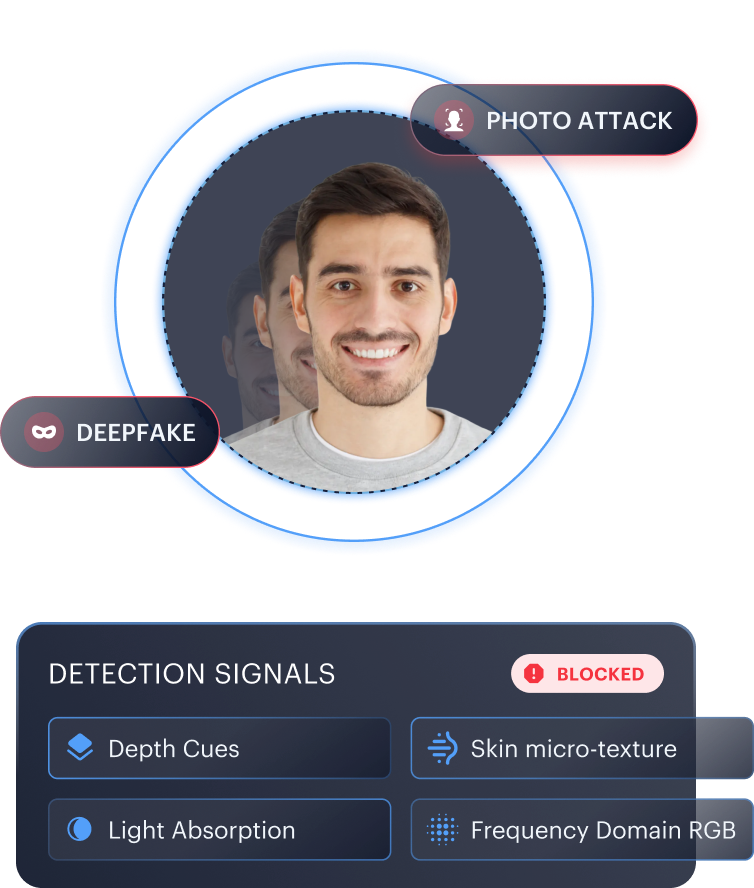
High-resolution photos remain the most common attack at scale. Shufti analyses via Face Verification Technology depth cues and skin-reflection patterns to rule them out at first capture.
Silicone masks, 4K replays, and injection attacks remain a persistent threat. Texture and light-absorption analysis of real human skin catches them.
Synthetic and AI-generated faces are an evolving attack vector. Dual-domain analysis combines RGB with frequency-domain signals to surface them.
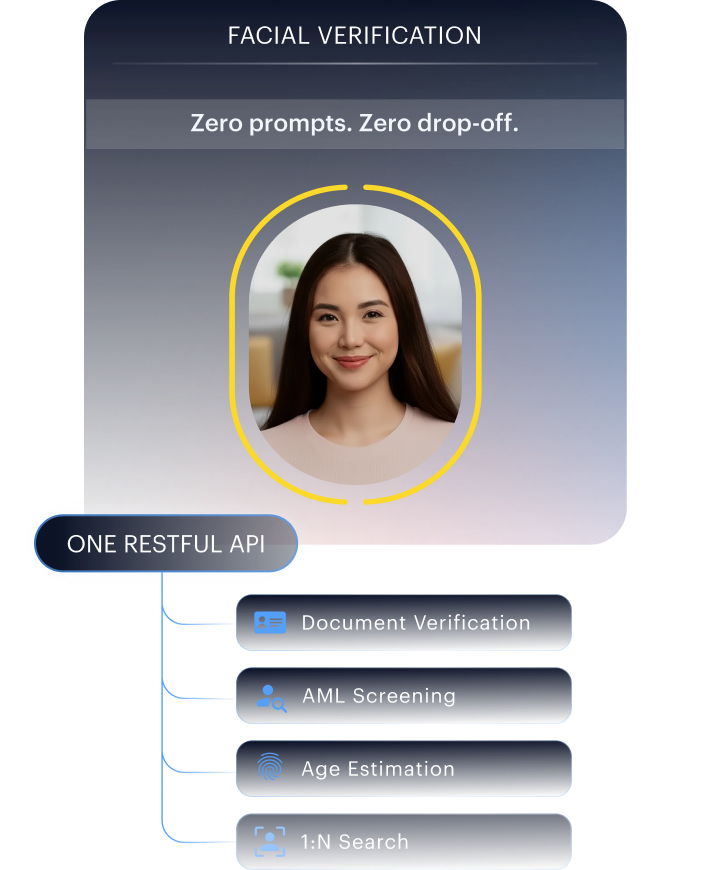
Verification Without the Conversion Tax
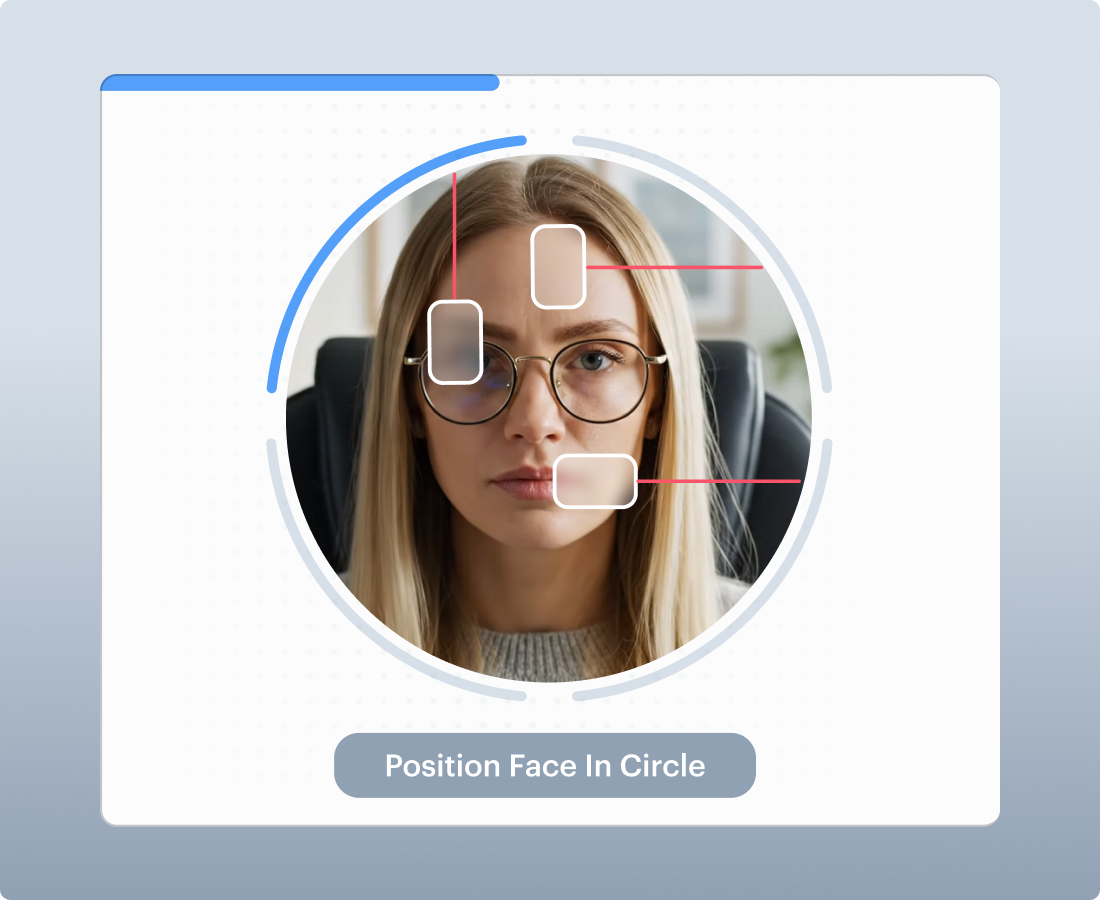
No head movement, no flashing lights, no prompts. Skin micro-textures, eye reflections, and replay signals are analysed in the background.
Document, AML, address, 1:N search, and age estimation route through the same RESTful API. No third-party document scanner, no separate AML provider.
Active liveness is configurable for clients who require challenge-response flows. Same SDK, same accuracy, same audit trail.
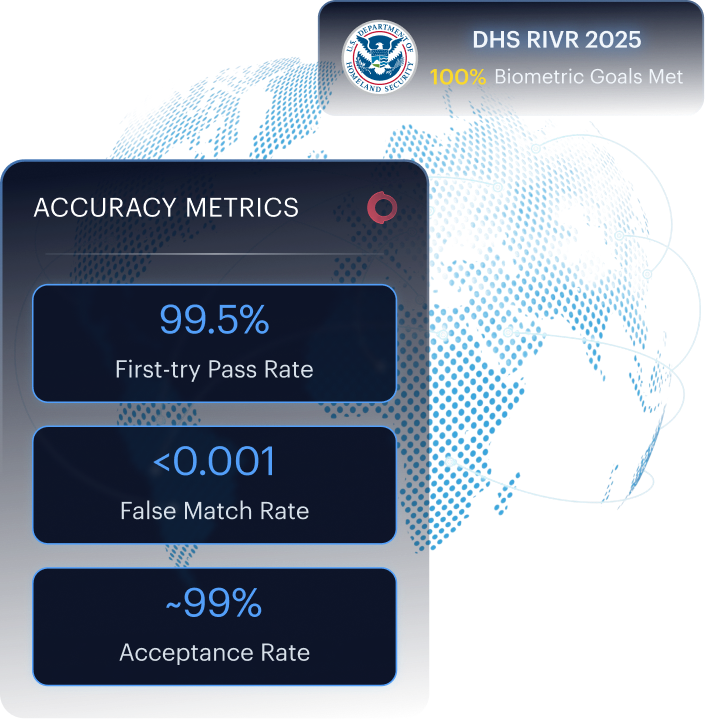
Numbers Your Compliance Team Can Defend
Under 1% false rejection means legitimate users complete onboarding instead of dropping out at verification.
Met 100% of biometric accuracy goals in the U.S. Department of Homeland Security's RIVR 2025 challenge. Tested under worst-case conditions across diverse populations.
CERTIFIED LIVENESS FOR REGULATED ONBOARDING
End-to-End Face Verification Service Built to Defeat Sophisticated Fraud
Smart Face Liveness
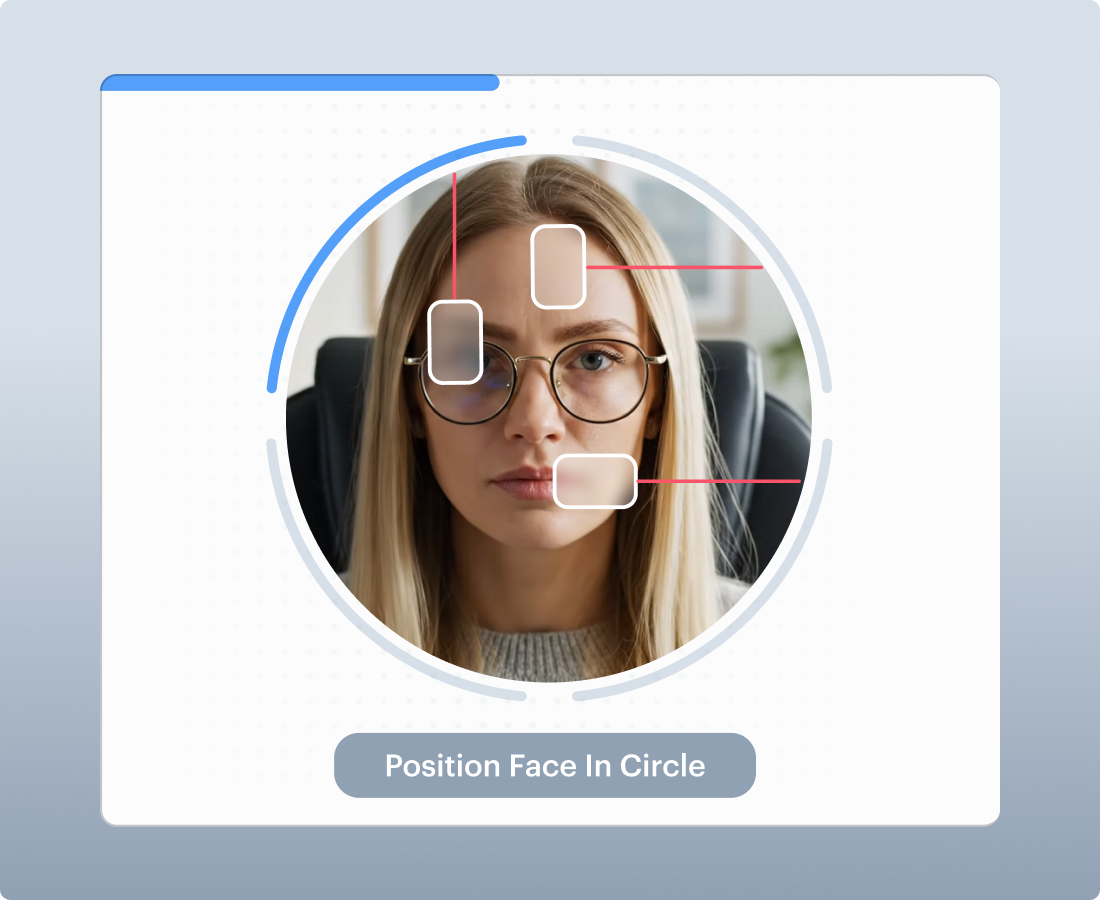
Passive Liveness
Runs to confirm a real human is present, analysing texture, reflections, and depth cues.
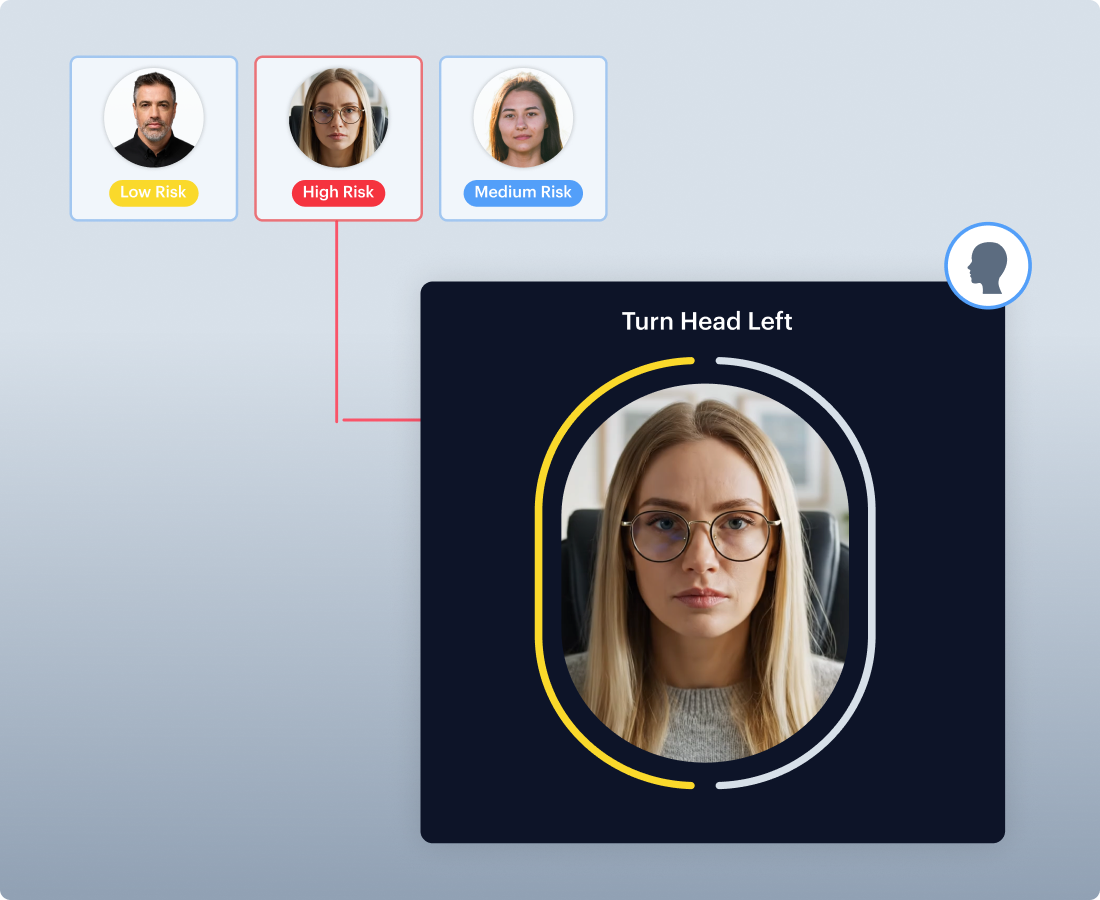
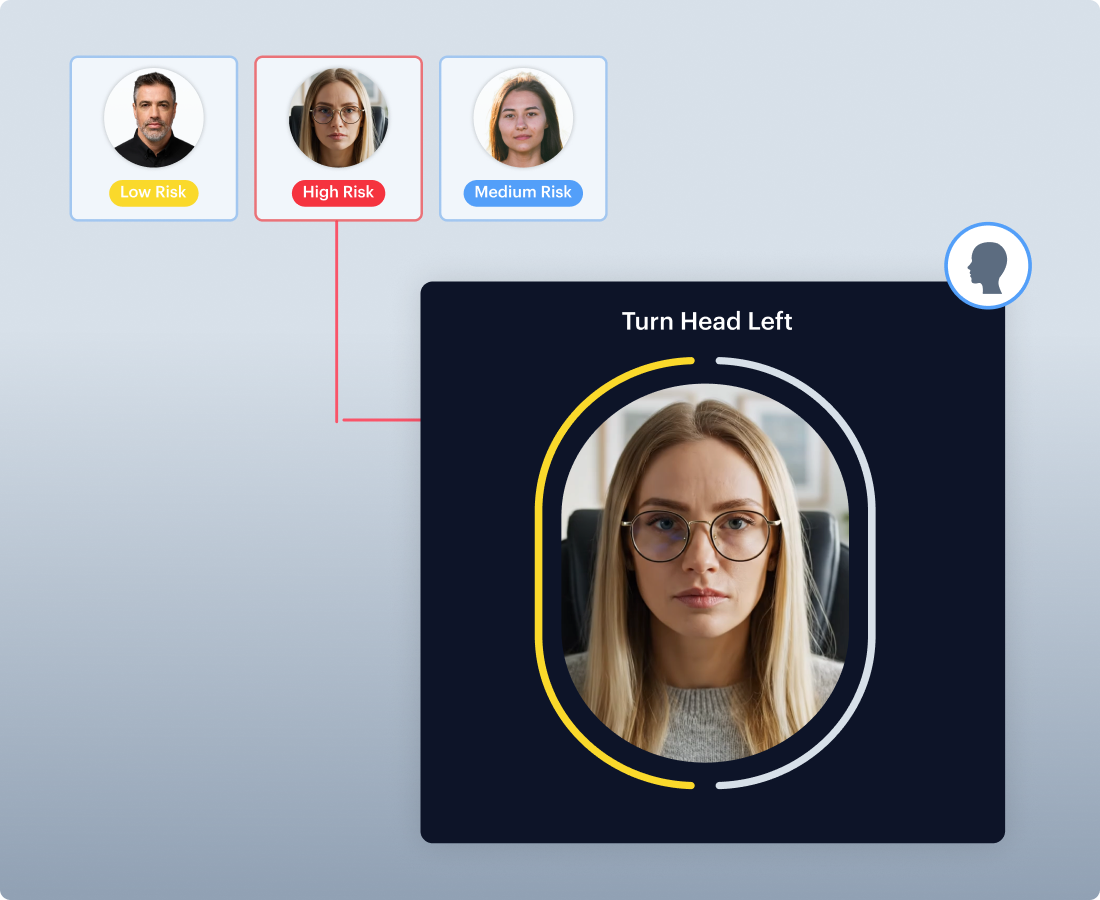
Active Liveness
Prompted action (head movement/gesture). 3D depth, motion, and texture analysis confirms physical presence.
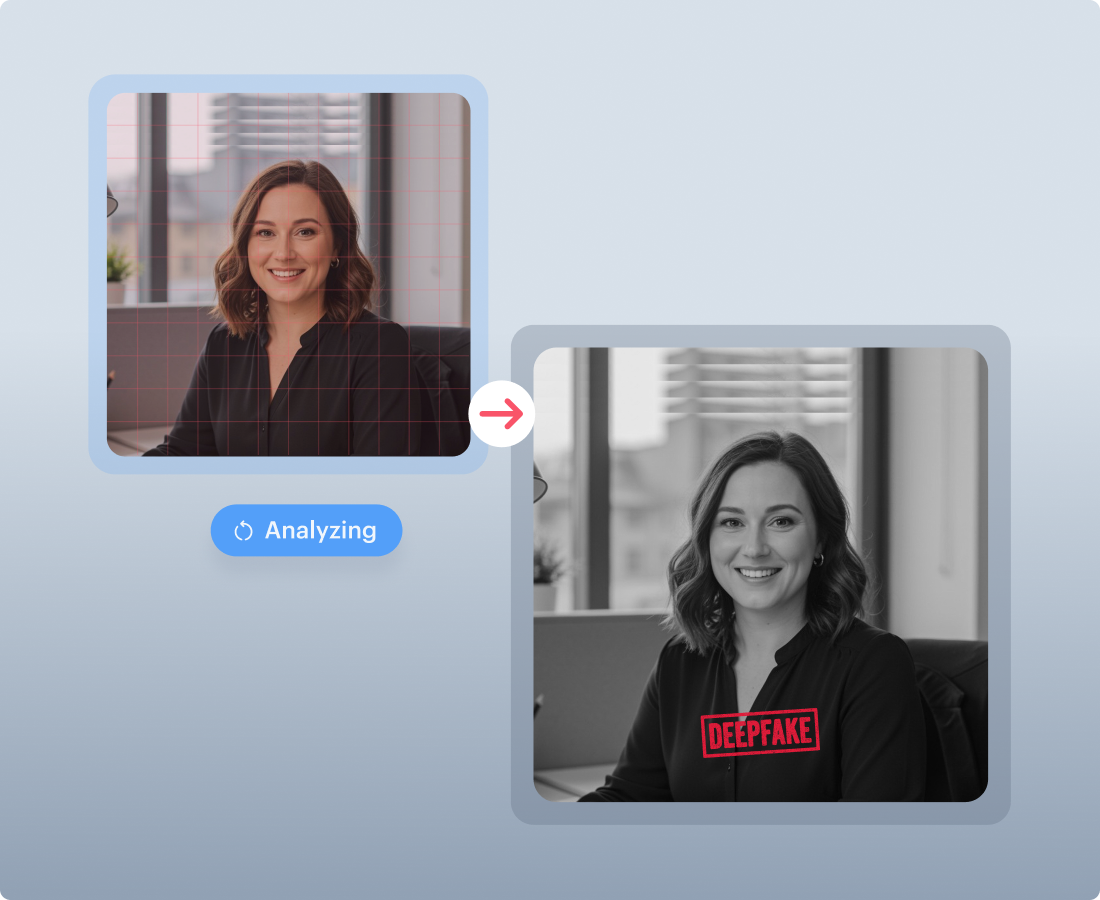
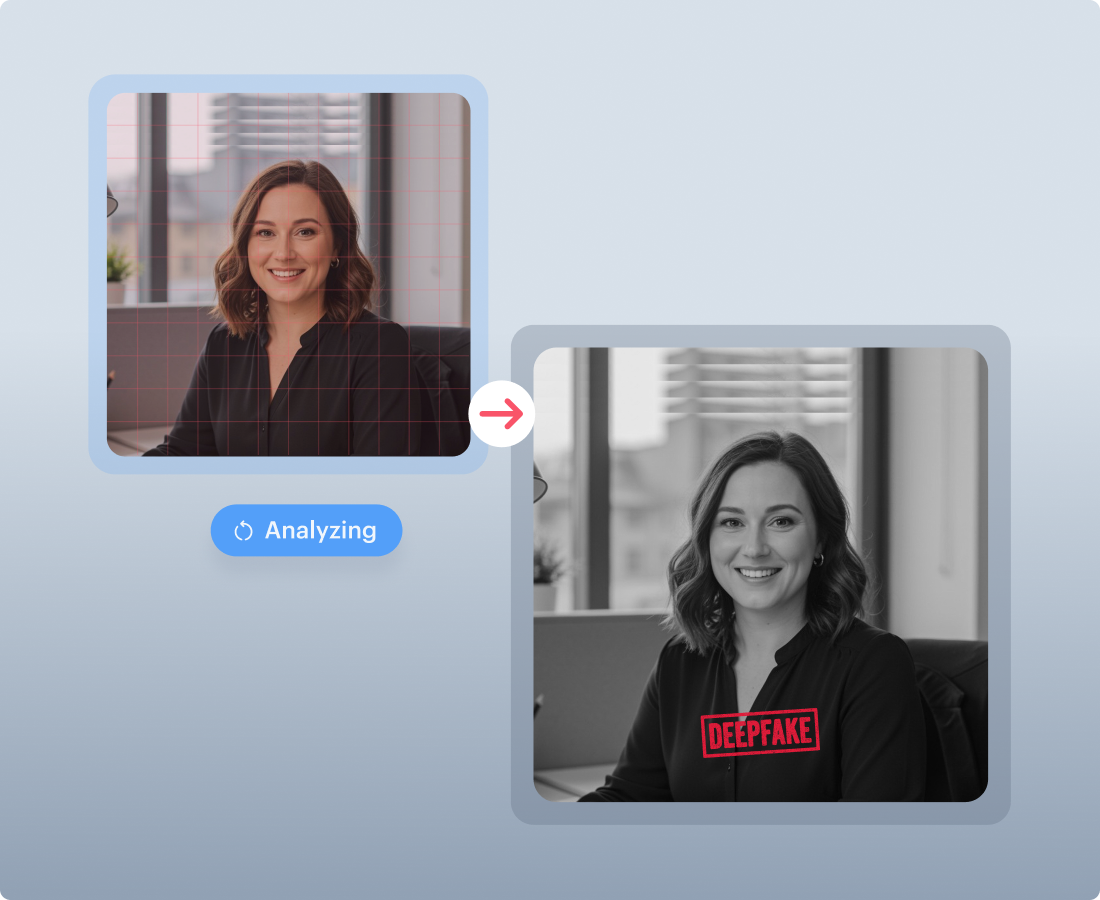
Deepfake, Replay & Injection Defence
Detects AI deepfakes, video/screen replay, and injected streams in real time using layered liveness signals.
Multi-Stream Detection Architecture
Parallel RGB + DCT Processing
Shufti processes standard visual inputs alongside high-frequency DCT representations simultaneously , catching generative artefacts invisible to conventional RGB-only systems.
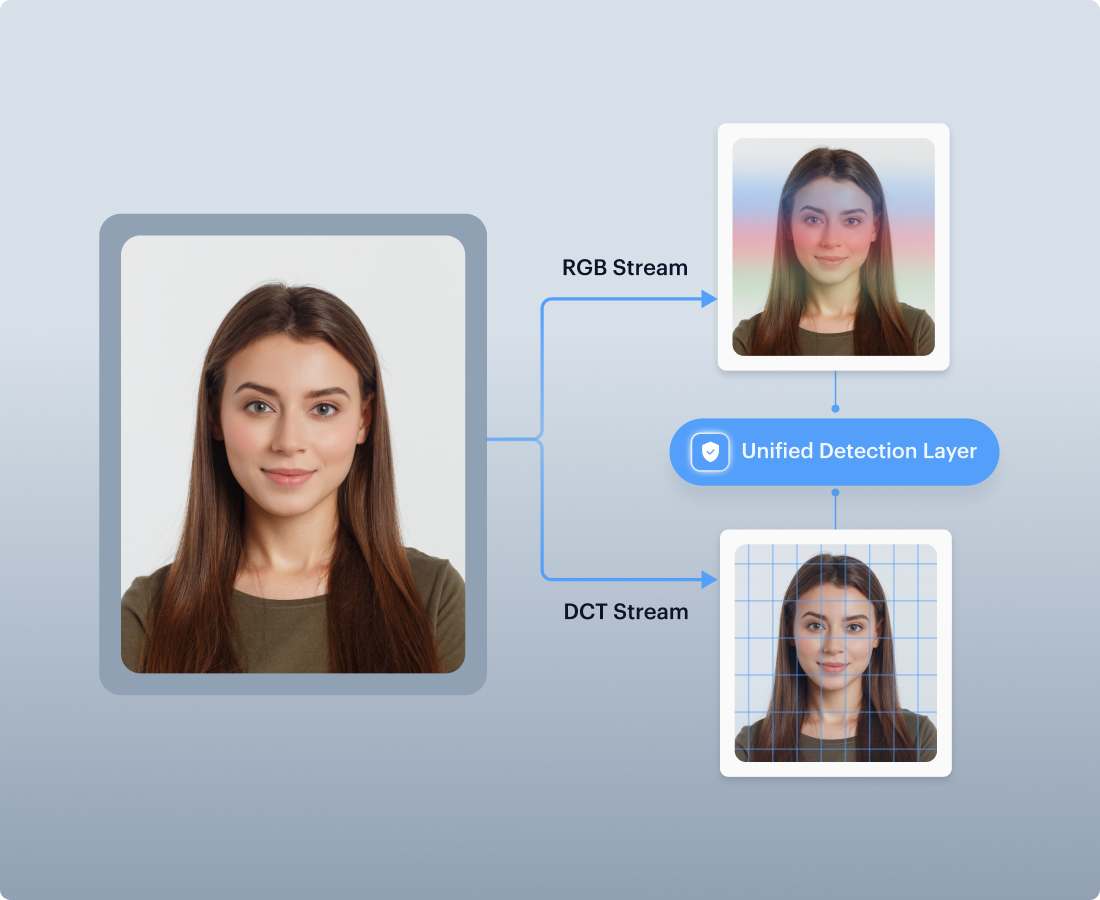
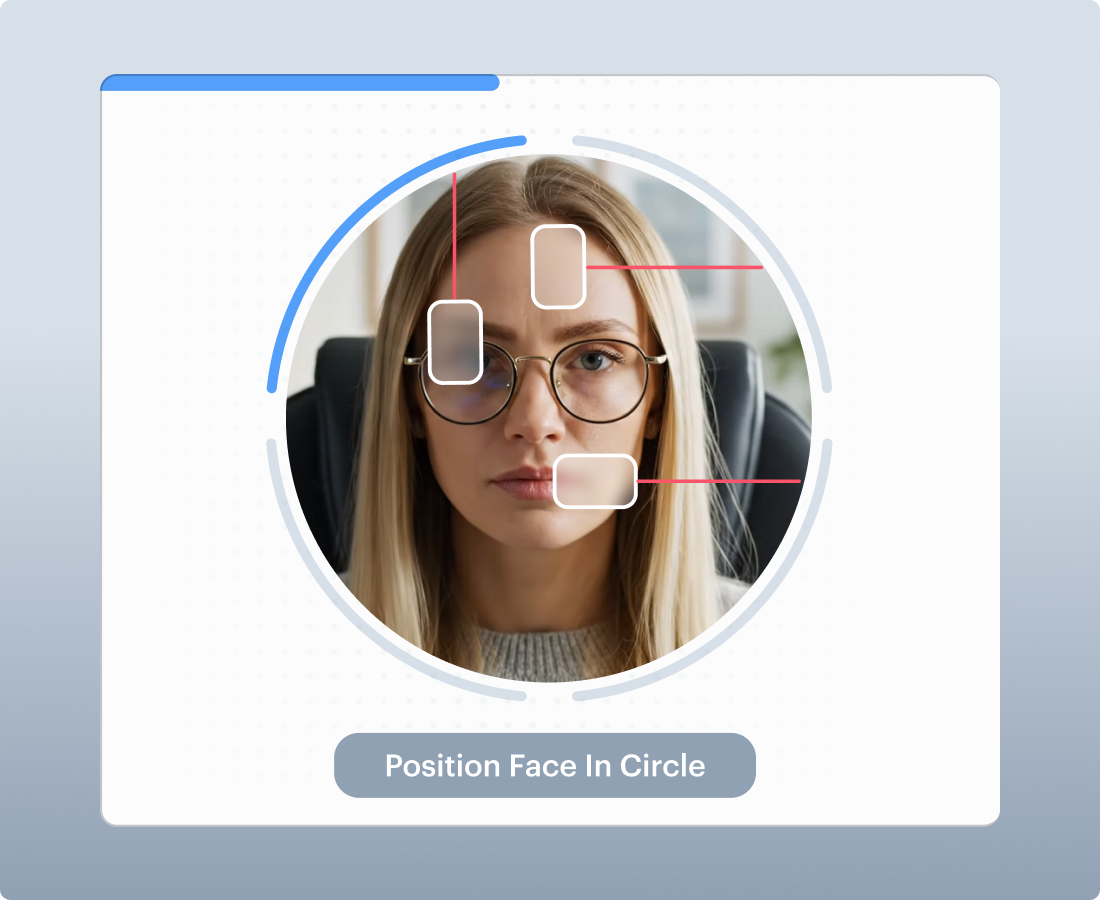
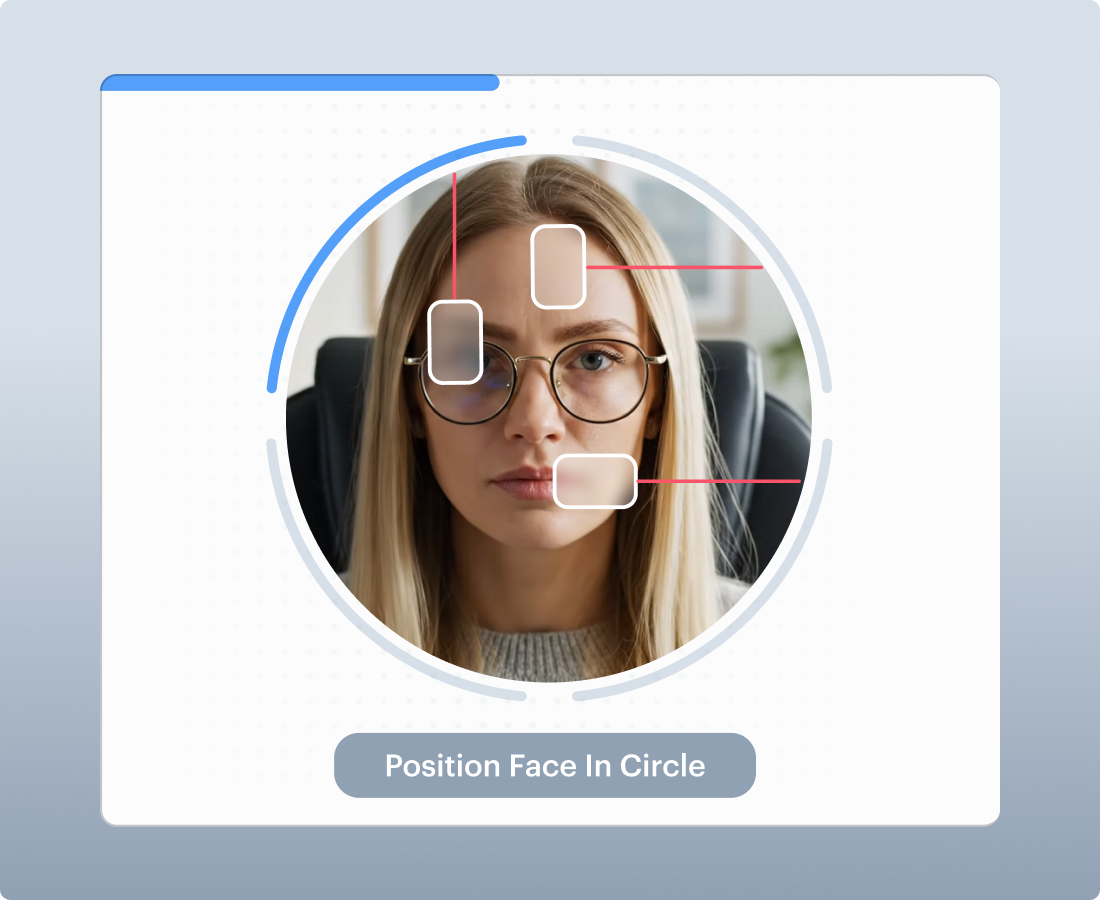
Region-Based Facial Analysis
Specialised models analyse facial regions independently , eyes, nose, mouth, skin boundaries ,detecting localised manipulation that full-frame detectors miss. Works on partial and cropped faces.
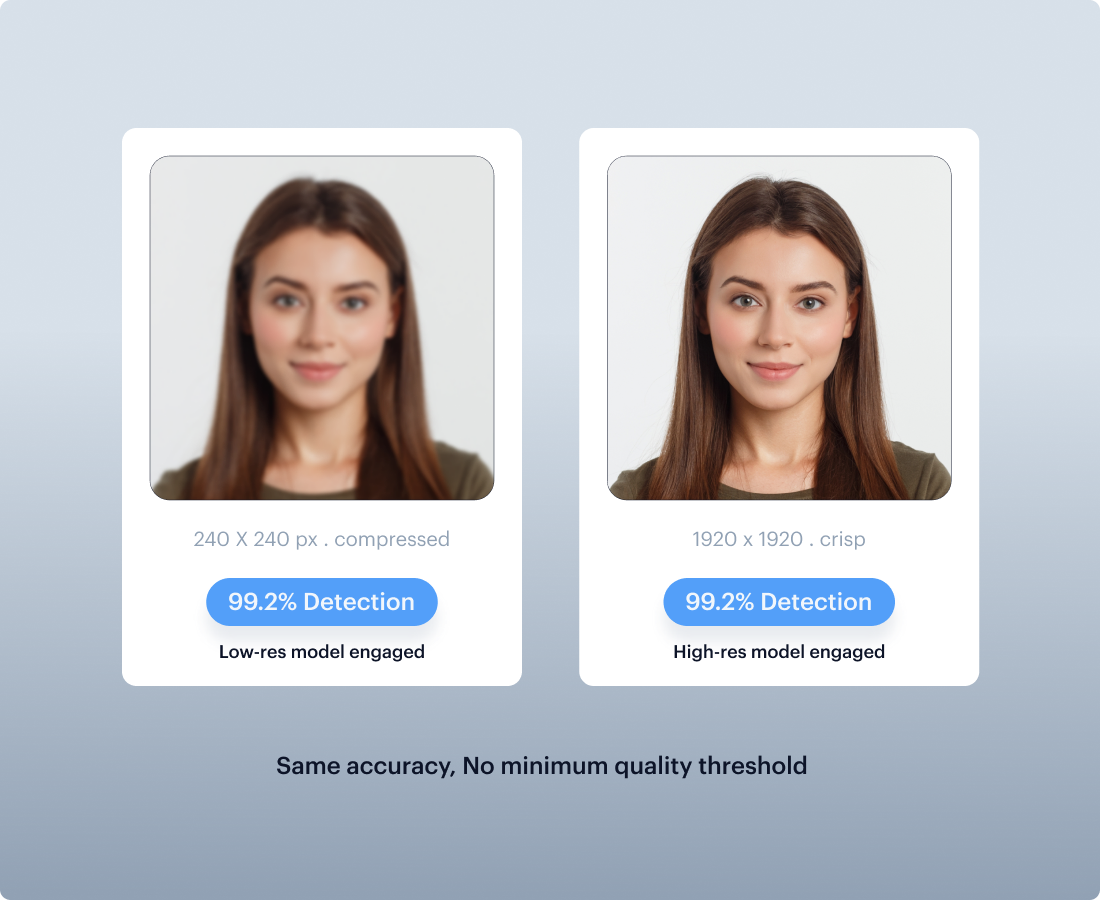
Resolution-Aware Models
Separate models trained for low-res and high-res inputs. Compressed mobile captures receive the same detection accuracy as high-resolution images , no minimum quality threshold.

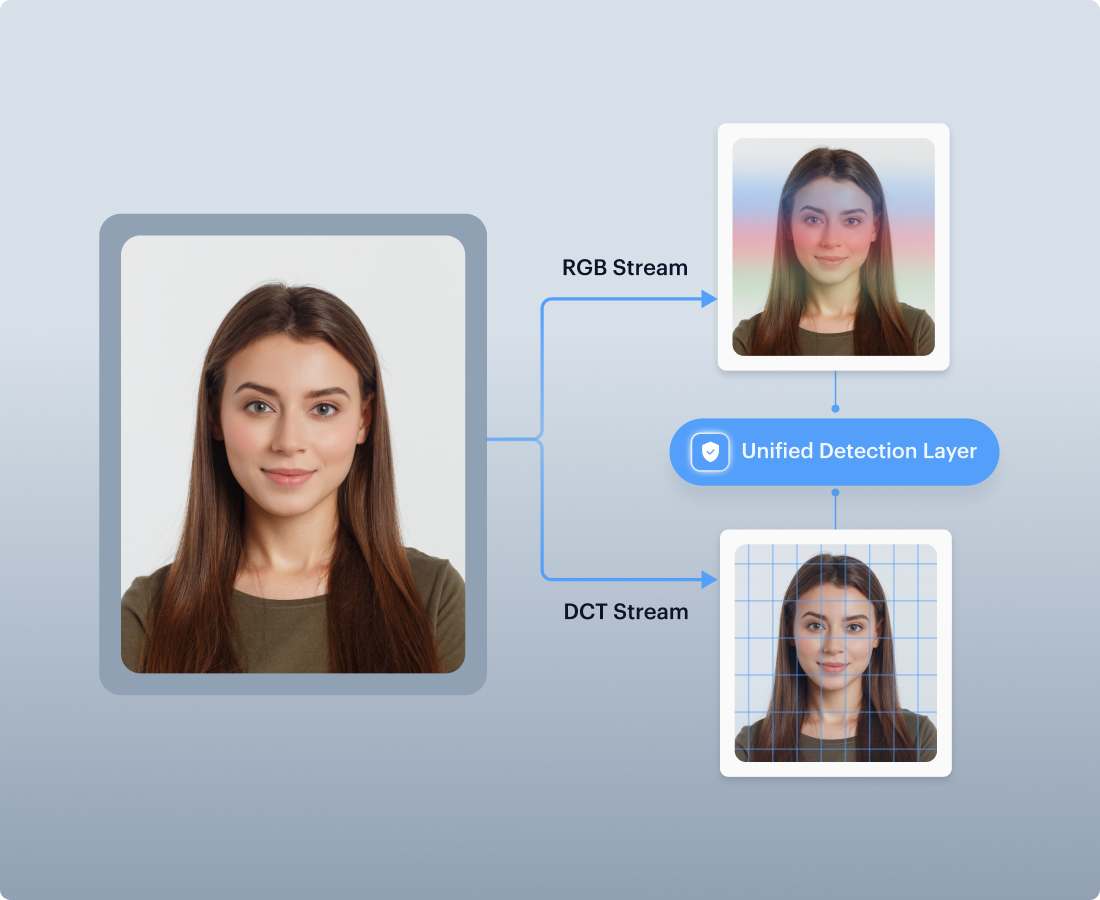
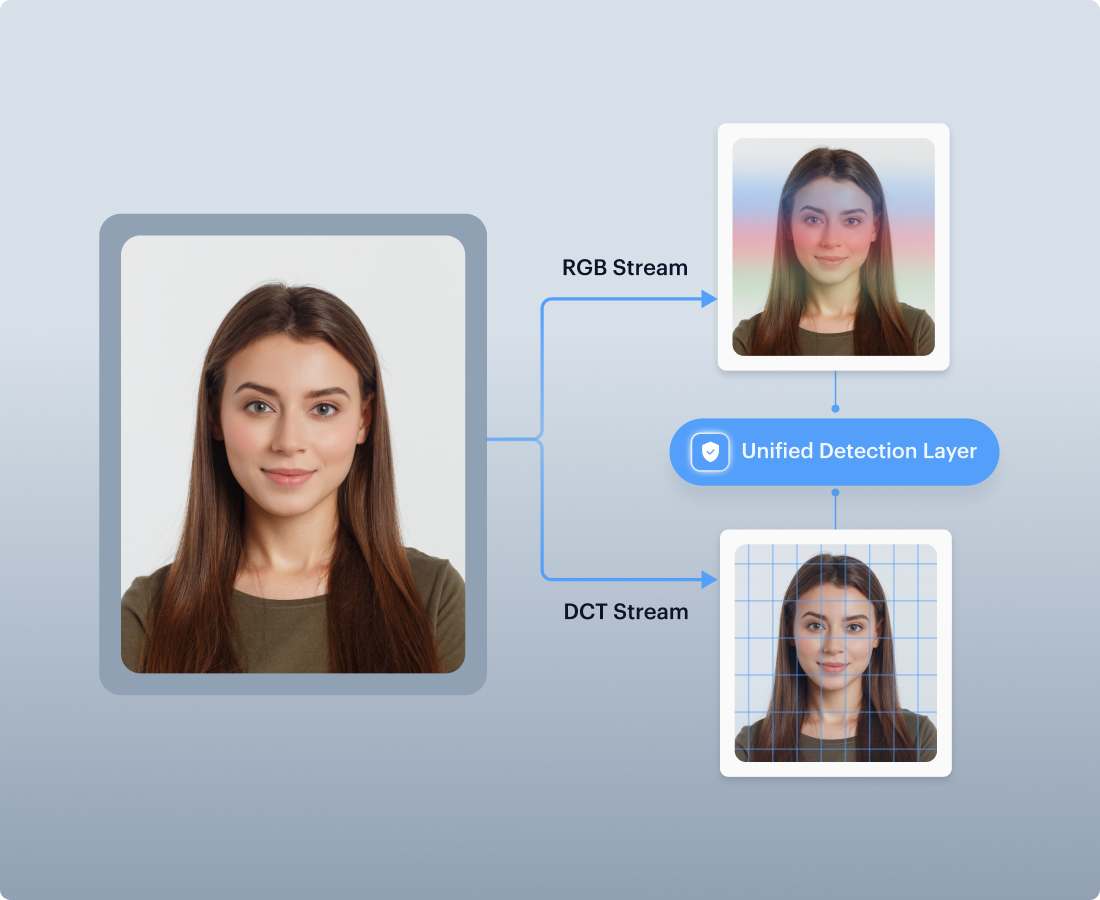
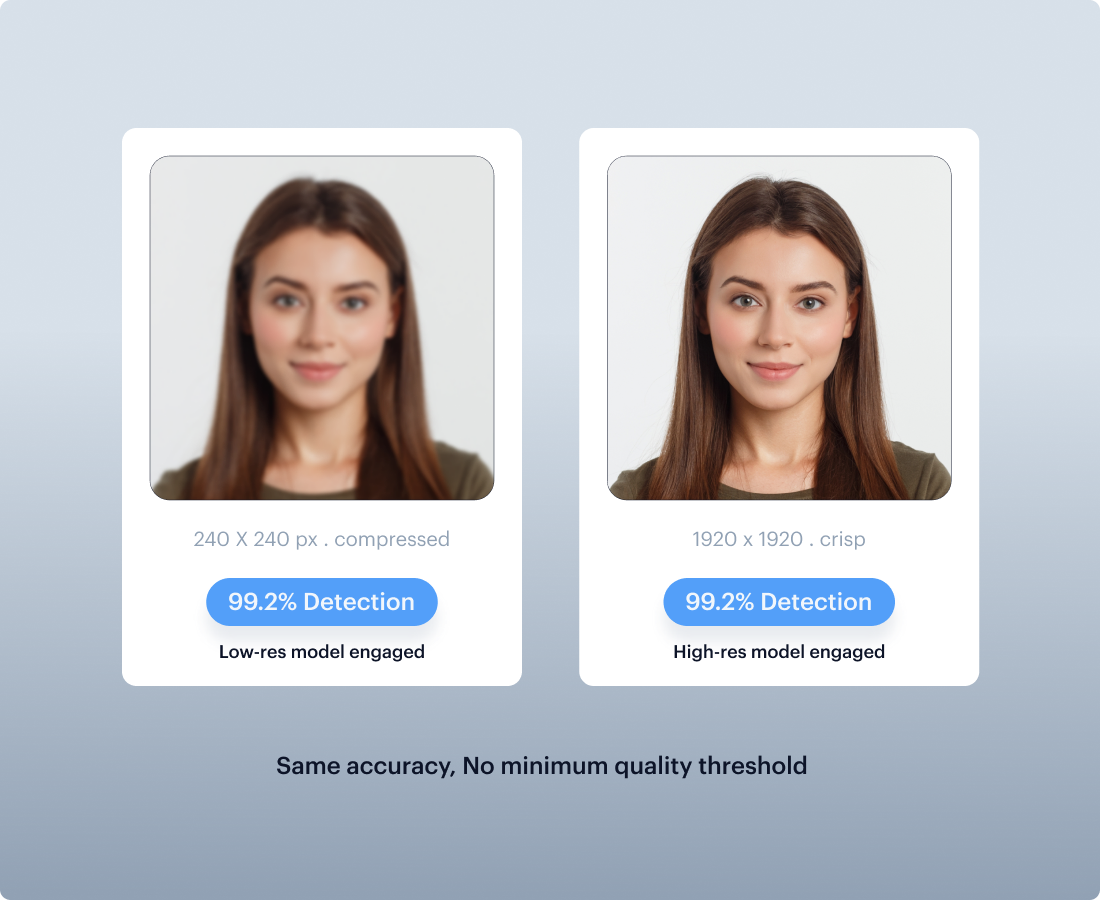

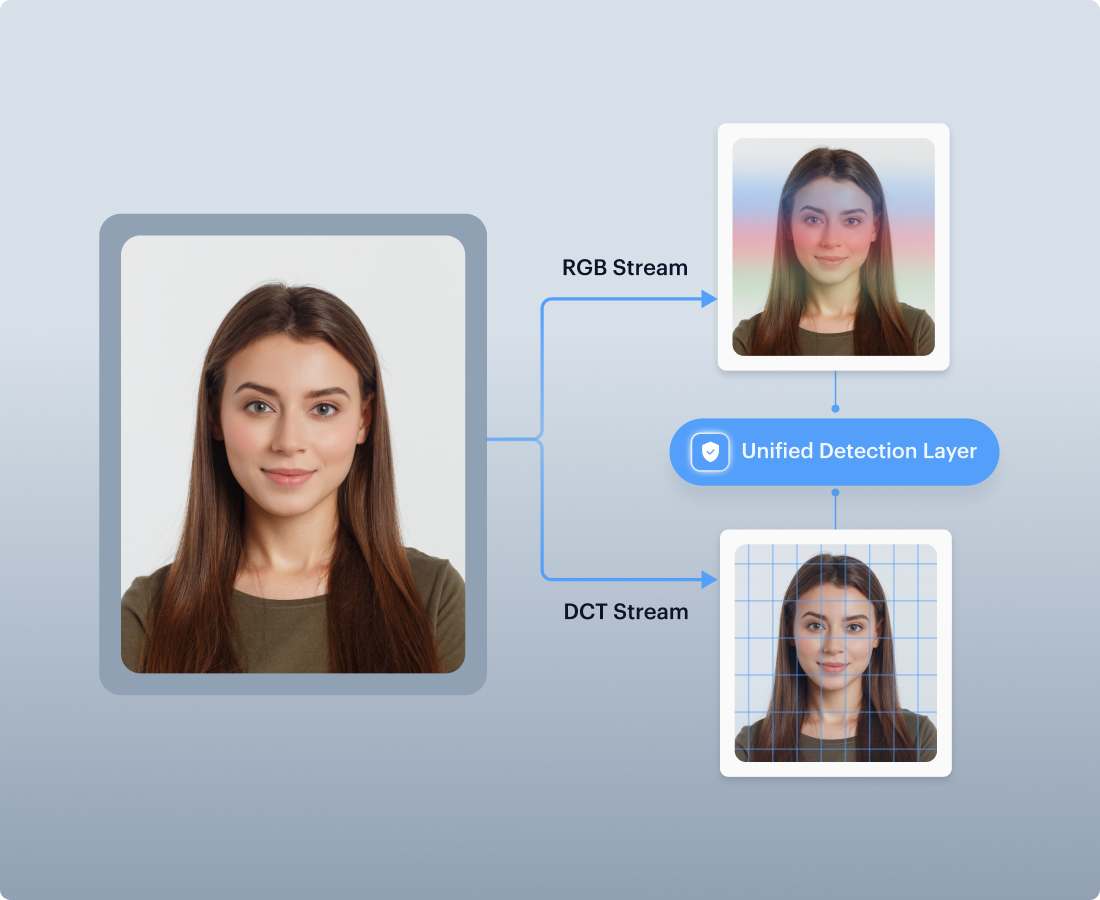
Image Forensics
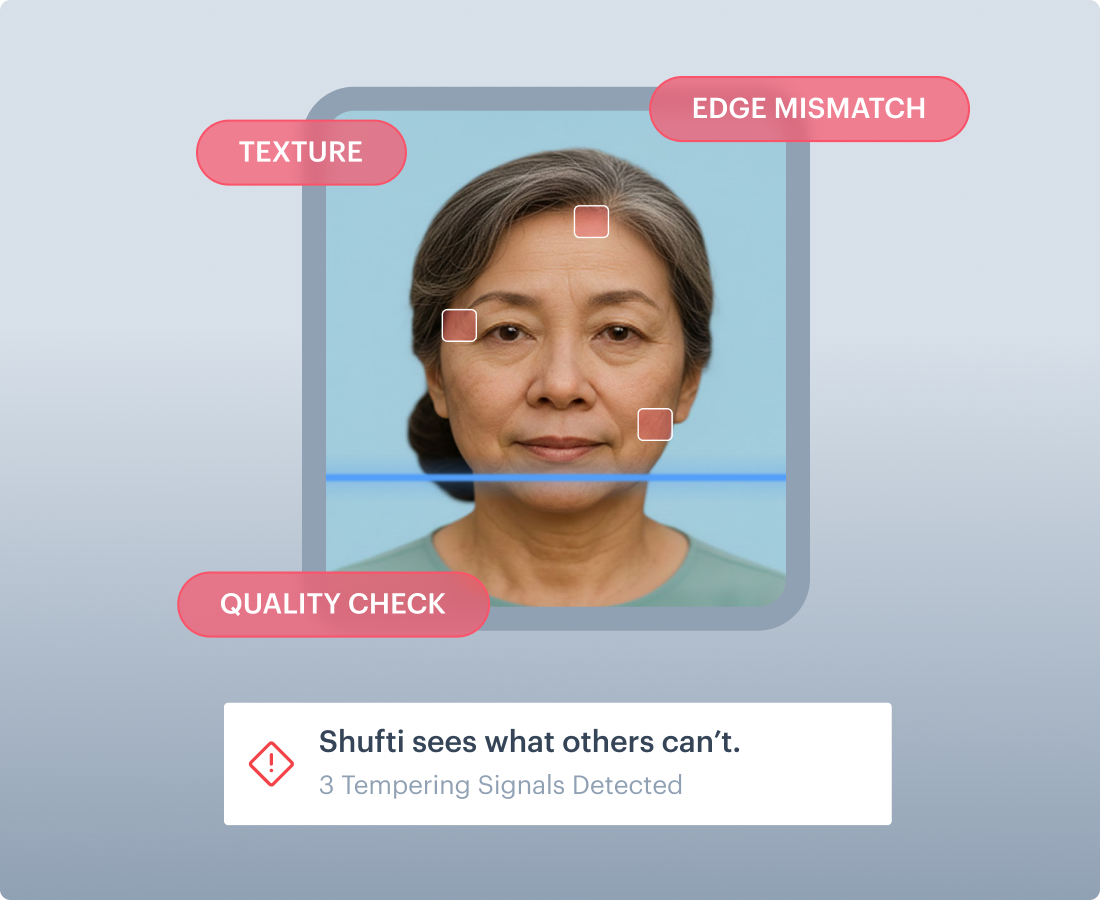
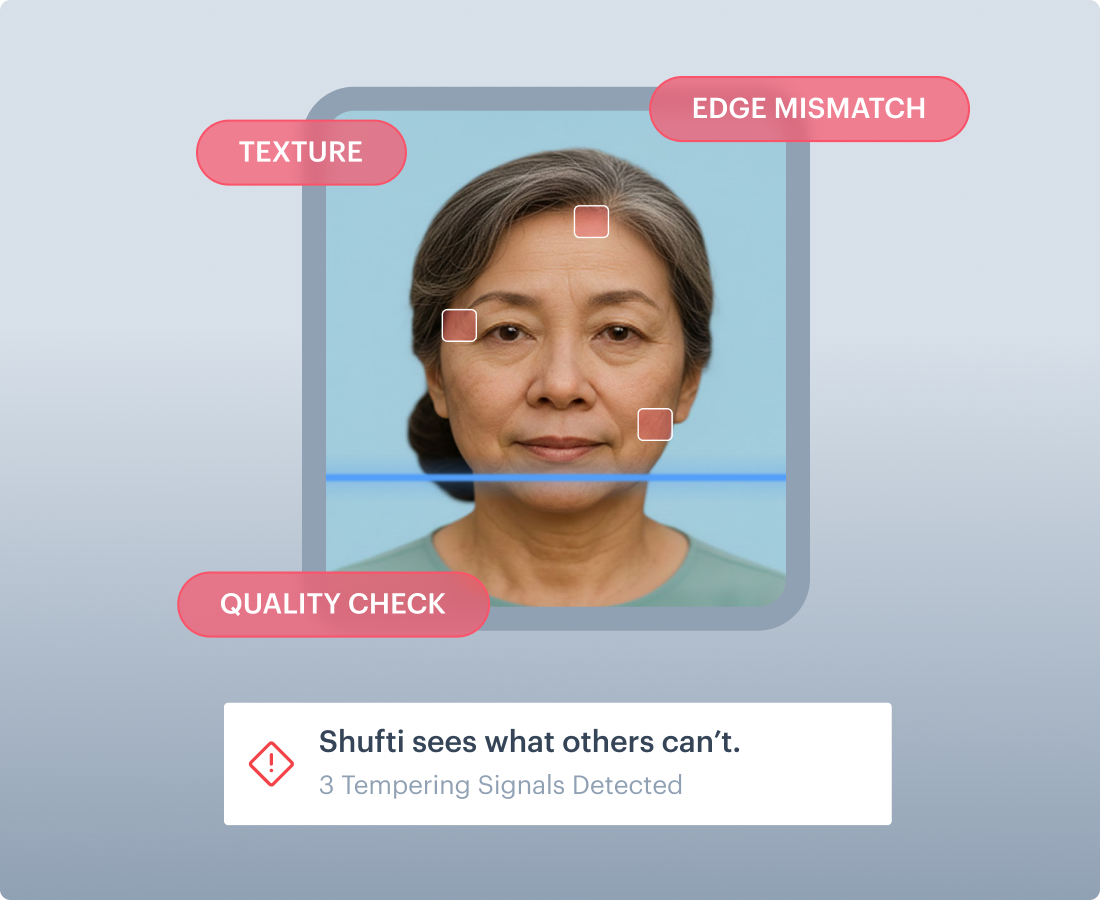
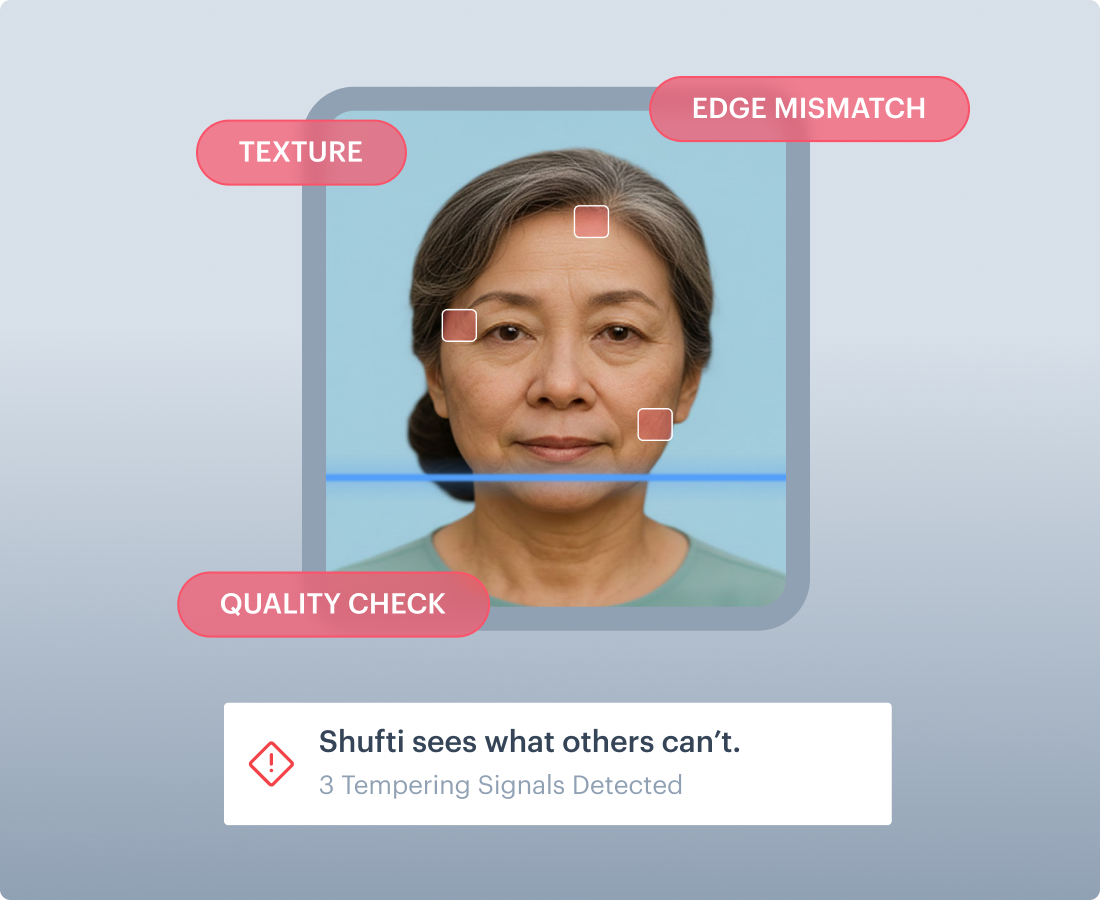
Brings hidden tampering to the surface
Shufti enhances the spots where manipulation usually leaves traces, fake-edge seams, mismatched textures, unusual noise, so the AI catches near-invisible tampering even on low-quality images.
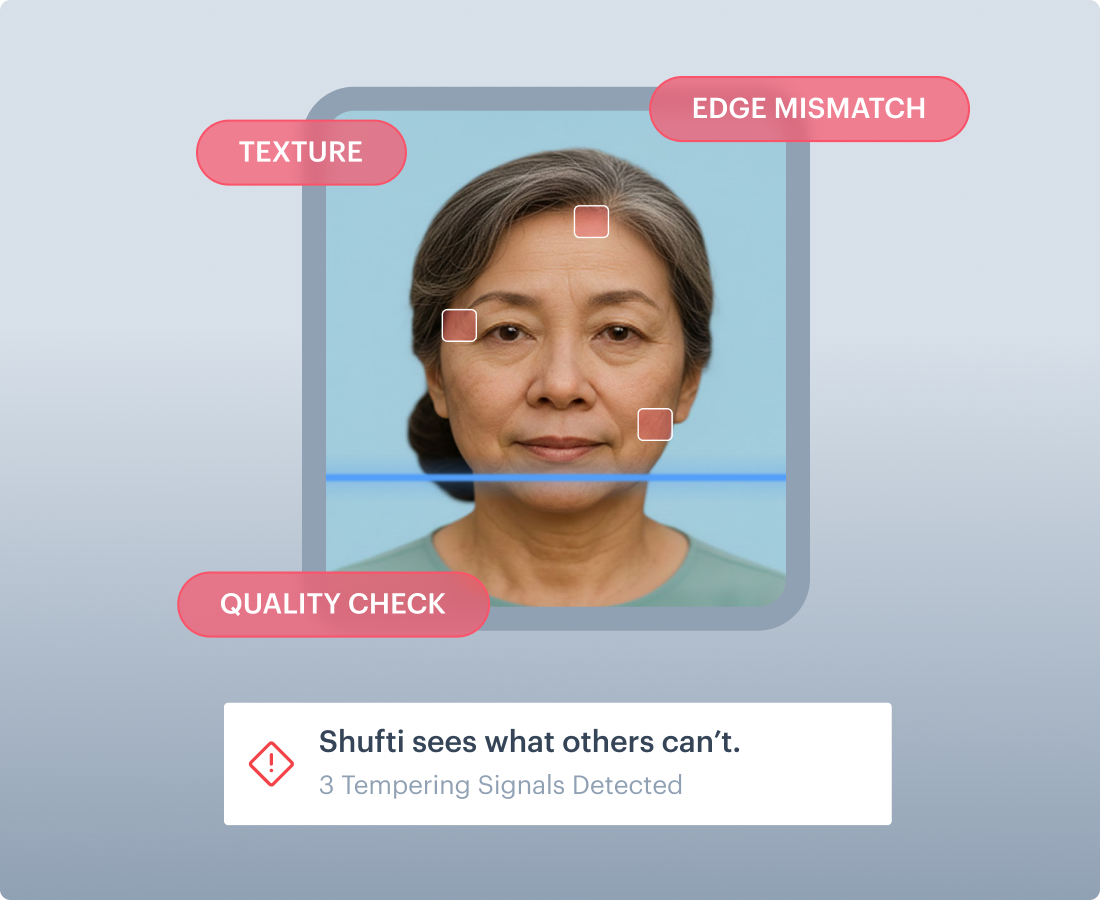
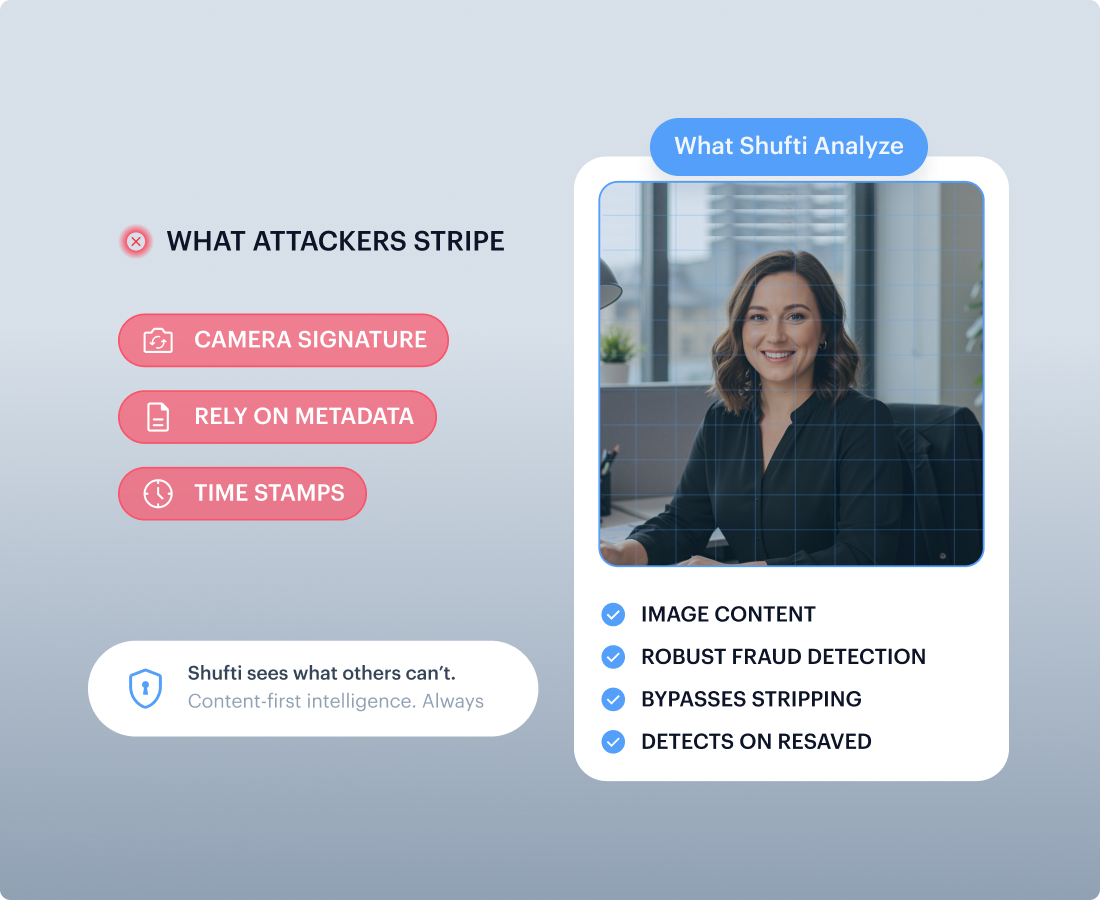
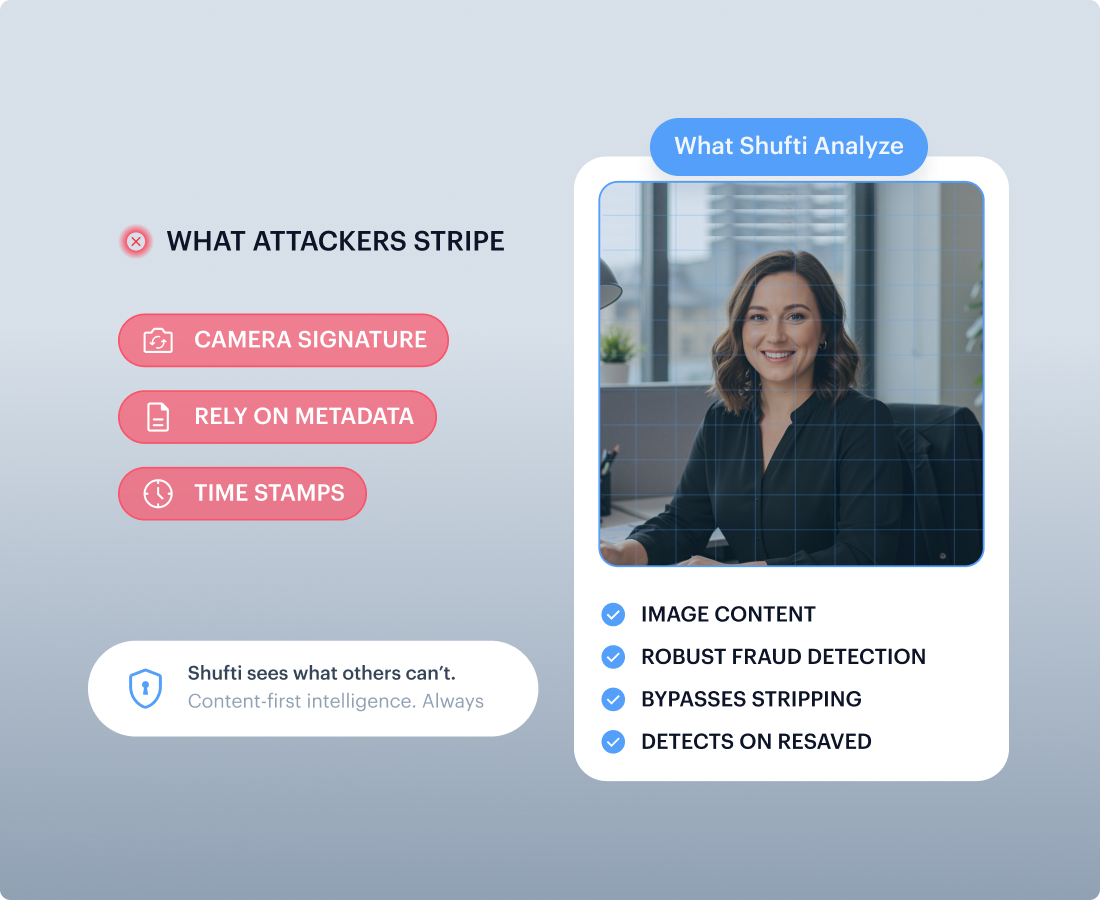
Reads the image, not the metadata
Attackers can strip file metadata, camera signatures, and timestamps in seconds. Shufti ignores all of that and learns from the image content itself, so detection still holds even on repackaged or re-saved files.
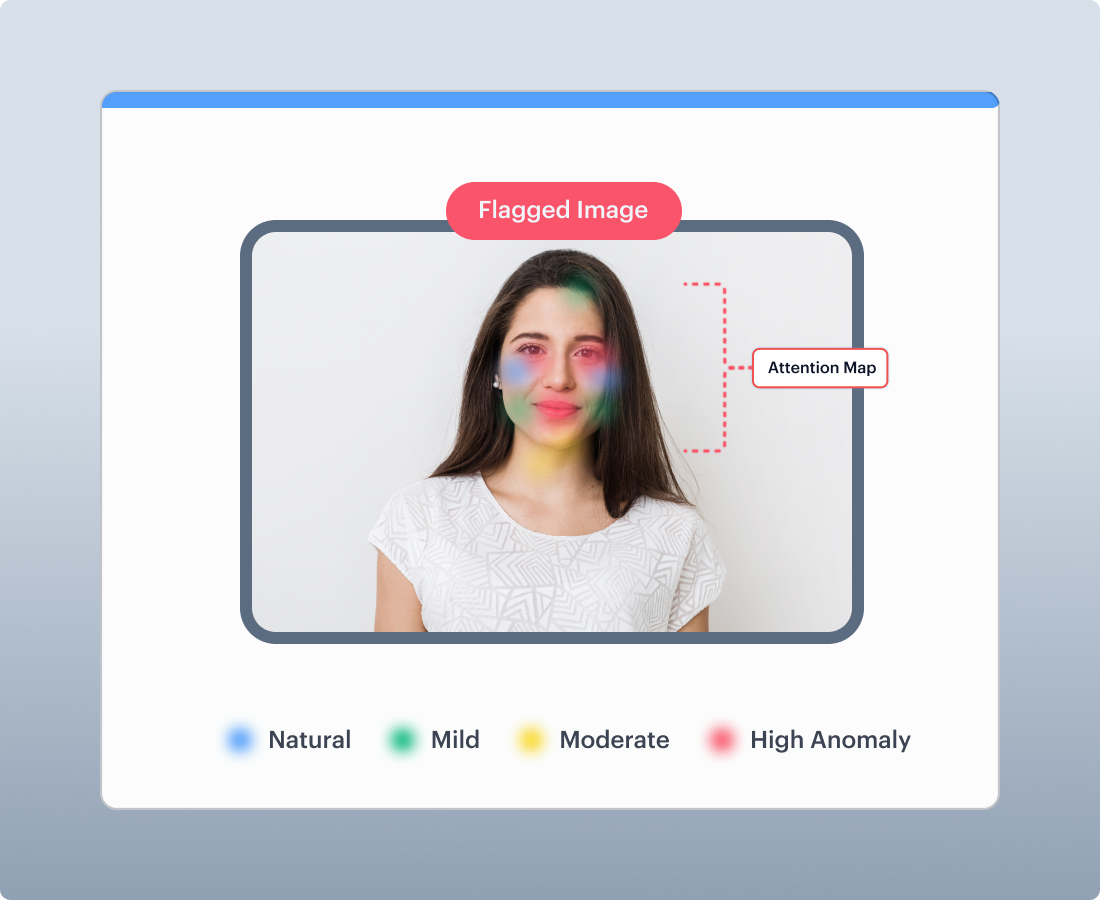
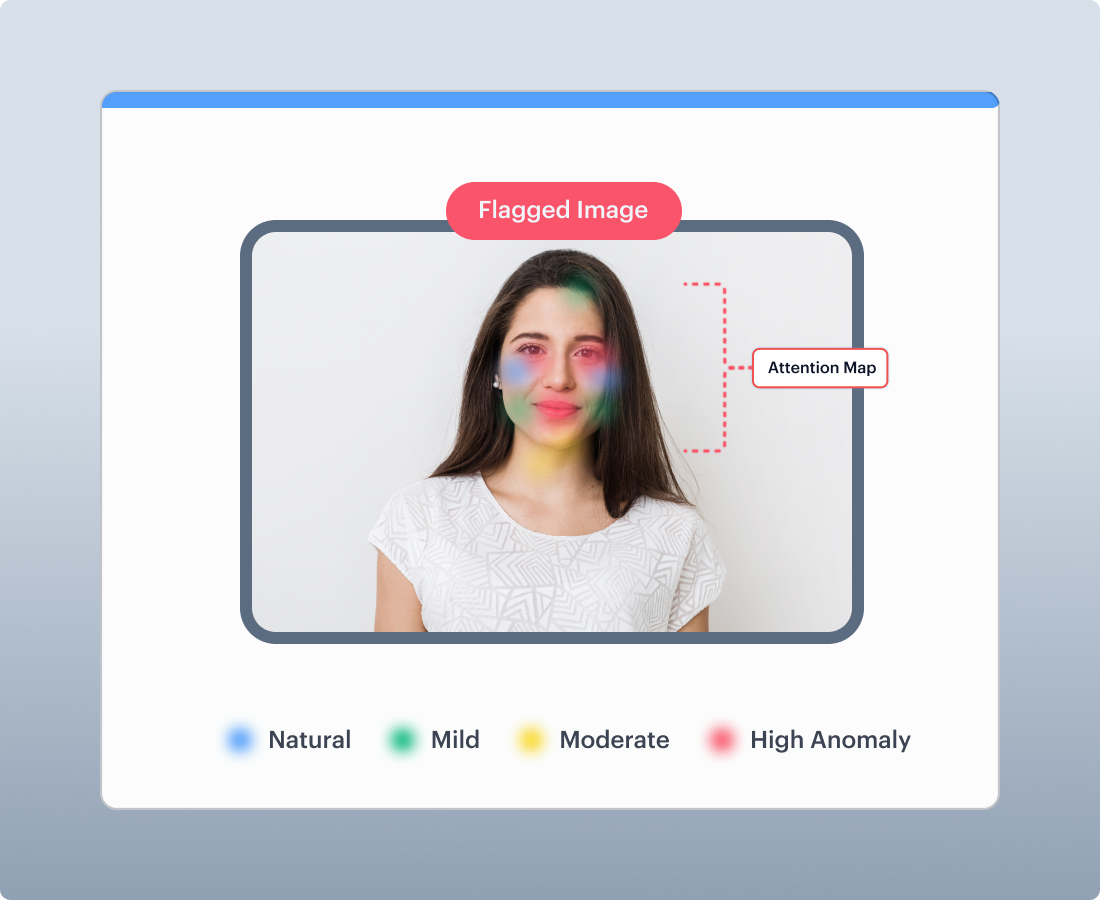
Attention map for every decision
Every flagged image gets a colour-coded attention map ,blue for natural areas, green/orange for moderate deviations, and red/yellow for high-anomaly zones that triggered the deepfake alert ,so fraud teams see exactly where and why.
Continuous Learning Pipeline
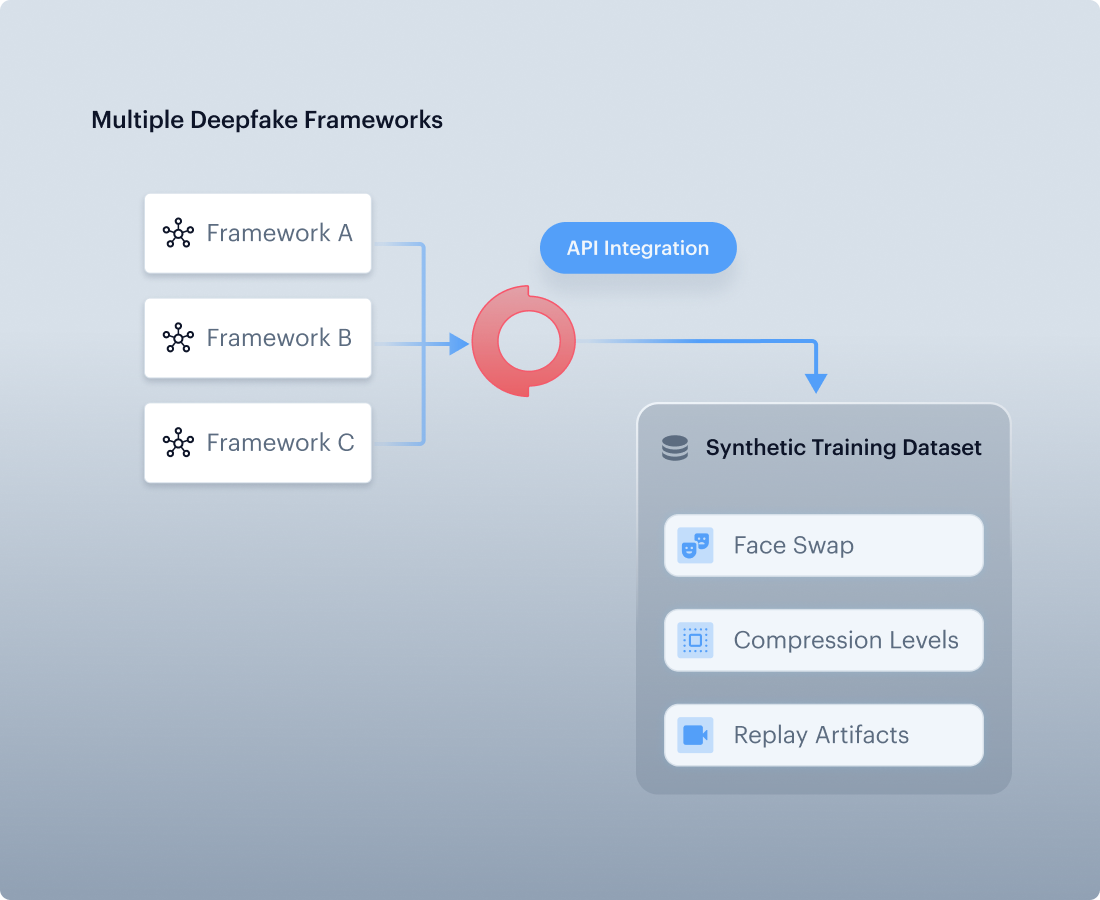
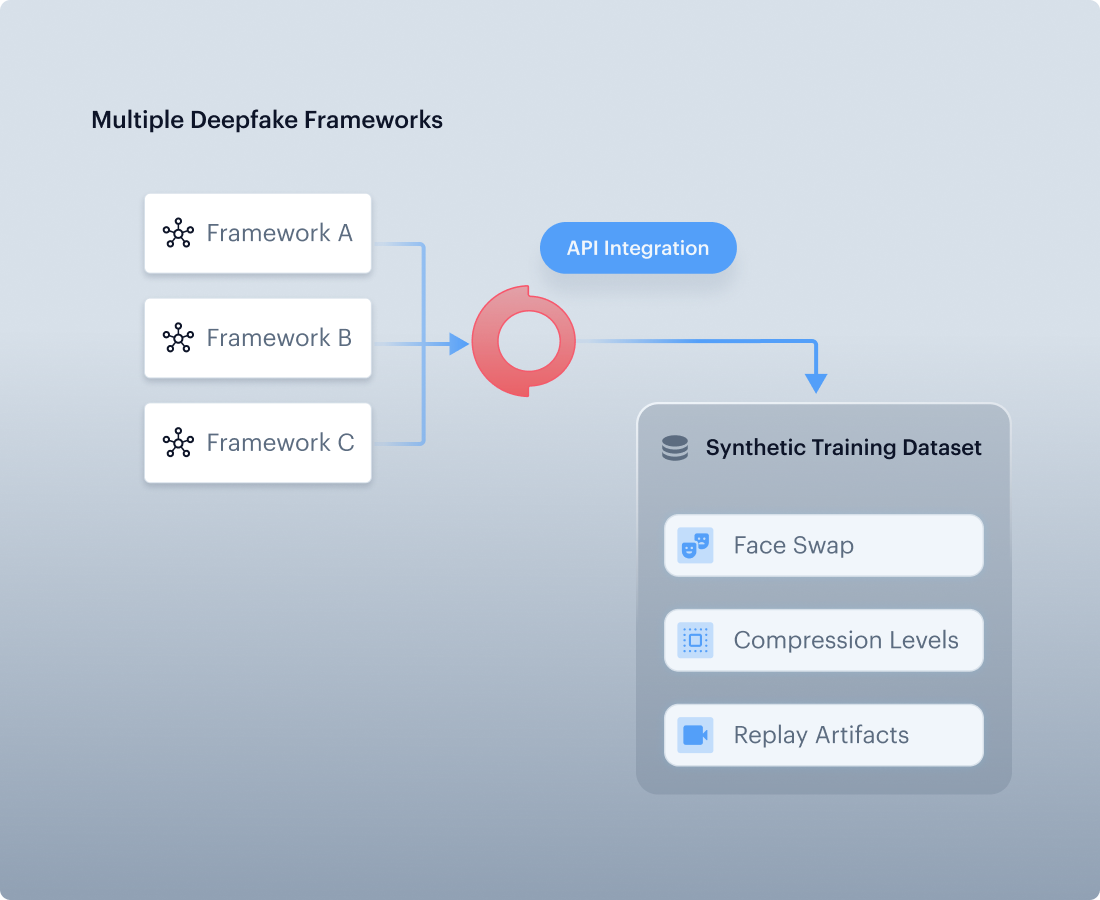
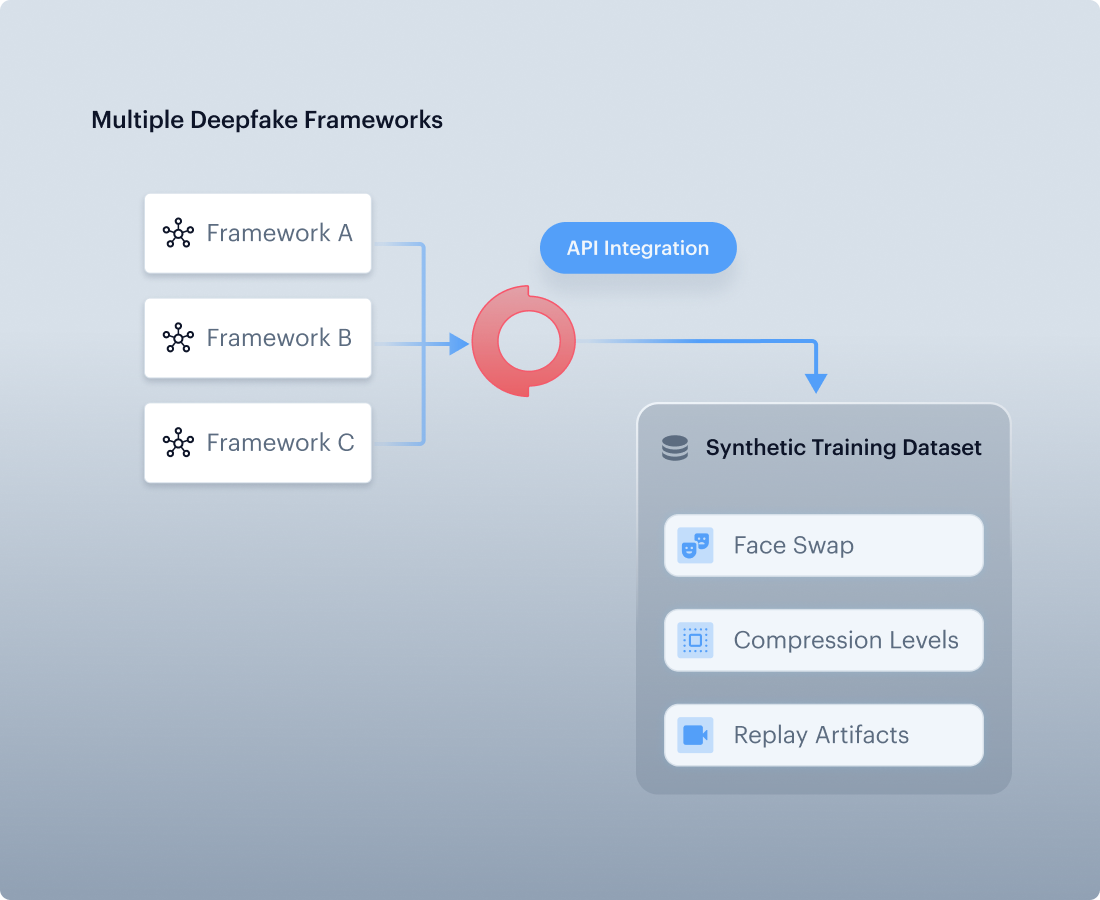
Synthetic Training Data Generation
Shufti integrates APIs from multiple deepfake frameworks to generate its own training data , face swaps, compression levels that mirror real attacks.
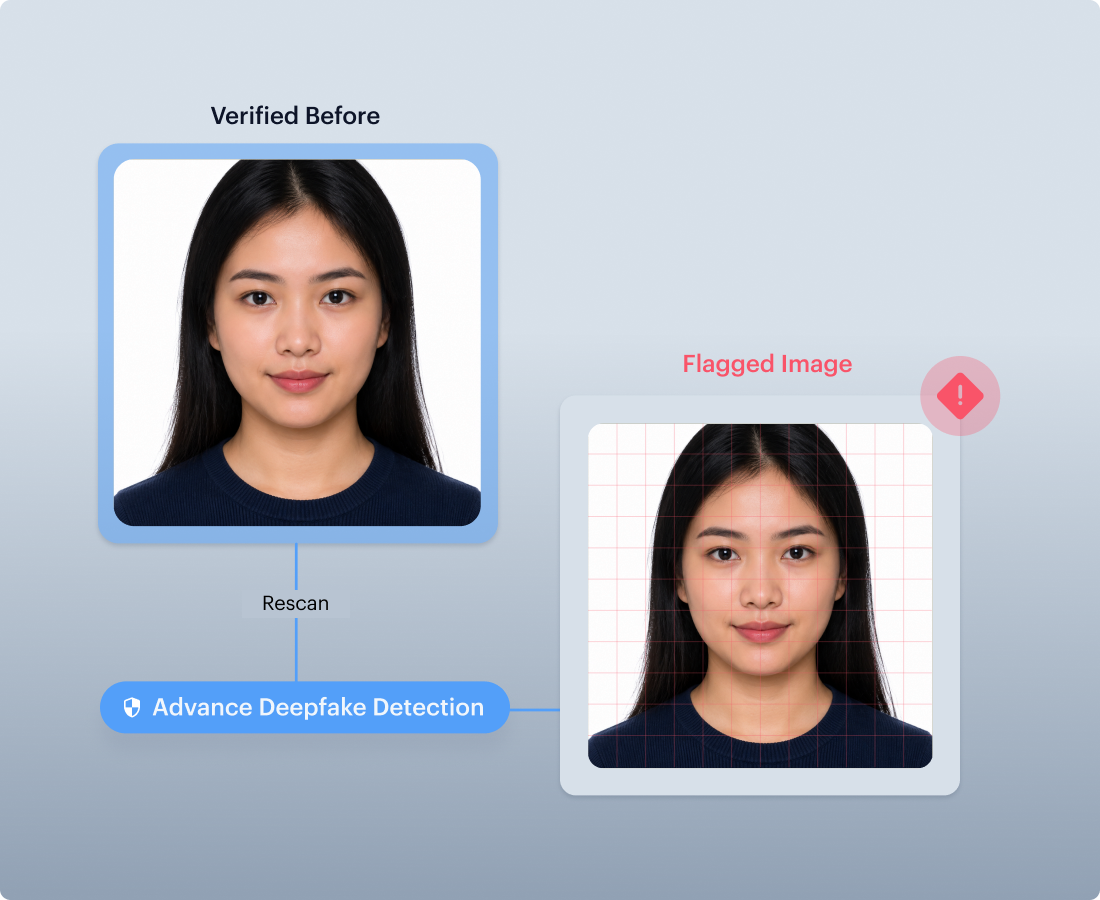
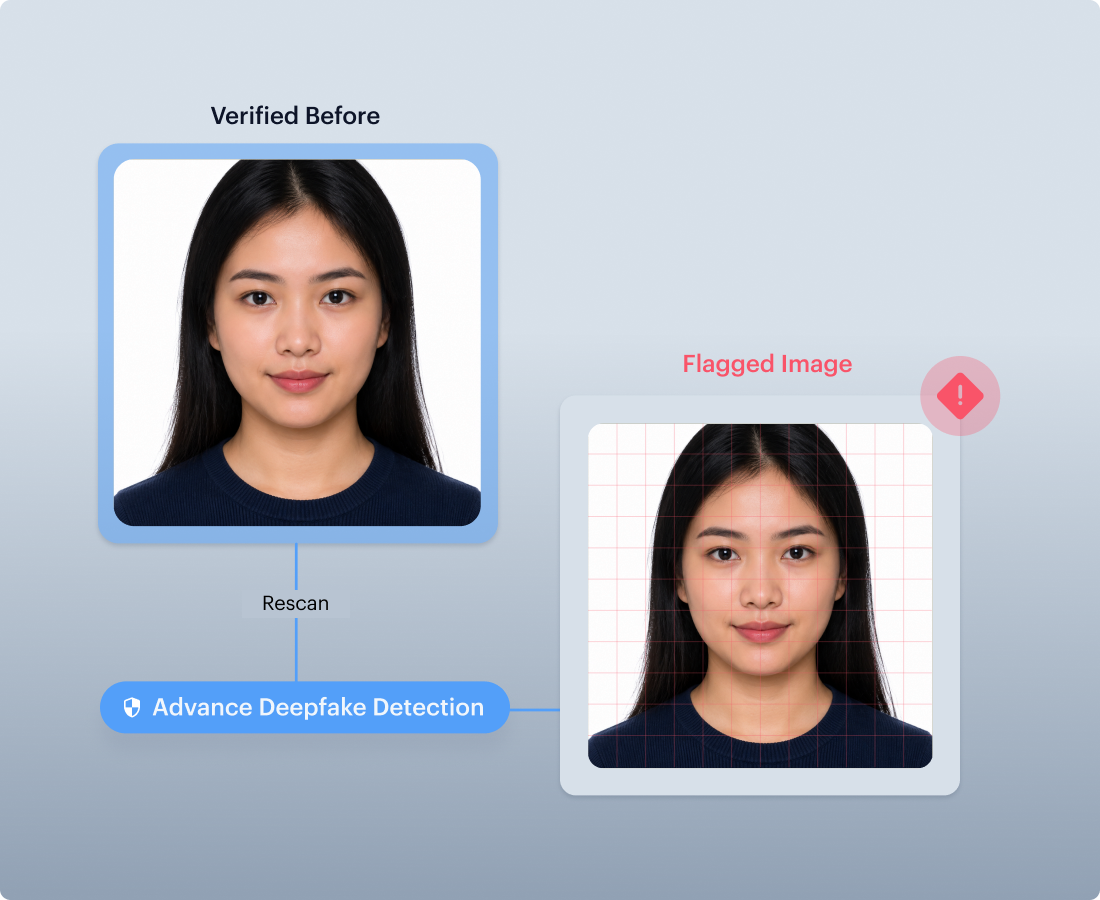
Retrospective Biometric Audit
Rescan past biometric records with today’s deepfake detection models to identify high-risk accounts for review, re-verification, flagging, or closure.
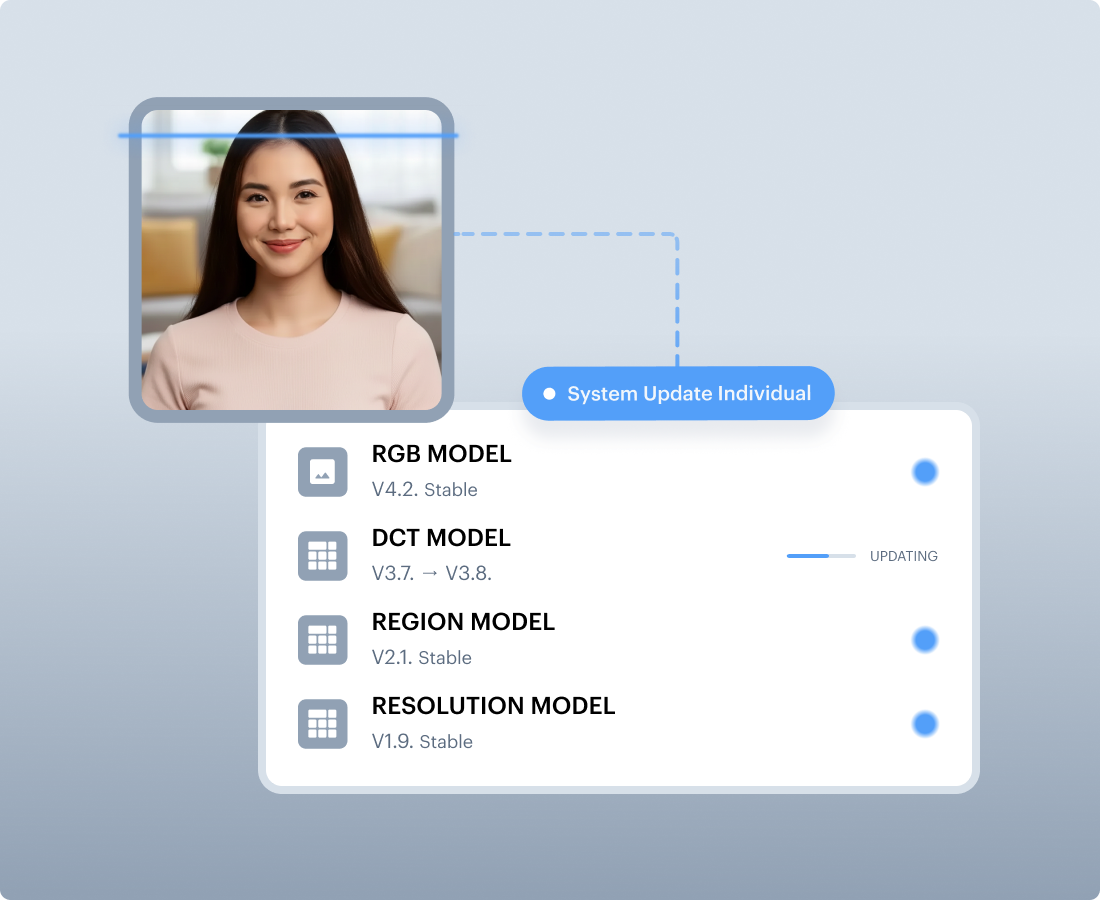
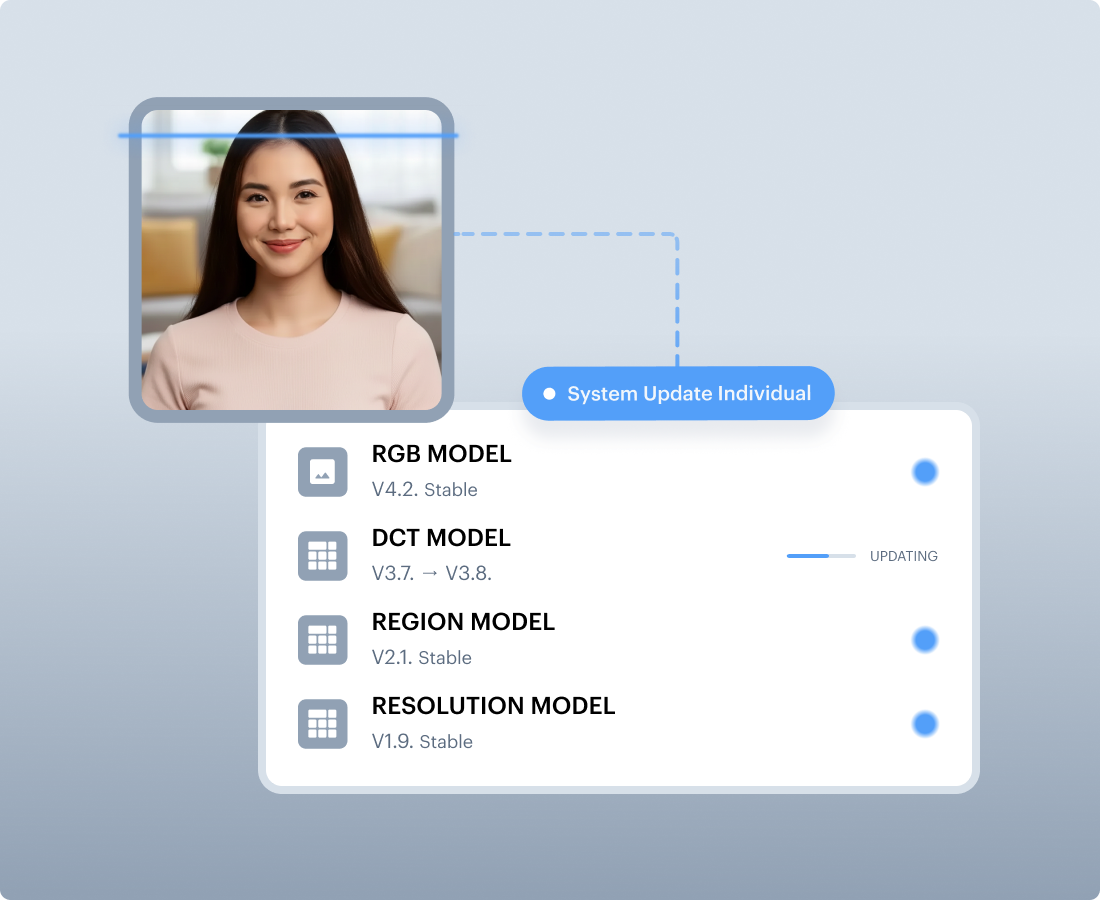
Modular Production Updates
Individual models update independently without disrupting live services. Production metrics are continuously monitored for distribution shifts , catching degradation before it reaches clients.
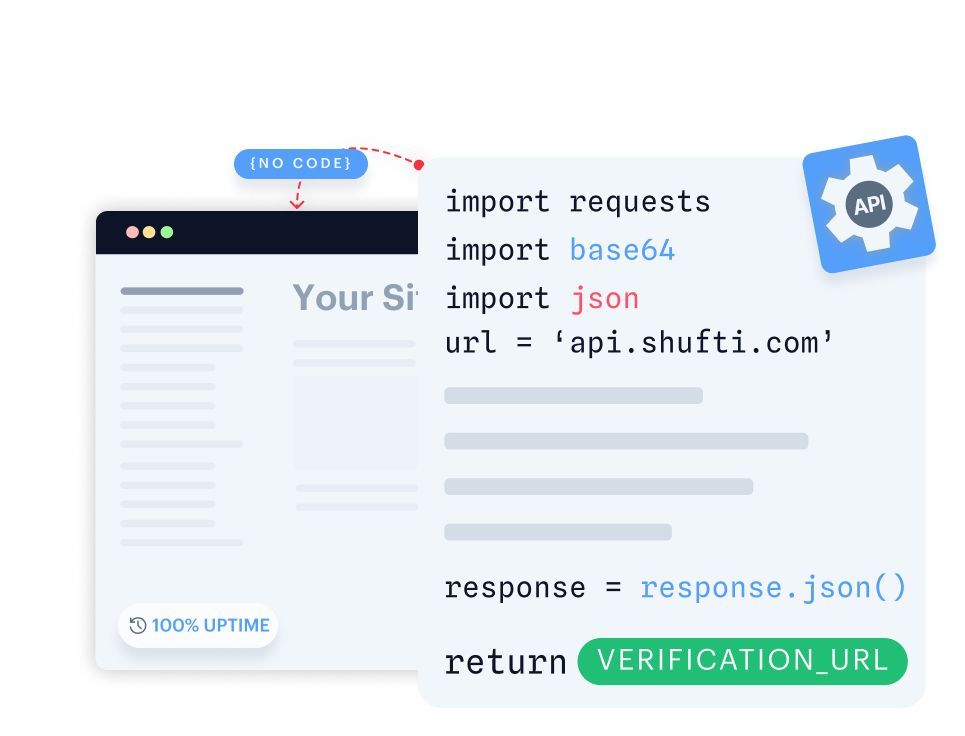
Single API, Seamless Integration
Build fully customisable verification flows with seamless backend integration.
- Gain full control by customising verification flows end-to-end.
- Integrate seamlessly with your backend for quick implementation.
- Design flexible verification journeys tailored to your users.
Launch a native verification experience in your mobile app within minutes.
- Launch native verification within minutes on iOS or Android.
- Use ready-made UI with camera, capture, and real-time feedback.
- Customise flows to fit seamlessly into your mobile app.

Run Shufti within your own identical-capability infrastructure for maximum data control and privacy.
- Keep all sensitive information in-house to meet strict governance and data residency requirements.
- Keep sensitive information fully private and secure in-house.
- Deploy in highly regulated sectors without compromising compliance.
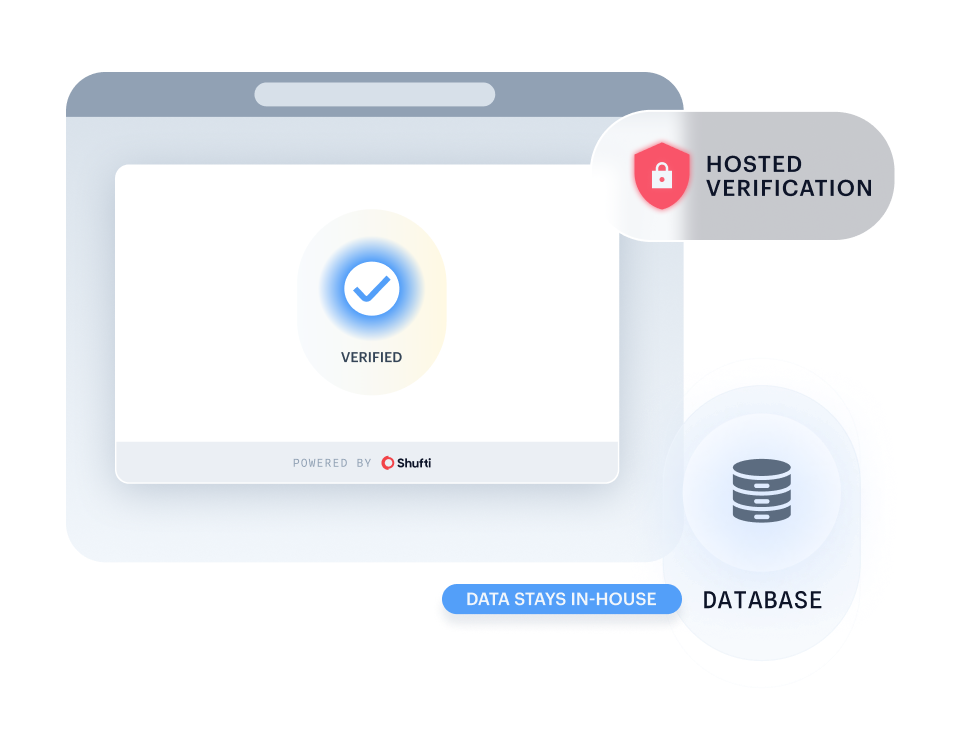
Quickly launch identity verification through a secure, customisable web link, no code required. Learn more.
- Start verifying users instantly with a no-code setup.
- Deliver a consistent identity experience via a link or embedded iframe.
- Deploy quickly via a secure link or embedded iframe.

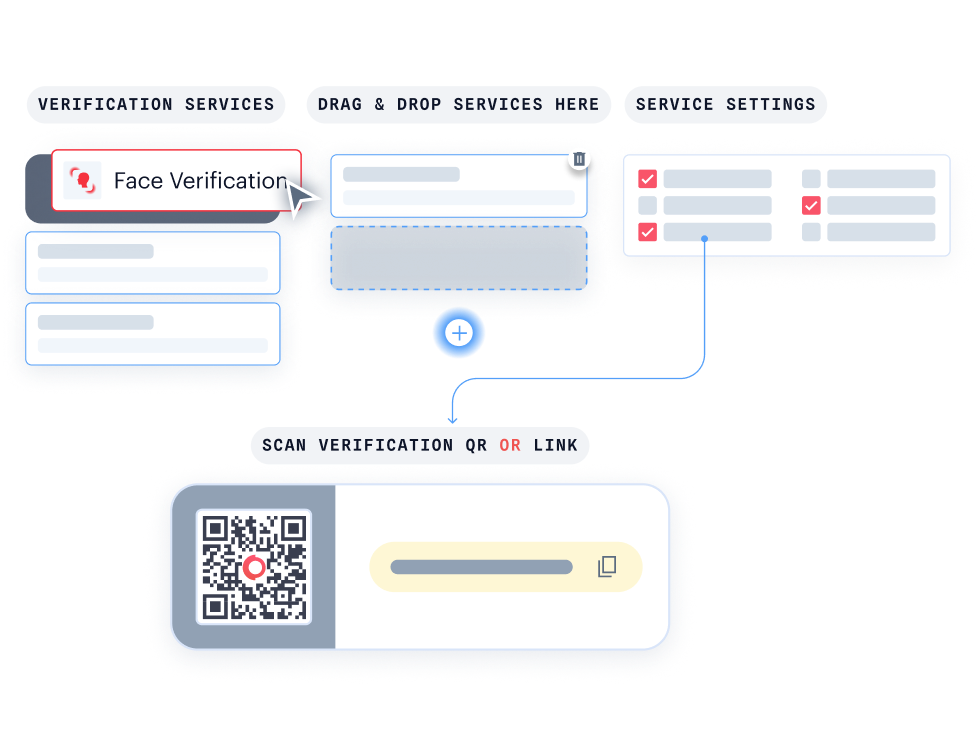
With KYC Journey Builder, create personalised verification journeys without writing a single line of code.
- Customise your journey effortlessly with drag-and-drop functionality.
- Instantly see how your verification flow looks for your users.
- Easily connect with Hosted Verification for a consistent, branded experience.
Where AI Face Verification Fits Best
Built For Regulated & High-Risk Businesses
Trusted Sellers, Repeat Fraud Blocked
Verify the seller is real at onboarding, then prevent re-joins with duplicate detection and optional 1:N matching across the marketplace.

Don't just take our word for it, hear from our customers
The Confidence Our Clients Share
The future of digital identity is defined by trust, interoperability, and regulatory alignment, so our partnership with Shufti reinforces DevCode Identity's commitment to supporting our global customers with the most secure, best-in-class, complaints identity verification solutions available today.
Combining our Conversion Driven Compliance Orchestration Platform with Shufti's global KYC and IDV capabilities allows our customers not only to navigate complex regulatory demands but also to maintain a seamless customer onboarding experience with the highest achievable conversion rates.
Shufti gives us verification journeys we can trust across every market we serve. The ability to route players through passive database checks, eID authentication, and full biometric liveness — all behind one API — has reshaped how we think about onboarding compliance.
Their team acts like an extension of ours. When regulators added new requirements across two European markets, Shufti’s journey builder let us adapt in days, not months.
FXBO customers demand speed without compromising AML rigour. Shufti’s eIDV fits exactly there — high-assurance verification for large deposits, invisible background checks for everything else, and one compliance trail across the board.
Integration took a single sprint. The SDK handled the full journey, so our product team stayed focused on trading features instead of building KYC screens.
As a regulated European payments platform, we need identity verification that meets eIDAS 2.0 and AMLD6 without multi-vendor stitching. Shufti delivers both — native eID authentication for high-assurance markets and docless database checks where eIDs don’t reach.
One contract, one audit log. That changes the compliance conversation entirely.
Everything you need to know in one place
Frequently Asked Questions
Is face verification only for onboarding with an ID?
No. Use it anywhere fraud shows up, login challenges, account recovery, withdrawals, payouts, and resets. It can also match to an ID photo when required.
How does face verification detect deepfakes?
Face verification systems apply multiple detection layers. Shufti uses RGB colour-space analysis combined with DCT frequency-domain decomposition to identify synthetic artefacts in the captured image. This detects AI-generated faces, digitally manipulated photos, and injected data streams that bypass the camera.
What levels of iBeta liveness certification does Shufti provide?
Shufti provides iBeta-certified liveness detection across Level 1, Level 2, and Level 3 testing. These levels assess presentation attack detection against increasingly advanced spoofing attempts, from basic printed attacks to higher-quality replays, masks, and more sophisticated presentation attacks.
Can historic KYC selfies be rescanned for deepfakes?
Yes. Shufti's retrospective deepfake audit tool, available through AWS Marketplace, rescans biometric records collected during previous onboarding against current-generation deepfake detection models. This identifies selfies that passed verification at the time but would fail under today's detection standards.
What happens when a user wears glasses, a headscarf, or has a facial difference?
The 68-landmark facial mapping and 3D depth reconstruction are designed to work across a range of facial presentations. iBeta Level 2 testing includes demographic diversity requirements.
Prove the Person Is Real Before Risk Moves Forward
Stop deepfakes, presentation attack defence, masks, and injected video streams with 3D face verification built for regulated onboarding and high-risk user actions.





