Healthcare Industry and Prevailing Crimes – What Shufti Can Offer

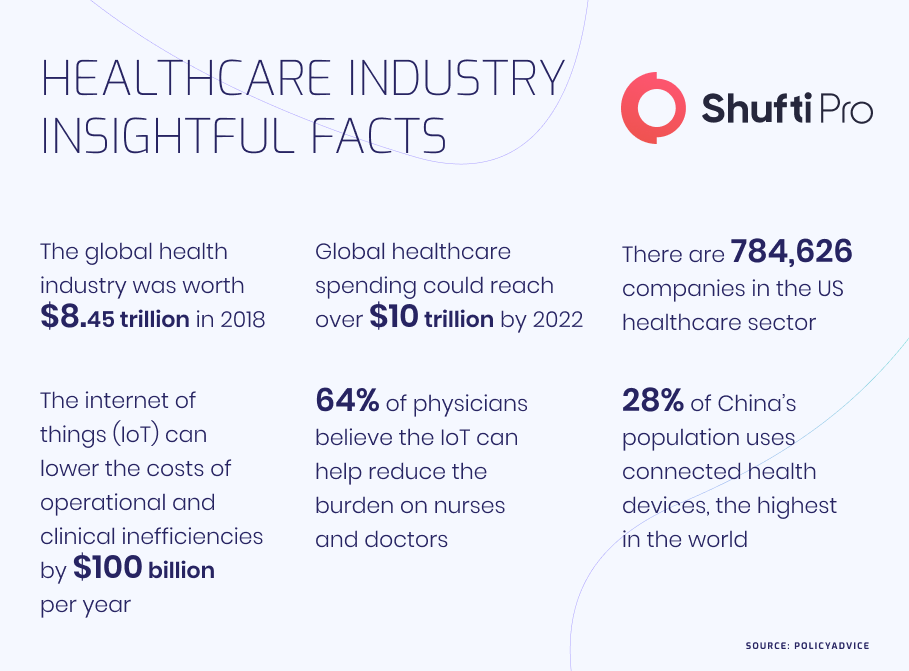
Over the recent years, the medicare industry has completely transformed, and emerging innovations have changed the way the sector operated. Whereas, global digitization has driven various trends including telemedicine which has solidified its place as a sustainable healthcare model as it is more convenient for patients to seek service virtually. Thus, around $4 trillion is spent to enhance medicare operations in the US, while it’s projected that the spending growth will increase by 5% by 2028. Similarly, almost $200 billion is invested in the US medical smart device market which is also expected to grow at the same pace. As the pandemic has reshaped the way of business operations, patients continue to demand more control and transparency in the medicare system, customized care is becoming the new norm.
Therefore, to meet the patients’ demands, the businesses are making efforts to push forward with digital transformation. On another hand, the integration of new technologies is also providing opportunities for criminals to exploit virtual services. Crimes including patient identity theft, data breaches, false insurance claims and much more, are putting both healthcare businesses as well as patients at stake. Thus, to secure operation regulatory authorities have come up with regulations like HIPAA, GDPR, HITECH and Know Your Patient (KYP).
Overview of the Healthcare industry – Still Remains a Prime Target for Cyberattacks
The global medicare industry is continually evolving, while businesses are making efforts to fight emerging challenges presented by the coronavirus pandemic as well as cyberattacks. The health sector is making healthy efforts to increase the patient experience while reshaping operational activities and swiftly expanding virtual medicare services for patients. However, at the same time, they continue to address the significance of healthcare, the environment, sustainability and emerging crimes that patients need to watch for.
To date, many cases have been reported regarding medicare scams. An incident response company BreachQuest has published a report that has highlighted the techniques and risk of crime that the healthcare industry is prone to. Criminals are getting smarter and using technology-driven tools as well as variants of malware viruses against health businesses to get their hands on databases. However, based on the challenges identified in healthcare, data hacking is among the top occurrences as the medicare data is so valuable that it can be used by cybercriminals to manipulate systems. Although ransomware attacks are also among the critical challenges that healthcare is trying to fight with. Thus, sixty per cent of ransomware attacks have occurred within the US market only. The number is projected to rise in the coming years as the sensitive information placed in medical databases is valuable and can be sold over the dark web or held hostage in case ransom is not paid. In addition to this, healthcare businesses are also under stress to maintain the optimum level of data privacy and patient integrity.
However, it is forecasted that the problems faced with zero-day attacks, stolen finances, data breaches and other crimes will continue to increase the challenges for healthcare businesses. Whereas, to safeguard this industry, regulatory authorities and businesses need to work together to come up with solutions including identity verification systems along with regulations or guidance to put a stop to criminal activities.
SuperCare Health Faces Lawsuit for Having “Incompetent Security Measures” to Stop Data Breach
Plaintiff filed a lawsuit against SuperCare Health as the company was alleged to have “incompetent security measures” to prevent data breaches. This lawsuit was filed in the wake of the July 2021 data breach. According to the reports, the healthcare firm’s 318,379 records were compromised making it one of the biggest data breach incidents reported in 2022. As per the firm’s briefings, the fraudsters accessed the company’s database without legal authorization between the dates July 23 and 27. In this attack, the cybercriminals got their hands on the Personally Identifiable Information (PII) including patient names, insurance data, addresses, medical record numbers, date of birth, account numbers, insurance claim numbers, treatment data and healthcare groups information.
In addition to this, specifically, the US Central District of California alleged that SuperCare for failure to determine as well as preventing the data breach and integrating effective cybersecurity measures, “despite the fact that data breach attacks against medical systems and healthcare providers are at an all-time high.”
“Upon information and belief, the mechanism of the cyberattack and potential for improper disclosure of Plaintiff’s and Class Members’ Private Information was a known risk to Defendant, through frequent news reports and FBI warnings to the healthcare industry, and thus it was on notice that failing to take steps necessary to secure the Private Information from those risks left the property in a dangerous and vulnerable condition,” the filing stated.
2 Million Patients Affected by Shields Health Care Group Cyberattack
In a recent cyberattack on Shields Health Care Group, personally identifiable health records of nearly 2 million victims have been compromised. It’s a Massachusetts-based company that provides ambulatory surgical centre management as well as medical imaging services across England. On March 28, 2022, suspicious activity was identified within the firm’s network. However, immediate actions were taken to safeguard the network to reduce the risk of further unauthorized access to the company’s sensitive databases. The investigations concluded that cybercriminals access the Shields systems between March 7, 2022, to March 21, 2022. The company said that a security alert occurred on March 18, 2022, but it didn’t appear to be a data breach. Furthermore, the company also said that there are yet no cases of attempted misuse of patient data.
Regulations for Securing Healthcare Industry
Both the medicare businesses and regulatory bodies are well aware of criminal activities that are becoming the major reason for putting patients along with service providers at stake. Such things include false insurance claims, free medical services, data breaches and patient data theft. Due to these reasons, regulatory authorities are working closely with the healthcare businesses to get to know their problems along with legislating compliance to secure the operations.
Let’s dive into the some of the regulations for safeguarding medicare businesses;
HIPAA Privacy Rule
The Health Insurance Portability and Accountability Act (HIPAA) Rule establishes national standards to safeguard citizens’ medical information and other personally identifiable information. It also applies to the medicare service providers that provide healthcare through digital transactions. Under this law, the businesses need to have secure systems or measures to safeguard the privacy of patients and set the limit as well as conditions on the usage of data. Specifically, no records are to be used without the patient’s consent. The HIPPA Act also gives citizens rights over their information, including the right to examine and get a copy of their medical records.
21st Century Cures Act
The 21st Century Cures Act aims to enhance the flow and exchange of electronic health data records. The office of the National Coordinator for Health Information Technology (ONC) is responsible for implementing part of Title IV, delivery, related to advancing interoperability, prohibiting information blocking, and enhancing the usability, accessibility, privacy and security of health IT. The department also ensures that the patients and their families have appropriate access to electronic health data records. Additionally, this act also supports medical research, enhancing interoperability, clarifying HIPAA privacy rules, along with supporting substance abuse, the Cures Act defines interoperability as the ability to exchange as well as use electronic health records.
How Shufti Can Help
Shufti’s all-in-all identity verification service is the optimum solution for healthcare service providers. Integrating Shufti’s IDV powered by thousands of AI models can assist to determine the true identities of patients before getting them onboard with 98.67% in less than a second. In addition to this, businesses can also stay put with the ever-evolving regulatory regime to reduce the risk of hefty fines and sanctions.
Want to know more about robust identity verification services?

 Explore Now
Explore Now