Risk Assessment and Management | Why do Businesses need it?

B2B partnership always carries risks that must be managed whilst staying compliant. Business partners, retailers, and other parties play critical roles in daily operations, helping the company achieve its objectives. However, this procedure now includes business risk assessment in today’s landscape. Although it is sometimes regarded as a hindrance to business, it is critical for assuring security because each new customer increases the possible attack surface.
The only way to thoroughly assess an organisation’s risk is to evaluate and validate them using effective security controls as well as risk managing processes. This assessment offers informed decision-making about the appropriate level of risk and the mitigation measures required to keep fraudsters at bay. A practical risk assessment explores real-world threats and the particular controls an institution employs to limit their impact, allowing management as well as the board to make more informed decisions before the risk increases.
What is Risk Assessment?
A risk assessment is a systematic process of detecting and analysing potential threats associated with the business, followed by implementing feasible control measures to eliminate or decrease them. Preventing identity fraud is critical for the digital sector, and now is the best time for businesses to invest in risk screening procedures. The risk assessment is an excellent solution for businesses, assisting them in combating financial criminals whilst staying compliant.
Key Insights into Risk Factors
A business might encounter a variety of risks, and being prepared will always offer them an advantage over their competition, especially when something unexpected happens.
Customer Risk
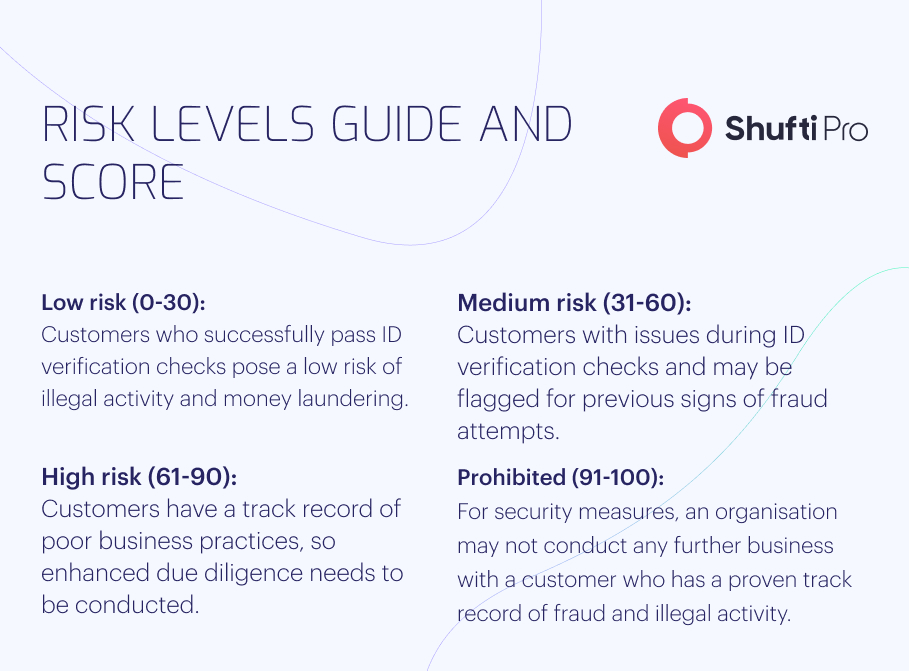
Customer risk assessment is a step conducted during client onboarding that refers to extensively analysing the potential risk that a new customer poses. Businesses can create risk profiles based on risk levels by analysing consumer information and taking the required precautions to protect business operations. Customer risk levels help businesses in determining the likelihood of committing illicit crimes, including terrorist financing and money laundering. On the contrary, if regulatory authorities uncover suspected customer behaviour, the firm may be penalised with substantial fines, resulting in reputational damage and permanent exit from the corporate world.
Geographical Risk
There are few countries in the world with lax AML and other cyber rules, allowing criminals to commit crimes without fear of regulation, facing minimal difficulty. FATF has placed many nations on grey or black lists, indicating they are all vulnerable to financial fraud. The risk assessment procedure examines the clients’ origins and determines how strict AML regulations are. It detects not only businesses (or related individuals) from high-risk nations but also device locations, online proxies, and private web browsers.
Business Risk
The risk screening verifies the users’ businesses and thoroughly inquires if the client participates in risky activities. The risk is analysed, tracked, and reported, ensuring that businesses connect with low-risk parties and are monitored in the future.
Why do Businesses need Risk Assessment?
Before a company can analyse or reduce business risk, it must identify potential threats and risks to its bottom line. Risk management methods grow and mature with time, but some fundamental principles remain consistent.
Risks in business come in different forms and sizes. This means that an efficient risk assessment must be adaptive to or built explicitly for certain risks. A company should bundle similar risks into related analytic procedures whenever possible.
A corporation should ideally allocate capital depending on risk, as determined by a cost-benefit evaluation. Every risk identification approach should result in effective evaluation, and each review should contribute to corporate governance.

Fighting Fraud Through Risk Assessment
Risk assessment is a collection of severe measures organisations commonly employ to verify the legitimacy of their clients when establishing a new professional relationship. B2B enterprises use risk screening methods to validate the documents and identities of other companies before entering into contracts with them. It is an appropriate technique for all digital service providers because it gives detailed information about the other party and keeps a record of it. Risk assessment is not only a viable answer to identity theft but also a significant instrument in the fight against financial crimes like terrorist financing and money laundering.
Although various identity verification systems are effective enough to stop criminals, risk assessment is more complex and advanced, offering businesses the best verification choices. It includes a variety of security checks, such as verifying identities, backgrounds, places of origin, businesses, and criminal records. All of these characteristics have shown to be effective in combating cybercriminals and assisting numerous organisations in complying with worldwide legislation.
Onboard Legit Partners and Clients with Risk Assessment
Risk assessment service is essential to client onboarding since it allows organisations to detect and minimise fraudulent behaviour. Without a proper risk assessment plan, there will always be an elevated risk of working with organisations and individuals that are prone to future fraudulent attempts. Further verification of new clients against sanction lists is critical in reducing the likelihood of future financial offences.
However, risk assessment should not be confined to the onboarding process. In reality, monitoring clients who engage in activities that differ from their risk profiles should be an ongoing risk monitoring and management process. For example, if a client or partner suddenly shifts to transactions involving large sums of cash, avoid bank transfers for transactions or transfer funds through offshore organisations. This could be a warning sign that firms should be on the lookout for heading fraud.
Business Risk Analysis – The Processes of Ensuring Secure Operations
A cutting-edge financial risk assessment method involves a strict set of principles or protocols for evaluating, assessing, and mitigating risks that a firm may encounter in the future. Here are five phases that a business’s financial risk assessment approach must include.
Identify the Risk
Each corporation faces distinct types of risk depending on its cash flow, location, industry, and reserves. The business’s finance or regulatory department should know the risks it will likely face. However, if an unknown scenario or possible risk is recognised, the executive members must begin a risk assessment service to determine the amount of risk.
Assess and Document the Risk
A firm’s major purpose of risk assessment should be to determine the worst-case scenario, the possibility of that scenario occurring, and the method required to recover from the possible financial loss.
Efficient Management Steps
When a business requires risk management procedures, efficient personnel should be on standby to manage and look after the risk-handling operation. A skilled and informed risk assessment manager will improve transparency and interdepartmental collaboration.
Use Strict Measures
If a company has a strict risk management system in effect, taking measures against a client or partner who commits fraud will be quite simple. When a risk is flagged for a financial crime like terrorist financing or money laundering, transaction habits and fund sources are identified, and risk analysts can spot such suspicious behaviours before the crime is committed.
Monitor Progress
When the risk assessment and management procedure is finished, deploy a team to track the business’ ongoing activity. Nevertheless, if the risk is reduced, ongoing evaluations will guarantee that additional factors do not increase the risk caused by the original circumstance.
Triggers for Risk Assessment
To combat the money laundering risk successfully, businesses must analyse their clients frequently, recognising that what appears obnoxious to one client may not be to another. Certain generic behaviours can cause concern or prompt a reevaluation of client risk:
- Changing banks several times
- Attempts to hide the true owner of a company
- Requests for accelerated or unusual transaction processing
- Participation of unconnected third-party donors in the industry
- Using forged or suspected documents
- Financial transactions of huge amounts of cash are out of pattern for the customer.
- Countries’ business transactions have a high risk of laundering funds and terrorist financing
- Overly complicated ownership structures
- Unpredictable amount of commercial activity
Firms must improve their ability to detect suspicious clients and actions. This necessitates an extensive understanding of the need for continuous risk assessments and the use of data and technology to support these attempts.
Misclassifying low-risk clients as high-risk and collecting incorrect or incomplete Know Your Customer (KYC) information can reduce the impact of AML security measures. Relying only on tedious and intricate processes might yield a different result.
Businesses should streamline risk models and incorporate statistical evaluation for expert judgement. Data quality can be enhanced by using artificial intelligence and machine learning algorithms. In streamlined risk models, customer profiles can be regularly updated whilst considering behavioural patterns and other pertinent factors.
Risk Assessment with Shufti
Adherence to KYC & AML regulations is a daunting task. The market dynamics are rapidly changing, so staying ahead of them requires time, effort, strategy, and a move in the correct direction.
However, businesses recognise that keeping up with the speed of ever-changing fraud risk is difficult. That is where Shufti’s risk assessment solution comes in, assisting businesses in adhering to industry standards.
Our risk assessment solution enables organisations to test everyone, ensuring that each client onboard goes through a complete risk assessment process. Both individuals and corporations are screened against 1,700+ watchlists to minimise the risk and threat of being compromised. For businesses, it is essential to assess the risk to protect their finances and reputation.
Finding it hard to assess risk, secure business operations, and meet compliance?












