Simplify Payment Processes with Biometric Authentication

- 01 The History of Biometrics in Payment Processing
- 02 What is Biometric Payment?
- 03 Biometrics: An Edge in Payments Security
- 04 How are Biometrics Changing the Payment Service Industry?
- 05 How does Biometric Authentication Payment Work?
- 06 The Future of Biometric Authentication and Payment Processing
- 07 Biometric Authentication in Payment Processing with Shufti
A developing trend that is altering how customers handle their money is the use of biometric authentication in debit cards and payment processing. Utilising a person’s distinctive physical characteristics, such as voice, facial, or fingerprint identification, to confirm their identity is known as biometric authentication.
According to reports, online payment theft costs the global e-commerce industry $48 billion in 2023 compared to $41 billion in 2022. Firms in their early stages may not find online fraud a significant concern. But, when companies expand, they must take into account the amount of daily transactions they get. Ensuring the effective security of such transactions must be the business’s top responsibility. Explore the use of biometrics in payments and its history, work processes, and future.
The History of Biometrics in Payment Processing
The origins of biometrics can be found in the ancient societies that identified people by their physical characteristics, such as handprints and facial features. But in the modern era, fingerprint authentication became the most popular biometric technology in the 20th century for verification purposes.
Since the early 2000s, payment systems have made use of biometrics. To offer safe and practical payment services, government initiatives and financial institutions were the main users of biometric payment systems at first.
The first biometric payment system was introduced in 2002. Consumers would only need to place their finger on a scanner at the checkout counter to begin utilising the system, which requires them to first provide their fingerprint.
Mobile payment systems have recently gained popularity, and many now use biometrics. For instance, Apple Pay, which existed in 2014, authenticates payments using the Touch ID and Face ID biometric technology on Apple products. Similarly, biometric authentication is available through Google Pay and Samsung Pay.
What is Biometric Payment?
With the help of cutting-edge digital transaction technologies like fingerprint, face, or iris scanning, customers can now successfully complete transactions using biometric payment.
Users no longer have to provide their bank details each time they make a purchase owing it to the method of payment. Rather, biometric payment verifies authenticity using distinct bodily identifiers like fingerprints or face recognition information. The authentication and transaction are then safely processed by the system in a single, smooth step.
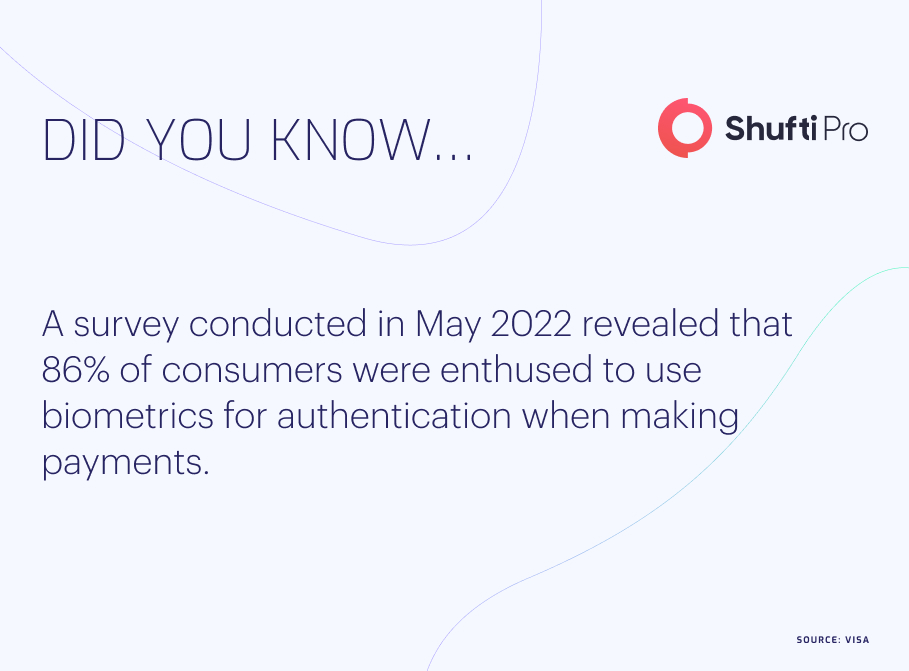
Because biometric payment technology removes the need for consumers to memorise complex usernames and passwords, it is growing in popularity. Additionally, because each person’s biometric data is unique, it offers a more secure method of making payments.
Biometrics: An Edge in Payments Security
Currently, there are a few biometric payment options for confirming e-commerce transactions and payment service provider identities:
- Digital fingerprinting is a technique that scans a user’s fingerprints digitally; a print mapping is preserved, and the original image is deleted.
- Rather than saving the user’s actual photo, facial recognition technology maps dozens of distinct spots on the user’s face to produce a unique impression of the person. This technology functions similarly to digital fingerprinting.
- A pre-recorded sample is compared to the user’s speech pattern through voice recognition. Although voice isn’t always as unique as a fingerprint or facial shape, it does have some benefits over other techniques, such as being less expensive and less invasive.
- Iris identification uses the irregular pattern of the human iris to help identify distinct people, much like our individual fingerprints. Like a fingerprint, this technology can map eyes at close range using the cameras found on the majority of contemporary smartphones.
- A palm vein scan maps the distinct vein structures in the palm using infrared light and then encrypts the data points. Palm mapping is still somewhat new and not very common. But with the recent advancements in iOS and Android application development, this will probably change.
How are Biometrics Changing the Payment Service Industry?
The emergence of biometric authentication is being fueled by several causes, such as the arrival of 5G, which will offer businesses and consumers greater speed than ever before, and the widespread use of mobile devices on a large scale. Future developments in biometric authentication will probably come from increased use and ongoing technical advancements rather than from a single, stand-alone hardware update. This technical breakthrough would benefit not only the financial industry but also payment service providers, eCommerce merchants, supply chains, international trade, and other industries.
How does Biometric Authentication Payment Work?
Integrating the aforementioned technologies, biometric payment offers users a simple, secure, and safe way to make digital payments. This is how the payment process works when biometrics are used:
Step 1: Verification of Identity
To confirm the user’s identity, biometric authentication must occur before money is handled. To verify their identity, this usually entails detecting their iris, face, or fingerprint. Initially, the user applies the chosen verification technique that the organisation has incorporated. The user will use their thumb, index finger, or any other fingerprint for the process, for example, if the digital fingerprinting method is used.
Step 2: Processing
The user’s biometric is scanned, and it is then compared to the previously saved database. In order to ensure that no fraudster got past the security, authority, and legitimacy are examined for additional assessment. This procedure entails authenticating the transaction with the appropriate payment processor and confirming the user’s payment credentials.
Step 3: Permission
The payment is executed after the biometric data has been confirmed. The transaction is then finalised once the payment processor authorises it.
Biometric payments provide users a safe and easy way to make digital payments by fusing biometric technology with processing and authorisation.
The Future of Biometric Authentication and Payment Processing
Consumers will gain from biometrics in a manner that many may not have anticipated in the future. Every year, businesses lose huge sums of money due to fraud, which negatively impacts profitability and ultimately impacts customers by raising the cost of services and goods.
Smart device users are probably aware of the evolution of biometric authentication in the last few years, from fingerprints to face ID check and beyond. Businesses can increase their profitability and consumers can benefit from more affordable, higher-quality items thanks to biometrics’ increased ability to prevent fraud. Authentication with biometrics can help create this promising future.
As consumers continue to input more data into their devices, such as health information like blood pressure, for example, this will grow more advanced in the coming years. Individualised multi-factor authentication patterns will be enhanced with the use of this data.
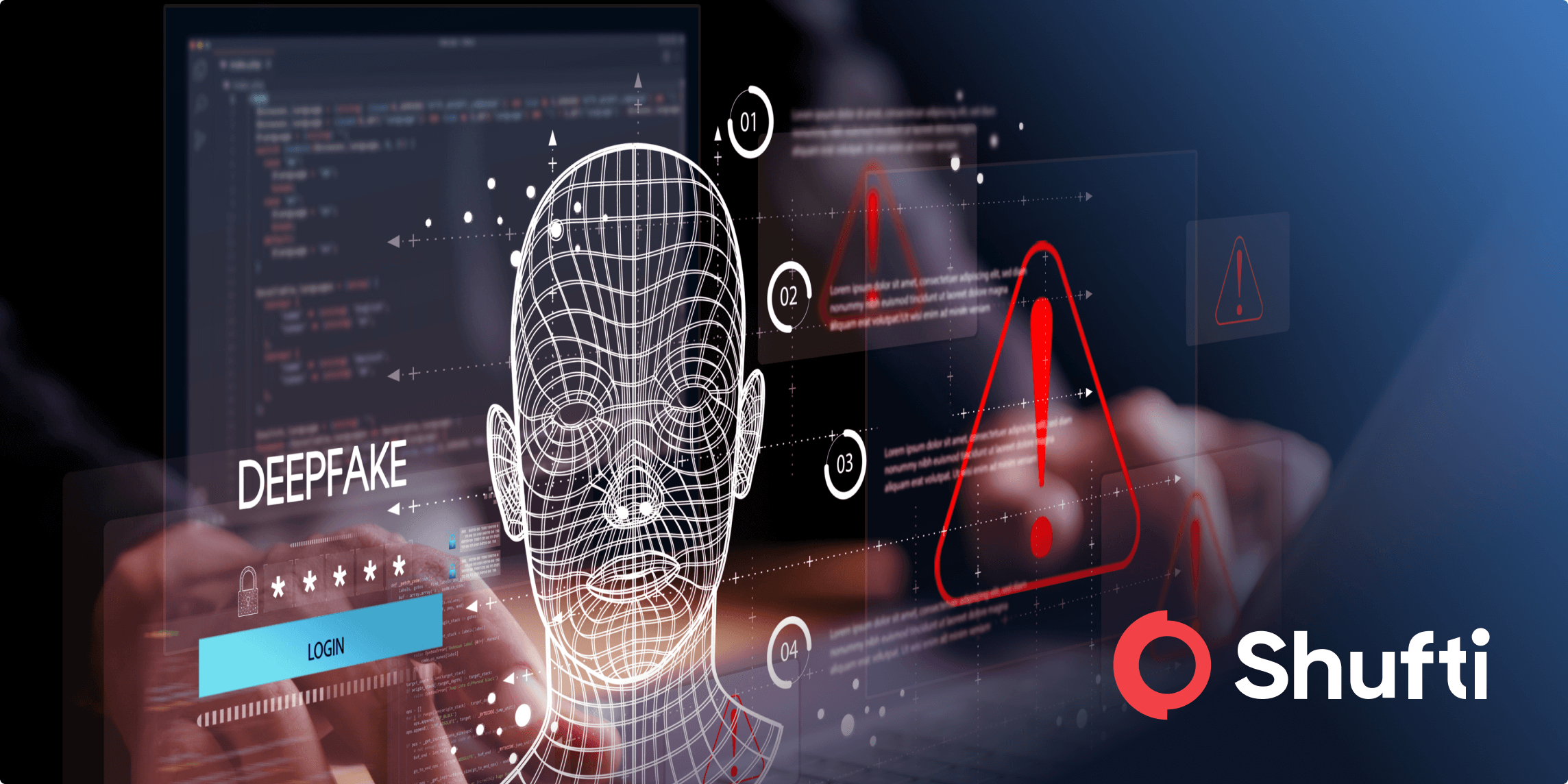
Businesses constantly challenge these advancements because they might provide far greater security for customers. More than ever, the need for this is because new technologies are changing the fraud scene.
For instance, early biometrics can now be defeated by Artificial Intelligence (AI), which enables attackers to mimic people’s voices and faces. Businesses must combine various biometric patterns and solutions to provide the next degree of security in response to this ever-evolving threat. This will prevent fraud and give customers a safe and reliable payment experience.
Biometric Authentication in Payment Processing with Shufti
Shufti uses state-of-the-art biometric technologies to transform digital security. Our cutting-edge biometric authentication services, which include fingerprint and face recognition, guarantee the best possible defence against fraud and unauthorised access. With features like the “selfie login,” we put the convenience of our users first, streamlining the login procedure and improving the payment processing industry’s overall user experience.
Shufti leads the way in contemporary biometric security solutions by thwarting spoofing, and impersonation attempts and offering a safe and easy user experience for cross-border payment services and payment processing. Organisations can safely protect systems and critical data with Shufti whilst still providing a simple, hassle-free user experience. Our dual emphasis on security and usability establishes it as a reliable partner in the ongoing fight against fraud and threats.
Still, confused about which biometric authentication is suitable for your business that provides complete security whilst maintaining compliance?