What is SCA? Strong Customer Authentication Explained
In Europe, new customer authentication requirements for online payments were introduced on September 14, 2019. These requirements were part of the Second Payment Service Directive (PSD2), which is expected to be enforced by 2021. As per news by SiliconCanals, the internet commerce of the EU is expected to grow to about 1 trillion dollars by 2022, and along with this, online fraud too.
According to the European Central Bank, every year, online fraud on the EU cards is estimated to be about €1.3 billion. The increasing incidence of online payment scams calls for stringent regulations in place that could help curb the fraud density.
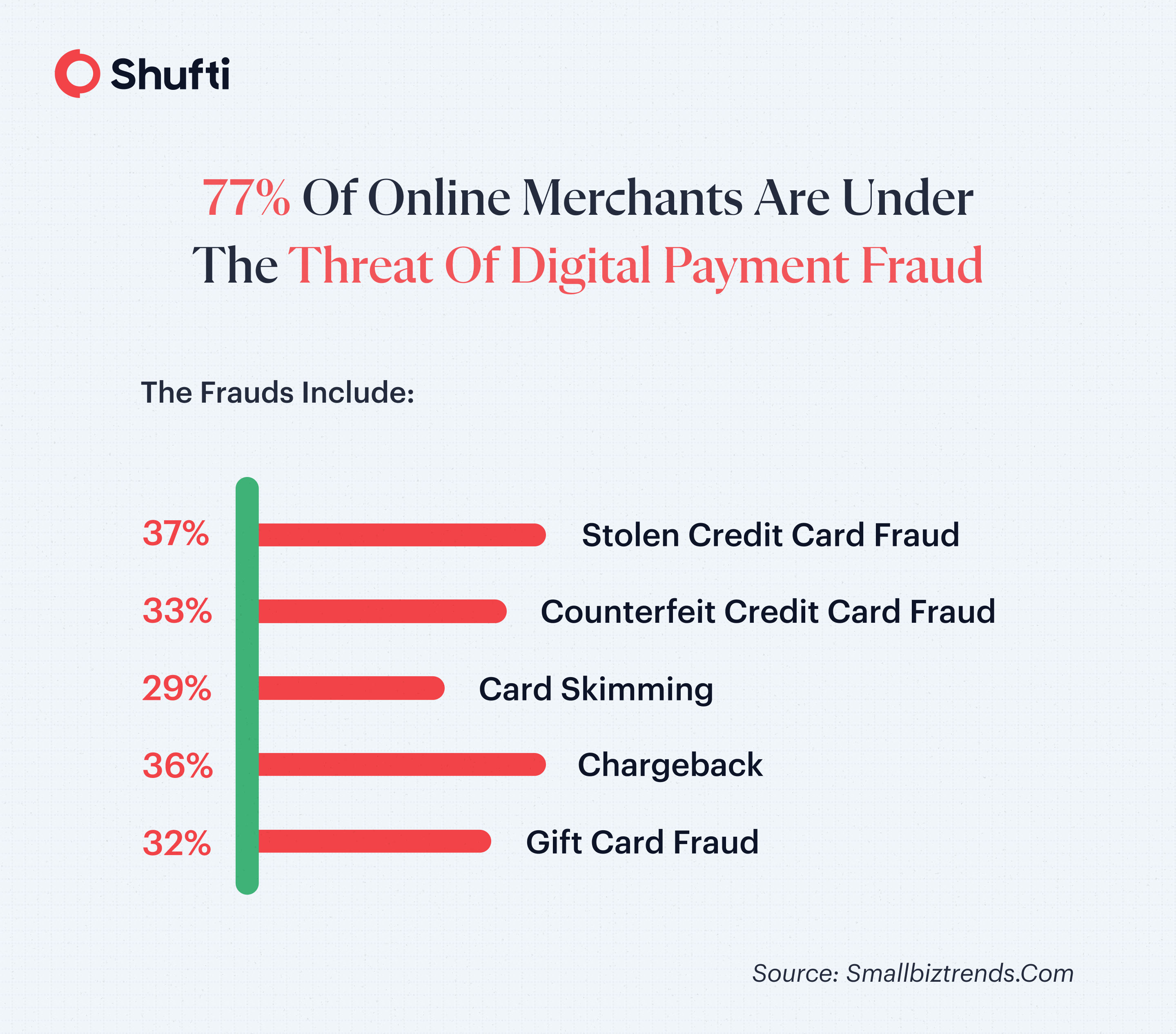
Digital payment scams and fraudulent transactions increase friction in the digital environment, which ultimately becomes the reason for the reduced number of online conversions. According to a survey, 77% of online merchants are under threat of digital payment fraud. This list of fraud includes stolen or counterfeit credit card fraud, card skimming fraud, false chargebacks, and gift card fraud.
Background of SCA:
The SCA full form is Strong Customer Authentication. It was introduced under PSD2 to strengthen security in electronic payments across the European Economic Area. The primary objective behind SCA in banking and digital payments was to reduce online fraud and enhance consumer trust in digital transactions.
With the rapid growth of e-commerce and remote banking services, regulators introduced secure customer authentication standards to ensure that electronic payments are verified using multi-factor authentication. These SCA requirements became mandatory for payment service providers to improve transaction security and ensure SCA Compliance across financial institutions.
What is SCA?
The SCA meaning refers to Strong Customer Authentication, a regulatory requirement that applies to customer-initiated online payments, including bank transfers and digital card transactions. The purpose of SCA is to provide stronger authentication in the checkout process regarding online payments and customer authentication.
Stronger Customer Authentication or SCA applies to customer-initiated online payments, which means that SCA covers all bank transfers and digital card payments. The purpose of SCA is to provide stronger authentication in the checkout process regarding online payments and customer authentication.
Elements of Strong Customer Authentication (SCA)
The SCA authentication process should include two of the following attributes (which are also known as two-factor authentication):
Knowledge: It corresponds to something that the user knows. For example, it could be the PIN, passwords, or any secret key required to access the account.
Possession: It is something that the customer has. For example, it could be a smartphone, a token, or a smart card.
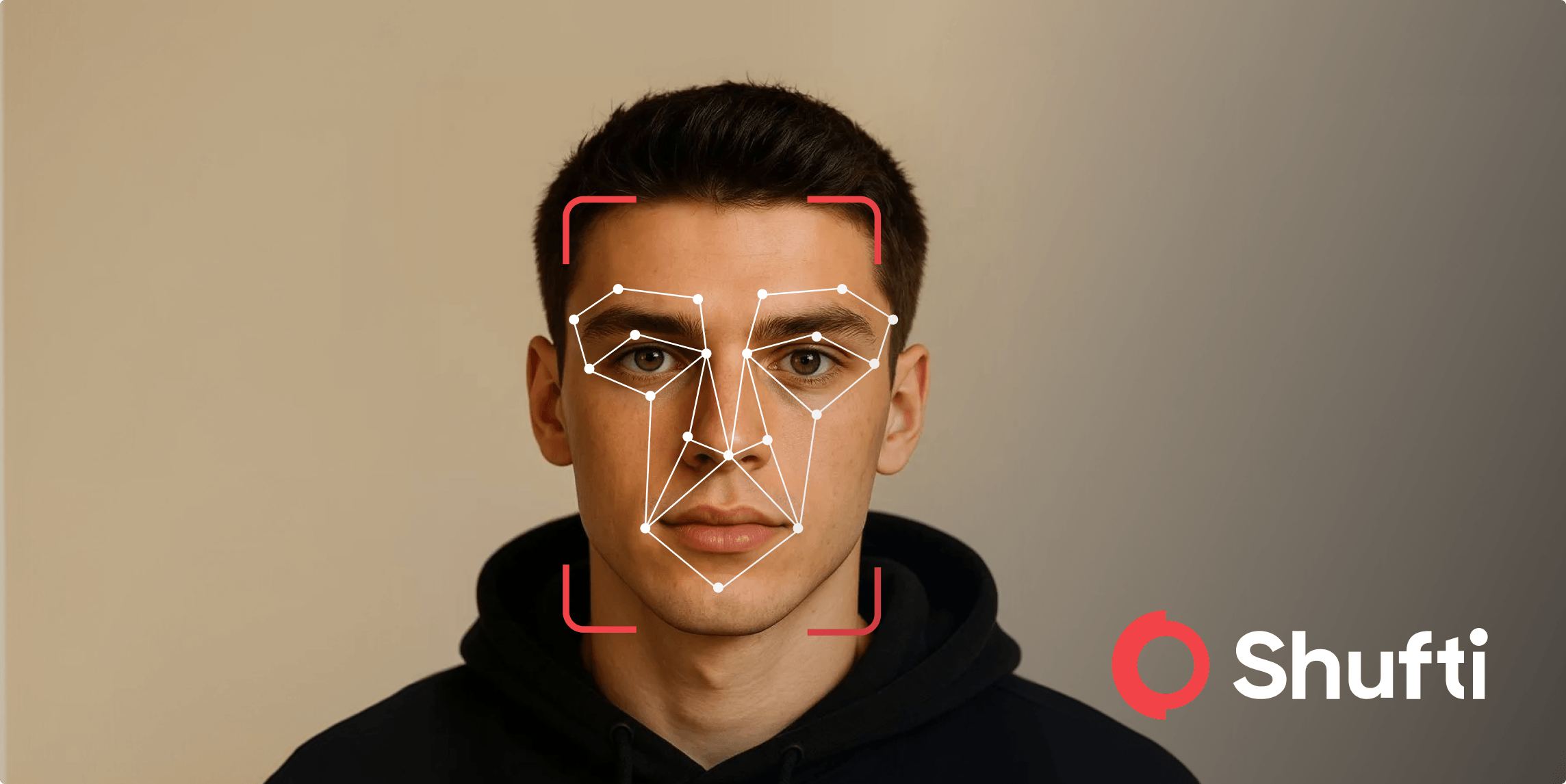
Inherence: It is something the customer is. For example, biometric elements such as face biometrics, voice patterns, fingerprints, etc.
Lack of authentication measures in place can increase the number of credit card fraud cases that come up with multiple facets.
To protect the online payments and transaction processes, it is crucially important for organizations to employ stronger authentication mechanisms as per the recommendations by EBA. It states that the person who is claiming to be some identity is actually the person to whom that particular identity was assigned. Thus, identity verification requires any of the two aforementioned elements for successful verification of an online identity.
Among these SCA elements, two are considered that question the user about what he knows and what he has. These two attributes correspond to the PIN, password, or 2-factor authentication that is based on SMS, which is sent to the mobile number of the user for verification purposes.
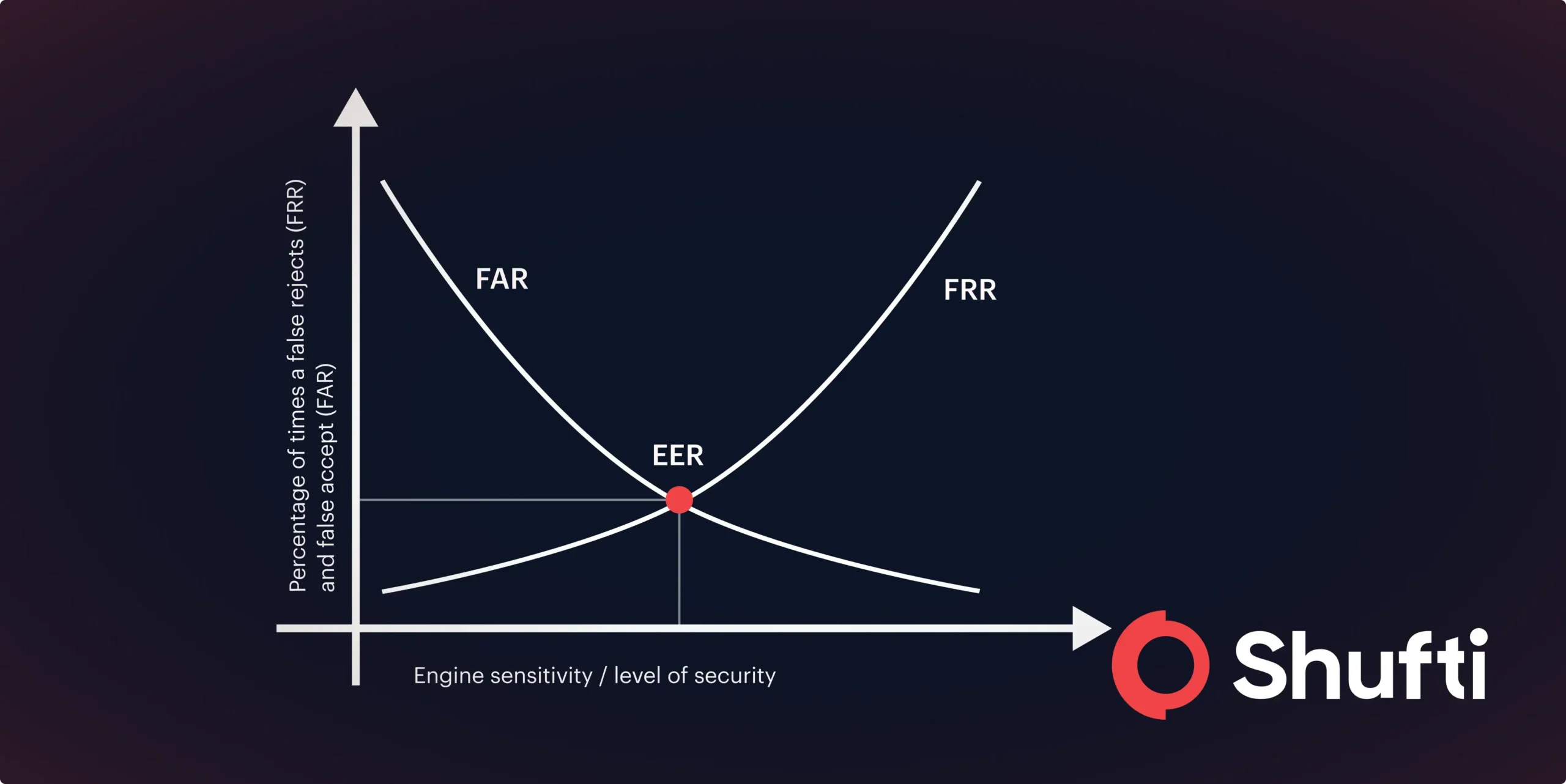
However, these methods are prone to cyberattacks, large-scale data breaches, and phishing scams, which can be mitigated by including another SCA attribute that is “who the customer is. With this, customer identification can be done through biometric verification that aligns with the need of verifying “the customer is who he claims to be”.
Accomplishing SCA through Biometric Verification
Biometric attributes such as fingerprints, face, iris/retina, voice, and similar unique biological traits are the strongest modalities of customer authentication. The increase of biometric technology on smartphones, thus, has made it possible to verify the online customers performing digital transactions.
Biometric authentication verifies the customers against their facial biometrics. The facial features are detected and verified against the information stored in the database previously at the time of account registration.
The biometric verification process ensures SCA while keeping intact the seamless customer experience and high online customer conversion rate. Biometrics eliminates the overhead of remembering PINs and passwords, provides high-end security over user accounts, and offers a robust authentication process.
Exemptions from SCA
Although SCA is mandatory in most electronic payment scenarios, certain sca exemptions apply to reduce customer friction while maintaining security.
Common SCA exemptions include:
- Low-value transactions below a defined threshold
- Recurring transactions with fixed amounts
- Transactions made to trusted beneficiaries
- Corporate payments through secure payment protocols
- Low-risk transactions identified through Transaction Risk Analysis (TRA)
These SCA exemptions are designed to balance security with customer convenience while still maintaining SCA Compliance standards.
Benefits of SCA
In this globally digitized world, there is a wide array of challenges, among which digital account security and customer experience are the primary ones. Strong customer authentication solutions provide the following benefits to help cope with them in an effective manner:
- Reduces the damage of fraudulent transactions
- Secures digital payment services
- Reduces the potential of online payment scams and frauds
- Ensure PSD2 compliance
- Increases the confidence of the cardholder in using online payment services
SCA requires advanced identity verification measures that could verify the identity of customers online in an efficient way, secure the digital payment services platforms against an array of digital frauds, and enable digital financial businesses to secure customer acquisition along with a high online customer conversion rate.
How Shufti Assists in Achieving Strong Customer Authentication?
Shufti helps businesses meet SCA requirements in a simple and reliable way. It verifies customer identities using document checks, face verification, and real-time identity validation to make sure the person making a transaction is genuine.
By combining biometric verification with multi-factor authentication, Shufti reduces fraud risks while keeping the user journey smooth and quick. The system works across onboarding, login, and payment stages, helping businesses stay compliant and protect digital transactions without adding unnecessary friction.
To see how it fits your business needs, request a demo or contact us for more details and integration support.
Frequently Asked Questions
What is Strong Customer Authentication (SCA) and how does it work?
Strong Customer Authentication (SCA) is a regulatory requirement under PSD2 that mandates multi-factor authentication for online payments to enhance security and reduce fraud. It requires customers to verify their identity using at least two independent methods, such as something you know, something you have, or something you are.
When is SCA Required?
SCA is required for most electronic payments, online card transactions, and remote banking activities within the European Economic Area, except in cases where specific SCA exemptions apply.
What are the Main Elements of SCA?
The main elements include knowledge (something the user knows), possession (something the user has), and inherence (something the user is). At least two of these factors must be used to meet SCA requirements.
Why is SCA required and how does it prevent fraud?
PSD2 mandates SCA to enhance payment security, protect consumers from fraud, and build trust in digital banking. Requiring multiple independent verification factors makes unauthorized transactions significantly harder, even if one factor is compromised.
How can payment gateways ensure SCA compliance?
Payment gateways can ensure SCA compliance by verifying multiple authentication factors, implementing real-time fraud monitoring, supporting 3D Secure 2, and keeping clear transaction logs for audits.
How AI Reduces SCA Friction in Online Payments?
AI helps streamline SCA by analyzing user behavior and risk in real time, allowing low-risk transactions to be approved with minimal interruptions while flagging suspicious activity for extra verification.
What are the Three Factors of Strong Customer Authentication?
SCA relies on three key factors: something you know (like a password), something you have (like a phone or card), and something you are (like a fingerprint or facial recognition).

 Explore Now
Explore Now