Identity verification solutions to fight against faces of fraud

In this digital world, billions of smart devices are circulating, connecting and communicating with each other regardless of their location. From online shopping to gaming, banking to investing, learning to teach and serving to digitize, smartphones are used. In 2019, a survey shows the number of smartphone users to be 3.2 billion, whereas users will increase up to 3.5 billion in 2020 and 3.8 billion by 2021. The reason being, pervasive access to the internet, world and its economy is changing drastically. Along with this, the expectations of online users are changing and the need for seamless customer experience and services is increasing.
Here, in the game, comes security. Security is a challenge for online businesses to balance simultaneously with customer experience.
Banking Industry, more specifically, online transactions and payment systems are prone to several cyberattacks. Bad actors that are facilitated through such platforms unknowingly are harmful. They misuse the system and perform malevolent activities. These activities vary from identity theft and account takeover attacks to severe ones such as money laundering and terrorist financing. Businesses need to take in place stringent measures such as while securing platform, customer experience is not compromised.
Innovations and Innovative Fraudsters – A Race
As technology is growing and solutions to real-world problems come onto the surface, they are secured using innovative measures. On the other hand, fraudsters are using similar technologies and hacks to fight against the security shields. It is an ongoing race. After the passage of time, businesses experience some major ruin and come up with a more stringent way of securing platforms that again are exploited by bad actors. Cybercriminals overwork and find out vulnerabilities in the system to launder money across the world, steal identity credentials of legitimate digital users or commit credit card fraud.
Marketplace fraud is increasing at an exponential rate, especially during online transactions. In peer to peer marketplaces, scammers create a product listing and scam buyers. Digital users’ personal and financial information is obtained through phishing attacks, malware injection and data breaches. With this information, customers create synthetic identities that seem real, misuse them in the online world. It is a challenge for the online marketplace to encounter these security issues keeping intact the customer experience.
One-stop Solution for Frauds – Identity Verification
Most of the online frauds and financial crimes take place as a result of uncontrolled access over confidential data. Whether it is a database, program section, online user account or organization’s confidential data store, the game starts when an unauthorized entity becomes part of the system. Identity verification is a one-stop solution that keeps online fraud miles away. Online identity verification ensures both security and enhanced user experience. In real-time, within seconds, an individual is identified and verified that helps businesses allow only honest traffic to make it part of their system.
Businesses have identified the need for identity verification into their system. The identity verification market that valued about 5.52 billion U.S. dollars in 2018 worldwide is expected to reach as per forecast to about 18.12 billion U.S. dollars by 2027. Moreover, being customer verification, a regulatory requirement in various sectors to deter the risks of financial crimes such as money laundering and terrorist financing, businesses are taking the verification process seriously.
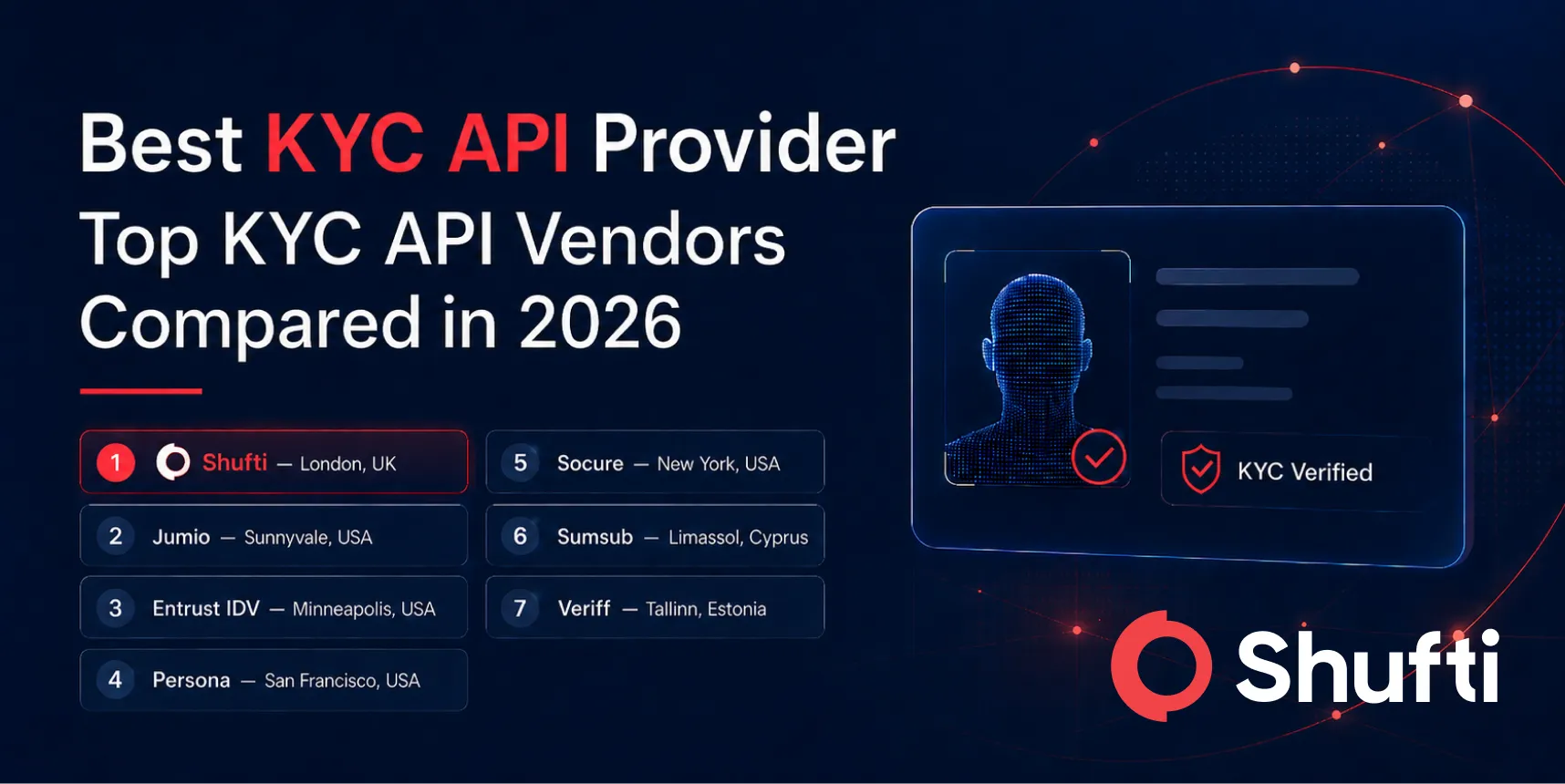
Identity verification covers both Know Your Customer (KYC) and Anti-money Laundering (AML) practices within an organization. While onboarding a customer, businesses can verify the identity of their customer to make sure that they are who they say are. This can be done at the time of account registration in which, other than identifying an individual, it is screened against various global watchlists and sanction lists. AML screening is performed to deter the risks of criminal entities from entering into the system.
In the identity verification process, these two terms are involved while actually implementing it. For instance, while conducting biometric authentication of an individual such as facial recognition, in the first step the facial features of an individual are identified and then they are matched with the features stored previously in the database in the form of a mathematical formula. If real-time captured features match with the one present in the database, identity is verified. The distinction between both these terms is important.
How does identity verification work?
The identity verification process involves three steps:
Collection of Information
In this first step, identity verification includes collection fo personal information from the user. Personal information includes name, address, date of birth, etc. All this information is collected at the time of account registration.
Ask the user to upload a picture
In the second step, the user is asked to upload a supporting piece of evidence in the form of the official document as an identity proof. The document could be
- ID card
- Passport
- Driving license
- Credit/debit card
Information Verification
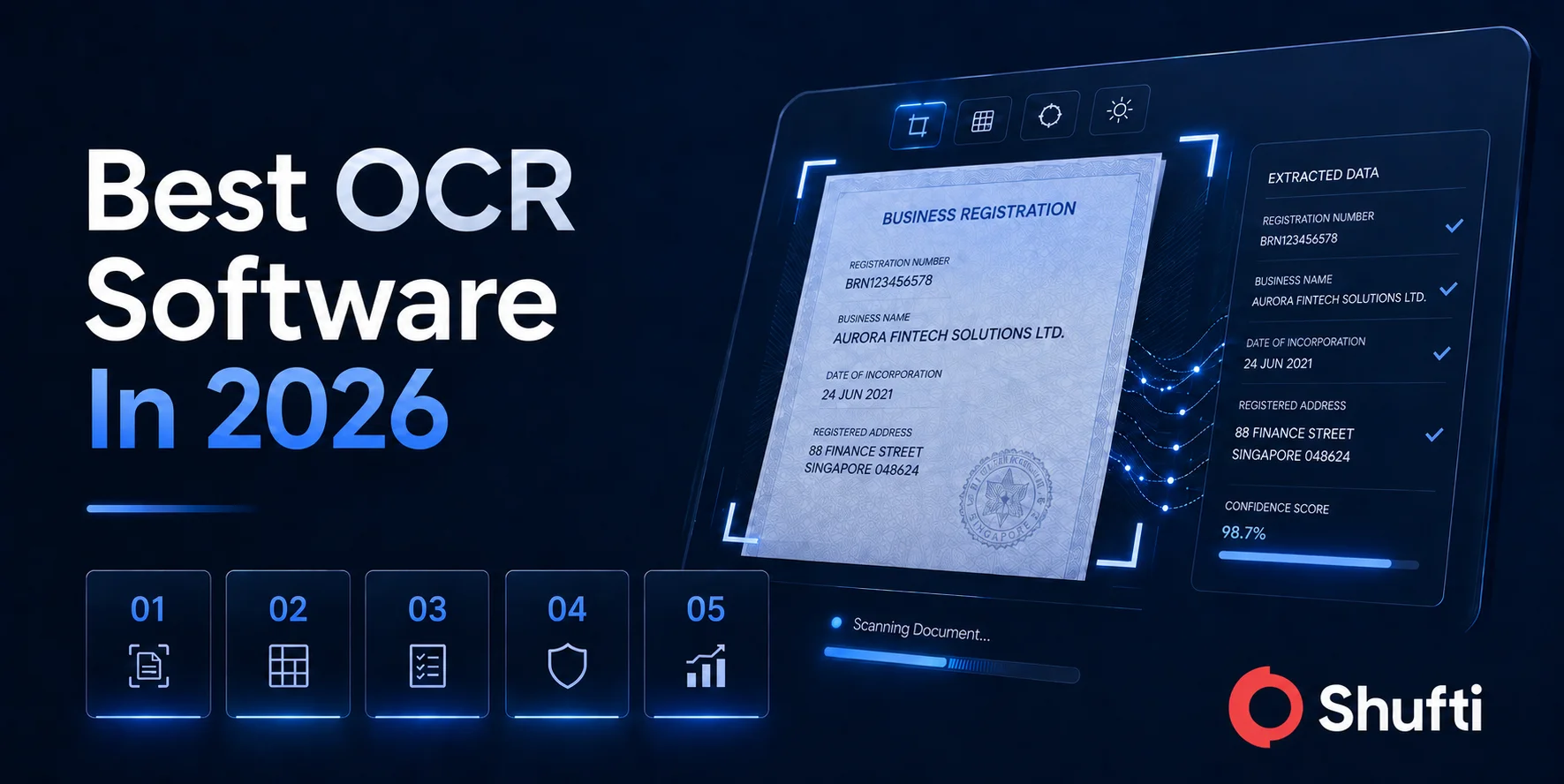
Once the identity document is uploaded, the document template is identified. The data from the document is extracted using OCR technology. During this process, the authenticity of the document is also checked. If the user-entered information and then one extracted fro the document match, identity is verified.
Common types of Fraud
Following are some common types of frauds that identity verification can better deal with:
Identity Theft
Fraudsters use various fraudulent techniques to steal the identity of online users. Through credentials stuffing in which an executable runs that stuff all possible combinations of username and passwords to get the right one and after accessing the account, steals personal and financial information. This information is then sued to perform various malicious activities in the digital world. Using a stringent identity verification measure such as biometric facila recognition, no unauthorized entity could fool the system. Only the one having unique facial traits could access the account.
Credit Card Fraud
A fraud in which fraudsters use a credit card that is revoked, stolen or reported lost and find something valuable in it. Moreover, sometimes the identity of a real person is used to receive the credit card issued on another person’s name. Identity verification can be sued by identifying an identity against the credit card.
Account Takeover
In account takeover fraud, the fraudsters first access the account of a user changes the user-provided information such as username and password and then perform fraudulent transactions. This account can no longer be used by the real user anymore. The identity on the account is used for various illegal activities. It is the responsibility of the online platform to ensure a secure mechanism of user login to make sure that customer information is well-protected and no criminal activity is facilitated through their platform.
Fake identity
Using fake identities and credentials, fraudsters create accounts in online platforms and manipulate the system. For instance, in social media platforms, fake accounts are created that are sued to troll, harass and spread misinformation on the social web. To combat this, identity verification measures should be taken and each onboarding identity should be verified against biometrics or document to make sure that no unauthorized or fake identity misuse the system in any way.
To sum up, identity verification solutions are used to fight against a variety of frauds. Various industries that are prone to online frauds can ensure controlled access over confidential data such as user accounts and organizational database to deter the risks of bad actors.