ICAIE Issues Report on Trade-Based Money Laundering in Free Trade Zones, Ports, & Safe Havens
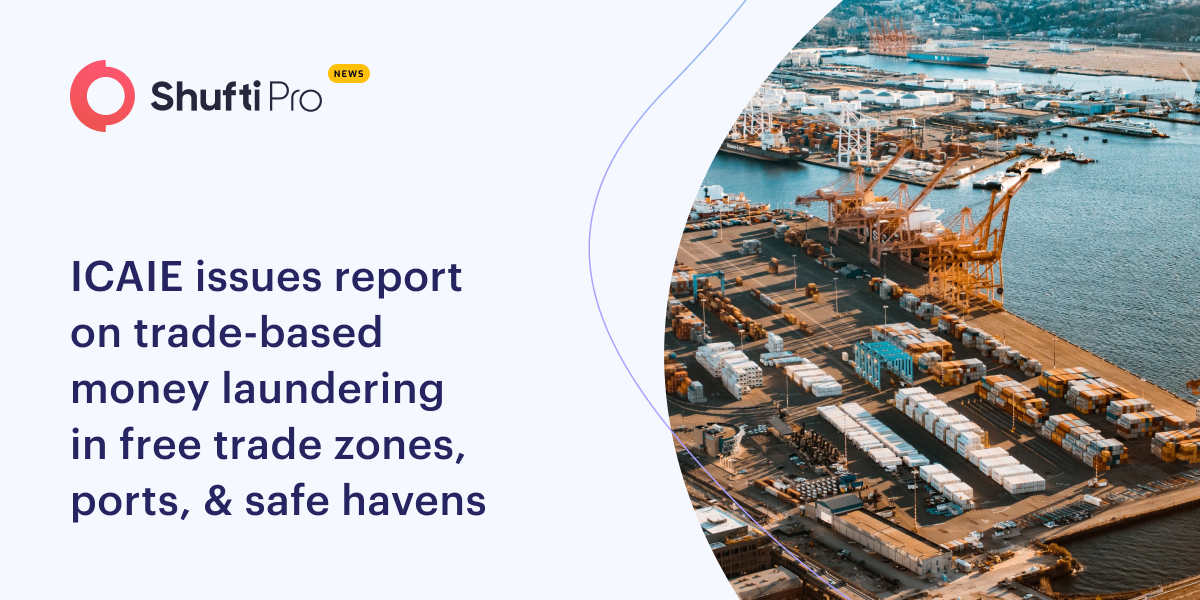
The ICAIE released a new report called “The Dark Side of Illicit Economies and TBML: Free Trade Zones, Ports, and Financial Safe Havens” to highlight the importance of public-private partnerships in combating illicit finance.
On Monday, June 13, the ICAIE issued its report that highlights the importance of leveraging strategic intelligence, network analytics, and pattern-of-life forensics to disrupt the logistics, financial wherewithal, and corruptive influence of criminals and their complicit enablers across borders, trade hubs, illicit economies, free trade zones (FTZs), and vulnerable ports.
The multi-trillion dollar global illicit economy experiences the flow of dirty money coming from various methods of illicit financing, cross-border smuggling and trafficking crimes.
Free trade zones, poorly regulated ports, ineffective enforcement of beneficial ownership laws and secretive financial hubs are threat multipliers that expand dark commerce, as criminals exploit cracks and seams in the global financial and trading systems to advance illicit trade and hide their profits.
Although the report mainly focuses on the Americas, it also sheds light on the convergence of transnational criminal activities and illicit financial threats across other regions and supply chains.
In recent times, the emergence of transnational criminal structures and illicit economies has created a clear and present danger to global security by obscuring trillions of dollars from legal economies.
These illicit funds contribute to growing corruption, instability and violence while destabilizing markets in the Americas and around the world.
Criminal actors and threat networks connected through global super fixers exploit advances in technology, transportation and other critical infrastructure for illicit enrichment. In these dangerous times, converging illicit vectors erode our collective governance, prosperity, and security.
“Illicit trade, the trafficking and smuggling of counterfeit goods, narcotics, humans, natural resources, WMD, illicit cigarettes, and other contraband impact the security of all societies. Kleptocrats, criminal organizations, terrorist groups, and their enablers exploit networked hubs of illicit trade centered on free trade zones, ports, and other logistical channels of transportation, communications, and trade,” said David M. Luna, ICAIE
Suggested read: Money Laundering and Drug Trafficking Account for Illicit Flow of US$ 1 Billion into Jamaica Annually

 Explore Now
Explore Now