Identity Verification
Identity Fraud Is Rising Across Regulated Markets
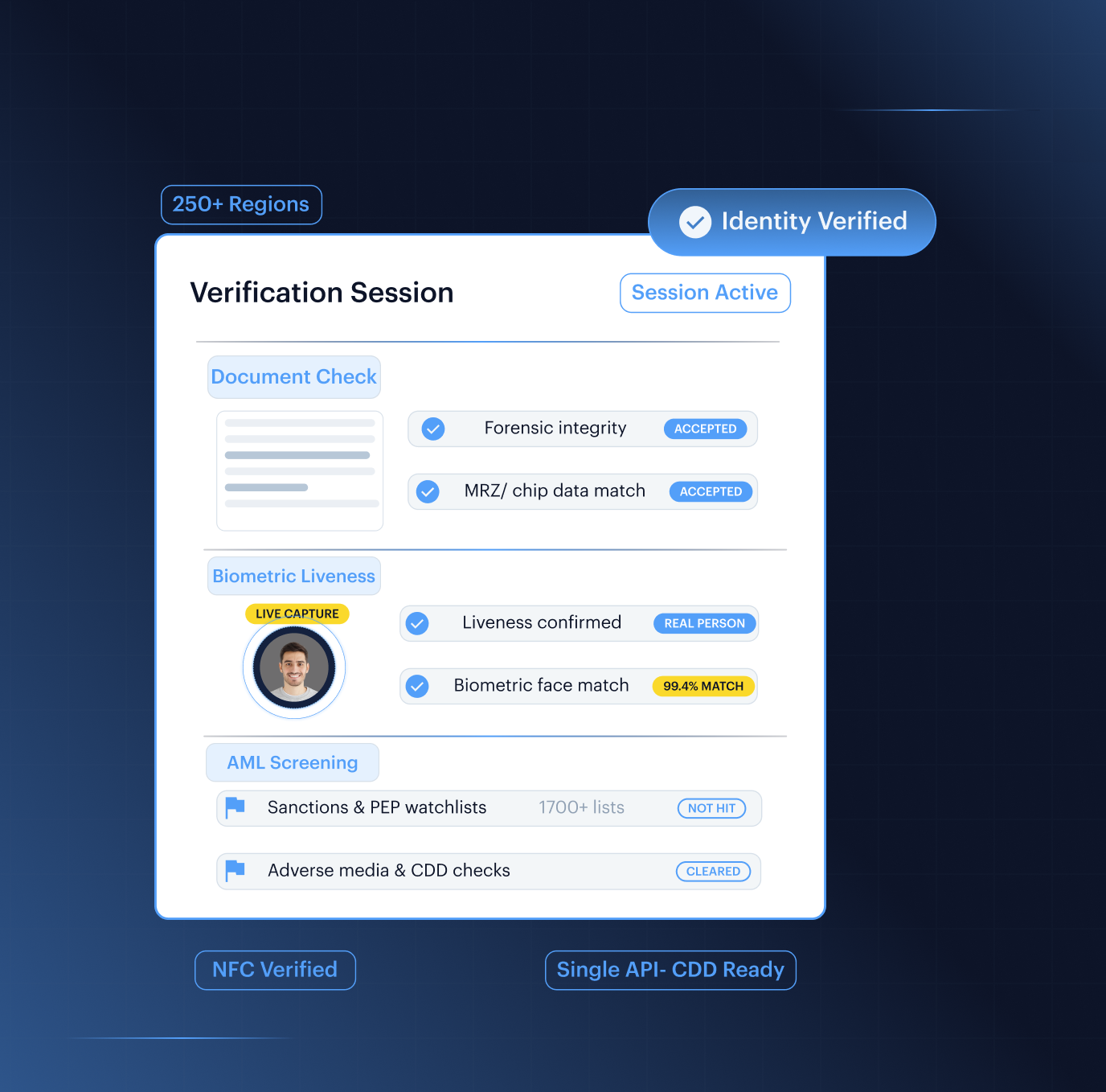
Shufti runs document forensics, iBeta-certified biometric liveness, NFC chip verification, and real-time AML screening through a single configurable API. Authenticate customers across 250+ regions, satisfy CDD mandates from one integration, and catch sophisticated fraud that bypass document-only stacks, without adding a second vendor.
Identity Verification Platform for the Entire Identity Lifecycle

Fraud Blocked Before Activation
Sophisticated fraud now enters at onboarding, with forged documents and deepfake ID attempts rising sharply. Shufti verifies MRZ integrity, document authenticity, visual field consistency, and biometric liveness before the account goes live.
Faster Flows, Better Coverage
Rigid verification creates drop-off and leaves risky users under-checked. Shufti routes low-risk customers through document and selfie checks in under 15 seconds, while high-risk profiles move automatically to enhanced due diligence

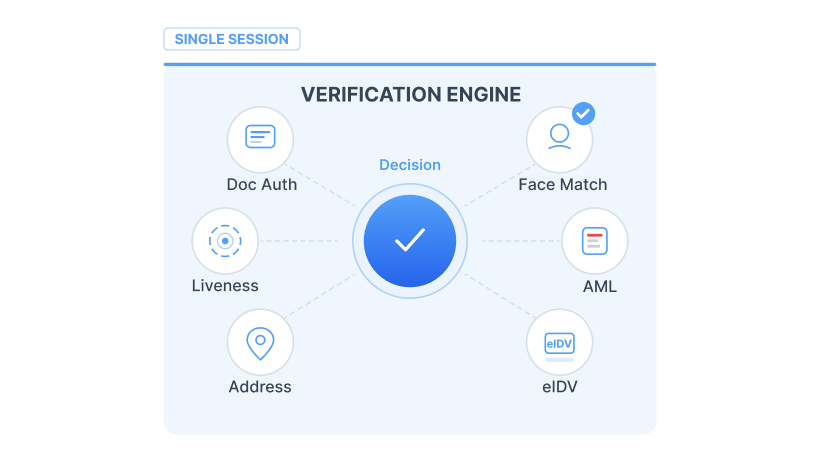
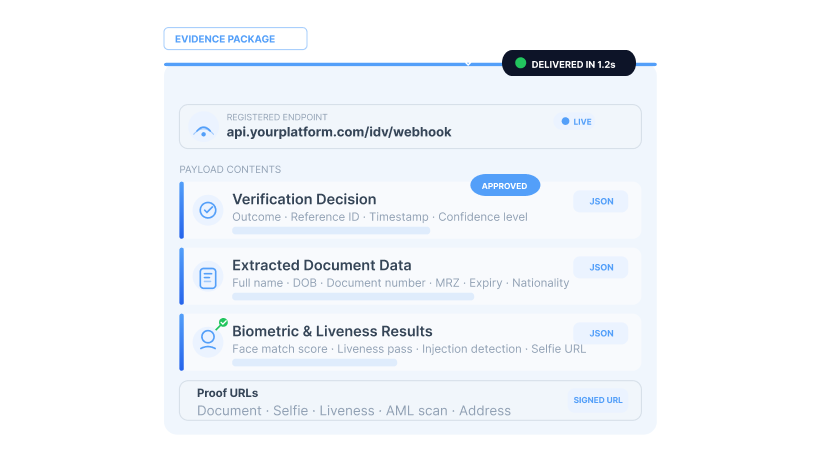
One Stack, One Audit Trail
Fragmented vendors increase cost and weaken evidence control. Shufti unifies document, biometrics, NFC, address, eIDV, and AML checks into one API, one contract, and one evidence package per verification.
Explore the Stack
Everything You Need to Verify Identity With Confidence





Verify customers in seconds, not days
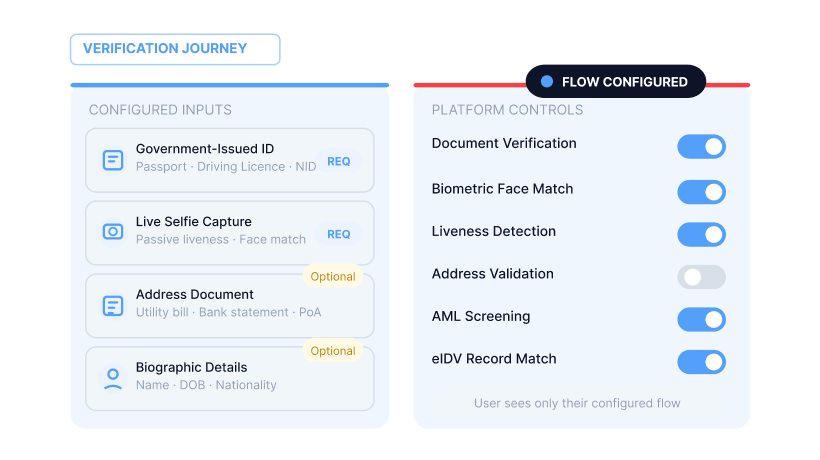
Combine document authentication, biometric matching, NFC chip extraction, and electronic identity verification into a single configurable flow. Risk-adaptive modes route low-risk profiles through faster checks while escalating high-risk cases with pre-scored confidence levels and visual forensic evidence.
-
Document Verification
Authenticate passports, national identity cards, driving licenses, residence permits, and work permits across 250+ regions and territories over 150+ languages. Forensic checks verify MRZ data integrity, field consistency, and document authenticity so tampered and AI-generated documents are caught before account creation. Decisions returned within 15 seconds.
-
Facial Biometrics
Confirm the person verifying is the person on the document. iBeta Level 3 certified liveness detection catches deepfake selfies, printed photos, and injection attacks during the selfie step.
-
NFC Verification
For ePassport and NFC-enabled national ID verification, read chip-stored biographic data and cryptographically verify it has not been altered. Cross-checks chip data against OCR-extracted fields to flag any mismatch between what the chip says and what the document shows.
-
Address Verification
Verify proof-of-address with OCR extraction in 150+ languages, structured field decomposition, and cross-checks against global postal databases. Geospatial distance detection flags signals inconsistent with the user’s location.
-
Fast ID
Streamlined one-step identity check for returning users and low-risk verification tiers. Combines biometric re-match against enrolled templates with session continuity signals to deliver a faster result, no document re-capture required.
-
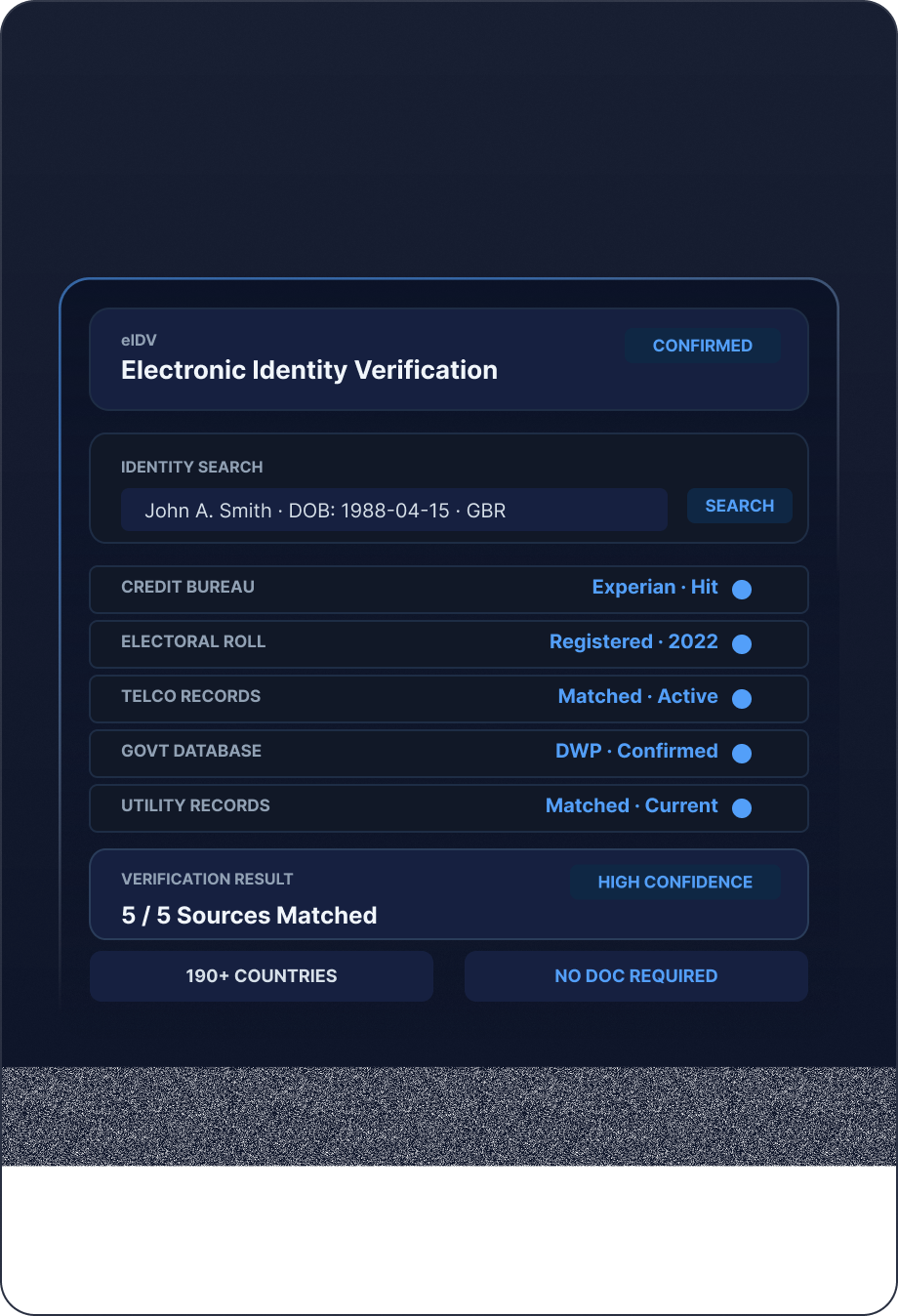
eIDV
Electronic identity verification against authoritative government and commercial databases. Database-only tier for jurisdictions where document capture adds friction but authoritative registry coverage is available. Routes automatically to document verification in markets where eIDV coverage is thin.
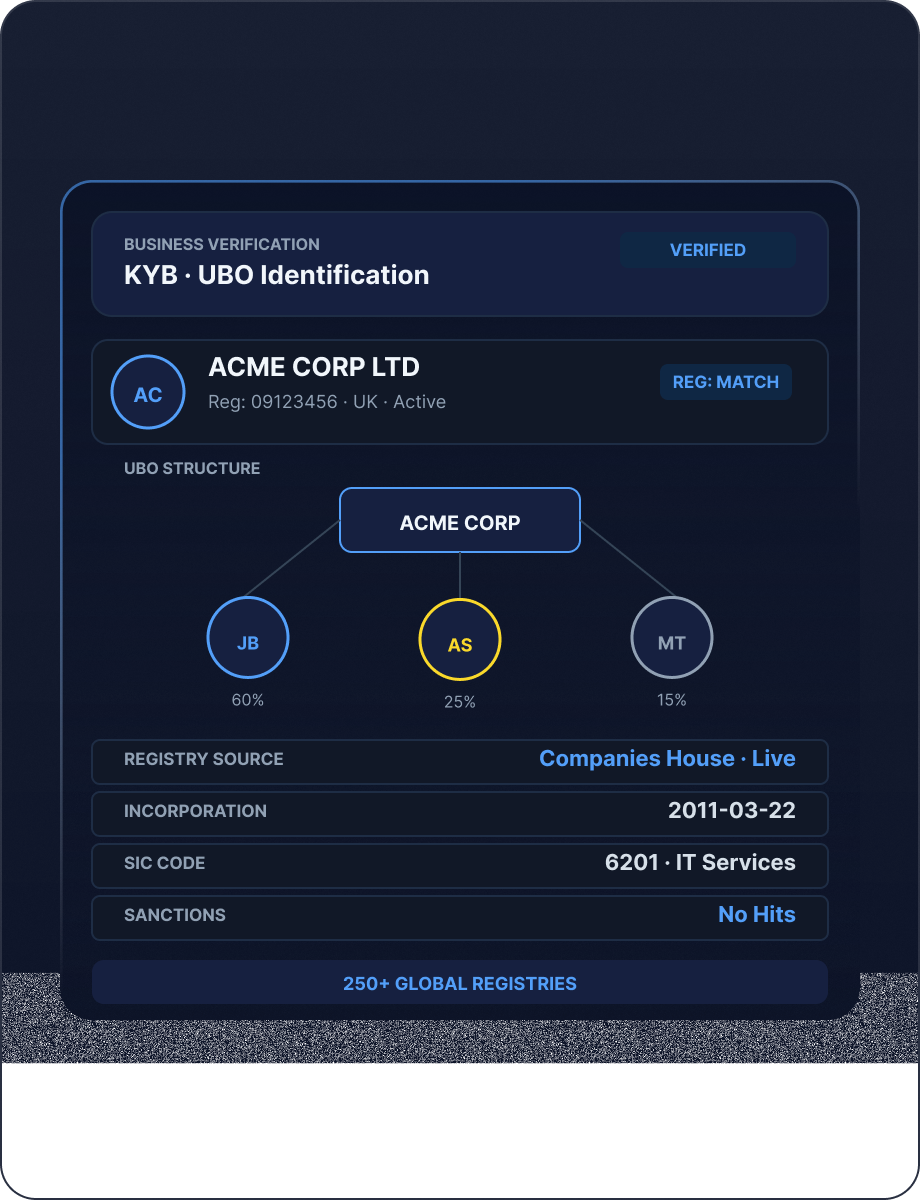

Verify businesses, not just individuals
Identity verification for corporate clients requires entity-level checks, UBO identification, director-level document and biometric verification, and beneficial ownership screening against sanctions lists. Shufti’s business onboarding module covers the full corporate identity verification chain, from registry checks across 100+ jurisdictions to investor-level KYI, under one API.
-
Business Verification
Verify corporate entities by cross-referencing registration details, UBO ownership chains, and director identities against 100+ registries. B2B identity verification moves from weeks of manual registry checks to minutes of automated entity verification with structured JSON output.
-
Due Diligence
Escalate high-risk corporate identity checks to Enhanced Due Diligence with source-of-funds verification, adverse media screening, and corporate document authentication. Configurable risk thresholds determine which entity profiles trigger EDD review automatically.
-
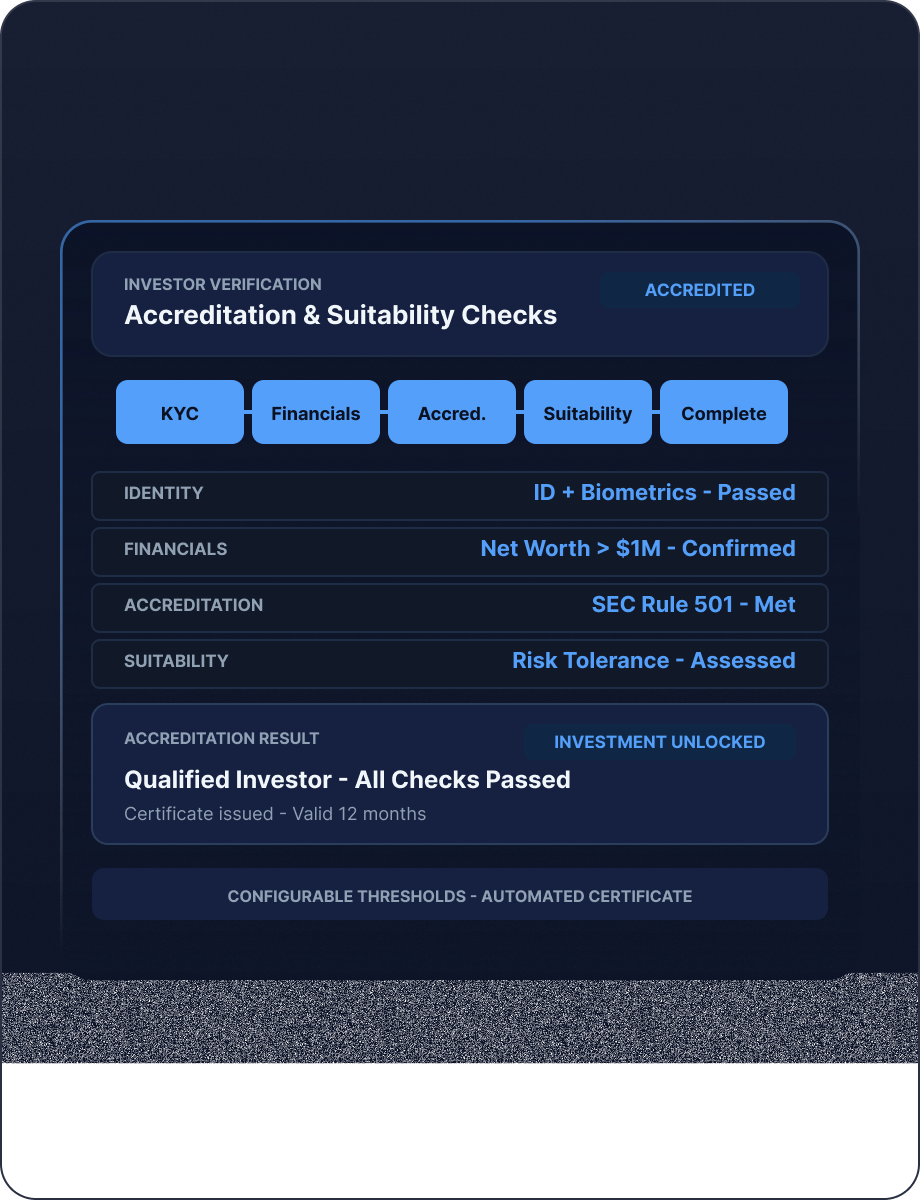
Investor Verification
Streamline investor identity verification for fund subscription workflows by combining individual KYC, entity KYB, and AML screening in one flow, built for the compliance requirements fund administrators and regulated investment platforms actually face.




Screen Once and Monitor continuously
Run identity verification, sanctions, PEP, and AML screening in one API call. Shufti creates a unified evidence trail at onboarding and monitors customer risk changes throughout the relationship.
-
AML Screening
Screen every verified customer against 3,500+ official watchlists at the point of identity verification, in the same API call. Covers 2.6+ million PEP profiles across 80+ screening languages. Watchlist data updated every 15 minutes.
-
PEP & RCA
Identify politically exposed persons and their relatives and close associates during identity verification. Ongoing monitoring flags PEP status changes and sanction additions automatically after the initial verification event.
-
Sanctions
Check every verified identity against OFAC, EU, UN, HMT, and 50+ jurisdiction-specific sanctions lists. List updates propagate within 15 minutes so customers flagged between your last check and today do not slip through.
-
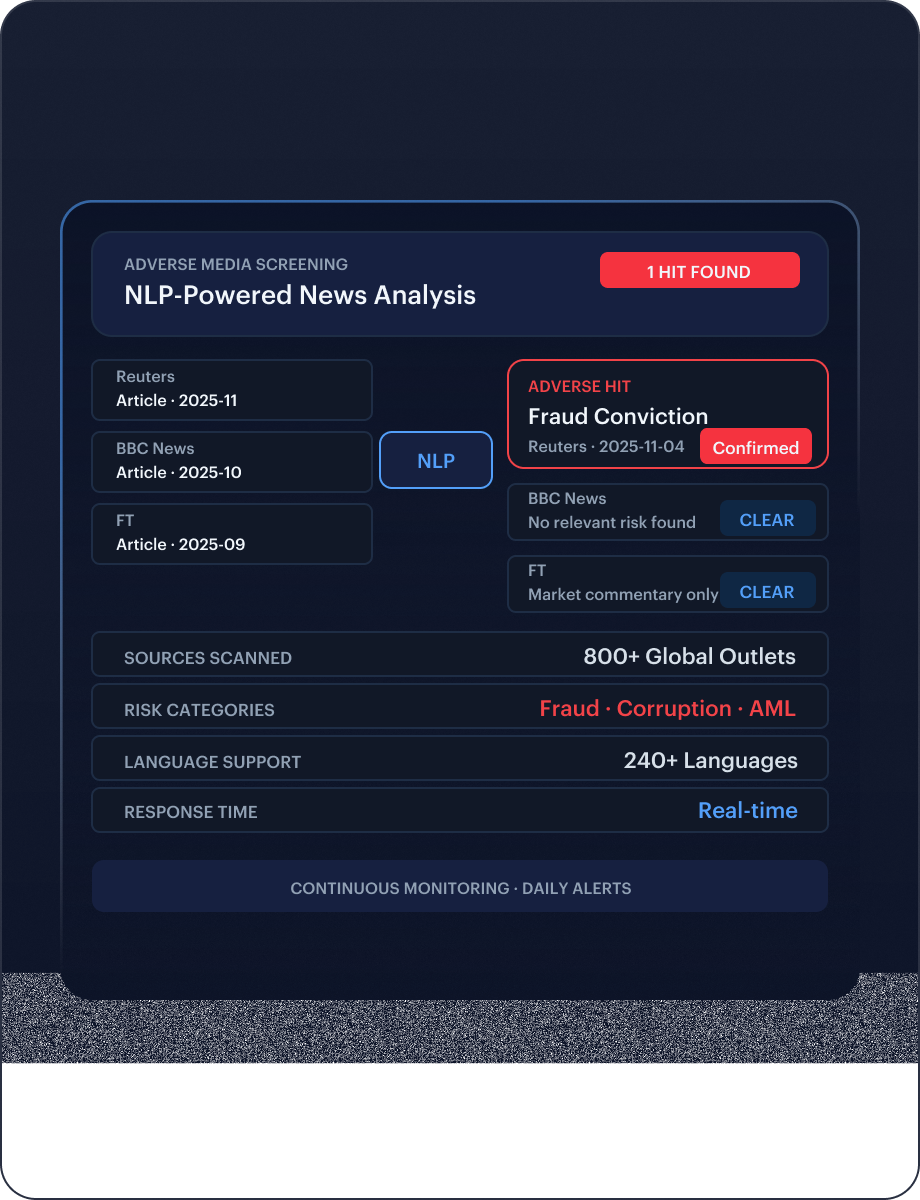
Adverse Media
Screen verified individuals and entities against 50,000+ sources for links to fraud, financial crime, terrorism, and regulatory action. NLP entity disambiguation filters false positives from common names, keeping review queues focused on genuine risk.
-
Watchlist
Maintain continuous watchlist monitoring across your verified customer base. Configurable alert thresholds, risk-tier routing, and automated SAR evidence packaging reduce compliance team workload on post-verification monitoring obligations.





Stop sophisticated fraud
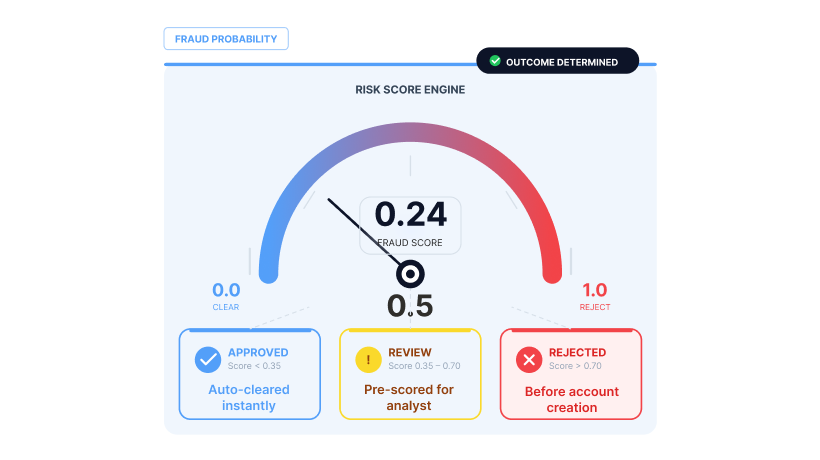
Layer behavioral signals, device intelligence, and risk scoring on top of identity checks to catch fraud that document verification alone misses. Rejected verifications include visual forensic heat maps and textual evidence so analysts see why, not just that.
-
Fraud Hub
Every identity verification receives a Fraud Probability Score (0–100%) from Shufti’s AI-powered detection layer. Rejected verifications include visual heat maps and textual evidence packages identifying the specific area of concern for analyst review.
-
Behavioral Biometrics
Detects bots and automated verification attacks by analysing interaction patterns during the verification session. Flags emulator-based submissions and scripted flows before the user reaches the document capture step.
-
Device Fingerprinting
Identify the device submitting each verification by manufacturer, model, OS version, and software environment. Flags virtual machines, spoofed device attributes, and devices previously linked to fraudulent attempts.
-
1:1 Authentication
For returning users undergoing re-verification or step-up identity checks, match a live selfie against their previously enrolled biometric template to confirm the same person is returning.
-
MFA
When the fraud score exceeds a configurable threshold during verification, trigger step-up biometric or OTP authentication before proceeding. Risk-tier configuration ensures legitimate users are not interrupted while suspicious submissions are challenged.
Built for Every Stakeholder in the Verification Decision
Build the right verification stack for your risk profile. Combine document authentication, biometrics, address validation, and AML screening into a single configurable flow.
Fraud Analyst
Pre-scored evidence and fraud signals on every flagged case, so your team reviews decisions, not raw submissions.
Compliance Officer
Audit-ready evidence on every verification, structured for regulatory inspection across every jurisdiction you operate in.
Product Manager
Configurable verification flows that balance speed against risk tolerance, without rebuilding the integration each time.
Developer
REST API, mobile SDKs, and sandbox access. First verification call within hours of integration start.
Detect Every Fraud Type Targeting Your Platform

Fraud Blocked Before Activation
AI-generated faces and synthetically forged documents bypass legacy liveness checks at scale. Shufti's passive liveness & document forensics detects synthetic media before it reaches your onboarding flow.

Faster Flows, Better Coverage
Credential theft, blended synthetic identities, and manipulated documents exploit gaps in manual review. Shufti's layered verification surfaces fraud signals before accounts are created.

One Stack, One Audit Trail
Duplicate registrations, bot-driven sign-ups, and referral exploits erode platform economics. Shufti links device, identity, and behavioural signals to flag abuse rings at scale.

One Stack, One Audit Trail
False chargeback claims, money mule networks, and sanctions evasion expose your business to financial and regulatory risk. Shufti ties identity verification directly to transaction context.
Single API, Seamless Integration
Build fully customisable verification flows with seamless backend integration.
- Gain full control by customising verification flows end-to-end.
- Integrate seamlessly with your backend for quick implementation.
- Design flexible verification journeys tailored to your users.
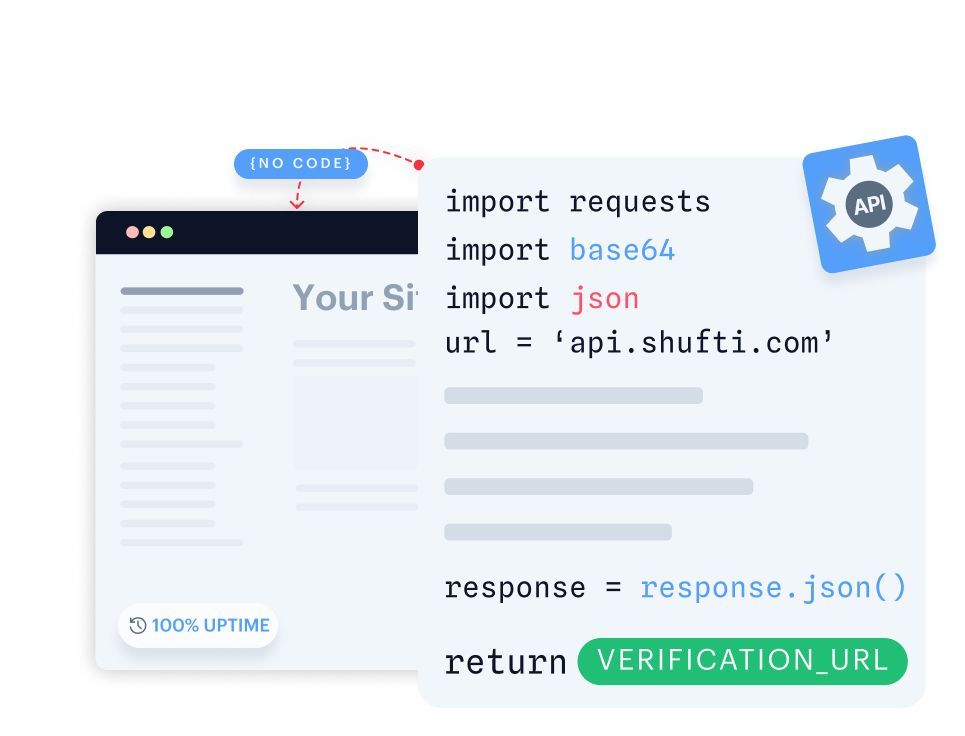
Launch a native verification experience in your mobile app within minutes.
- Launch native verification within minutes on iOS or Android.
- Use ready-made UI with camera, capture, and real-time feedback.
- Customise flows to fit seamlessly into your mobile app.

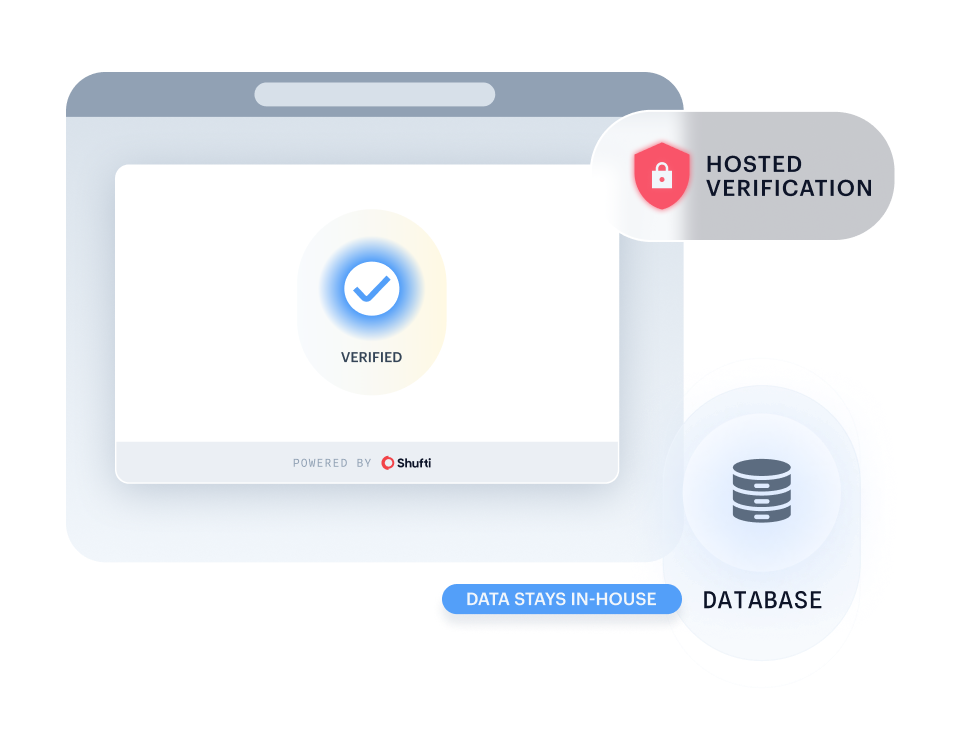
Run Shufti within your own identical-capability infrastructure for maximum data control and privacy.
- Keep all sensitive information in-house to meet strict governance and data residency requirements.
- Keep sensitive information fully private and secure in-house.
- Deploy in highly regulated sectors without compromising compliance.
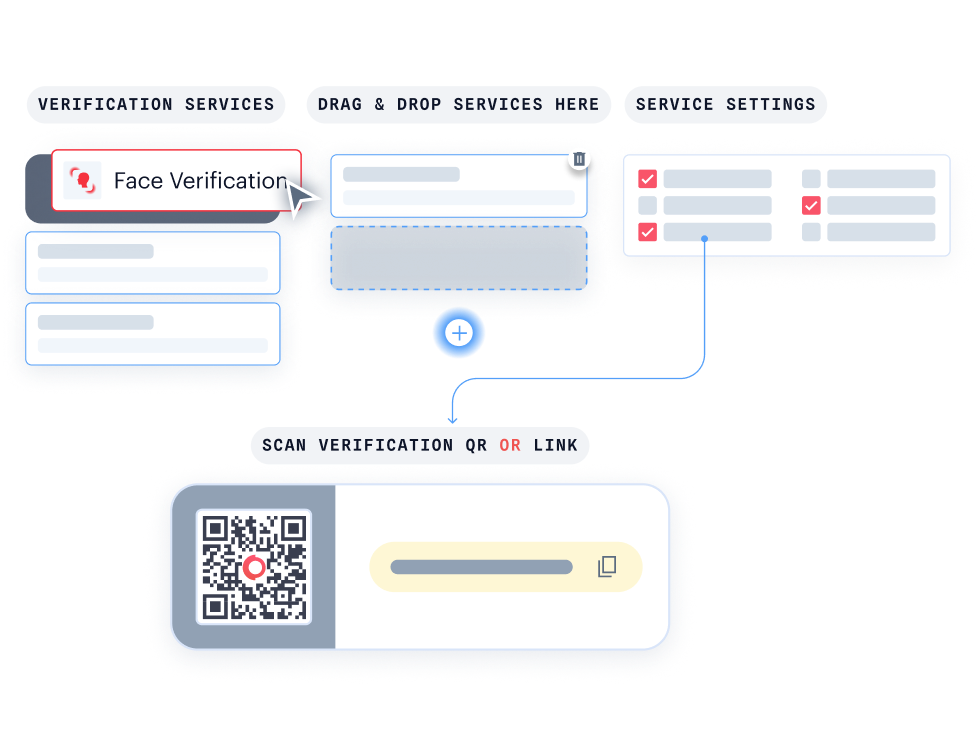
Quickly launch identity verification through a secure, customisable web link, no code required. Learn more.
- Start verifying users instantly with a no-code setup.
- Deliver a consistent identity experience via a link or embedded iframe.
- Deploy quickly via a secure link or embedded iframe.

With KYC Journey Builder, create personalised verification journeys without writing a single line of code.
- Customise your journey effortlessly with drag-and-drop functionality.
- Instantly see how your verification flow looks for your users.
- Easily connect with Hosted Verification for a consistent, branded experience.
Detect Every Fraud Type Targeting Your Platform



INDUSTRIES
Identity Verification Services Across Every Regulated Industry
Trusted Sellers, Repeat Fraud Blocked
Verify the seller is real at onboarding, then prevent re-joins with duplicate detection and optional 1:N matching across the marketplace.
Don't just take our word for it, hear from our customers
The Confidence Our Clients Share
The future of digital identity is defined by trust, interoperability, and regulatory alignment, so our partnership with Shufti reinforces DevCode Identity's commitment to supporting our global customers with the most secure, best-in-class, complaints identity verification solutions available today.
Combining our Conversion Driven Compliance Orchestration Platform with Shufti's global KYC and IDV capabilities allows our customers not only to navigate complex regulatory demands but also to maintain a seamless customer onboarding experience with the highest achievable conversion rates.
Shufti gives us verification journeys we can trust across every market we serve. The ability to route players through passive database checks, eID authentication, and full biometric liveness — all behind one API — has reshaped how we think about onboarding compliance.
Their team acts like an extension of ours. When regulators added new requirements across two European markets, Shufti’s journey builder let us adapt in days, not months.
FXBO customers demand speed without compromising AML rigour. Shufti’s eIDV fits exactly there — high-assurance verification for large deposits, invisible background checks for everything else, and one compliance trail across the board.
Integration took a single sprint. The SDK handled the full journey, so our product team stayed focused on trading features instead of building KYC screens.
As a regulated European payments platform, we need identity verification that meets eIDAS 2.0 and AMLD6 without multi-vendor stitching. Shufti delivers both — native eID authentication for high-assurance markets and docless database checks where eIDs don’t reach.
One contract, one audit log. That changes the compliance conversation entirely.
Frequently Asked Questions
What verification checks are included in a standard identity verification flow?
A standard flow includes document verification, biometric face matching with iBeta-certified liveness detection, and AML screening against 3,500+ official watchlists covering sanctions, PEP, and adverse media. Optional layers include NFC chip verification, address verification, and eIDV database checks. Each check is configurable based on your regulatory requirements and customer risk tier.
How long does a typical identity verification take?
Most verifications complete in 15-60 seconds. Low-risk profiles routed through automated decisioning are typically processed faster. High-risk cases escalated to enhanced due diligence or manual review may take longer depending on your configured review SLA.
How does Shufti detect synthetic identities and deepfake documents?
Multi-layer document forensics analyzes template structure, MRZ integrity, font consistency, and security feature placement. Biometric liveness detection, iBeta Level 3 certified to ISO 30107-3, identifies deepfake selfies, 3D mask presentations, printed photo attacks, and digital injection attacks.
What is the difference between passive and active liveness detection?
Passive liveness requires no action from the user. The system analyses a single selfie or short video for presentation attack indicators. Active liveness asks the user to perform a specific action to prove physical presence. Passive mode suits standard CDD onboarding; active mode provides higher assurance for step-up authentication or high-risk flows.
Where is identity data processed and what data residency options are available?
Shufti processes identity data through regional cloud infrastructure across EU, UK, US, APAC, and MENA. Clients configure their preferred processing region during onboarding. Retention is client-configurable. The Data Processing Agreement covers GDPR Article 28 requirements, and Standard Contractual Clauses are available for cross-border data transfers.
What happens when a verification fails?
Failed verifications generate a structured reason code and a Fraud Probability Score. Document failures include a visual forensic heatmap identifying the specific area of concern. Failures can be auto-rejected, routed to manual review with pre-scored evidence, or escalated to enhanced due diligence. Every decision is audit-logged with a timestamped evidence package.
Evaluate Whether Your Verification Stack Covers Every Market You Operate In
Fraud tactics, identity regulations and onboarding expectations are changing quickly. Assess whether your current stack can verify users, businesses and high-risk cases through one audit-ready workflow.