3 ways to protect your organizations from coronavirus cyber security threat

Due to the spread of the coronavirus, the world adapts to new ways of working. Cyber criminals are proving themselves as adaptive as ever at finding innovative ways to exploit new cybersecurity vulnerabilities of businesses. These criminals are coming up with different tricks to exploit a system in this pandemic. It is paramount that businesses look for ways to better understand the risks to their organizations and learn how to mitigate or eliminate those risks.
Cybercriminals are continuously exploiting the ongoing pandemic and fulfilling their malicious intent. In this pandemic, cybercriminals are taking advantage of the situation escalating their malicious activities. According to the “100 Days of Coronavirus” report by Mimecast, malicious cybercrime activities have increased significantly by 33% from January to March 2020.
This situation is alarming, businesses need to take proper steps for cybersecurity to mitigate the risk of cybercriminal activities. In the name of updates about coronavirus, many fraudsters are becoming successful in identity theft, data breaches, and other online scams. Following are the three ways how businesses can stay a step ahead of such activities in this pandemic:
Guarding against coronavirus phishing attacks:
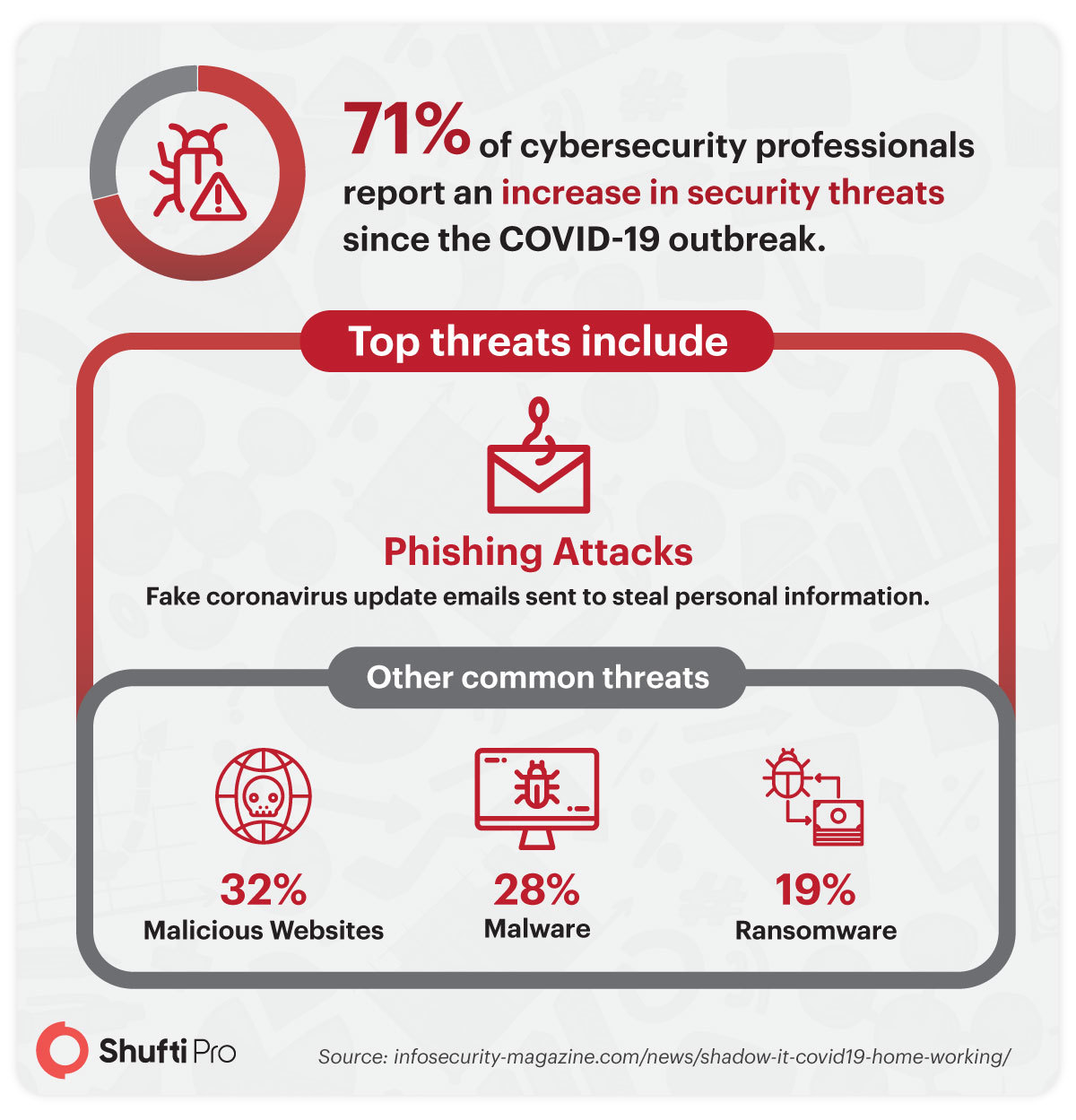
According to a report, 71% of cybersecurity professionals have reported an increase in security threats since the virus outbreak has shaken the world. The top of these threats includes phishing attacks-fake emails sent for coronavirus updates supposedly sent from well-known companies in order to induce individuals to reveal personal information. Among the other, most common threats are malicious websites (32%), malware (28%), and ransomware (19%) as per experts.
Cybersecurity threats are not a domestic issue but span across all countries and impact all sectors. Businesses need to learn how to better prevent attacks and protect themselves. In fact, in a recent Federal Bureau of Investigation (FBI) report, the agency reported that cyber actors have engaged in phishing campaigns by deploying ransomware at medical facilities and by creating fake COVID-19 websites that quietly download malware to victim devices. This underscores the importance for businesses to use cybersecurity best practices, such as:
- Rule and Policy for Telework:
Make rules or policies for telework for your business, and make sure the employees comply with them. Businesses offer differing guidance on bringing your own device (BYOD), so be sure you comply with your organization’s policy.
- Strong Security of Internet Connection:
Businesses need to protect their digital communications from eavesdropping. Configure your home Wi-Fi router for strong security and ensure it is protected with a hard to guess password.
- Secure Virtual Private Network:
Businesses having a virtual private network client, have to use it on their telework device. Enable basic security features (e.g., antivirus, multi-factor authentication) if using personal devices.
- Keep Updated Softwares:
Keep all devices patched and updated in your organization to combat certain cybercriminal activities.
- Do Not Open Suspicious Links:
In these moments it is best to be cautious and verify identities. So do not click on any links or open any attachments that you find suspicious and were not expecting. To assist in this regard the Australian government has a website that gives information on how to prevent phishing attacks and know which elements in emails set off alarm bells. These are enlisted here:
- Requests for money, especially if urgent or related to overdue bank account changes.
- Suspicious or Unwanted Attachments.
- Requests to check or confirm login details or credentials.
Ways to conduct safer meetings
As many companies shifted to remote work cybercriminals also understand that the physical IT infrastructure for many companies has shifted tremendously. Securing online meetings are a top concern for remote workers. As even by now many software have fallen foul of privacy concerns like Zoom. So always use your organization’s approved web conference platform to avoid data breaches and other online scams.
- Use digital identity verification to authenticate new participants as they join in.
- Keep on changing the passwords.
- Do not record the meeting unless necessary.
As the way businesses work has quickly evolved, so cybercriminals’ tactics have become advanced too for exploiting these new ways of collaborating. This means it’s especially important to rely more closely on existing cybersecurity standards.
Integrate Identity Verification Solutions:
The pandemic is affecting businesses globally. Digital transformation is substantial for every sized business during this pandemic to continue their activities. To ensure customer sustainability in this challenging time, digitally active businesses are playing best to fight risks of digital security. Businesses can verify their customers online by deploying eKYC practices.
eKYC ensures customer identity verification online by document verification using OCR technology and video KYC verification process. Such identity documents include ID card, passport, driving license, etc. By verifying customer information through these documents, businesses can operate seamlessly. The process is simple and the information from the documents is extracted using OCR technology and the identity is verified based on that data by screening it against sanction lists and PEPs.
A video KYC is another method in which KYC business experts connect the customer on a video call and conduct the process of customer verification which includes both documents and behavioral verification of the customer. In this way, all the customers can be authenticated to shield the scammers away from the system and add an additional layer of cybersecurity.
Moreover, biometric technology can be used to enhance the authentication process. By using 3D liveness detection features of facial reaction technology individual’s real presence can be authenticated to mitigate the risk of deep fake or spoof attacks. So in order to comply with regulatory authorities and to authenticate an individual for cybersecurity measures businesses need to have proper identity verification solutions integrated into the system. This will screen out all cybercriminals and businesses will be a step ahead.
Read more : How businesses can prevent fraud during COVID-19.