5 reasons why passwords are no more safe – What’s next?

Online platforms are using passwords to secure the privacy and data of their users – but are they secure?
Passwords started with the Compatible Time-Sharing System (CTSS), an operating system introduced at MIT in 1961. It was the first computer system to implement a password login. We are in 2020 and the decades of passwords usage made it the major security protocol. Although the increase in data breaches, social engineering attacks, and cyber crimes has tarnished the reputation of passwords. But still, the masses are using it as a medium to ensure customer privacy and data security on their platforms. Even the banks are using passwords to allow online access to their customers. But the research and increasing cyber crimes hint that passwords are losing their value. Newer technologies such as two-factor authentication and AI-based biometric authentication are the trends slowly building up.
A survey found that one out of five American consumers has experienced an online account compromise. And these frauds are possible due to a lack of efficiency in password security.
Data breaches are a common way to get hold of someone else’s confidential data. 4.1 billion records were lost in the first half of 2019 (Forbes). And the data stolen in these data breaches are used to gain illegal access to online platforms, protected with inefficient passwords. But why are the passwords inefficient?
Why passwords are losing value?
Passwords are in use for decades but gradually people are losing faith in the security provided by passwords. When it comes to actual impenetrable security, businesses prefer other security means such as biometrics and two-factor authentication along with passwords. Even cell phones now have biometric unlock feature to secure the device. So passwords are no more the favorite security tool.
- The traditional authentication checks
Passwords are still limited to traditional binary and alphanumeric figures. The typical input for password-protected access is still username and password. Guessing someone’s username is not difficult. And people use the same email address to onboard several online platforms. The research found that in the U.S the average email address is associated with 130 accounts. This leads to easy access to someone’s email ID. Next comes the password. It is also the same in most of the cases. Google found that 52% of the people use the same password for multiple accounts and 13% use the same password for all accounts.
- Changing passwords frequently is not enough
The supporters of passwords always say that frequently changed passwords are the key to security. But let’s see how this frequent password changing mechanism works. The best practice is to change the password every month and the password created must be complex enough to make it difficult to crack. But does it actually works this way? No, it doesn’t.
Users find this password changing thing very hectic and most of the time they don’t change their passwords frequently. Research on 1,000 U.S google users found that one-third of the users change their account passwords one to two times a year. 10.9% of respondents said that they never change their passwords. So it shows users, generally don’t bother sticking to the secure password policies.
If we talk about the strength of passwords, people generally tend to create easy to remember passwords especially when they are directed to change passwords every month, they make easier passwords and save them somewhere (written and digital form) or shares with a colleague. 69% of users still share their password with a colleague. National Cyber Security Centre (NCSC)
So the user behavior is key behind the inefficiency of password security. 57% of the people who have fallen for a phishing attack still haven’t changed their password in the UK.
Hence the passwords security mechanism doesn’t have any concrete measures to make the people develop a habit to change their passwords or to develop strong passwords. The web portal could send reminders for password change and security alerts, but could not force them to do it.
- Complexity is not paying off
It is often considered that strong passwords are difficult to hack. But still, there is a risk of hacking or forgetting the password. People tend to forget difficult and complex passwords, so they frequently reset the passwords. It affects the user experience on your online platform.
The hackers are well aware of the science of strong passwords, Brute force attacks are used to decode these passwords. A Brute force attack is conducted by trying all the machine-generated combinations for a password unless a match is found. So even strong passwords might fall for a brute force attack.
- Hackers are becoming smarter
Hackers are becoming smarter and they know well how to use the technology. Social engineering (phishing attacks) is the commonly used technique that helps them get the required information from the people. 50% of internet users receive at least one phishing email a day and 97% of them can’t actually identify a phishing email. So it is very easy for a hacker to get into someone’s system and hack log in credentials of a user.
Also, the hackers are aware of all the password protection techniques and know well how to surpass them.
- Readily available password reset options
Due to phishing attacks, it is not difficult for hackers to enter the system of a person. It is quite easy to enter someone’s mailbox and get access to confidential emails of a person. Every login page allows the user to make several login attempts and an option to reset a password. Some take 24 hours to reset a password, others do it right away. If a hacker has access to someone’s account it can easily use the password reset link to invade an account. Given the practice of using the same passwords on all accounts, it becomes, even more, easier to hack an account. Because most of the online businesses are using passwords to protect an account.
What does the future hold for user onboarding?
With the decrease in the value of passwords, businesses are looking for new ways to replace passwords. Biometric verification solutions and 2FA delivers high security that passwords lack.
Biometric authentication
Biometric authentication is one of the fastly rising technologies used in this world. Biometric authentication solutions use face verification to allow access to an online account. It covers all that lacked in password systems.
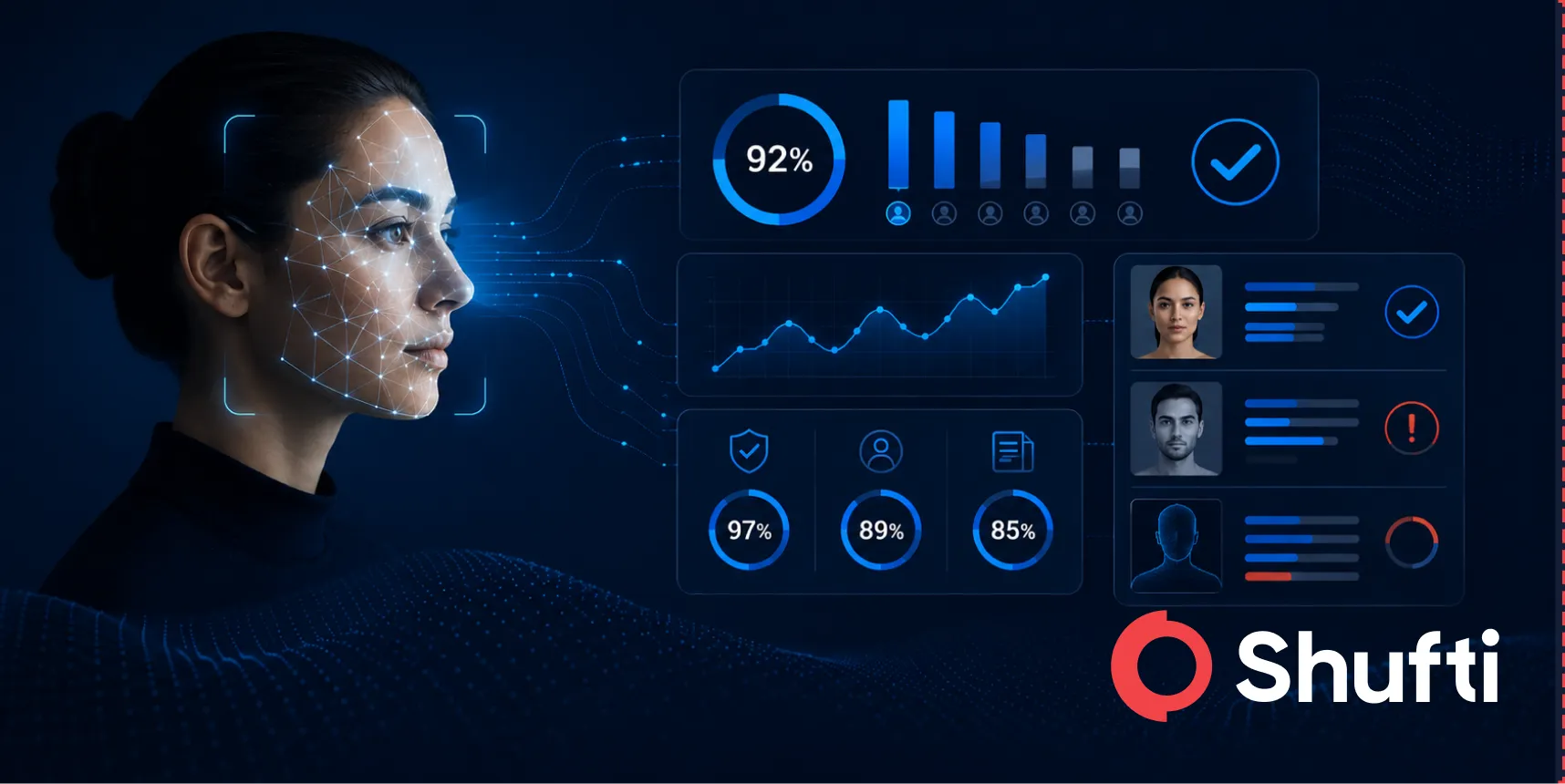
It is almost impossible to manipulate a biometric authentication system. It uses a liveness detection mechanism to identify paper backed images used for verification. A real-person must make the verification to get past the security checks. Minor facial movements are traced to check that a real person is behind the camera. Unique facial features and contour points are detected with a 3D depth perception technique to identify paper-backed and photoshopped images.
The picture of the real user is saved in the database in the form of a mathematical formula and used to compare the facial image submitted for login. Artificial Intelligence is used in these solutions to perform verification on the user.
Biometric login is quite easier to use for the end-users due to vast usage of selfie cameras in mobile phones. Also, these solutions deliver high accuracy (98.67%). So, due to all these perks, biometric signage is the next big thing and businesses are using it to increase security on their platforms.
Two-factor authentication
It is often used in combination with passwords. 2FA sends a unique code to the mobile phone of the user, that is required to log in to his account.
To wrap up, passwords are losing value due to high risk. This lack of efficiency of passwords requires businesses to explore new user security techniques. Strong security measures that allow fast logins enhances user experience. As the ultimate goal is user satisfaction, businesses must think of giving up the old security practices, to gain higher customer value.