e-KYC Services for Libraries

Have you ever had those series of events that leave you shaking your head? That makes you believe that life is actually a Rube Goldberg machine where one small event triggers a lot many more. Well, that is exactly what happens when you get your wallet stolen, you remember to close down all your credit cards, but sometimes you forget you had other things in there as well. You go to the police station to inform them and get a report just in case something pops up. Life continues as normal then a couple of months later you get a bank statement and as you go through it you find some charges you don’t seem to remember. Confused, you call the bank and they say that you had applied for a credit card. You tell them you had applied because your cards were stolen but it was over two months ago and you had already received them. You confirm the branch of the bank and you realise you don’t do business with them. You inform that someone has stolen your identity and these are not your charges. You ask them don’t you do a complete e-KYC verification? They say the application was online and almost all required verifications were done except for an image check. Obviously they did not do a background check. After clearing the issue up with the bank you believe that things have settled down. Yet after another couple of months you get a letter from the public library you used to borrow books from. You see that there are some books that are overdue and you have been fined as well. You slap your forehead realising that you had your library card in your wallet as well. You go to the library show them the report and inform them that someone had stolen your identity. You request them that they should have some sort of verification system to deter fraud activities. After clearing the issue with the library, you hope that no other issues pop up…

How Can e-KYC and Identity Verification Deter Fraud Activities in Libraries?
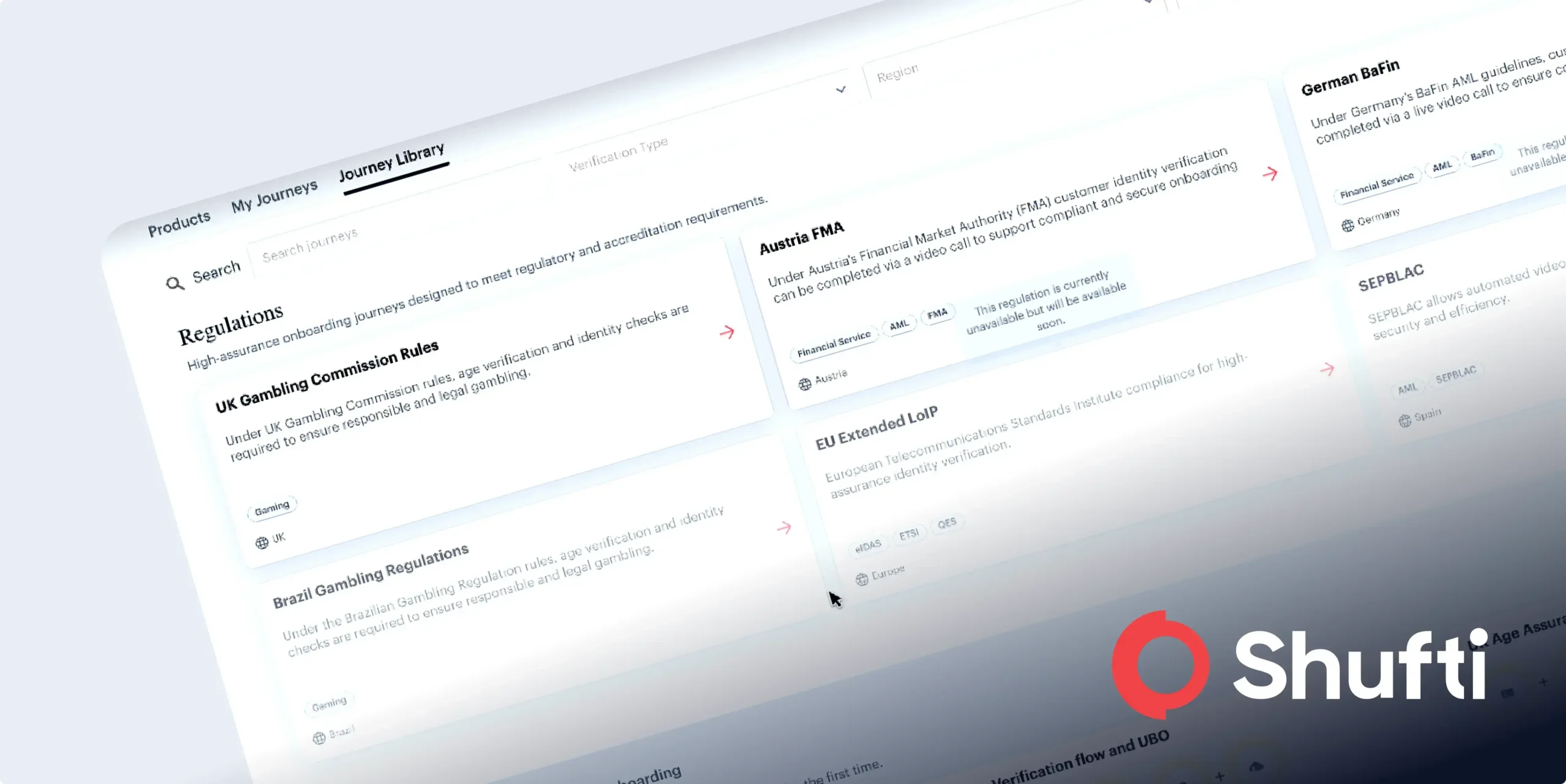
KYC identity verification has become a need for online as well as physical libraries. Most of the public and private libraries around the world provide their customers with library cards that are used to keep a record of their visits to the place or if they wish to borrow books. This means that without an identity verification system installed in the library, imposters can use the stolen library cards/information at the library They could use its resources and check out books all the while using the identity of another person as mentioned in the story above. With a simple 3rd party verification system the libraries can actually stop such fraud activities from happening. Basically, when the imposter finds out that there is an ID verification check before they are allowed to check out books, they will be reluctant to use someone else’s ID. They understand that they will get caught.
How Do e-KYC Verification Systems Work?
Most of the e-KYC verification systems are powered by AI. The AI checks and matches images and information among other things. It utilises the Internet and the user’s webcam or smartphone camera. In order to get a better understanding lets take the example of a library system. If someone wishes to check out a book online, the system will ask them to face their webcam or smartphone camera. It will inform them that this is a verification check and the session will be recorded. The system will then analyse the user’s face and check for excessive makeup, masks and any other signs that would show that someone has changed their outlook. The system is smart enough to keep into account the changes due to glasses, haircuts and facial hair. Then it will ask the user to present their library card focusing on the name. Then it will ask the individual to share their ID card and ask them to focus on picture, name, DOB and number (if applicable). The AI checks the data including the picture and matches it with what is available in the library system. The entire process takes less than a minute. Since the session is recorded, it will act as proof in case of any fraud activity. In this same way a PC for verification can be allocated within physical libraries where the borrower is requested to verify their identity.
Libraries and the Importance of Background Checks
Although background checks are not done in libraries but they should be. In fact the same system that carries out the identity verification can also check the background of the individual. The process need only be carried out initially when an individual registers with the library. The system checks the individual against global watch lists and other databases for criminal records. Such information can be considered an important part of e-KYC identity verification.

 Explore Now
Explore Now