Enhancing Workplace Safety: The Role of Employment Screening

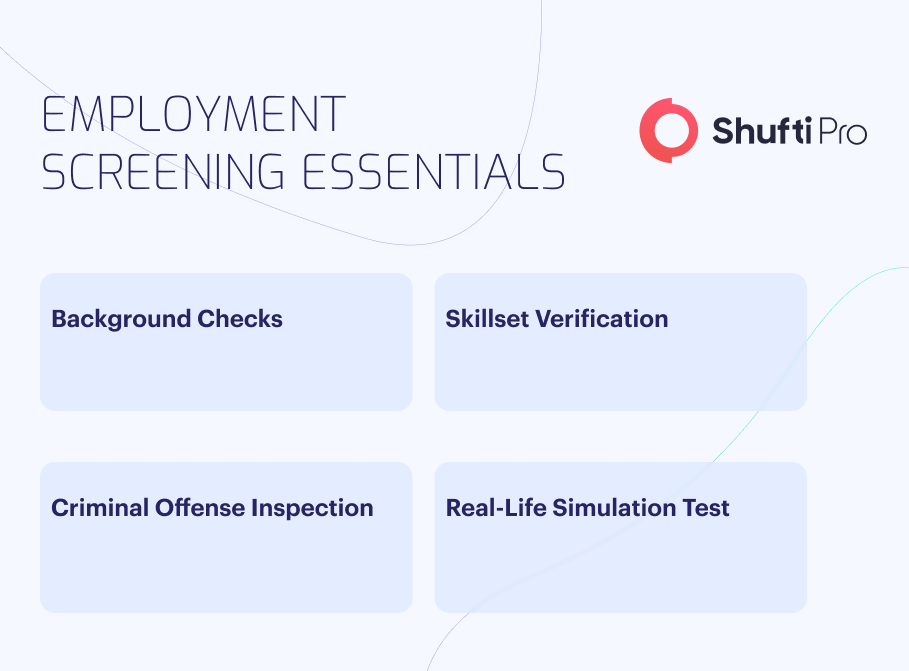
Recruiting new hires can often be a daunting task, as it is a time-consuming and work-intensive process. When hiring, recruitment officers need to ensure that the individual being hired has no connection to any illegal affairs and no past criminal records, as this can gravely impact the business. Establishing relationships with an entity involved in criminal activities can result in non-compliance charges and often damage the business’s reputation.
The United States is accountable for almost 44% of all global regulatory AML/KYC fines and 91% of the total value, which is $23.52 billion. These fines make it clear just how important it is for companies to comply with Know Your Customer (KYC) and KYB regulations. Employment screening is an essential part of the standard KYC procedure and is necessary as it assures safety and eliminates probable financial crimes.
What is employment Screening?
Employment screening involves gathering information on a job candidate and running that information through identity verification (IDV) checks to catch any possible threats. The employment screening services market is projected to grow from US$ 5.360 billion in 2022 to US$9.296 billion by 2028.
In most cases, the standard documents include government identification documents, proof of eligibility to work, educational transcripts, professional licenses, drug tests, and criminal records. These documents are then verified against official databases and government records to ensure the entity is legitimate and unrelated to illegal activities. Employment verification is conducted to determine an individual’s eligibility for the job. The employee onboarding process commences once the documents are verified, and the entity has been established as legitimate.
As the majority of companies have digitized operations to meet the demands of a digital world, the hiring process has also followed in concurrence with this change – with most hiring processes being conducted on platforms and websites such as LinkedIn and Indeed. A general pool of users can apply to various open jobs in standard cases. Once the applicant submits a job application, the job portal’s process closes, and the company establishes personal communication with the applicant. At this point, there is no plausible way for the company to determine the applicant’s intentions accurately or whether they are a threat. Employment screening services are handy at these checkpoints so companies can successfully identify threats before dealing any damage.
Employment Screening for Companies and Employees
Conducting employment verification is a legal obligation and requires business owners and individuals to comply. Legal and accurate documents should be present on both ends for proper verification. The general public is less aware of what employment is and what employee onboarding is.
These requirements have some essential elements that need to be considered:
-
Fair Credit Reporting Act (FCRA)
This was enacted in 1970 and allows consumers to dispute credit report inaccuracies and requires background checkers to collect, distribute, and use employee data with informed consent. This was necessary to improve transparency in the sector and allow businesses to have a more transparent view of their employees. With the crucial legal information of employees now available to regulatory authorities, it was relatively straightforward to differentiate offenders from legitimate entities.
-
Investigative Consumer Reporting Agencies Act (ICRAA)
This act allowed companies and private business owners to access the personal records of their employees. The enactment of this law took place in collaboration with global regulatory bodies, after which it was made clear that business owners are required to get the consent of the person in question first. Once the private data is gathered, it is cross-checked against legal records in close collaboration with the regulatory authorities.
-
State and Local Fair Hiring Laws
The aim of this law was to further streamline the employment verification process, making it convenient for both businesses and individuals. Job applicants must submit their details with the actual application in standard cases. Otherwise, companies were allowed to collect this information after getting the applicant’s consent. Collecting data without permission was prohibited, but on the applicant’s end, not providing the required information was also considered an offense, ultimately eliminating the candidate.
As these laws state, providing background information was necessary for the job applicants, and companies were free to verify those sets of information with the regulatory bodies. However, the threat of fabricated documents and stolen identity information still remains in this system. A more robust and straightforward verification solution is needed to fill this loophole.
Pre-Employment Screening with Modern Technologies
The advent of modern technologies such as pattern recognition, machine learning, and artificial intelligence has wholly transformed the employment screening processes. To begin with, companies have started to utilize applicant tracking systems (ATS) that allow them to filter job applications according to their demands. For instance, say a company requires only IT graduates. Using an ATS solution, the company can create a filter that rejects all non-IT graduates and presents only the IT graduates, helping recruiters sort the employee onboarding checklist better.
A significant contribution to the pre-employment background screening process is identity verification. Using identity verification can help businesses sort their employee onboarding process. It takes care of all of the crucial aspects of the onboarding, such as sorting the low-threat entities from the high-threat ones and maintaining all the necessary documentation.
Industries that are well-regulated and have a higher threat of financial crime usually utilize such solutions.
Identity Verification (IDV)
A robust identity verification (IDV) solution conducts accurate verifications on entities before onboarding to ensure their legitimacy. These software solutions use OCR-integrated document verification to verify the legal documents of applicants. These documents are checked for fabrication and identity theft, ensuring that it is not a shell entity being onboarded. Biometric verification, liveness detection, and address verification are also conducted, leaving no fake individuals in the application process. This is also a proactive measure against cybercriminals and scammers that can deal significant damage if left unchecked.
Financial and AML Screenings
Anti money laundering checks and transaction verifications are also conducted when a company utilizes IDV for employment screening. This is done to ensure that the applicant has no association with any financial crime or illegal financing activities. It is better to avoid entities that might be involved in any unlawful financial activities. This is because if such an employee is found to be working for a company, it can severely damage its reputation and lead to financial losses. Moreover, if the employee uses the company’s system to carry out their activities, it can further exacerbate the problem.
To help prevent these activities, IDV Solutions carries out anti-money laundering (AML) and transaction verifications on the applicants during the pre-employment verification process. The personal information gathered about the entity is verified against global watchlists and sanctions to ensure the entity has no involvement in any illegal financial activities.
Maintaining Compliance
An IDV solution also aids businesses in ensuring that the applicants being onboarded comply with the regulations of the country or jurisdiction they’re functioning in. This holistic process involves reports from all aspects of the identity verification process. These reports are checked against the standards set by the regulatory bodies, which determine if the entity is compliant.
This is done because if an entity is non-compliant, onboarding them would put the company at risk of fines and penalties.
Choosing the Right Employment Screening Partner
To maintain safe onboarding processes and ensure that no illegal entities get by, businesses must choose an identity verification solution that conducts in-depth verification of entities
Shufti is a full-scale identity verification (IDV) solution that allows businesses to verify the identities of entities accurately. With Shufti’s employment screening solutions, companies can easily navigate the complex regulatory landscape whilst onboarding legitimate customers by screening them against 1700+ financial crime databases in real time with 99% accurate results.