Blog
UK’s On-Demand Culture – Building Trust & Security with Digital ID Verification
People across the world are spending more time on the internet ever since the pandemic struck the...
 Explore More
Explore More
Blog
Politically Exposed Person – An unsaid threat to Businesses
A politically exposed person or PEP is the one who has been assigned to perform prominent public ...
 Explore More
Explore More
Blog
How AI is Transforming the Banking Sector
Artificial Intelligence has extensive applications across several domains: from banking to health...
 Explore More
Explore More
Blog
GDPR Compliance vs BlockChain Debate – Things you must know
GDPR Compliance is here to stay and it is going to be binding on every business and online enterp...
 Explore More
Explore More
Blog
Optical Character Recognition (OCR) – Powering Shufti’s Document Verification
Trust is a key factor when it comes to doing business or getting financial services from banks. A...
 Explore More
Explore More
Blog
Identity Verification – Combating Fraud in the Telecommunication Sector
Developing technology, rapid growth in digitization, and increased use of digital transactions ha...
 Explore More
Explore More
Blog
Know Your Player – Preventing Identity Fraud in Sports Events
The ongoing trend of globalizing sports activities since the last few decades has resulted in a l...
 Explore More
Explore More
Blog
A Brief Overview of the RegTech Industry [2022 Update]
The rising financial crimes have raised concerns of global regulatory watchdogs giving rise to Re...
![A Brief Overview of the RegTech Industry [2022 Update] A Brief Overview of the RegTech Industry [2022 Update]](https://shuftipro.com/wp-content/uploads/Regtech.png) Explore More
Explore More
Blog
Why Do Freelancing Platforms Need KYC?
Technological advancements came with several betterments for humans. Where every industry is bene...
 Explore More
Explore More
Blog
Digital KYC to Trace and Tackle High-Risk Customers
Customers are the assets and building blocks of any business. Customers are responsible for takin...
 Explore More
Explore More
Blog
July 2023 Recap: Major Compliance Events and How AML Verification Can Help
Anti-Money Laundering (AML) violations pose a substantial and concerning threat to the reliabilit...
 Explore More
Explore More
Blog
Shufti’s Secret to Acquiring 92% End-User Satisfaction Rate
Shufti, the global identity verification service provider, started from humble beginnings wit...
 Explore More
Explore More
Blog
Here’s to 2021 – NFTs Conquering the Crypto Market
From DeFi’s in 2020 to NFTs in 2021, a lot has changed in the crypto market. Since the beginning ...
 Explore More
Explore More
Anti Money Laundering, Artificial Intelligence, Blog
AI a Blessing – AML compliance cost reduced by $217 billion
The U.S. financial firms spend approximately $25.3 Billion in terms of compliance, risk managemen...
 Explore More
Explore More
Blog, Reg Tech
Shufti GDPR Review 2018: How we protected our clients from regulatory fines?
Shufti stands out in KYC industry not only because of its highly customizable and global iden...
 Explore More
Explore More
Blog
ID Verification for Ultimate Subscription Fraud Prevention
Cellular phones were first introduced in the consumer market in 1973 when Motorolla first introdu...
 Explore More
Explore More
Blog
Designing a Risk-free Customer Onboarding Flow for the Freelancing Industry
Freelancing websites saw an increased demand during the pandemic, and the trends continued to ris...
 Explore More
Explore More
Biometric Technology, Blog, Fraud Prevention, Identity & KYC
Multi-factor Authentication is being defeated’ warns FBI
For years, online businesses and organizations have been adopting various strategies and defense ...
 Explore More
Explore More
Blog
Impact of California Consumer Privacy Act on Online Businesses
California consumer privacy act has been revolutionizing consumer data regulations. The act was p...
 Explore More
Explore More
Blog
AML in Real Estate – Combating Property Scams at the Forefront
Real estate is deemed to be a profitable and safe business to invest in thanks to its ever-growin...
 Explore More
Explore More
Blog
Record-Breaking Fines on Banks for KYC/AML Non-Compliance
Know Your Customer (KYC) and Anti-Money Laundering (AML) compliance have been structured to make ...
 Explore More
Explore More
Blog
Safeguarding Financial Operations with Transaction Monitoring and AML Screening
To enhance the power of anti-money laundering regulation, transaction monitoring systems have evo...
 Explore More
Explore More
Blog
Know Your Investor | Understanding Which Investors to Onboard
Investor onboarding is regarded as one of the most critical stages of the business’s lifecy...
 Explore More
Explore More
Artificial Intelligence, Blog
Knowledge Based Authentication a Thing of Past
If you are wondering what is knowledge-based authentication or KBA, let me ask you a question, ‘w...
 Explore More
Explore More
Blog
Art Market in the Frame of Money Laundering
The highly volatile finance and crypto sector is not appealing for many investors, so they turn t...
 Explore More
Explore More
Blog
Identity Proofing – 7 Reasons Why Businesses Need it Now!
Modern-day cyberspace has effortlessly diminished the boundary between the real-life and digital ...
 Explore More
Explore More
Blog
Investor Onboarding | Navigating the Challenges of Digitization
Private market companies are setting their sights on retail investors and exploring technology an...
 Explore More
Explore More
Blog
Top 10 Cybersecurity Trends for 2021
Cybersecurity in 2020 became the biggest challenge thanks to the COVID-19 pandemic. Global lockdo...
 Explore More
Explore More
Blog
Anti-Money Laundering Screening – Enabling Financial Institutions to Handle Suspicious Activities
Financial crime is becoming a global concern, yet it’s often tough to spot. That is why gov...
 Explore More
Explore More
Blog
Know Your Patient – Curbing Healthcare Fraud through Identity Verification
With global digitization and emerging technologies, the healthcare sector has adopted a variety o...
 Explore More
Explore More
Blog
Significance of Facial Recognition Technology in FinTech Fraud Detection
Compliance with Anti-Money Laundering (AML) requirements is challenging for financial organisatio...
 Explore More
Explore More
Blog
ID verification prevents 8 Security Issues of businesses
The biggest concern for businesses, in terms of safety, nowadays is online or cybersecurit...
 Explore More
Explore More
Blog, Online Marketplace
Benefits of KYC services for Money Services Operators
Money service operators are at the forefront of international financial system as they help with ...
 Explore More
Explore More
Blog
Video KYC (VKYC) | Identity Verification and Fraud Prevention
In the last few years, the verification industry has experienced remarkable expansion. As our tec...
 Explore More
Explore More
Blog
How FinTech can Leverage on FINMA Blockchain Initiative?
Swiss Financial Markets Supervisory Authority (FINMA) has taken a revolutionary step in the histo...
 Explore More
Explore More
Blog
Enhancing the Effectiveness of KYC Checks with Shufti’s Forensic Document Verification
With emerging technologies and rapid digitization, identity fraud has become quite common, raisin...
 Explore More
Explore More
Biometric Technology, Blog, Online Marketplace
Face Verification Becoming Vital For Travel Industry
Over the past few years, biometric technology has become increasingly mainstream. This is due in ...
 Explore More
Explore More
Blog
Synthetic Identity Fraud: Fake Identities for Criminal Activity
An increase in financial crime has been predicted by economic downturns during the previous two d...
 Explore More
Explore More
Blog
Top 10 AML Trends to Watch for in 2022
In 2021, the increasing scope of regulatory sanctions has affected businesses globally. The use o...
 Explore More
Explore More
Blog
The Mesh of Human Behavior and Technology: CX Expert Saroni Kundu on Building Customer-Centric Businesses
No matter the industry, customer experience (CX) is key to building trust and loyalty. If you’re ...
 Explore More
Explore More
Blog
The Age Verification Advantage: Speed, Trust, and Privacy
Businesses operating in age-restricted industries like gaming, social media, and alcohol sales na...
 Explore More
Explore More
Blog
Shufti Celebrates 5 Years of Innovation in the IDV Industry
October 2022 marks Shufti’s 5th anniversary – five successful years of building trust globall...
 Explore More
Explore More
Blog
A Basic Guide to Know Your Customer Online (2023 Update)
In our current digital landscape, where identity theft seems rampant, protecting personal informa...
 Explore More
Explore More
Blog
Online Dating Scams – ID Verification Solution to the Rescue
COVID-19 exposures and its associated risks with today’s in-person meetups and traditional ...
 Explore More
Explore More
Blog, Online Marketplace
Secure Online Gaming with Digital KYC
Here is a scenario that shows the importance of having a digital KYC system integrated with your ...
 Explore More
Explore More
Blog
Solving the Cheating Problem in Online Gaming with Robust ID Verification Solution
The digital gaming and esports industry has grown at an immense pace in recent years, topping 1 b...
 Explore More
Explore More
Blog
The Crucial Role of Face Liveness Check in Fintech
Fintech firms lose approximately $51 million to scams annually. However, the cost of fintech frau...
 Explore More
Explore More
Blog
The Vicious Cycle of Money Laundering in the Gambling Industry
Money launderers opt for various channels to obscure the origins of their illegally obtained fund...
 Explore More
Explore More
Blog, Identity & KYC
Identity Verification Market ‘Hitting High Record’
The advent of technology has pushed businesses to digitize their operations for better customer e...
 Explore More
Explore More
Blog
Digital Safety for Social Media, Gaming & E-Commerce Platforms
As people and businesses are getting more and more connected online, social media continues to pl...
 Explore More
Explore More
Anti Money Laundering, Blog, Financial Crime / AML, Reg Tech
EU’s Sixth Anti-Money Laundering Directive (AMLD6)
Summary: Sixth Anti-Money Laundering Directive (AMLD6) highlights a stringent framework to combat...
 Explore More
Explore More
Blog
Facial Recognition in the Workplace: 2025 Benefits, Risks & Compliance Blueprint
Facial recognition has matured from an emerging novelty into a mission‑critical control for secur...
 Explore More
Explore More
Blog
Top 5 Ways to Improve Transaction Monitoring in Fintech
Fintech is a fast-growing sector that combines finance and technology to assist businesses and cu...
 Explore More
Explore More
Blog
Post COVID-19 – What are the alternatives to fingerprint biometrics for identity verification?
The way things are headed, there is no doubt about the fact that the world will be a different pl...
 Explore More
Explore More
Blog
Difference between KYC and AML
The growing Fintech industry leads to an increased demand for KYC and AML compliance requirements...
 Explore More
Explore More
Blog
AML Compliance – Mitigating Financial Crime Risks in the Payments Industry
After the Covid-19 pandemic gave rise to the digital payments trend, the world has seen rapid gro...
 Explore More
Explore More
Blog
Identity Verification – Safeguarding Pharmaceutical and Controlled Substance Sales
With emerging technologies, the pharmaceutical industry has transformed significantly, and rapid ...
 Explore More
Explore More
Blog
KYC Identity Verification – Building Customer Trust in Ride-Hailing Services
The transportation industry is in the phase of significant disruption, redefining its services an...
 Explore More
Explore More
Blog
A Basic Guide to Smurfing and the Role of AML in Combating It
Scammers employ various strategies to conceal illegally acquired funds, and one increasingly prev...
 Explore More
Explore More
Anti Money Laundering, Blog, Financial Crime / AML, Identity & KYC
Know Your Business-Pillar of Strength To AML Regulations
Moving in the world of technology, where every industry is going digital, there has been very les...
 Explore More
Explore More
Blog, Financial Crime / AML, Identity & KYC
Fighting Financial Crime: Why KYC and AML Compliance Is Essential for the Global Finance Sector
Banks and other financial institutions are often the first line of defense against financial crim...
 Explore More
Explore More
Blog
e-IDV: Improving Client Onboarding for Banks and FinTech
Individuals and business owners often face significant time constraints when visiting banks physi...
 Explore More
Explore More
Blog
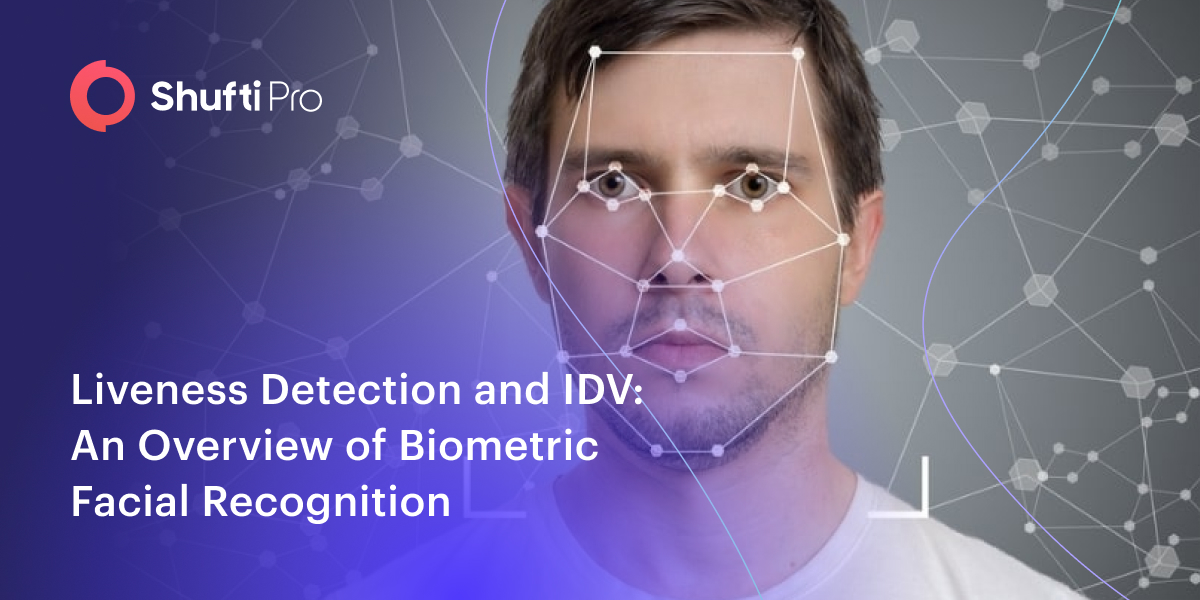
Liveness Detection and IDV: An Overview of Biometric Facial Recognition
Identity fraud and cybercrime have significantly surged in the past few years. Deepfake technolog...
 Explore More
Explore More
Blog
5 Ways Banks Can Minimize Risks In Light of KYC/AML
If you’re dealing with customers across borders, how can you safeguard your bank by ensuring that...
 Explore More
Explore More
Blog
KYC ID Verification – A Critical Component for Securing Online Dating Activities
Social manipulation in online dating platforms targets numerous users and their personal informat...
 Explore More
Explore More
Blog
Wholesale or Retail CBDCs? Settling the Endless Debate
The world is now moving towards digitisation at a faster pace than ever. The payment systems have...
 Explore More
Explore More
Blog
5 Key Questions About KYC Compliance to Look Out for in 2021
With the COVID-19 pandemic bringing challenges every day for businesses, the rate of identity fra...
 Explore More
Explore More
Blog
Building an Effective Customer Due Diligence (CDD) System with Shufti
There are various factors that businesses have to consider while implementing measures to gather ...
 Explore More
Explore More
Blog
A Brief Overview of KYC Requirements for Foreign Exchanges in EMEA
The forex industry is recognizable for being a dynamic and profitable platform due to its high li...
 Explore More
Explore More
Blog
How to Design an Effective Client Lifecycle Management (CLM) System with ID Verification
The customer journey with a business is very comprehensive. It does not end once the customer is ...
 Explore More
Explore More
Anti Money Laundering, Blog, Financial Crime / AML, Reg Tech
EU’s Sixth Anti-Money Laundering Directive (AMLD6)
Summary: Sixth Anti-Money Laundering Directive (AMLD6) highlights a stringent framework to combat...
 Explore More
Explore More
Blog
Identity Verification | A Complete Guide to Compliance and Risks
The United Nations says $2 trillion is laundered globally every year. Of that, less than 10% is d...
 Explore More
Explore More











![A Brief Overview of the RegTech Industry [2022 Update] A Brief Overview of the RegTech Industry [2022 Update]](https://shuftipro.com/wp-content/uploads/Regtech.png)