What is Replay Attack and How Businesses Can Prevent It in 2026

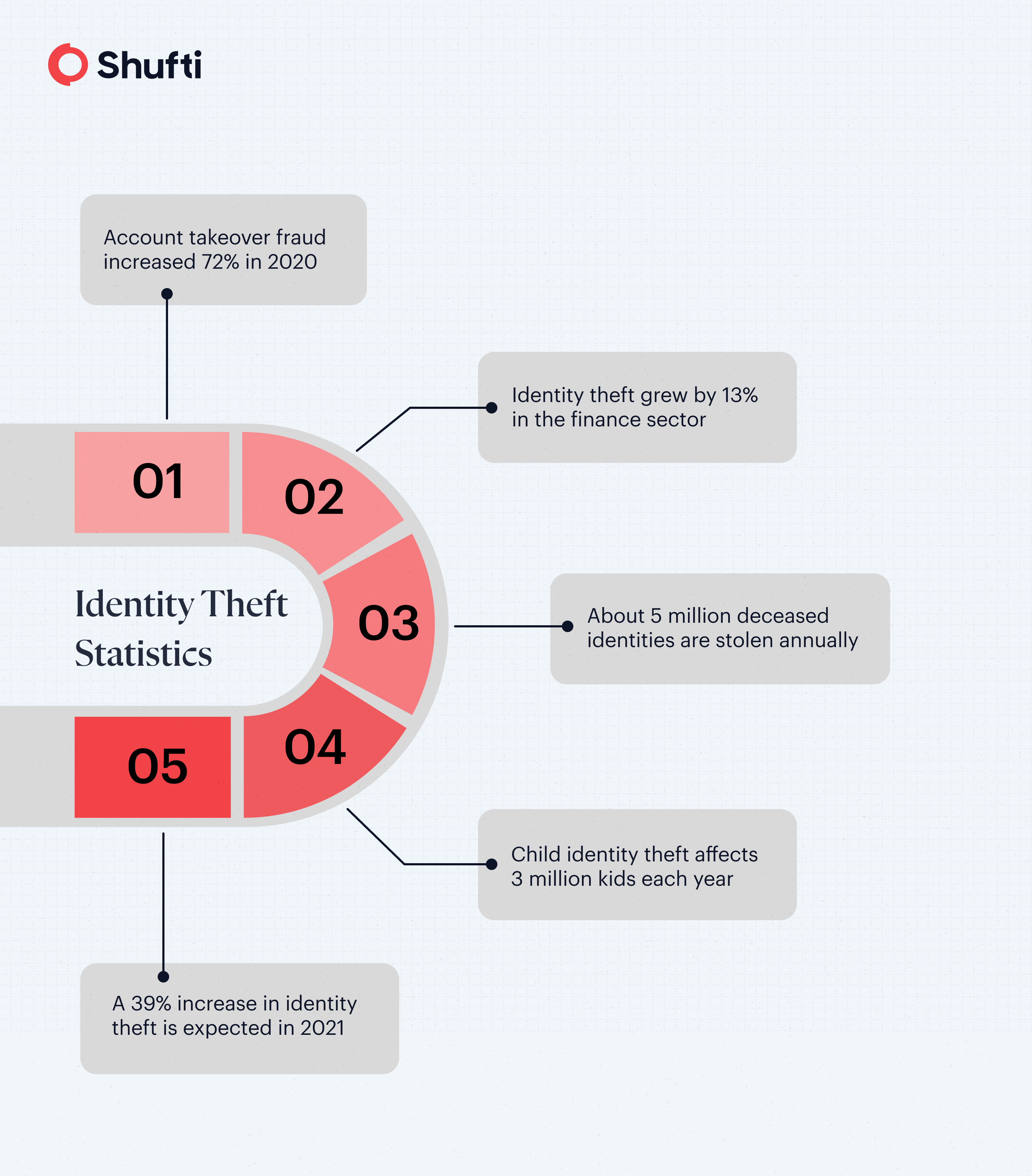
As businesses embrace digital tools and online solutions, life has become more convenient than ever. Unfortunately, cybercriminals are taking advantage of these advancements for their own gain. Over the years, frauds like identity theft, account takeovers, spoof attacks, and deep fakes have already caused headaches for many organizations. In 2020, another type of fraud surfaced called replay attacks, posing a new challenge for businesses trying to stay secure.
A report from Comparitech shows that 80.7% of surveyed organizations experienced successful cyberattacks. While replay attacks were rare before, the pandemic created opportunities for fraudsters, leaving many businesses unprepared. These attacks have already caused significant financial losses, making strong replay attack prevention more important than ever.
What is a Replay Attack?
Replay attacks occur when fraudsters submit the same information multiple times in different ways to manipulate systems or bypass verification. For instance, a fraudster may submit the same identity document repeatedly, changing one or two details each time. In the digital world, these attacks are increasingly sophisticated and difficult to detect, making them a serious threat in replay attack in cyber security.
Examples of Replay Attack
Given below are some of the replay attack examples, which help in a better understanding of how fraudsters attack in real scenarios:
- Submitting the same government-issued ID multiple times with minor changes, like a different date of birth or name.
- Reusing authentication tokens or login credentials to access accounts fraudulently.
- Exploiting OTPs or session information from previous transactions to mimic legitimate users.
How Do Replay Attacks Work?
With rapid digitisation, replay attacks have taken the virtual road as well. Digital replay attacks are extremely sophisticated because there are different methods of perpetrating the attack. The different methods target a wide range of devices and networks. Here are the three main ways through which a replay attack occurs.
Changing the Device Information
In the virtual world, tracing the IP of the device is not a problem anymore. This means fraudsters can be easily detected when submitting the same information over and over again. For a successful replay attack, criminals change the device information, like the IP address, to make sure they are not being tracked. They might use a different device or mask their IPs when doing so.
Different Network Information
This is the second way of successful replay attacks. Using the same network can help organisations to identify replay attacks in no time. To stay hidden, fraudsters use different network information, such as a different internet connection or mobile data, for submitting the same data multiple times.
Fraudulent Information for ID Verification
As stated earlier, fraudsters change a piece of information in the documents to perpetrate a replay attack. For instance, once a fraudster changes the date of birth, and the next time, he uses a different name and submits the same document.
Industries Targeted by Replay Attacks
Certain industries are particularly attractive to fraudsters because of the financial, personal, or strategic value they hold. Here are some of the main industries that are frequently targeted by replay attacks:
- Financial Services: Banks, fintechs, and payment gateways are prime targets due to the direct access to money and accounts.
- Healthcare: Fraudsters exploit patient records, insurance claims, and telehealth authentication systems.
- E-commerce: Replay attacks manipulate account logins, gift cards, and transaction approvals.
- Government & Defense: Sensitive government portals or secure communications may be exploited by replay attacks to gain unauthorized access.
Advanced Techniques to Prevent Replay Attacks
Protecting against replay attack detection requires advanced security measures and the smart use of technology. The following techniques can help businesses reduce risk and block fraudulent activity:
One-Time Passwords (OTPs)
Using dynamic, single-use passwords ensures that intercepted credentials cannot be reused.
Nonce Values
Randomized numbers (nonces) in communication prevent replaying old messages in digital protocols.
Digital Signatures
Encrypting and signing messages verifies authenticity and prevents attackers from resubmitting captured data.
Secure Routing and Communication Protocols
Protocols such as TLS and HTTPS encrypt data in transit, making replay attempts much harder.
VPN
Using VPNs can help secure connections and reduce the risk of replay attacks originating from untrusted networks.
Replay Attack Prevention Practices
Successful replay attacks continue to cause account takeover fraud and identity theft. As digital replay attacks remain a serious and evolving threat for businesses in 2025, investing in advanced prevention solutions is more critical than ever. Fortunately, there are various solutions that can secure your business from replay attacks. Take a look at some of these solutions:
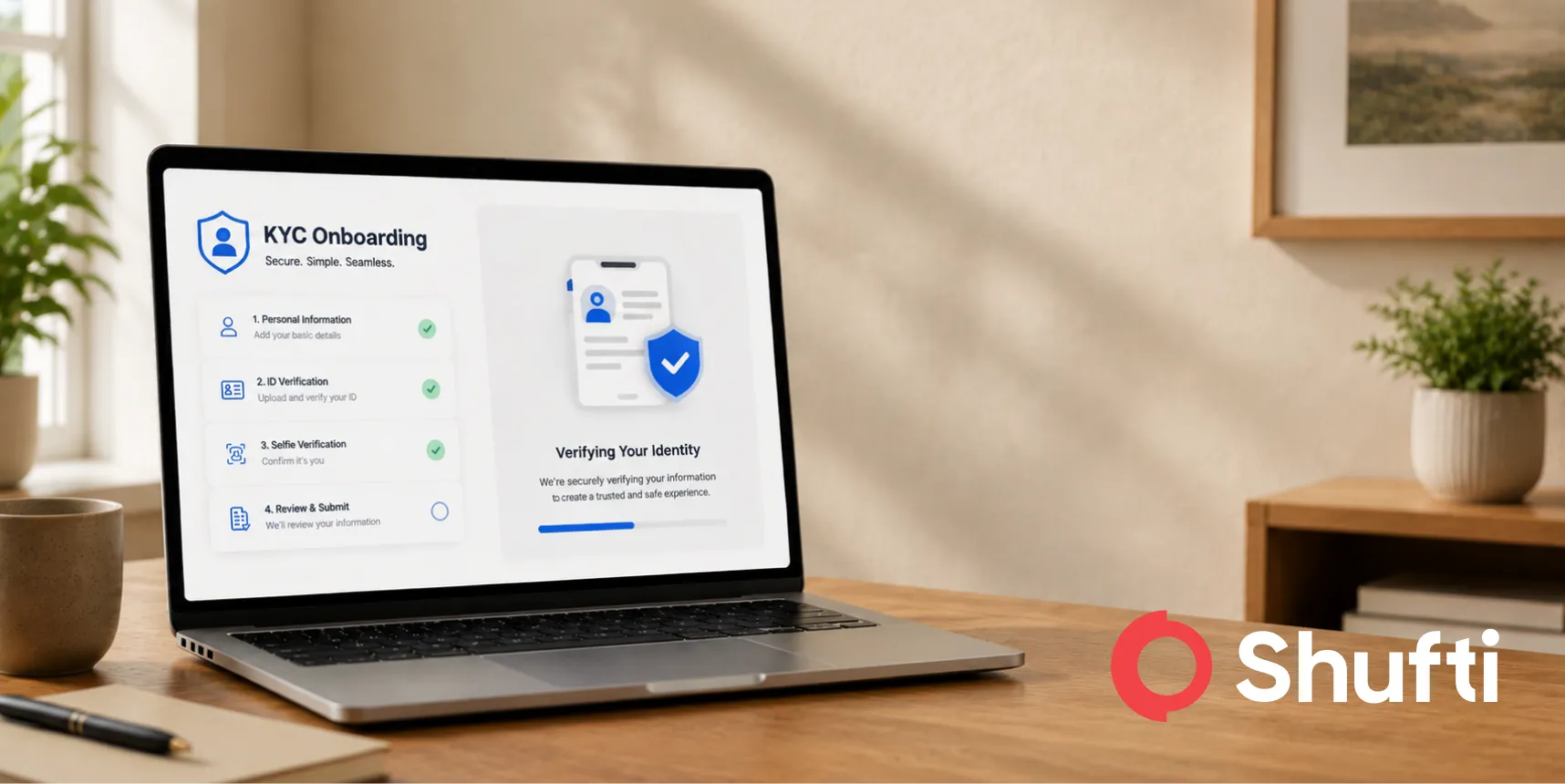
Track Customers’ Response Time
First, be sure to track the time your customers take to respond. Legitimate en-users only take a few seconds to upload a selfie or government-issued ID documents. On the contrary, perpetrating a replay attack requires time. Fraudsters require some time to change details within the same document. If your customer is taking a lot of time to respond, perform more robust checks on the documents previously submitted. You can opt for a face verification check as well, or video KYC can be an all-in-one solution.
Geolocation Assessment
As mentioned earlier, fraudsters use different location details for replay attacks. With the help of a geolocation assessment, you can trace the location that is being used during verification. In case the customer jumps to several different locations within the same verification session, there might be a replay attack in the pipeline.
Biometric Authentication
Performing biometric authentication checks is one of the ideal ways to combat replay attacks. You can perform face verification checks or other liveness detection checks to ensure that the user is physically present at the time of verification, rather than a fraudster planning spoof or replay attacks on the other end. For better security, you can add extra biometric checks to bring friction to the fraudsters’ processes.
How Shufti Strengthens Defence Against Replay Attacks?
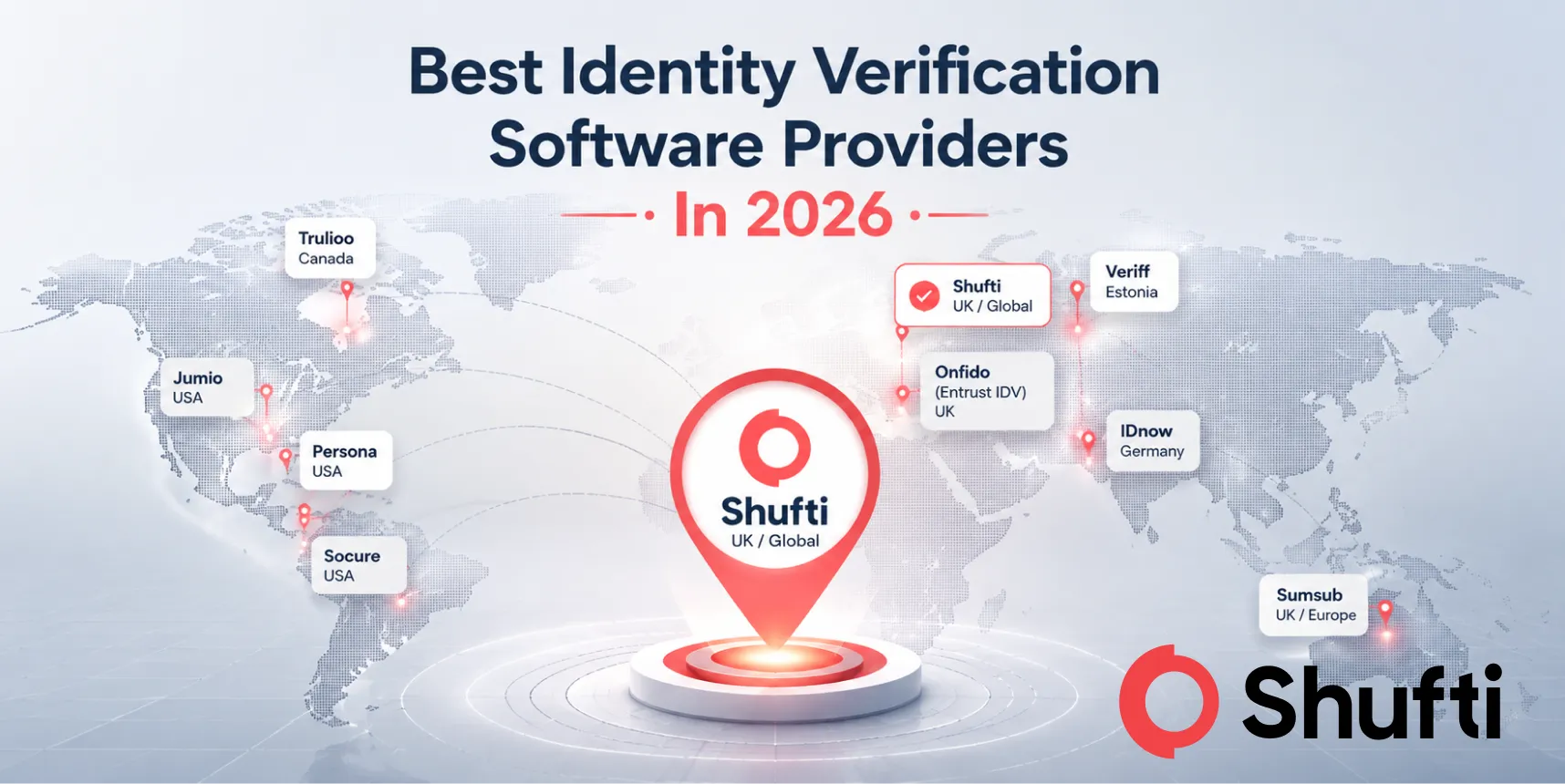
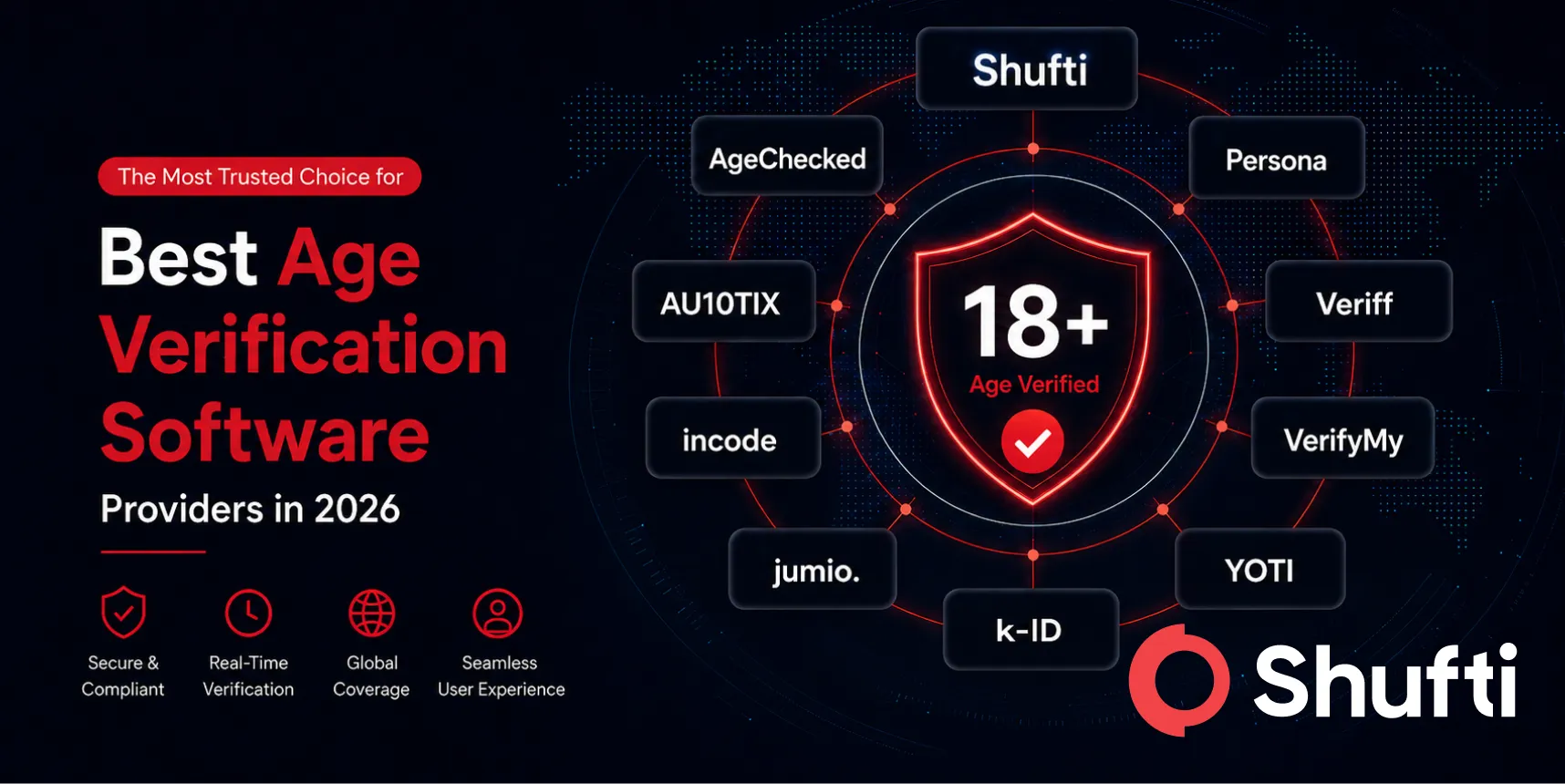
When it comes to protecting your business from fraud like replay attacks, having a comprehensive AML and identity verification platform is essential. Shufti offers an integrated suite of AI‑powered tools that help detect risks at every stage of the customer journey, from onboarding to ongoing monitoring.
Its platform combines real‑time document and biometric verification with continuous AML screening against global sanctions, watchlists, and PEP lists, giving you deeper visibility and stronger fraud protection.
With customizable risk scoring, identity‑aware screening, and seamless API integrations, Shufti helps reduce false positives while improving compliance workflows. Whether you are safeguarding financial services, healthcare, e‑commerce, or government systems, its tools work behind the scenes to identify suspicious activity and prevent fraudulent access.
Request a demo to see how Shufti can help secure your business with advanced replay attack and AML prevention.