Risk Assessment – Building Trust in Financial Institutions

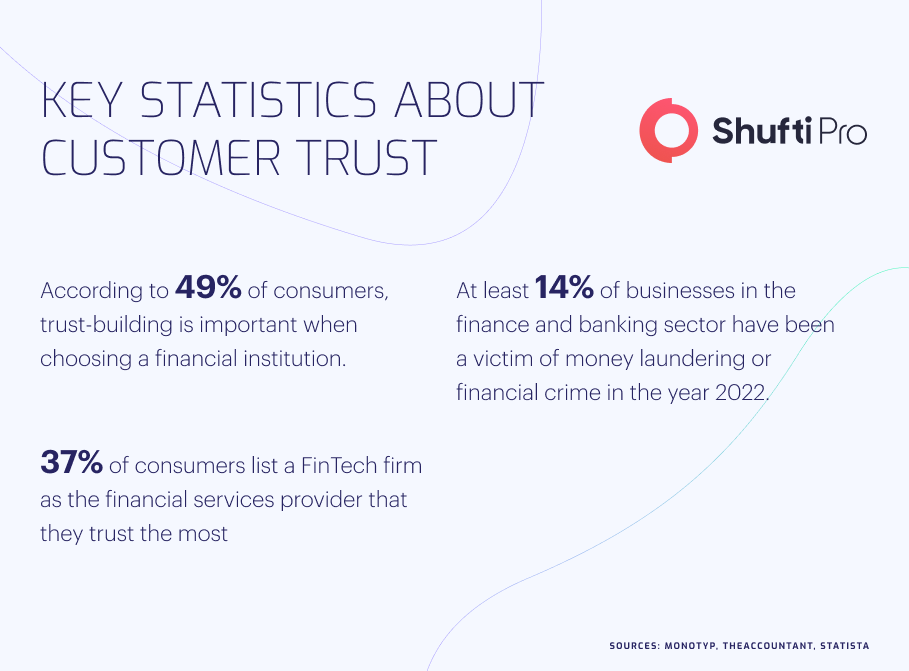
For financial institutions to hold onto their customers, they must build and conserve advanced levels of trust in the products and services they provide. In the US alone, consumers reported losing more than $5.8 billion in 2021, which is 70% more than in 2020.
Terrorist financing, money laundering, and financial fraud are some common crimes linked to financial institutions, particularly banks, insurance companies, and crypto firms. Risk assessment is the latest technology that can help companies to establish trust by evaluating customers’ risk factors and genuine client onboarding.
Prerequisite for Trust Building in Financial Institutions
Customer identity has always been the top priority in financial services organizations, without which cybercrime cannot be minimized. In 2021 alone, there were 5.8 million fraud complaints registered by US citizens, which has raised the need for a system based on risk assessment of customers.
1. Security
In a highly digitized world, consumers are asked to build trust in innovative and more profound ways by providing more personal information online. This has elevated the hacking instances, and customers are facing severe threats of identity theft and other financial losses. Through a proper risk assessment system by onboarding genuine clients while keeping fraudsters away.
2. Personalization
The growth of electronically programmed services escalated the level of personalization consumers anticipate from their financial services ally. Technologies like artificial intelligence are making personalization highly feasible. Through risk assessment, financial organizations can ensure safe client onboarding and minimize the chances of fraud.
3. Radical Transparency
Providing customers with all the pertinent information about accessible products and services not only assists them in making suitable financial conclusions but also builds trust in financial firms. Monetary institutions should reveal what customers need to acknowledge and stay away from misleading information and marketing.
How Law Enforcement Authorities are Countering Cybercriminals
Law enforcement authorities across the globe are working tirelessly to counter criminal activities by legislating and implementing stringent governmental laws. In the recent past, several cases have surfaced, urging the authorities to implement a risk assessment-based system to identify criminals while onboarding:
Gang Arrested for Stealing €12 Million from US-Based Banks
Spanish National Police, along with the US Secret Service, dismantled a gang of 105 criminals who are suspected of being involved in fraud and money laundering. The operation was conducted with the collaboration of Denmark, Austria, and Greek law enforcement authorities, which is still ongoing to arrest more criminals.
It was found during the investigation that criminals, through several fraudulent activities, managed to steal €12 million from the users and further laundered this illicit money to other countries. Police are still working to find more whereabouts of the gang, and cases against all of them are pending in court.
Spanish Police Dismantle Europe’s Largest Criminal Gang
Law enforcement authorities in Spain arrested one of the largest criminal gangs in Europe, which was involved in a large number of cybercrime cases and money laundering. Spanish Police conducted a giant raid along with the cooperation of Europolice in different countries and dismantled the whole gang.
It was found during the investigation that criminals managed to launder €200 million to other countries using multiple channels. Not only has the illegal money been confiscated, but a huge quantity of drugs have also been discovered in the residence of criminals.
Curbing Financial Fraud through Risk Assessment
Customer risk assessment is a technical process used to verify customers’ true identities by implementing stringent verification checks, including questionnaires, data points for fraud prevention, and other risk parameters. FATF also recommends all these screening measures through which client onboarding can be made secure.
An efficient risk assessment system has all the necessary checks which criminals cannot bypass. It obtains detailed customer information with multiple answer types while leaving no space for bad actors. Due to rapid digitization, a large number of financial institutions are implementing risk assessment systems which is not only securing their onboarding process but also helping customers to avoid financial losses.
There are multiple checks involved, which help companies get information related to their customers’ identities, geography, and businesses. In this way, an efficient risk assessment system leaves no room for fraudulent activities while also screening the customers’ details against the global sanctions list by financial watchdogs.
Imperatives of Risk Assessment
There are a lot of verification checks involved in the risk assessment, which are generally considered enough to verify the true identities of customers and report to authorities in case of any suspicious activity. Here are the significant checks which are associated with the risk assessment process:
1. Evaluating Email and Phone Numbers
Most initial verification is related to email and phone numbers which are performed to make sure that the customer or the company has genuine details. Once the customer clears this stage, the system puts them under the next verification, and in this way, the individual is removed or otherwise reported to law enforcement authorities.
2. Verifying IP Address
The IP address is one of the major reasons through which criminals take advantage of the system to defraud customers. They make fake accounts and IDs to get registered for banks, insurance companies, and crypto firms and inflict financial losses on sophisticated users.
3. Sanction Screening of Customers
The customer risk assessment also involves screening customers against the global sanctions lists, which financial watchdogs like FATF, Interpol, and the European Union generally accumulate. If the users’ data are matched with the one in the sanctions lists, the system is efficient enough to report it to the law enforcement authorities to take strict action against them.
Key Takeaways
Cybercrimes have become quite prevalent nowadays, which has increased the risks of a large number of crimes like identity theft, money laundering, and terrorist financing. Risk assessment is an efficient system that contains all the necessary verification checks to verify customers’ true identities while leaving no room for criminals.
Shufti’s risk assessment services are an ideal option for financial institutions as they can verify customers and businesses through the most advanced checks, including dynamic questionnaires, multiple risk parameters, and data points for fraud prevention. Powered by an AI algorithm that is getting smarter over time, Shufti’s risk assessment system completes verification in seconds with a ~99% accuracy.
Want to know more about the customer risk assessment system?