Securing Business Operations with Risk Assessment

- 01 What is Risk Assessment?
- 02 The Crucial Elements of Risk Assessment
- 03 What is a Risk-Based Approach?
- 04 Business Risk Analysis – The Processes of Ensuring Secure Operations
- 05 Effective Risk-Based Approach to AML
- 06 Risk Assessment - A Luxury or a Necessity?
- 07 Minimise Business Risks with Shufti
The increasing connectivity and dependence of the world on technology have led to a rise in sophisticated cyber crimes. Money laundering and terrorist financing are two ways fraudsters hide their illicit funds’ origins. They take advantage of a variety of techniques and instruments to evade laws and financial system restrictions. Nonetheless, governments do not just observe from a distance. Money laundering and terrorist financing are illegal in the majority of contemporary countries. Additionally, they have granted financial institutions and authorities the flexibility and resources they require to reduce risk.
According to a new ISACA study, more than half (52%) of cybersecurity experts report that there has been an increase in cyberattacks over the past year. Companies are failing to assess cyber risk despite the rise in attacks frequently; only two out of five (40%) and less than one in ten (8%) of organisations undertake cyber risk assessments on a monthly basis.
What is Risk Assessment?
A risk assessment is an orchestrated or streamlined procedure that identifies and evaluates any risks related to the company and then puts workable control measures in place to reduce or eliminate those risks. The digital industry depends on preventing identity fraud, and this is the ideal time for companies to engage in risk screening practices. Businesses can fight financial fraudsters and maintain compliance by using risk assessment.
The Crucial Elements of Risk Assessment
A company may face a range of risks, but being ready for everything might provide them an advantage over competitors, particularly in the event of an unforeseen circumstance.
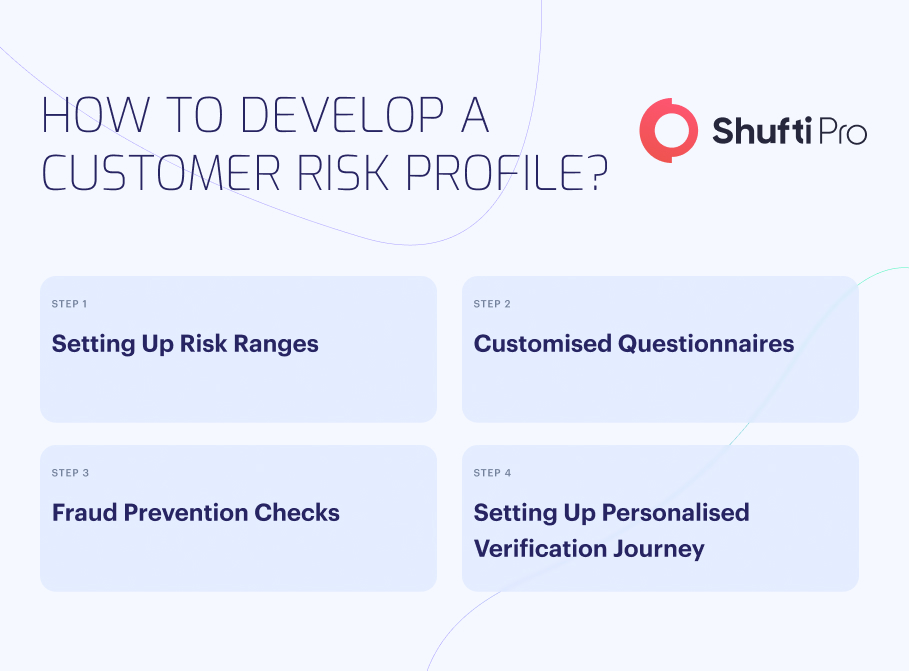
Customer Risk
A component in the client onboarding process called “customer risk assessment” entails a thorough analysis of the possible risks that a new customer may provide. By assessing consumer data and adopting the necessary safety measures to safeguard business operations, businesses can develop risk profiles that are based on risk levels.
Customer risk scores aid companies in assessing the possibility of committing crimes such as money laundering and terrorism financing. Conversely, if regulatory bodies unearth suspicious consumer activity, the company can face heavy fines, harm to its brand, and permanent expulsion from the business world.
Any business that works with renowned clients, such as politicians and actors or other high-profile individuals, may pose a risk of affiliation or involvement in money laundering. These individuals could be attempting to evade paying taxes to the government, or they could be blackmailed. Being aware of possible issues with these politically exposed people (PEPs) to assess potential risk is essential more than ever.
Having too many transactions with foreign companies is always a warning sign, particularly if those are nations with weak financial regulations. One method of violation of AML enforcement that has previously worked is money laundering through offshore accounts.
Customers with a suspicious background, a history of suspect transactions, or no clear source of money should be carefully evaluated by businesses. They inevitably pose a risk to business’s efforts to comply. Hence, risk assessment is not just a recommendation; it is a legal necessity.
Geographical Risk
A mere few countries have loose AML and other cyber regulations, which gives criminals the freedom to commit crimes without worrying about being caught. Numerous countries have been placed on the FATF’s grey or black lists, meaning they are all susceptible to financial fraud. The risk assessment process looks at the origins of the clients and establishes the level of AML regulation enforcement. It not only finds companies (or associated people) in high-risk countries, but it also finds device locations, internet proxies, and secret web browsers.
When clients conduct business in specific regions, companies should examine their activities more thoroughly. Whilst some people invest overseas merely to pay legally reduced taxes, several nations are classified as having high levels of financial crime, particularly high levels of drug trafficking and money laundering.
Business Risk
The risk assessment evaluates whether the client engages in risky activities. Additionally, it validates the users and enterprises against possible risk. To ensure that companies interact with low-risk partners and are kept under observation going forward, the risk is analysed, documented, and reported.
Customers or businesses who exhibit high levels of risk or suspicious financial activity could pose a significant threat to the company. As a result, businesses should evaluate this regularly and adjust their AML risk assessment process as necessary.
What is a Risk-Based Approach?
The G7 countries established the Financial Action Task Force (FATF), an intergovernmental body, to fight money laundering globally. A set of guidelines for countries to prevent domestic money laundering was released by the Financial Action Task Force (FATF) in 2012. The concept of risk-based methods for anti-money laundering served as the foundation for the FATF’s recommendations.
Banks and other financial institutions must carefully evaluate any potential threats they may encounter to comply with risk-based methods to AML. For firms to do this, they must know their customers. It implies that businesses need to get comprehensive information about the business practices, sectors, and traits of both current and potential clientele. With this information, they will be better able to respond swiftly and efficiently to possible issues.
Business Risk Analysis – The Processes of Ensuring Secure Operations
A rigorous set of guidelines or procedures is used in a state-of-the-art financial risk assessment approach to evaluate and mitigate potential future risks that a company may face. A business’s financial risk assessment approach needs to comprise the following five phases.
Assess Risks
Different forms of risk are faced by different corporations based on their reserves, industry, location, and cash flow. The financial or regulatory department of the company should be aware of the dangers it is likely to encounter. To ascertain the level of risk, the executive members must start a risk assessment service if an unknown scenario or potential risk is identified.
Document the Risks
The primary goal of a company’s risk assessment should be to identify the worst-case scenario, the likelihood that it will occur, and the necessary steps to recover from any potential financial loss.
Effective Management Procedures
When a company needs to implement risk management measures, businesses should be available to oversee and manage the risk-handling process. Transparency and departmental cooperation will increase under the direction of a knowledgeable and experienced risk assessment solution.
Use Strict Measures
Implementing a rigorous risk management system can make it very easy to take action against a client or partner who engages in fraudulent activity. Transaction patterns and funding sources are detected when a risk is recognized for a financial crime, such as money laundering or terrorism financing. Risk analysts can identify such suspicious behaviors before the crime is committed.
Track Progress
Once the risk assessment and management process is complete, monitor the company’s ongoing operations. However, if the risk is mitigated, continuous assessments will ensure that new variables do not compound the risk resulting from the initial situation.
Effective Risk-Based Approach to AML
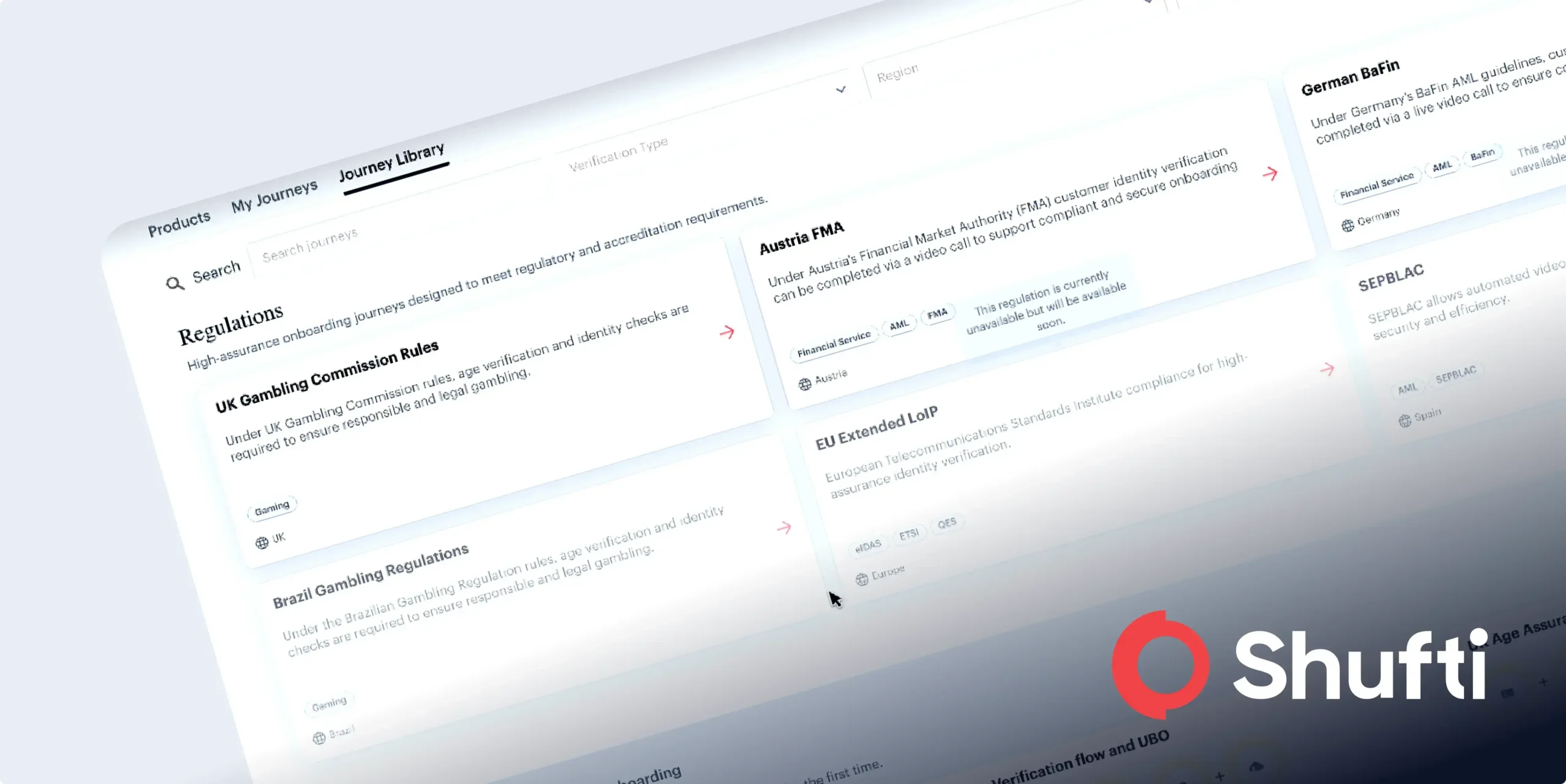
Know Your Customer (KYC) Guidelines
KYC verification calls for a client’s identification and business claims to be verified by a financial institution. Aside from more specific financial data, the information acquired may also contain basic identity details like name, birthdate, address, and identification number. With the aid of all this data, the financial institution will be able to anticipate any risk related to the customer in more depth.
Screening of Watchlists
Screening customers for PEPs, sanctions, adverse media coverage, and other watchlists is part of a risk-based strategy.
Advanced Solutions
Modern financial institutions will require the most recent developments in AML technology if they are to remain ahead of potential threats, risks, or fraud. Risk assessment may now be completed more quickly and successfully due to the advanced technology.
Risk Assessment – A Luxury or a Necessity?
It is not an option to tackle anti-money laundering from a risk-based perspective. It is essential. Hence, risk assessment, in the era of digitisation, is a necessity, not a luxury. Cutting off money to terrorists, traffickers, and other criminals is the best method to deal with them in today’s digital and always-linked world. Furthermore, risk-based AML strategies make it easier than ever for financial institutions to accomplish this. It is obvious that a risk-based strategy is required. A risk assessment protects businesses from financial criminals’ money-laundering operations. Businesses face a major risk to their financial stability and reputation if they don’t have a plan in place.
Minimise Business Risks with Shufti
Following KYC laws and rules is a difficult task. Staying ahead of the market dynamics demands time, effort, strategy, and a step in the right direction because they are evolving quickly. Businesses are aware that it can be challenging to stay up to date with the ever-evolving fraud risk. Shufti‘s risk assessment solution helps companies comply with industry standards in this situation.
Organisations must verify every candidate with a risk assessment solution. Our risk assessment solution guarantees that every new client undergoes a thorough procedure. To reduce the threat of being compromised, companies and individuals are scanned against more than 1,700 watchlists to safeguard their finances and reputations.
Finding it hard to assess risk whilst maintaining compliance and securing operations?

 Explore Now
Explore Now