What is an OCR Screening and How Does it Work?
In our digital environment, where automated technology has already taken over corporate processes, there is a growing demand for quick and efficient identity verification processes. An online KYC check uses artificial intelligence technology to detect fraud whilst also assisting organisations in meeting compliance, minimising friction, and unnecessary delays from onboarding operations. The rising requirement for firms to meet regulatory obligations has resulted in a variety of challenges for enterprises online.
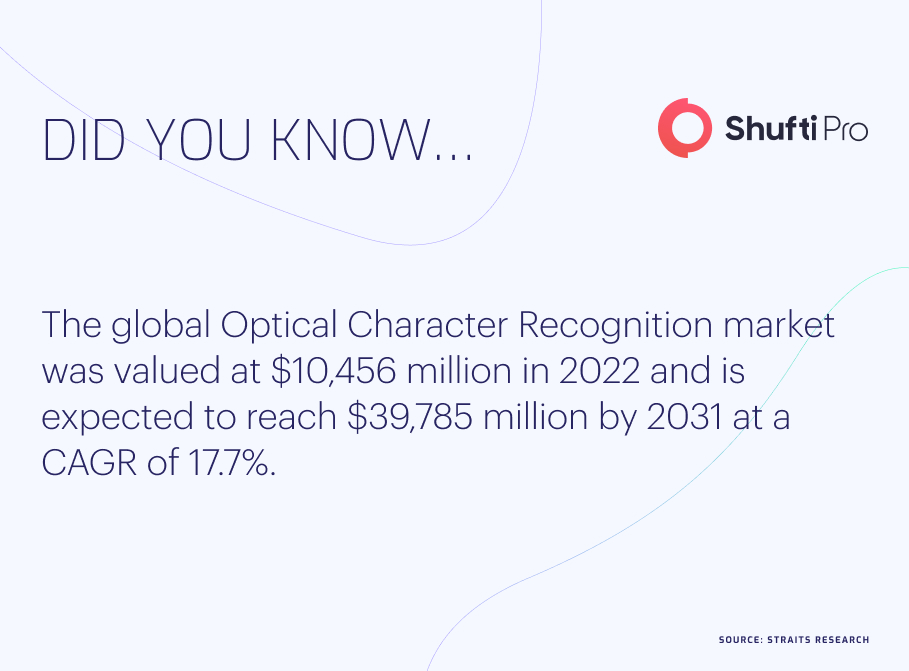
The advancement of OCR screening technology has enabled businesses to employ it for effective verification. According to one report, Optical Character Recognition (OCR) technology is predicted to reach $27 billion by 2020 at a CAGR of 15%. Learn what an OCR screening is and how it works.
What is OCR?
A text photograph is converted into a machine-readable text file using an Optical Character Recognition OCR tool. When an individual scans a billing document or a receipt, for example, the computer saves the scan as an electronic file. They cannot use a text editor to modify, search, or measure the alphabets, numeric digits, or content written in the picture file. A written file, on the other hand, can be transformed from a picture to a text file that contains the image’s content.
What are OCR Screening and IDV Processes?
An identity check in the current day entails digitally validating a potential employee’s Name, birth date, residence, nationality, and so on. This entails the use of different technologies to combat fraud, comply with rules, and reduce the Optical Character Recognition manual labour necessary for in-person verification. Using technologies such as (OCR), picture rectification, blurring detection, spoofing, and others, identity verification can be completely automated, making it quick, reliable, and time-efficient.
Why is OCR Reader Important for Businesses?
The primary benefit of the OCR reader is that it streamlines finding text, editing, and storing, simplifying data entry. OCR allows businesses, individuals, and other organisations to save files on their desktops, laptops, tablets, and other devices, ensuring continuous access to all paperwork or documents.
Friction and unnecessary delays can have various consequences, with customer experience being one of them. Consider creating a bank account where the user satisfaction standards are extremely high. To do so, an array of client data is necessary to authenticate identity, which might require several days to process if done manually. However, in today’s fast-paced world, the account opening procedure must be quick and clear, with no surprises. This is where OCR technology may help by customising procedures to meet the needs of clients.
Optical character recognition is a method of transferring handwritten or printed texts into digital versions. The efficiency of an OCR scanner is determined by the text quality and the operation of the system or technology. Because neural networks can localise symbols, language, and characters, organisations can extract information from documents in real-time.
Standard optical character recognition OCR system rely on system designers to make decisions; nevertheless, neural nets, artificial intelligence, and machine learning algorithms that replicate the statistical behavior of the human mind make decisions in AI-based OCR scanners. These models are developed on millions of data points; the larger the data collection, the more accurate the model.
What Technology Lies Behind OCR?
OCR Technology is a process that converts numerous types of documents into configurable and accessible data, such as digitised paper documents, PDFs, or photographs taken with a camera phone.
In scanners, a raster image consists of a series of black-and-white or coloured dots that reflects the document. To retrieve and reuse data from document photos, camera pictures, or image-only PDFs, businesses will require OCR software. This programme will choose letters in the picture, turn them into sentences, and then sentences into expressions, allowing businesses to access and change the information from the original letter.
Organisations can utilise OCR to scan and recognise identity papers, particularly when AI and machine learning algorithms are used. It can detect complex ID documents, for example, despite variations in form and structure. Using OCR to extract data from ID papers eliminates human mistakes and other safety risks, assisting in AML/KYC compliance.
What is the Process of OCR?
Organisations can scan and recognise documents using OCR, especially when AI or machine learning algorithms are applied. It can detect complex ID documents, for example, despite variations in style and layout. The OCR programme operates in the following manner:
Image Collection
Documents are scanned and converted into binary data by a scanner. OCR software analyses the scanned image, identifying the light sections as a background and the black or shadow areas as text.
Pre-Processing
The OCR programme cleans and rectifies the image before it can be read. Documents are initially transformed into images, such as recorded images, by technology. The main aim of this stage is to make the machine’s reading as accurate as possible whilst also removing any unwanted delays and friction. The design is then converted to a black and white representation and analysed for light and dark parts. Using an OCR technology, the image is then split into distinct elements such as worksheets, text, or embedded graphics.
Recognition of Text
The two basic types of OCR techniques or software processes used by an OCR programme for recognising texts are pattern matching and feature extraction.
Pattern Recognition
A word in an image, known as a glyph, is compared to another similarly recorded glyph in a pattern match. The cached glyph must have the exact same typeface and dimensions as the input glyph for pattern recognition to work. This method works well with scanned copies of documents typed in a familiar font.
Extraction of features
Feature extraction divides glyphs into features such as lines, enclosed loops, line orientation, and line intersections. It then uses these qualities to find the best fit or closest neighbor from the various glyphs it has saved.
Post-Processing
Following processing, the technology converts the retrieved text data into an electronic file. Some OCR systems can provide annotated PDF files that contain both the initial and final versions of the photographed material.
The Benefits of OCR Technology
Some of the benefits of adopting OCR technology are as follows:
Increased Speed
Compared to the time-consuming and laborious manual document verification approaches formerly used by organisations, OCR-based document verification is significantly more efficient for organisations. Many consumers are said to leave organisations that need lengthy verification processes. By automating the data collection process, OCR technology, on the contrary, eliminates these potential risks for organisations.
Reduced Expenses
Because the OCR process reduces the need for human labour, businesses may be able to run their businesses with fewer workers. The corporation’s expenditures may be significantly reduced if fewer staff members concentrate on document verification for clients. Staff can additionally be used for other vital tasks.
Enhanced Storage
Businesses face more than only the issue of collecting and streamlining client data. They must also preserve and protect the sensitive data of their clients. By removing the need for paper records, OCR also enhances data management. The information is recorded digitally and can be safely stored for as long as the firm desires.
How Can Shufti Help?
Shufti, a pioneer in providing verification services, employs OCR technology as the foundation of the client identification procedure. Businesses can use automated OCR-powered KYC systems to evaluate if the identity data is valid or if criminals are trying to distort the verification system. Shufti’s powerful OCR technology is combined with artificial intelligence (AI) algorithms, allowing it to extract text from identity records in real-time. To authenticate the customer’s identity, our system allows customers to use their smartphone’s camera to snap real-time photos or simply upload previously obtained images. Rest assured, OCR-based KYC verification works flawlessly.
Still wondering how OCR screening is implemented, how it works, and whether your business can implement it?