Biometric Authentication: The Importance, Use Cases & Myths

Today’s business owners rank security among the highest priorities. As hackers continue to develop methods to circumvent even the most advanced security systems, it remains challenging for businesses to keep sensitive data, customer information, and trade secrets safe. Many companies have switched to biometric technology like fingerprint scanners and facial recognition software since traditional security methods like passwords and knowledge-based authentication have been shown to be vulnerable.
In 2022, more than $16 billion records containing passwords, personal and financial information have been disclosed on cybercriminal forums. According to IBM, a data breach may cost an organisation an average of $3.86 million, though others have been much more costly. For context, it is believed that the whole cost of the Equifax breach in 2017 was $700 million, while the total cost of the Marriott breach in 2018 was over $200 million. Let’s pretend these scary numbers aren’t enough to convince businesses to improve authentication procedures. In this scenario, rules such as Europe’s Payment Services Directive 2 (PSD2) are hastening efforts to implement Multi-factor Authentication.
Deep Dive into Biometric Authentication
Biometrics is a form of security that uses an individual’s distinct physical characteristics to confirm identification. These include things like fingerprints, iris scans, retinal patterns, and facial recognition. When a user attempts to log in to a system or enter a restricted area, the biometric data is used to swiftly and accurately validate the person’s identity. Biometric authentication is often more secure than conventional authentication methods since it relies on information that is highly specific to each individual.
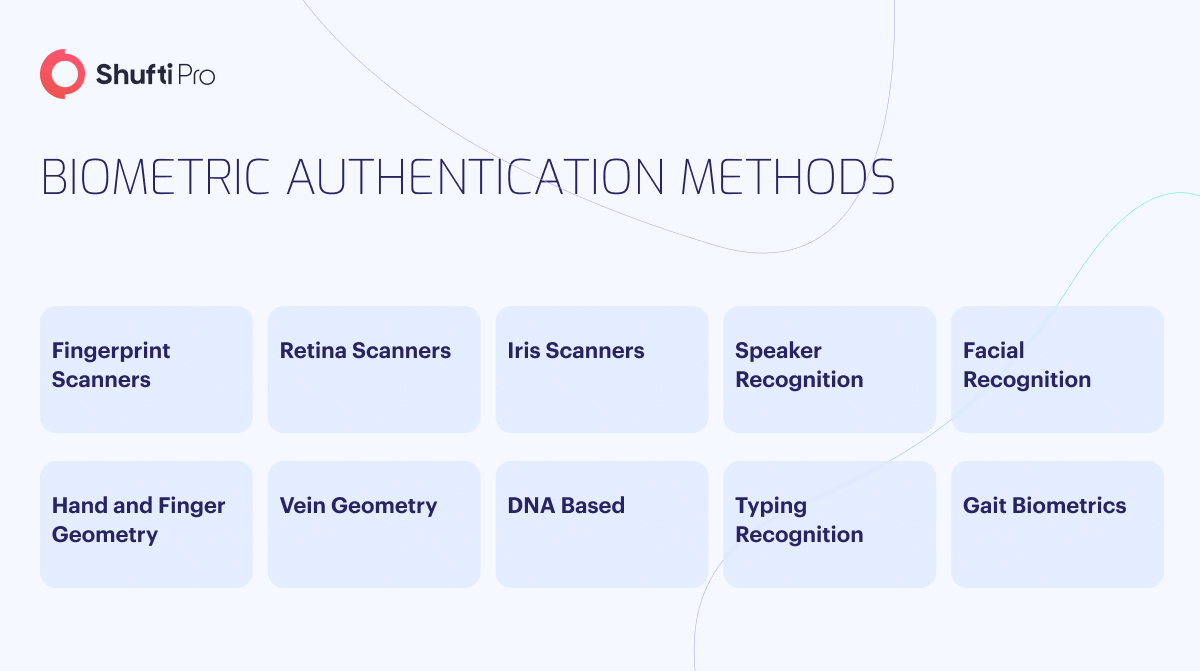
Biometric user authentication is typically used to enter a protected online account or open a locked door or gate. Still, it is increasingly being integrated into everyday electronics as well. Private corporations and government agencies still use biometric authentication technologies at checkpoints and border crossings. The following are examples of widely used biometric user authentication methods:
Facial Recognition – This system compares the user’s face to a database of pre-verified faces based on various measurements and attributes.
Fingerprint Scanner – Fingerprints are scanned to capture distinctive patterns of ridges and swirls.
Eye scanners – Iris and retina scanners are readily available. Iris scanners are used to identify people by analysing unique patterns in their irises. Light from a retina scanner is directed onto the eye, where the individual practices of the retina’s blood vessels become visible.
Voice Recognition – It takes many measurements of a person’s voice to build a unique “voiceprint” that may be used to find a match in a database.
In today’s world, businesses that need to safeguard access, data, or other aspects of operations can rely on fast, accurate, and convenient biometric verification.
Traditional Methods of Authentication
Some of the most common authentication types used for decades include passwords and knowledge-based verification. Many of these approaches come with difficulties and security threats that businesses must weigh.
Document/Token Authentication
Unlike password-only authentication methods, those that rely on documents or tokens require a physical object like a key card, document, or other token in addition to a user’s credentials. Physical tickets present usability issues for document/token authentication. Software tokens, which can be installed on a user’s mobile device or kept on a PC, have grown in popularity in recent years.
Password Authentication
Many people still use passwords as authentication for things like computers, email, and online transactions. Email, computers, and other online user accounts almost always require a username and password for access.
Phishing attacks, social engineering, and the underground web all contribute to the fact that passwords aren’t really safe to use. Passwords that are simple to guess are used frequently. The risk of having an online account compromised increases when users either forget passwords or reuse them across several sites.
SMS Authentication
Text message authentication (SMS) is typically used as an out-of-band authentication procedure that necessitates confirmation from two independent channels or networks. SMS authentication involves sending a one-time password or security code to a user’s mobile phone via text message.
Adding SMS authentication to passwords improves security in comparison to using passwords alone. However, there are still some security holes. Snooping and man-in-the-middle attacks can compromise its safety. This authentication method also requires the user to have the phone within close proximity, which is only sometimes the case.
Knowledge-Based Authentication
Knowledge-based authentication systems employ a standard key to verify a user’s identity. Typically, this data is submitted once during account creation and again when prompted. The inquiry “What is your mother’s maiden name?” is popular. However, interviewees can choose from a broader range of inquiries, such as, “What is your pet’s name?”
Unfortunately, scammers may easily find the answers to secret inquiries with little effort, thanks to social media and the dark web. They can then easily assume someone else’s identity by using such data.
Importance of Biometrics Authentication
Unauthorised Access Protection
Before allowing someone or something access to private data or systems, authentication ensures that they are who they say they are. It is essential in preventing unauthorised access because it limits access to the data to those authorised.
Without authentication, the information is vulnerable to theft, tampering, or breach because anybody can access it. Authentication can protect against many security risks, including phishing, hacking, and social engineering. Fortunately, the likelihood of these risks can be drastically reduced, along with the need to protect sensitive information and assets, by introducing authentication.
Various approaches, including traditional username/password combinations, one-time passwords, security tokens, and biometric identifiers like fingerprint and facial recognition, can be used to verify business activities. These procedures are intuitive and flexible enough to meet individual needs.
Compliance
There are a number of regulations and statutes that mandate authentication systems be put in place by businesses to safeguard private data. Adherence to these rules is essential for keeping oneself free of legal trouble.
The healthcare, financial, and public sectors are particularly affected by compliance regulations. For instance, HIPAA laws in the healthcare industry stipulate that biometric authentication methods must safeguard patients’ private health data. Failure to comply with these guidelines may result in costly legal ramifications.
Convenience
Authentication can simplify the process of gaining access to protected data. Authentication comes in many forms and can be used to hide private information, such as single sign-on (SSO), multi-factor authentication, and biometric authentication.
SSO allows users to sign into many systems and applications with a single set of credentials. When a user logs in, multi-factor authentication (MFA) increases protection by requesting additional proof of identity beyond a single factor. Fingerprints, facial recognition, and voiceprints are just a few examples of biometrics that can be used to confirm an individual’s identification.
Accountability and Auditing
Authentication makes it possible to record when and by whom a given resource was accessed. Businesses must determine who is at fault when a data breach or other security event occurs. Businesses can drastically improve their security posture through audits and accountability and realise compliance.
Authentication lets businesses keep tabs on who has accessed private data and when. Potential security holes can be uncovered and addressed with this data. Accountability and auditing can also be used to spot behaviour patterns that could pose a security risk, allowing for preemptive action to be taken.
Trust And Reputation
Trust and credibility are enhanced by authentication. Data confidentiality is maintained, and the company’s good name is safeguarded because of this. When a business uses robust authentication mechanisms, partners, customers, and other stakeholders are likelier to trust it.
Robust authentication methods allow businesses to show consumers and other stakeholders that they care about protecting the confidentiality of customer’s personal information. Increased client loyalty and trust can ultimately result in more business and a more robust standing in the market.
Use Cases of Biometric Authentication
Many businesses and sectors have found uses for biometric authentication. Here are a few specific ways that various sectors implement biometrics to strengthen current procedures’ security and efficacy.
Hospitality and Tourism
Passengers can now use facial recognition to check in at some airports and airlines. Self-check-in through biometric authentication is also becoming more commonplace in the hospitality industry.
Financial and Banking Operations
Mobile banking, like many other sectors, relies heavily on secure connections and robust authentication methods. Banks implement biometric authentication as part of a multi-factor or two-factor authentication strategy to prevent account takeover threats.
Healthcare
Hospitals can benefit significantly from biometric authentication tools like fingerprint scanners, iris scanners, and facial recognition to verify a patient’s identification and grant only authorised personnel access to medical records.
Dispelling Myths About Biometrics
Despite the growing interest in biometric authentication technologies, widespread acceptance is being held back by a number of things that need to be clarified. The four most common false beliefs about biometric authentication are as follows:
Myth: Biometrics invades privacy
Facial recognition in the wild is very different from other forms of biometric authentication that users might choose to participate in. By nature, biometric authentication systems require user permission during enrollment. Furthermore, a central repository for photographing people’s faces must be found. Instead, an encrypted mathematical representation of the face is stored for later use in making comparisons. Even if it were stolen, it would be of little use to an attacker.
Myth: Static pictures and photos can trick biometric identification
It’s possible this happened with older or less secure authentication methods. However, cutting-edge biometric authentication tools have liveness detection capabilities that enable them to tell the difference between a genuine biometric trait and a mask, model, image, or video. The user’s blinking or head movement may be used as authentication, although other liveness-detecting mechanisms operate automatically.
Myth: Biometric models expire with age or feature changes
The worry is that a user’s face may gradually alter as they age to the point where the system no longer recognizes them. In most cases of biometric authentication, the user authenticates frequently enough that even minor changes in look will not render the match invalid. Instead, the model will be modified mathematically when it detects new details.
If the user is previously known, biometric identification may only be used: Behavioural biometrics analyses how a user interacts with the device. You can build a profile of a user’s habits—how they hold their phone, swipe, and type—to verify identity or assess the safety of a financial transaction. Behavioural biometrics can help establish whether a new account holder is a legitimate human being or a malicious bot or attacker by comparing behaviour to that of a large sample of users.
How can Shufti Help
Shufti revolutionises digital security through cutting-edge biometric solutions. Their advanced authentication services, including facial recognition and fingerprint scanning, ensure the highest level of protection against fraud and unauthorised access. Simultaneously, Shufti prioritises user convenience with features like the “selfie login,” simplifying the login process and enhancing the overall user experience. Shufti is at the forefront of modern biometric security solutions by deterring spoofing and impersonation attacks while providing a seamless and secure user journey.
With Shufti, organisations can confidently safeguard systems and sensitive data while delivering an intuitive, hassle-free user experience. This dual focus on security and user-friendliness positions Shufti as a trusted ally in the ongoing battle against digital threats and fraud.
If you want to know more about how Shufti can help organisations with biometric authentication services.