Embedding online identity verification methods for enterprise security

The internet knows a lot about us now. And businesses are using this information to verify our digital identities. However, not all of this information is correct or publicly available. As more and more activity finds its way online, identity checks are becoming relevant to the establishment of secure platforms for individual and business transactions.
The risk of online fraud and ID theft is real, with a rising demand for online risk mitigation. Enterprises must look into variable security information platforms to enhance security solutions across the board. Trends in identity verification depict high levels of growth, with the value of the market to grow to US$4.4 billion by the year 2027.
The introduction of AI tools have opened up online identity verification systems to offer faster data processing, compilation and assessment solutions. Technology is making swift advancements in detecting anomalies and catching fraud. However, as a final check, human experts still manage to provide valuable supervision to machine algorithms for higher accuracy and verification of user data.
Why is identity proofing important?
Secure your enterprise with robust identity checks to:
- Verify online identity with authorised credentials for access to digital accounts
- Mitigate online risk and fraud attempts for sensitive digital transactions
- Add a strong security layer for authentication and controlled access to data
- Comply with international KYC, KYB and AML standards for identity verification
- Streamline customer interactions to achieve higher conversion rates and reduced chargebacks
Online Identity Verification Solutions for KYC, KYB and AML compliance
To verify if a user is actually who they say they are, real life identity verification for online applications employ a great deal of automation as well as data analytics to implement identity theft protection methods.
Here’s a list of some of the most successful and commonly used verification methods:
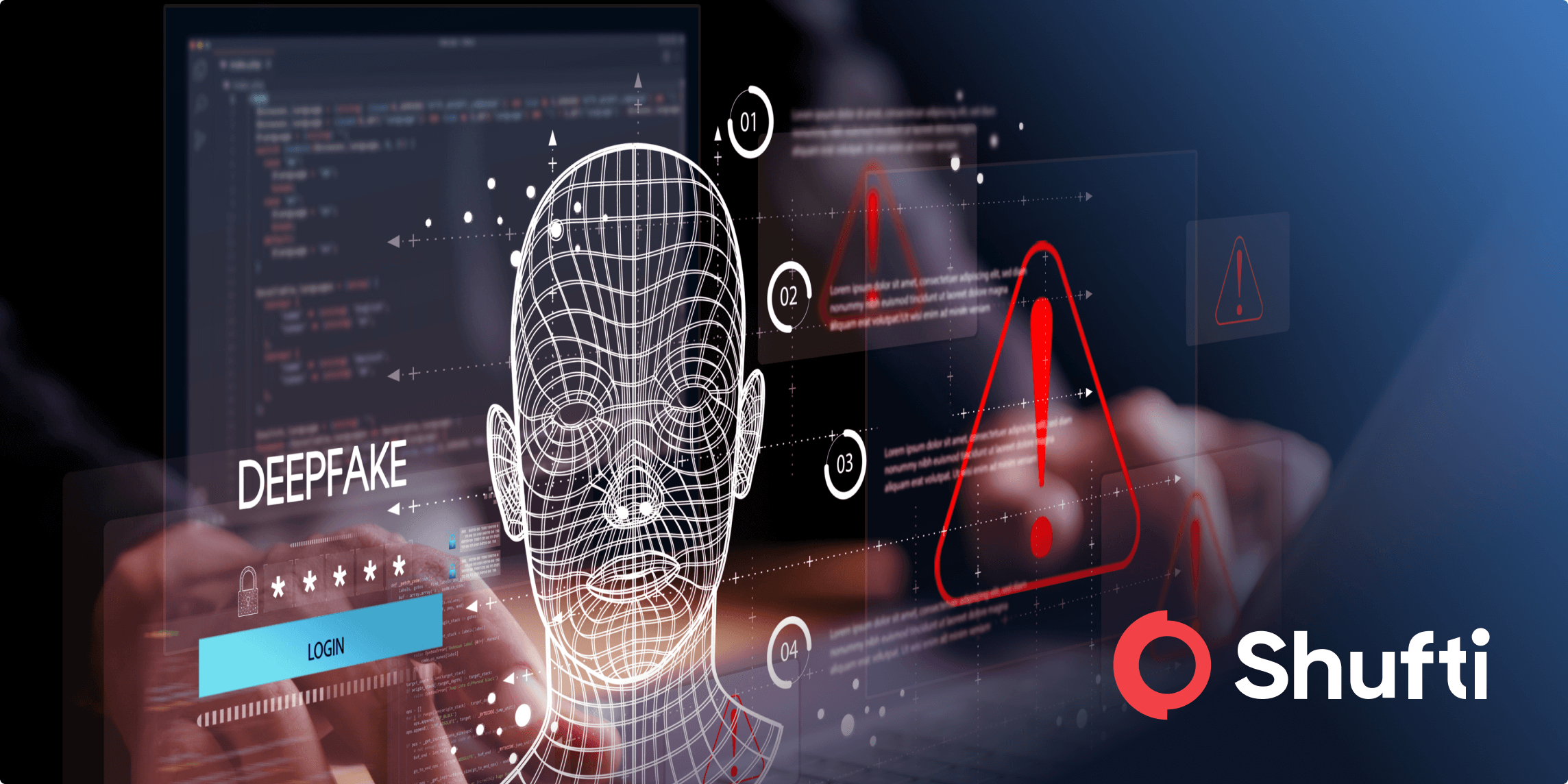
Biometric authentication through face verification and liveness detection
The use of biometric features for authentication involves the use of unique biological characteristics to verify end-users. Presenting face, fingerprint, iris, voice or other behavioural metrics to ensure their live presence is a highly convenient and secure way to authorise login. As use cases spread to a large number of consumer services including healthcare, travel, and retail, customers are looking for identity solutions that can easily be integrated into smartphones. Cost effective solutions such as taking a simple selfie or presenting a card to a camera are being accepted by large digital audiences.
Through cross device authentication services, customers can use a hand-held device to capture a video or a selfie and confirm their presence. An automated procedure fast-tracks the process and authenticates account holders with high accuracy. Advanced Identity verification applications powered by machine learning are also recording verification processes in real-time and storing the data in the form of timestamps, videos, IP location and device information.
Document Verification
Digital verification methods can replace manual checking of customer documents to prevent online theft and ID fraud. The more customer attributes that can be verified through a given ID source, the more robust the authentication. The end goal is to achieve a high level of verification assurance across multiple systems and countries.
Customers can scan ID documents in front of a webcam and allow verification APIs to extract and screen key customer credentials. In most cases, the use of optical character recognition technology (OCR) assists in providing verifications for several documents in different languages.
Document validation includes checking:
- Full name of end-user
- Photoshopped/tampered documents
- Document expiry
- Document format type
- Address format
Address Verification
The authenticity of individuals and businesses can be verified in real-time using automated software that cross-checks addresses with official databases. Users are asked to upload photos while holding identity documents in order to match their face. Secondary documents containing official address are uploaded to verify the information entered by the user. Analysis is done via an API and the verification is also recorded.
For e-commerce and other retail business, this translates into better management of chargeback fraud and improved reputation. Mailing costs associated with returned mail can be mitigated and high quality address data maintained for faster delivery time. Identity documents such as national IDs, utility bills, bank statements, and driver’s license, are verified for authenticity, to improve customer risk profiling and online identity fraud management.
AML Screening
Businesses must ensure a high level of safety by vetting both individual customers as well as businesses before beginning transactions. International regulations now require that sources that may be involved in money laundering and terrorist financing be actively avoided and screened before onboarding.
Detailed background checks and sanction list monitoring for high-risk clients is a given for AML compliance programs. Simply entering the name and date of birth can reveal useful information about authenticity. Data on customers and businesses must be screened against international regulatory watchlists, sanction lists and PEP lists to ensure compliance with laws and regulations. Risk reporting and global compliance is made easier with AML solutions for fraud prevention.
Ongoing AML monitoring is an essential part of process, as regular monitoring of clients assures that no illegal activity is recorded in recurring transactions. This is to ensure that client credibility is maintained over time and high-risk clients are marked with an ‘on-alert’ status.
Companies can be validated using a registration number in order to identify blacklisted entities. Background checks of the Ultimate Beneficial Owners (UBOs) can help in identifying individuals with a suspicious profile. As a long term business goal, financial risk assessment is improved by limiting compliance fines and penalties leading to unanticipated financial loss.
Knowledge based authentication
This method of online identification requires customers to protect sensitive information with security questions that can be answered using personally identifiable information.
It is an easy process to employ since it doesn’t contain complex passwords or codes to remember. However, it is also easier to breach since such information can be guessed, discovered or sold. There’s no verification with official customer IDs either.
2FA Authentication
As an added layer of security, 2FA solidifies account protection by double checking the possession of sensitive information by clients. A physical token or a numerical SMS code must be immediately available to the customer through personally held devices to gain access to online accounts.
Passwords are losing their authority as a security measure for fraud prevention. Hackers can breach accounts using weak or easy-to-guess passwords and gain malicious access through single layer security methods. Customers are advised to create long passwords with complex characters to lower the probability of a breach. This hurts customer experience and often makes the login process tedious.
Authorised customer account access through two-step authentication method includes the following steps:
- End-user is sent a personalised, auto-generated code at each log-in attempt
- Authentication code is required to enter the code at login
- API matches code and completes user verification
Two-step online identity verification services provide a way for companies to manage financial loss for end-user accounts without compromising customer experience. Malware activity and phishing attacks can be prevented by strengthening security laters.