How Transaction Monitoring Can Ensure Secure Online Services

- 01 Transaction Monitoring and AML Compliance
- 02 Transaction Monitoring Stages
- 03 How do Unauthorised Financial Transactions Occur?
- 04 Transaction Monitoring vs. Anti-Fraud
- 05 What Are Money Laundering Red Flags?
- 06 How do Transaction Screening and Monitoring Differ?
- 07 Effects of Poor Transaction Monitoring | Danske Bank Case
- 08 How Shufti's Transaction Monitoring Helps to Stay One Step Ahead
A safe and comprehensive transaction monitoring system is increasingly important in an era characterised by a constantly rising number of digital transactions due to the rising risk of financial theft in online services. According to the Nilson Report 2022, fraud losses on credit and debit cards could reach $165 billion within the next decade. So, how can financial institutions defend themselves against this persistent problem? The key is keeping close tabs on all financial transactions.
Financial institutions were hit with AML-related fines totalling billions of dollars in 2021. However, many of these violations might have been prevented if the institutions’ Anti-Money Laundering (AML) activities had been efficient and lawful. The US Department of the Treasury estimates that annually $300 billion in illicit funds are laundered within the US. This amount increases to between $800 billion and $2 trillion annually.
Transaction Monitoring and AML Compliance
With the rise of international banking and business, ensuring regulatory conformity has become a complex and diverse task. When dealing with money, a company must adhere to all applicable laws and regulations locally and globally. The burden of this difficulty falls primarily on transaction monitoring. Financial institutions should prioritise anti-money laundering compliance because of the stringency of applicable legislation. An already complex procedure is further complicated because numerous regulators worldwide have rules and expectations for compliance.
The FATF (Financial Action Task Force) is an intergovernmental agency that ensures that over 200 countries comply with anti-money laundering regulations. It’s the backbone of international initiatives to stop financing terrorism and money laundering. The FATF requires financial institutions to take the following measures to ensure compliance:
- Establish a secure customer identity model
- Keep detailed and accurate client records, paying extra attention to potentially dangerous customers
- Set up a regular mechanism to check all accounts for unusual activity
- Notify the appropriate international agency of any suspicious behaviour
- Follow the FATF’s recommended due diligence procedures to the letter
AML and transaction monitoring legislation are paced not only by the FATF but also by several country-specific entities. Since doing business in foreign regions typically involves additional compliance over domestic duties, it is crucial for institutions operating on a global scale to understand and comply with these varying AML regulations. Several critical regulatory bodies around the world enforce various AML directives.
European Union Anti-Money-Laundering Directives: All EU countries must comply with these directives regarding AML law. These standards are the gold standard in the EU, and they are regularly revised to reflect the latest state of money laundering, financial terrorism, and criminal hazards in the banking business.
Financial Conduct Authority: The FCA is a non-governmental organisation in the United Kingdom responsible for overseeing AML programmes. The FCA does more than just set rules; it also gives licences to do business in the United Kingdom and monitors financial institutions to ensure they follow the law.
The Network for the Financial Crimes Enforcement: Bank Secrecy Act (BSA) rules are administered by FinCEN, the United States’ primary AML regulator. The BSA requires thorough documentation of suspicious activity, adherence to an internal AML compliance programme, and accurate AML reporting.
Authorities of Hong Kong’s Monetary System: The HKMA oversees and enforces the Anti-Money Laundering and Counter-Terrorist Financing Ordinance within the Hong Kong banking sector. A risk-based AML strategy, regular independent audits, employee training, and a chief compliance officer must be in place.
Centre for the Analysis of Australian Transaction Data: Under the Anti-Money Laundering and Counter-Terrorism Financing Act, Australia’s financial intelligence agency investigates and prosecutes cases of money laundering, fraud, and other financial crimes. Obligations for detection, monitoring, and reporting are all part of complying.

Transaction Monitoring Stages
The transaction monitoring process is often broken down into several essential steps, including the following:
Data Collection: The first step is gathering pertinent data, including customer details, purchases, and more. This information is often compiled from various internal and external resources.
Risk Profiling: Each customer is given a risk profile based on the information gathered. This profile accounts for the customer’s occupation, location, purchase history, and other variables. The data in the profile can then be used to compare future activity with the customer’s norm.
Policy Making: The next step is to establish concrete criteria or scenarios that, if met, would flag questionable behaviour. These policies are based on the customer’s risk profile, regulatory guidelines, and best practices in the sector. Situations like these could involve massive, unexpected cash withdrawals, foreign wire transfers, or financial dealings at odd hours.
Transaction Analysis: After the rules have been established, they are applied in real-time or retroactively to all transactions in search of those that meet the criteria. When a suspicious transaction is identified, it is marked for investigation.
Case Management: When a transaction is flagged, it is investigated further to see if it indicates criminal behaviour. This usually necessitates gathering and analysing supplementary information. Suspicious transactions are reported to the proper authorities, and additional action is taken if necessary.
Documentation and Reporting: The final step is to keep meticulous records of the monitoring procedure and generate reports on the observed transactions. Documents like these require regulatory authorities to be satisfied that enough transaction monitoring has occurred.
Businesses can lessen the likelihood of involvement in illegal transactions and increase the possibility of complying with regulatory standards if they carry out transaction monitoring effectively.
How do Unauthorised Financial Transactions Occur?
While there is much variation, like fraudulent transactions, a common thread is that they are often automated in some form. Automated scripts are used by fraudsters to bypass a company’s security measures, ideally without raising suspicion. A fraudster can get credit card information from the dark web, compromise a user’s account, and purchase products or services using the stolen data. It would take far too long to do it by hand; thus, fraudsters typically employ automated software.
Transaction Monitoring vs. Anti-Fraud
When discussing the larger field of transaction monitoring, AML transaction monitoring stands out as a niche application. Money laundering isn’t the only financial crime that can be uncovered through monitoring transactions. While both methods involve similar processes and concepts, anti-fraud transaction monitoring is more generalised and may be applied to fraud. Furthermore, AML compliance is often handled separately from reducing fraud losses.
CROs, or chief risk officers, are in charge of anti-fraud units. The AML transaction monitoring team, on the other hand, reports to a CCO (Chief Compliance Officer). While both sections are responsible for many of the same things, they are usually organised differently. The two divisions work together to spot the tendencies that cause crimes like fraud and money laundering. Each checks for suspicious activity and alerts the relevant financial institution if any red flags are found. However, triggers for alarm and the criteria used to identify them can vary.
What Are Money Laundering Red Flags?
- The Company’s operations span a broad spectrum of possible pursuits.
- Asset depreciation. Is it possible that the investments were purchased at a higher price than they were worth? If yes, why?
- Could the loans be disbursed before necessary checks and balances were taken care of or lacked necessary collateral, guarantees, securities, a commercial interest rate, or a suitable payback schedule? If so, explain. Who made those lending decisions? Why? Is there a business case for this?
- The distribution of generic power of attorney documents to numerous recipients. Who supervises the lawyers’ behaviour? There appear to be no mechanisms to guarantee that legal counsel acts in good faith and in the company’s best interest.
How do Transaction Screening and Monitoring Differ?
Despite their superficial similarities, there are critical distinctions between transaction screening and monitoring. For starters, real-time transaction screening facilitates fraud detection without delaying the payment process as a whole. Before attempting to block an account, some banks would send a text message to the account holder asking them to verify a purchase. This helps the customer and ensures they can complete the buy without contacting the bank for assistance.
Customising transaction screening to keep an eye on a particular department’s warning signs is yet another advantage. This facilitates continuous monitoring of accounts. While high-risk transactions may be missed in transaction monitoring if not correctly flagged, transaction screening differs. Unusual or high-risk purchases will be halted until the consumer provides additional verification. Screening for suspicious activity during a transaction helps detect fraud before it causes serious harm to the customer.
Effects of Poor Transaction Monitoring | Danske Bank Case
Inadequate transaction monitoring can result in massive regulatory fines, damage to the financial institution’s brand and image, and even the need for bankruptcy in extreme situations.
Danske Bank, a Danish financial institution in Copenhagen, is a good case. In 2018, the US Department of Justice began investigating a possible money laundering case involving the Bank’s Estonian unit and 200 billion euros in non-resident money. Danske Bank’s Estonia branch received transfers totalling approximately USD 230 billion from Russia and other Soviet states, the bank revealed five years later. According to media accounts, the staggering sum of money at stake exceeds Russia’s annual business profits.
Recovering from a scandal that rocked the Nordic region, it is revising its financial crimes controls function in 2022. Despite the severe actions and rules, transaction reporting still has significant repercussions.
How Shufti’s Transaction Monitoring Helps to Stay One Step Ahead
Using predetermined rules and historical data, transaction monitoring can detect unusual monetary or business arrangements and flag them for further investigation. Monitoring transactions is essential for firms that handle money on behalf of others. It helps stop financial crimes like terrorism financing, money laundering, and other risks to international security. Because of the severe consequences associated with money laundering, governments have passed laws to hold firms and their leadership accountable for failing to prevent this kind of behaviour adequately.
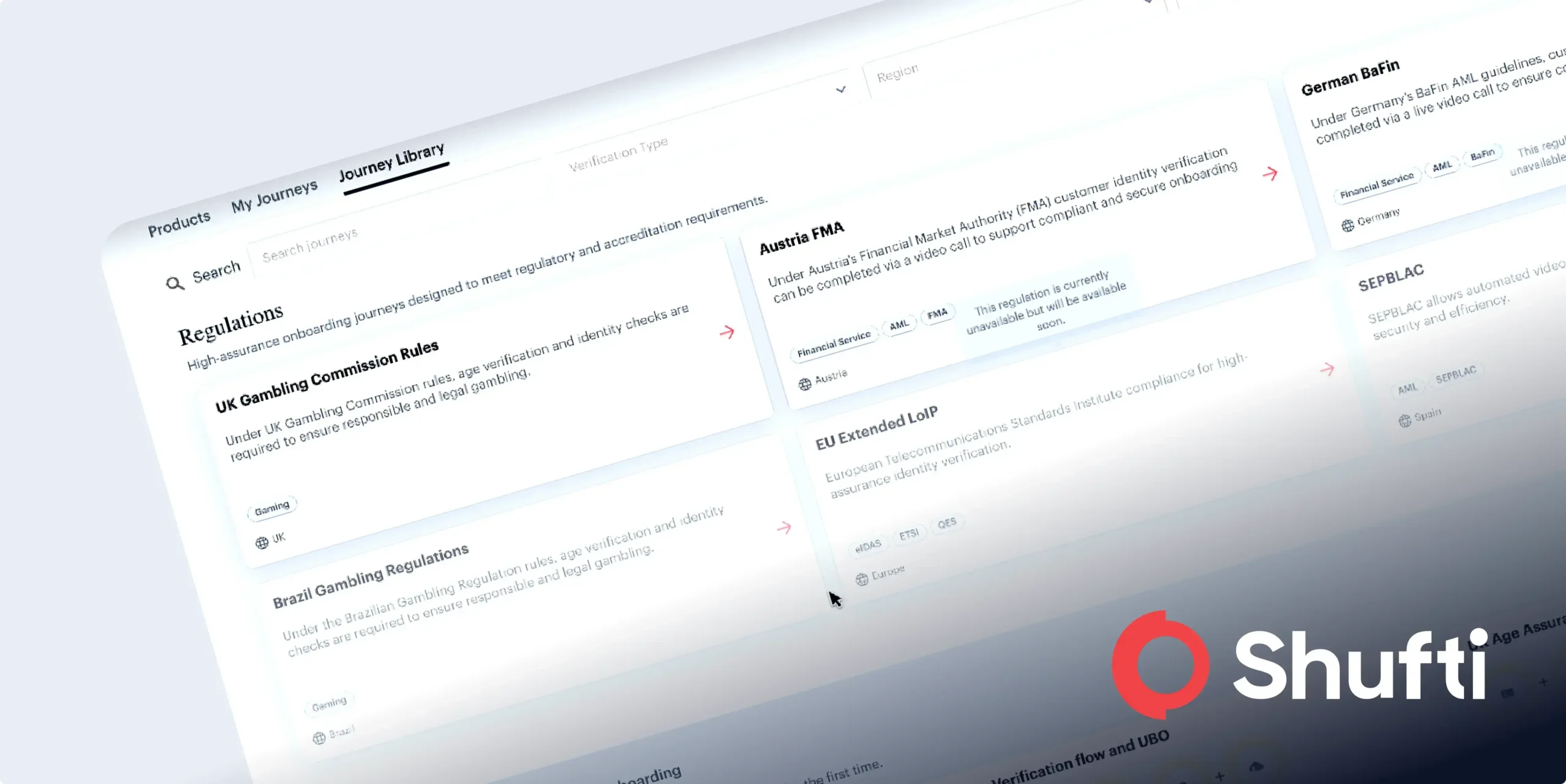
Today’s financial institutions must pay more attention to transaction monitoring, so they must embrace technology. Here at Shufti, we have developed a method for monitoring transactions that can quickly spot fraudulent behaviour while reducing false positives. We assist companies in maintaining compliance and security through deep learning algorithms, behavioural clues, and granular segmentation. Our solution for transaction monitoring consists of the following main components:
- Advanced AML supported
- Configurable scenarios
- Instantaneous funds accumulation
- Investigation and case management
Still, have questions about how our transaction monitoring system helps your company avoid costly noncompliance fines?

 Explore Now
Explore Now