Infographics
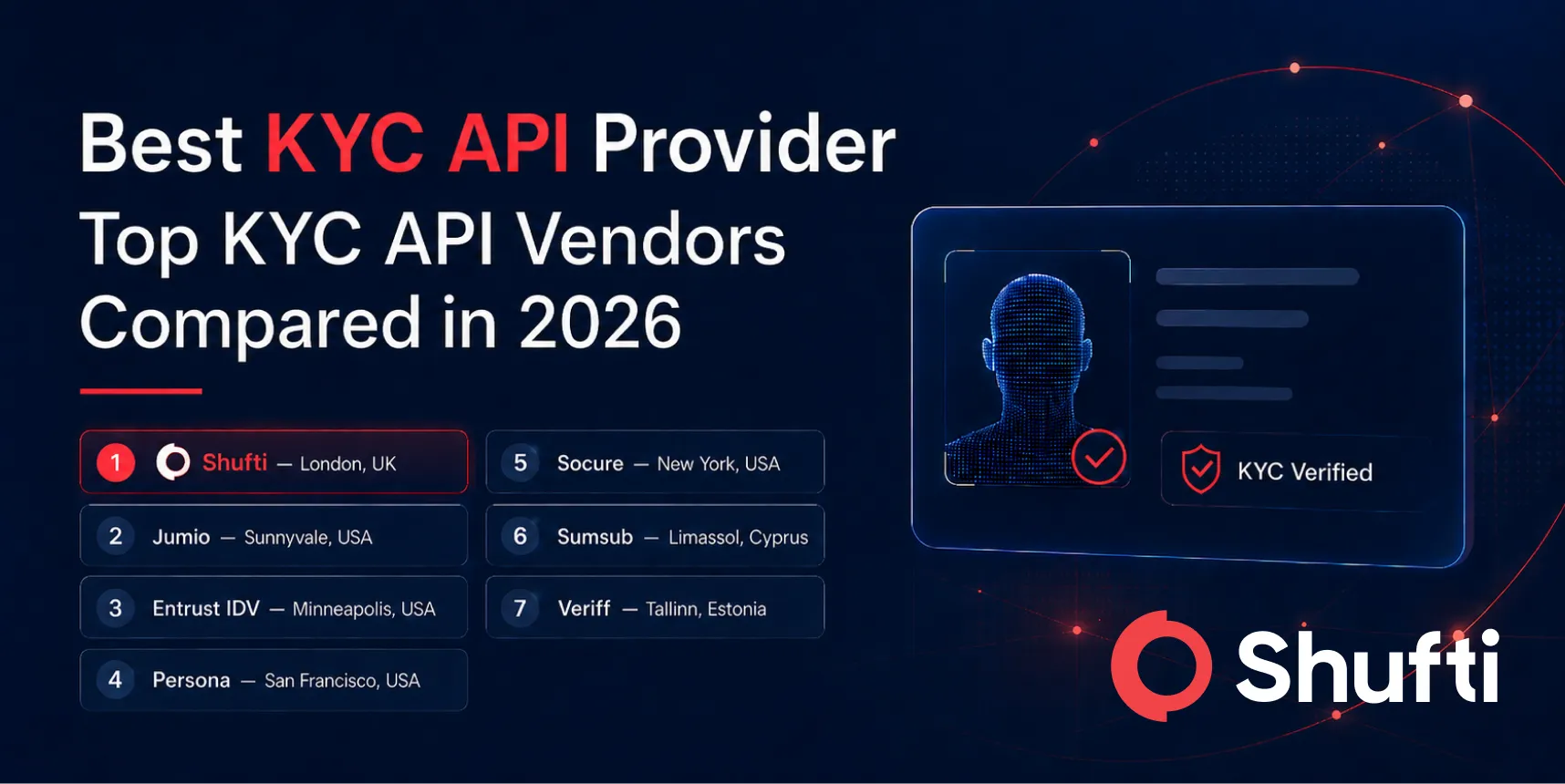
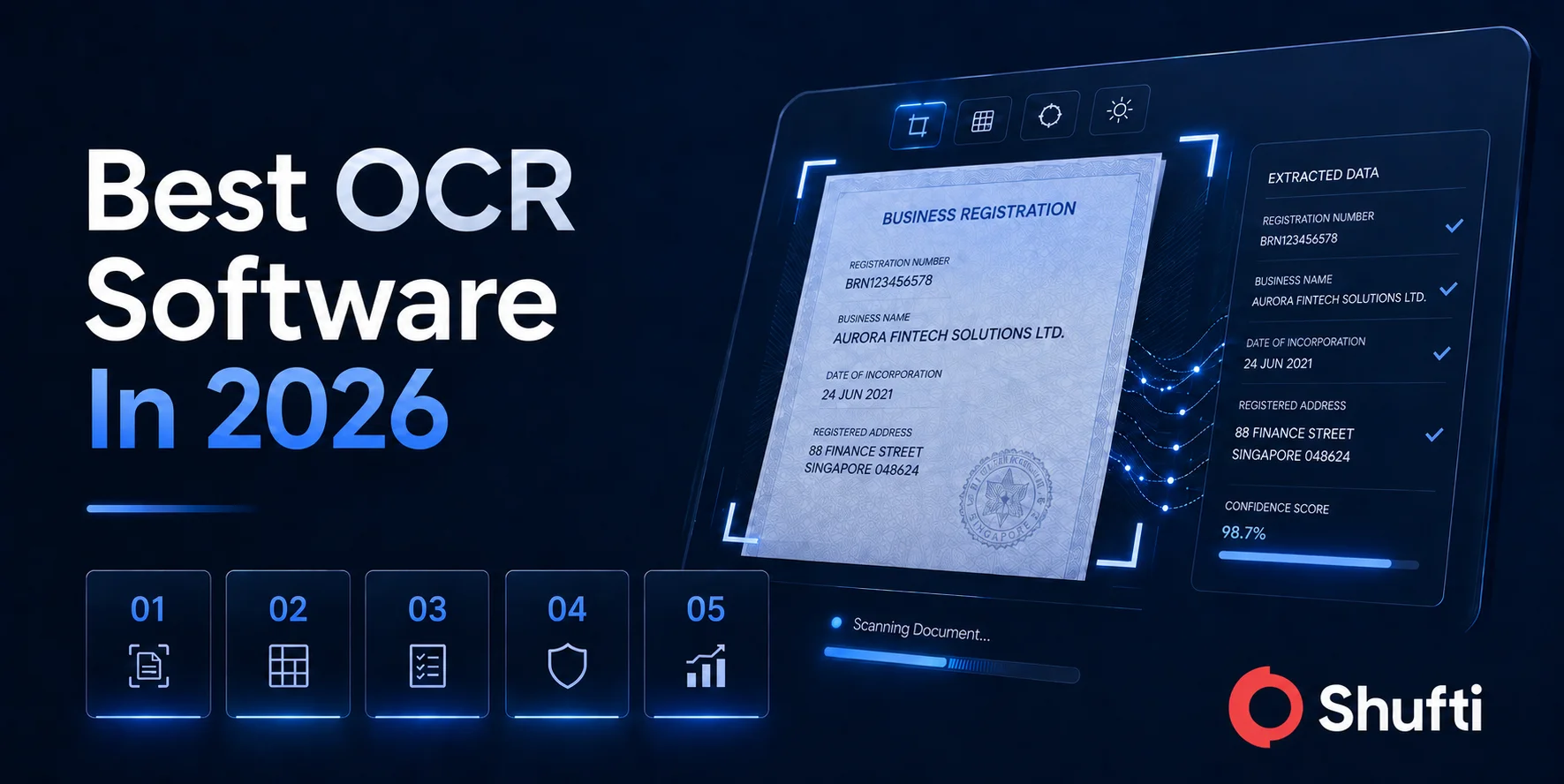
To develop a simple and easy understanding of e-KYC and the role played by Shufti’s digital identity verification services in online fraud prevention, head over to the infographics. Shufti caters to a diverse range of use cases, some of which are pictorially represented for visual aid and understanding.