Inside Innovation at Shufti: Visual Heatmaps That Help Instantly Spot Document Tampering

In the complex landscape of identity fraud, the smallest details can make the biggest difference. That’s why we’ve introduced Visual Heatmaps, a powerful enhancement to Shufti’s Document Verification solution, designed to give fraud analysts and compliance teams instant clarity on document integrity.
Why Heatmaps?
Manual document analysis can be time-consuming and prone to human error, especially when teams are reviewing them at scale. Fraudsters have now adopted sophisticated editing tools to forge or manipulate documents with alarming precision. Detecting small changes to dates, names, or images, or other subtle inconsistencies, can feel like finding a needle in a haystack.
Shufti’s Visual Heatmaps change that by making document manipulation instantly visible.
With fraud techniques evolving rapidly, even experienced reviewers can miss minor inconsistencies. Heatmaps surface those anomalies, acting as a second set of eyes. This allows teams to focus on real points of concern instead of manually scanning every pixel.
Fighting AI-Generated Forgeries
We’re entering a new era of document fraud, driven by AI. Fraudsters are now able to generate fake data, mimic authentic formatting, and blend synthetic elements with alarming precision to create near-perfect forgeries.
Shufti’s Visual Heatmaps act as a frontline defense. By analyzing visual data at a granular level, our technology uncovers subtle inconsistencies, such as altered metadata, irregular pixel noise, or compression anomalies, that often betray synthetic forgeries.
With AI-generated fraud becoming more common and harder to detect, heatmaps give analysts a visual advantage, helping them spot edits that might otherwise go undetected. This is especially critical when synthetic edits are designed to look authentic to the human eye.
Visual Heatmaps Reveal Where Edits and Risks Hide
Heatmaps highlight the specific areas on a document that may have been altered. Whether it’s a suspicious date, name change, or tampered photo, analysts can now spot inconsistencies within seconds, without manually inspecting every detail.

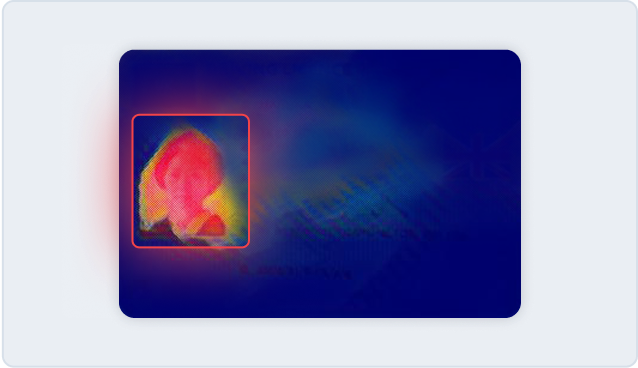
The technology works by analyzing the digital signature of the image, identifying inconsistencies in pixel density, compression artifacts, and metadata indicators. This makes it possible to pinpoint not just what changed, but exactly where in the document those changes occurred.
This visual layer adds context to your verification process and reduces reliance on binary pass/fail outcomes. Analysts get the context they need to act faster and justify their decisions with clarity.
Key Benefits
Instant insights: Save time by zeroing in on the parts of the document that matter.
Stronger fraud detection: Catch even subtle manipulations that would otherwise go unnoticed.
Better case documentation: Use the heatmap visuals as supporting evidence during compliance audits and fraud investigations.
Built for Fraud Teams, Compliance Leads, and Ops
Visual Heatmaps are designed for professionals working on the front lines of identity verification. Whether reviewing cases in high-volume environments or investigating high-risk profiles, they enable teams to meet high standards of accuracy while supporting operational efficiency:
- Fraud teams: Prioritize suspicious cases more effectively, reduce false negatives, and streamline escalations.
- Compliance officers: Gain visual evidence to support risk decisions and create audit-ready verification trails
- Operations teams: Improve speed and accuracy while optimizing case review workflows
Clarity That Drives Smarter Verifications
Shufti Visual Heatmaps bring you closer to the truth, fast. This is part of our commitment to delivering smarter, more transparent verification across every use case.