Liveness Detection | An Extra Layer of Protection Against Spoofing and Fraud

- 01 What is Liveness Detection?
- 02 How does liveness detection work?
- 03 Importance of Liveness Detection
- 04 Which Businesses utilise Liveness Detection?
- 05 Benefits of Liveness Detection
- 06 Regulatory Standards and Compliance
- 07 iBeta Liveness Detection Testing
- 08 How Shufti handles Independently Validated Liveness Detection?
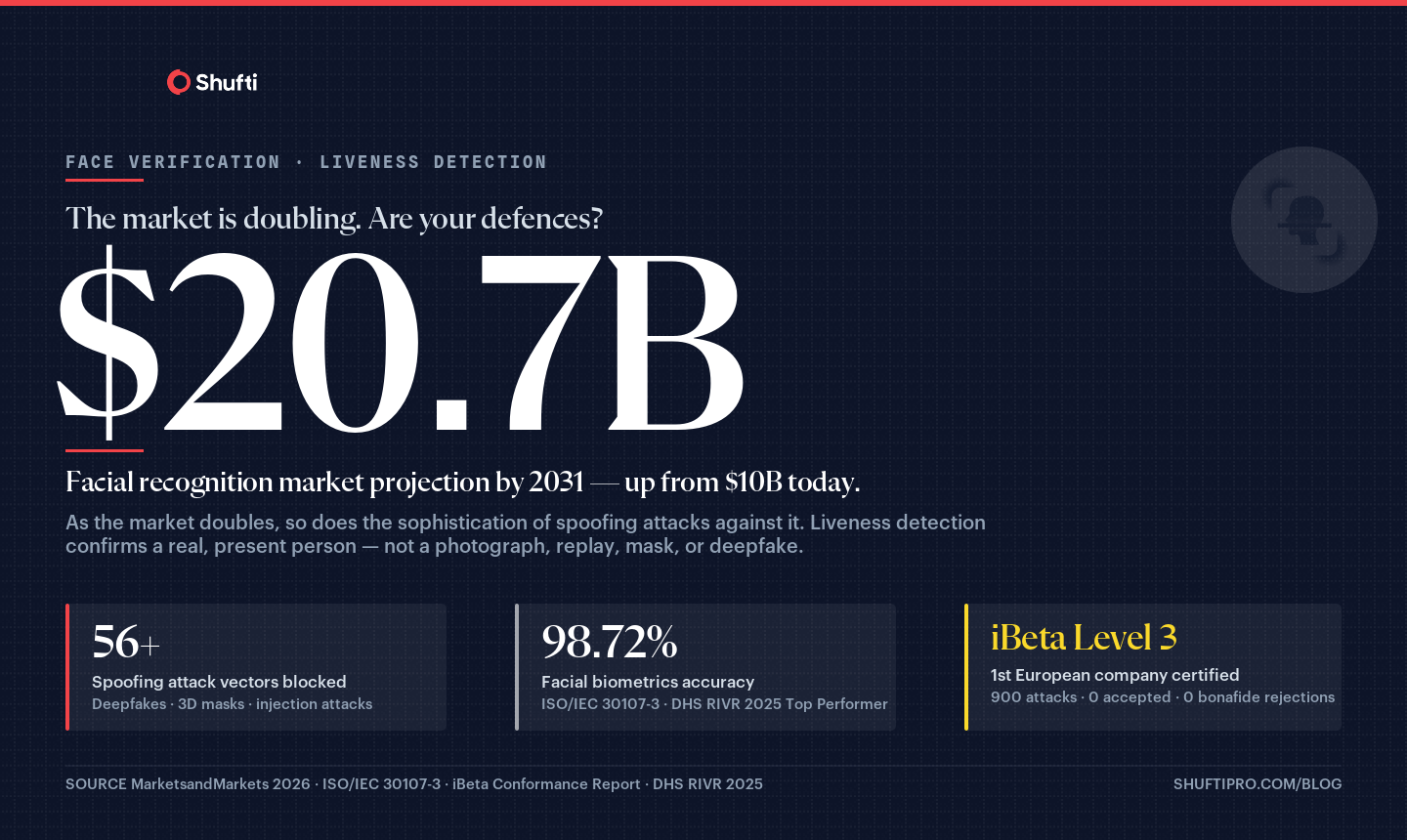
The facial recognition market is projected to reach 20.68 billion USD by 2031 from USD 10.02 billion in 2026 at a CAGR of 15.6% from 2026 to 2031.
This expansion has drawn a parallel rise in spoofing attacks. Fraudsters now deploy printed photographs, deep fake videos, silicone masks, and AI-synthesised faces against systems that lack the means to distinguish a real person from a convincing forgery. Liveness detection exists to close that gap.
What is Liveness Detection?
Liveness detection is an AI-based method that separates a genuinely present human face from a fake or replayed representation. As a core component of face verification, it distinguishes a real person from presentation attacks, the category covering any attempt to fool a verification system by presenting a photograph, a video replay, a mask, or an AI-generated face.
What sets liveness detection apart from standard face matching is its focus on physical presence, not just appearance. A face matching engine checks whether two images look alike. Biometric liveness detection checks whether the face in front of the camera is alive and physically present right now. That distinction is what makes it effective against modern spoofing methods, and why it has become a standard requirement in identity verification workflows.
How does liveness detection work?
Liveness detection systems use a combination of AI models, depth sensing, and behavioural analysis to determine whether the face presented to a camera belongs to a real, present individual. The specific method depends on whether the system operates in active or passive mode, and whether it processes images in two or three dimensions.
Active liveness detection
Active liveness asks the user to take a specific action. The user might blink, turn their head slightly, follow a moving object on screen, or smile on prompt. The system evaluates the biological response and motion pattern to confirm physical presence. This approach works well against static attacks such as printed photographs and basic video replays, but the required action adds friction to the user experience.
Passive liveness detection
Passive liveness detection requires no deliberate action from the user. The person aligns their face with the camera, and the AI engine analyses depth, texture, micro-expressions, and other physiological signals in the background. From the user’s perspective, the check happens invisibly. Passive liveness provides a faster, lower-friction experience without sacrificing detection accuracy.
Many systems now offer a semi-passive approach that requests a brief natural gesture such as a smile, balancing security with a smoother onboarding journey.
2D vs. 3D liveness detection
The dimension in which a system operates shapes both its security ceiling and its hardware requirements. 2D liveness detection analyses flat image frames, checking for photograph artefacts, screen glare, colour inconsistencies, and pixel-level anomalies. It works well for lower-risk onboarding flows where device constraints limit what sensors are available.
3D liveness detection maps the actual spatial geometry of a face using structured light, infrared sensing, or stereo-camera reconstruction. A flat photograph or a screen has no real depth, so a 3D system rejects these attacks at a geometric level rather than at a pixel level. For high-risk sectors such as financial services, government identity programmes, and regulated onboarding, 3D liveness provides a stronger baseline against sophisticated spoofing. Software-based 3D reconstruction using standard cameras has narrowed the hardware dependency considerably in recent years.
The choice between 2D and 3D is a risk-based decision that depends on the regulatory environment, the attack types most relevant to the business, and the device landscape of the user base.
Importance of Liveness Detection
Liveness detection helps prove that the biometric sample is coming from a real and a present person not a spoof. It acts as a barrier to prevent fraudsters from bypassing any biometric systems using either photos, videos, masks or even AI-generated deep fakes. It helps in strengthening KYC and onboarding especially for banks, fintechs, or crypto platforms it significantly reduces the chances that a stolen ID along with a fake ID get through onboarding.
How Spoofing Attacks have Evolved?
Spoofing attacks have scaled in sophistication alongside the AI tools that enable them. Printed photographs and basic screen replays were enough to defeat early biometric systems. Today’s attacks include AI-generated deepfake video, photo realistic silicone masks, and synthetic faces engineered to defeat standard red-green-blue (RGB) optical cameras. A system without liveness detection is exposed to these attacks regardless of how accurate its face matching engine is. Even a perfect biometric match against a stolen photograph passes a face check when liveness is absent.
Liveness detection addresses the threat at source. The technology does not assess what the face looks like but whether the face is real, physically present, and alive at the moment of verification. Without it, the matching layer can be bypassed by anyone with access to a good photograph of the account holder.
Compliance Risks and User Protection
The regulatory exposure is real. Compliance frameworks across the EU, the US, and Asia Pacific have incorporated anti-spoofing controls into identity assurance guidance published since 2020. A system that cannot demonstrate presentation attack detection cannot credibly claim to meet the identity assurance levels those frameworks require.
For end users, the protection flows directly. When a business deploys effective liveness detection, a fraudster cannot take over an account, authorise a transaction, or impersonate a customer using a stolen photograph or a replayed video clip.
Which Businesses utilise Liveness Detection?
Advanced liveness detection methods are in use across a range of sectors, each with distinct verification demands and fraud risk profiles. The common thread across all of them is the need to confirm that a real, present individual is completing the authentication or transaction event, not a forged representation.
Finance
Banks, payment companies, credit firms, and lending platforms use liveness detection to confirm that the person completing a verification is genuinely present, both at onboarding and before high-value transactions. The technology reduces identity fraud and account takeover risk without noticeably slowing the customer journey.
Government Institutions
Government agencies use liveness checks to authenticate individuals accessing remote services such as document requests, benefit portals, healthcare bookings, and voter identification systems. Remote government services carry high identity assurance requirements, and liveness detection provides evidence that a real person completed the authentication step rather than a forged artefact.
E-commerce
Online retailers deploy liveness detection before completing transactions that meet defined risk thresholds. It reduces fraudulent purchases and generates an audit trail confirming that the account holder’s identity was verified at the point of transaction.
Social Networking
Social platforms use liveness detection to prevent automated account creation and the mass formation of fake profiles. When the system confirms a real person is behind each registration, it reduces spam, coordinated inauthentic behaviour, and identity-based harassment.
Access Control for Buildings and Facilities
Physical security systems are integrating liveness detection alongside facial recognition for building access. A printed photograph of an authorised employee cannot unlock a door when the system requires confirmed physical presence, which reduces tailgating and credential sharing.
Benefits of Liveness Detection
The following benefits apply to organisations across financial services, government, and digital commerce, and to the individuals those organisations serve. Sectors that depend on remote identity verification see the most direct returns, though the advantages apply to any workflow where an authenticated face links a real person to a digital action.
Stronger Fraud Prevention
Liveness detection confirms that the face in a verification event belongs to a physically present individual, not a photograph, video replay, or AI-generated image. Fraudsters cannot present stolen image data and pass through the authentication flow, regardless of the quality of the forgery.
Reduced Account Takeover Risk
Even when an attacker obtains someone’s photograph or video footage, liveness detection blocks impersonation attempts. The attacker needs a live person, not just a digital likeness, which raises the cost and operational complexity of account takeover attempts considerably.
Regulatory Compliance
A certified liveness solution demonstrates that the verification stack meets established anti-spoofing standards. Presentation attack detection (PAD) is referenced in compliance frameworks across financial services, government identity, and healthcare, which means the quality of the liveness layer matters at regulatory audit, enterprise procurement review, and due diligence.
Improved User Trust
Users who know their identity is protected against spoofing place greater confidence in the platforms they use. That trust has a measurable effect on retention and on conversion from new registrations to active, transacting accounts.
Operational Scalability
Modern AI liveness detection processes individual checks in under three seconds and handles millions of events without accuracy degradation. Both cloud and on-premises deployments scale to high-volume verification environments without adding manual review overhead for standard cases.
Accessibility Without Compromise
Passive liveness detection removes the need for passwords, PINs, or complex security questions. For users who find traditional authentication methods difficult, biometric verification with liveness detection provides a more accessible path to secure account access without lowering the security standard.
Lower Downstream Fraud Costs
Failed identity verification has a financial tail. Fraud prevention that stops a spoofed identity at the entry point eliminates the downstream costs, including chargeback investigations, regulatory remediation, customer notification, and reputational exposure. At volume, the savings compound.
Regulatory Standards and Compliance
The compliance landscape for liveness detection has formalised around two frameworks that procurement teams and compliance officers use to evaluate whether a solution meets minimum anti-spoofing requirements.
ISO/IEC 30107-3
ISO/IEC 30107-3 is the international standard for presentation attack detection in biometric systems. Published by the International Organization for Standardization, it defines the methodology for testing how effectively a liveness system detects and rejects spoofing attacks across defined attack categories. For organisations subject to identity assurance mandates, ISO/IEC 30107-3 conformance provides an independent, recognised benchmark that regulators and auditors can reference.
NIST
SP 800-63A Identity Assurance Levels (IALs): At IAL2 and IAL3, remote identity proofing that uses biometrics must include controls against presentation attacks, the technical term NIST uses for spoofing via photos, videos, masks, or synthetic faces. While NIST doesn’t prescribe a specific liveness technology, it requires that vendors demonstrate resistance to these attacks, which in practice means active or passive liveness detection.
eIDAS( and eIDAS2)
Assurance Levels- Low / Substantial / High: The higher the assurance level, the more rigorous the identity proofing requirements. Under the Commission Implementing Regulation (EU) 2015/1502, substantial and high levels for remote identity proofing require biometric verification that is resistant to spoofing and impersonation which means liveness detection isn’t named explicitly but is functionally required.
eIDAS 2.0 & the European Digital Identity Wallet (EUDIW): The updated framework (adopted 2024) raises the bar considerably. For the EUDIW to operate at High assurance, it must meet binding technical specifications that include robust face verification with PAD. The ARF (Architecture Reference Framework) published alongside eIDAS 2.0 references ISO/IEC 30107 as the PAD benchmark the same standard NIST leans on.
GDPR
GDPR doesn’t mandate liveness detection; it governs how the biometric data involved must be handled. Under Article 9, facial scans and biometric templates qualify as special category data, requiring explicit consent or another valid legal basis before processing. Article 25 (Data Protection by Design) pushes providers toward minimal retention, process the liveness check, then delete the raw data rather than storing it. Article 22 comes into play if a liveness result alone triggers an automated rejection, potentially requiring human review and the right to explanation. And Article 35 typically mandates a DPIA before any large-scale biometric deployment. In short, GDPR doesn’t tell you to use liveness detection but the moment you do, it substantially shapes your consent flows, data retention policies, processor agreements, and subject rights obligations around biometric templates.
iBeta Liveness Detection Testing
iBeta liveness detection testing is the most widely recognised third-party evaluation programme in the identity verification industry. iBeta conducts blind, standardized attack testing under ISO/IEC 30107-3 and certifies solutions at three levels.
- Level 1 covers common presentation attacks, including printed photographs, digital display screens, and video replays.
- Level 2 adds higher-fidelity attacks including 3D masks and AI-reconstructed faces.
- The most sophisticated stage, Level 3 is where testers have expert level skills and access to equipment like hollywood grade silicone masks and enough preparation time to trick the system.
Conformance with all three levels signals that a solution has been tested rigorously by an independent body against the most demanding attack categories in use today.
Shufti, today is the first european company to hold ibeta level 3 conformance with zero attacks accepted across all 900 attempts, zero bonafide users rejected.
Regulated organisations in financial services, healthcare, and government face a compliance question that goes beyond whether liveness detection is deployed. The question is whether the liveness detection in use has been independently tested at a level that regulators and auditors can verify and accept.
How Shufti handles Independently Validated Liveness Detection?
Shufti’s AI liveness detection runs in both active and passive modes, allowing businesses to set verification intensity based on the risk level of each event. The engine uses 3D depth analysis to confirm physical presence, comparing spatial geometry against biometric reference points to reject flat photographs, screen replays, and 3D mask attacks across 56+ spoofing attack vectors, including AI-generated deepfakes and injection attacks that bypass standard RGB cameras.
Shufti’s conformances with all three iBeta level tests independently validate its performance to reliably defend against most sophisticated attacks in use today. Independent testing under ISO/IEC 30107-3 confirmed 98.72% total facial biometrics accuracy, with the DHS RIVR 2025 Top Performer designation adding a second external validation across diverse demographic groups. Cases that fall near the confidence threshold, due to unusual lighting, partial occlusion, or a flagged anomaly, escalate to expert human review in real time. No edge case resolves without a second assessment, and no legitimate user is turned away without one.
See how Shufti performs against the spoofing attack types most relevant to your verification environment book a demo.
Frequently Asked Questions
How to do a liveness check?
A liveness check runs within the biometric verification flow. The user faces the camera and either responds to a brief prompt (active liveness) or aligns their face (passive liveness). The AI engine analyses presence signals and returns a result in under three seconds, without manual intervention for standard cases.
Are liveness checks safe?
Yes. Liveness checks analyse biometric signals to determine physical presence and do not retain raw video after the check completes. Systems certified under ISO/IEC 30107-3 and independently tested by bodies such as iBeta operate within published security and privacy standards.
How does liveness detection enhance digital identity verification?
Liveness detection adds a physical presence layer that face matching alone cannot provide. It confirms the face is genuinely there before the system runs a biometric match, blocking spoofing attacks that use photographs, video replays, or AI-synthesised faces to impersonate an account holder.
What are the key features to look for in a liveness detection solution?
Look for ISO/IEC 30107-3 conformance, iBeta Level 1 and Level 2 certification, both active and passive modes, 3D depth analysis, a documented false acceptance rate (FAR), and hybrid AI with human review for edge cases. On-premises deployment support matters for data-sovereign organisations.
What kind of data is required for liveness detection to work effectively?
Liveness detection works from a live camera feed captured at the moment of verification. The system extracts facial geometry, depth, and texture data in real time. No pre-stored photo of the user is required. The captured biometric is compared against the document photo during the binding step.
How scalable is liveness detection for high-volume verification systems?
AI liveness detection completes individual checks in under three seconds and scales to millions of events without accuracy degradation. Cloud deployments scale elastically with demand. On-premises options let organisations with strict data-residency requirements maintain throughput on their own infrastructure without routing biometric data externally.
How do liveness detection systems handle false positives and false negatives?
False acceptance rates (FAR) and false rejection rates (FRR) are calibrated to the risk tolerance of the use case. Businesses can adjust these thresholds based on sector requirements and route near-boundary cases to human review. Well-configured systems minimise both error types without trading security for conversion performance.












