OCR Reader | How Does it Streamline the IDV Process?
The unprecedented growth in business automation has created a competitive market where businesses strive to optimise their operation. Due to the increased demand that requires businesses to meet regulatory requirements, the rise has resulted in various issues for businesses online. The evolution of OCR reader technology has made it possible for enterprises to use this technology for effective verification. A study has revealed that the OCR market is forecasted to be valued at $27 billion at a CAGR of 15%. Understand what an OCR reader is and learn its importance, use, how it works, and its role in the verification process.
What is OCR?
An optical character recognition OCR Technology converts a text photograph into a machine-readable text file. When a customer, for example, scans an invoice or a receipt, the computer captures the scan as a digital file. They are unable to edit, search, or quantify the letters or content written in the image file using a text editor. A text file can, however, be converted from an image to a text file containing the image’s content.
Why is OCR Important?
Many businesses work with paper documents, such as invoices, receipts, legal documents, contracts, and so on. Recording and keeping all paper documentation is difficult and time-consuming, whilst also posing other risks of easier theft and loss. Despite the fact that paperless document management appears to be the way forward, scanning the document into an image presents difficulties. There is a manual component to the process, which can take a lot of time and is inefficient.
Furthermore, digitising this document content generates image files with the text hidden inside them. Image text can’t be interpreted by word-processing programmes just as the text formatted documents can. The challenge is solved by OCR and ICR technology, which converts text images into data that can be analysed by other business applications. Businesses can then analyse the data to optimise operations, automate procedures, save time, reduce manual effort, and boost productivity.
How does OCR work?
OCR systems are made up of a combination of hardware and software. The hardware is utilised to optically scan the page, whilst the software analyses the characters and converts them into machine-readable text.
Step 1: Image Acquisition
Technically, OCR software converts the document into two primary colours including, black and white rendition. The digitised image, or bitmap, is then analysed for light and dark subjects, the latter of which can be identified as characters to be recognised. The earlier areas, on the other hand, are classed as background, and so eliminated from further processing.
Step 2: Pre-processing
The dark portions are examined for alphabetical letters or mathematical figures. This stage of the procedure often targets specific characters and recognises them using one of two techniques: pattern recognition or feature extraction.
Pattern Matching
Pattern matching matches a character picture (called a glyph) to another equally stored glyph. Pattern recognition operates only when the stored glyph has a typeface with a comparable font and scale to the original glyph. As a result, the approach performs best with scanned versions of documents using conventional typefaces.
Extraction of Characteristics
Another kind of algorithm employs feature extraction, a technique that divides glyphs into attributes such as segments, closed loops, lines, line orientation, and line junctions. These extracted characters are then used to evaluate the most suitable match among the previously saved glyphs.
Step 3: Post Processing
Following analysis, the system saves the retrieved text data as an electronic document. The extracted information document can then also be utilised for automated form filling.
KYC Verification Using OCR Technology
The Know Your Customer KYC industry, like other industries, is benefiting from OCR reader technology to enhance its verification processes because of the vast amount of predetermined formats and machine learning algorithms. Technology powered by AI appears to be one of the more powerful arsenals in KYC verification. Businesses can use OCR technology to validate the smallest data, such as a person’s name, birth date, social security number, residential address, and other personal information.
Aside from that, OCR relieves consumers of a lot of stress by allowing them to easily scan and upload photographs of their identification documents. The verification begins as soon as the photograph is posted to the web portal. Because there is very little human participation, the possibility of error and delays is significantly reduced. It is safe to claim that OCR technology is an innovative AI-enabled technology that greatly streamlines the KYC verification process by providing auto-fill in a verification system.
Challenges in OCR in Identity Verification
Employing OCR in identity verification is difficult due to the tremendous growth and advancement of technology. It faces considerably more comprehensive and random work (each country’s identity cards and compliance requirements are unique): it must extract complicated data fields with minuscule fonts, holograms, watermarks, various backdrops, and many more. Not only that, but it must arrange and verify key information besides identifying it.
As the title implies, optical character recognition technology discerns characters (words, digits, numbers, symbols, and so on). However, for the OCR to differentiate or recognise certain characters, it must be trained in advance.
During software training, the parts or words that the OCR must recognise (for example, characters, holographic images, backdrops, and so on) are saved, together with the templates of the identity documents to be validated.
When a user takes a picture of an id verification document with a smartphone or a web camera during a verification process, the software must have the authorised format of the identity document as well as the text and other aspects registered. Only then will it be able to recognise the document type and accurately arrange the data it needs to extract.
Essentially, OCR technologies analyse documents and photos pixel by pixel to locate what characters they have internalised. They operate similarly to facial recognition technology in that the system searches for similarities with the data it has stored.
What the Future Holds for OCR
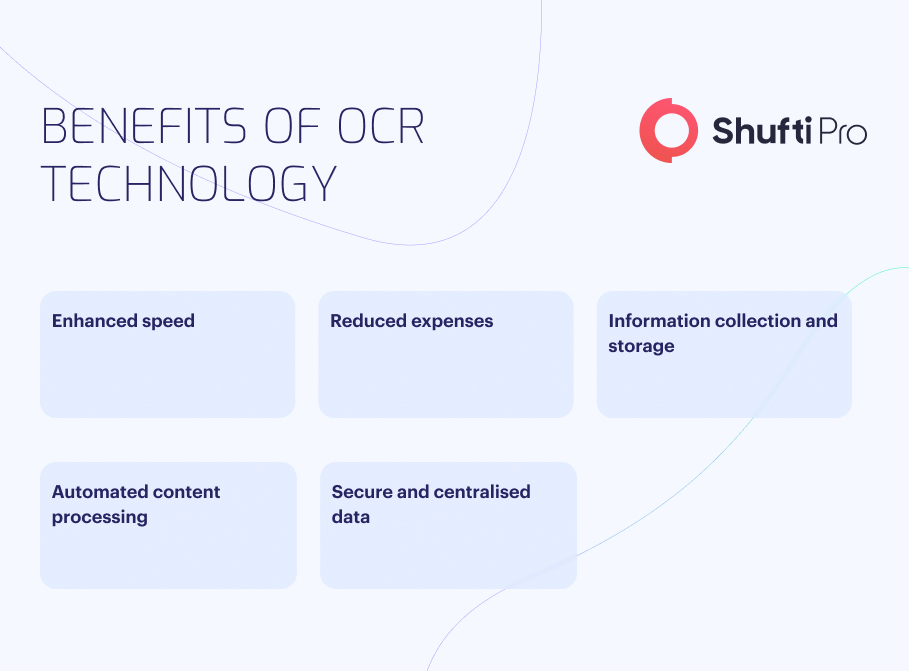
Optical character recognition enables far more accurate remote customer onboarding and ensures faster response times. Modern OCR technology not only assists in simplifying the procedure at the user end, but it also saves organisations money and time spent on manual data input activities. OCR technology may extract personal information from a digitised version of an identity document or translate a foreign language into the customer’s desired language.
The ability of today’s technological products to turn paper-based information into electronic information in real time is nothing but astounding. However, service providers continue to battle to remain a step ahead of other companies with the most accurate offerings on the market.
What Shufti Offers
Data collection and analysis are critical operations in businesses all around the world. Processing large amounts of consumer data can be difficult for online organisations in the finance, banking, investment, brokerage, insurance, and healthcare sectors.
Shufti‘s OCR for Enterprise integrates artificial intelligence to convert paper-based documents into digitised PDFs in real time. The system extracts data from a wide range of documents, including handwritten notes, business records, formal letters, invoices, and so on. Shufti’s OCR scanner supports over 150 languages and has worldwide coverage. Online firms may properly verify their consumer data with an astounding precision of more than 99% and reduce delays while verifying identities in real-time.
Need to extract sensitive information but still stuck to black-and-white technology and lack compliance assistance?












