Pension Fund Fraud and the Role of Employee Identity Verification

Old age is the scariest phase of life for everyone and organisations find it a big challenge to cater to the needs of their old employees. They cannot be retained as permanent employees after 60, but there is a gratifying reward for the employees after retirement – the pension fund. People spend years to save money for their old age and spend it peacefully, and companies fully support their employees, but is it just rainbows and unicorns for firms? With good comes bad! Pension funds are also a way of illegal activities and fraudsters are coming up with different ways of stealing pension funds from organisations.
If your company supports the retired employees, make sure you take all possible measures to keep the funds safe and readily available for them. As weird as it sounds, criminals do not leave any way of gaining financial benefits and your firm’s pension funds are not at all safe without any security measures taken. The details about pension fund fraud, how to identify them, and how to prevent them have been discussed in this blog. Keep reading to find out.
What is a Pension Fraud?
Pension funds are pools of investment that are collected for paying people after their retirement. Companies save some proportion of employees’ income that is accessible after retiring. Pension fund fraud occurs in two scenarios:
- A fraudulent attempt with the benefits of an employee’s pension funds.
- The common strategies from fraudsters to steal funds or fraudulently use other retirement benefits.
Conflicts between employer and employee result in the first type of pension fund fraud. The claim mentions that the employer is not providing the pension benefits or denying that there were any retirement benefits at all.
In the second scenario, some fraudulent activities, usually identity theft, result in loss of funds and these attempts are common now.
Read more about identity theft: 5 types of identity theft fraud and How businesses can prevent it?
Some Examples of Pension Fund Frauds
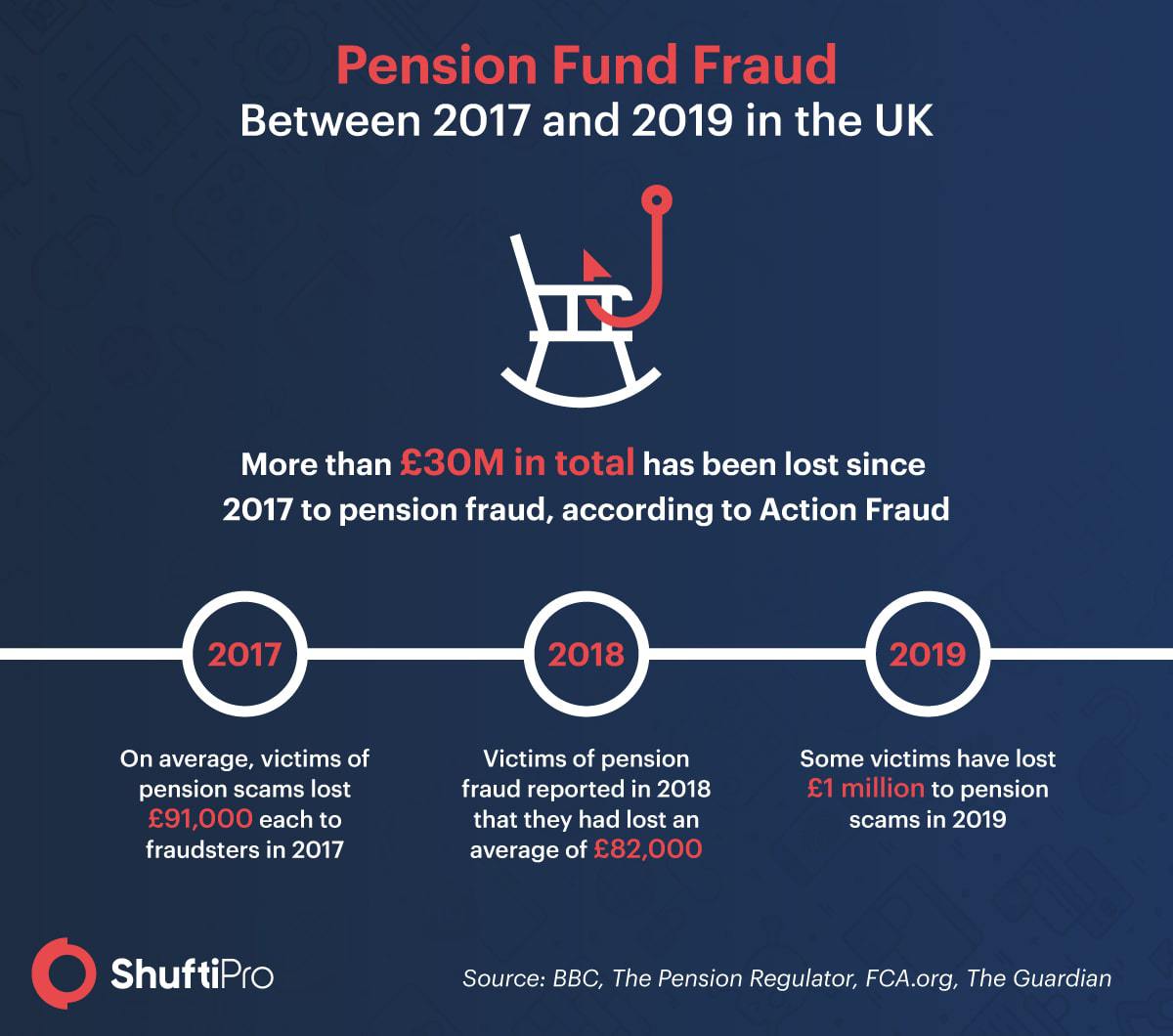
Pension-related fraud is increasing and The Times reported that investors lose £4 billion every year. The numbers are unknown in the year 2020. Let’s see how the COVID-19 pandemic will end up for the retired people. Take a look at some examples of pension fund fraud that your company might encounter.
Employees’ Fraudulent Activities for Pension Fund
Conflicts often end up in serious issues for all the employees in an organisation. Beware of the following activities in your company to avoid any pension-related fraud.
- One of the employees representing false numbers for paying the retiree.
- Misrepresenting the information regarding retiree’s transferable pension rights and benefits.
- False information about employee’s contribution to the retirement fund. Sometimes, retirees also communicate false information to get extra benefits. On the other hand, rivalry results in representing lower amounts so that the retiree gets the least pension funds.
- Tax-related issues can be associated to create problems in the release of pension funds.
These are some issues that can be audited so that none of your retired employees feel distressed or face challenges for spending their lives peacefully.
External Fraudulent Activities for Pension Funds
Amid the employees’ activities for messing up with the pension funds, fraudsters fight till the last breath. Here are some examples of fraudsters’ attempts to mess with pension funds.
- When a fraudster claims to be one of the family members and carries out a loan scheme from the retiree’s pension.
- Caretakers also claim pension loans on behalf of the person which is another scam alert for the company.
Online theft of pension funds is now the new normal for fraudsters. Keep your employees funds secure at all costs with digital identity verification. You can prevent fraudsters from gaining illegal access to your business.
How to Spot a Pension Fraud?
According to The Guardian, pension scams have cost £1 million to every victim and statistics for 2020 are still unknown. God knows where this will end up for the businesses. Nevertheless, there is always good news for businesses and you can spot pension fund fraud in no time with these tips in mind.
If your business gets a random application claiming pension funds, be sure to cross-check if the employee is near retirement or not.
Received an application for loan from a pension fund? Beware! It might be a scam. Fraudsters often appear as family members and claim loans from a person’s pension fund. It is ideal to create a policy that would not permit any loans without verifying consent of the employee.
How can Businesses Avoid Pension Scams?
Internal audits can help in identifying pension fund fraud if any employee is involved, but what to do about any fraudsters’ attempts? Moreover, claiming the funds after a fraudulent activity requires a lawsuit and the process never ends in some cases. Businesses can avoid pension scams if there are any identity verification measures for providing pension funds. This will not only help you cater to the needs of retirees efficiently, but it will also help your company in keeping the evil eyes away.
Identity verification is one way out of the rising problem. Your business needs a robust solution that can not only help you in onboarding legitimate employees for the company, but you can also authenticate the retirees before releasing their funds.
Identity verification in today’s digital world has also taken the virtual road. Verifying employees is helping different industries in remotely onboarding legitimate candidates and preventing fraud. Your company can secure pension funds with this process too. Resolving issues with the release of funds wouldn’t be a problem and fraudsters can be prevented from causing any issues for your retiring employees.
It All Boils Down To…
Retirement brings a lot of peace if the aftermath is not disappointing for the people. However, fraudsters make the simple retirement process inconvenient for the old employees. It is not only stressful for the workers to end their working phase, but there is a lot on their plates that is under consideration. Planning out the perfect life ahead can be convenient if they get the benefits on time without any external force messing up the process. Criminals are now targeting retirees to fulfil their malicious intent and stealing pension funds is the best way for them. Conflicts between employees result in a rivalry that never ends up well for anyone. The organisation becomes the biggest victim of all these issues. Hence, companies should consider employee verification to prevent fraud.
Eager to know more about employee verification? Get in touch with us today.













