Synthetic Identity Fraud: Fake Identities for Criminal Activity

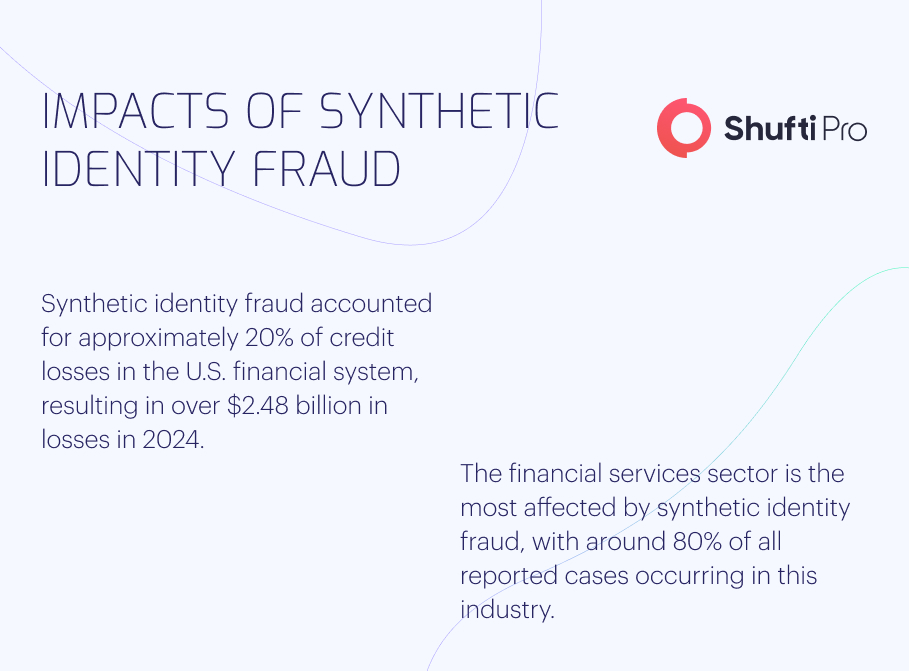
An increase in financial crime has been predicted by economic downturns during the previous two decades, most notably the Great Recession of 2007-2009. With this as a backdrop, Forbes estimates that synthetic identity fraud might cost up to $5 billion by 2024.
The damages from synthetic Identity fraud are in the billions of dollars, and they are rising faster than any other type of identity fraud. Synthetic identity fraud accounts for over 80% of all instances of account opening fraud. Identity thieves who use fake documents are devious and well-informed. To construct a new identity, they combine actual and made-up information. Once this identity has been established, the fraudster has a brand new persona from which to carry out an endless stream of fraudulent acts. Fraudsters using a stolen identity can go unnoticed for a long time while they rack up debts in their name. The fraudster will set up and operate various financial instruments before making a final, massive cash withdrawal and disappearing forever.
Synthetic Identity Fraud Scheme
Criminals who commit synthetic fraud use legitimate and fabricated data, such as names and social security numbers, to establish a new persona. The new identity is then utilised to commit fraud by opening new accounts at financial institutions, government agencies, or directly on the person’s behalf.
False or assumed identities are increasingly widespread in the United States. This is due to the fact that sensitive personal data like Social Security numbers are widely used for identity verification purposes in the United States. According to McKinsey, synthetic identity fraud constitutes the United States’ most rapidly expanding financial crime.
However, spotting this particular fraud can be challenging. Children, the elderly, and the homeless are at heightened risk since they are less likely to check credit reports regularly. In addition, fraudsters frequently care for these identities over time, applying for increasing amounts of credit and establishing a solid record of on-time online payments. They may go years without being seen before finally ‘busting out’ the credit line. This means that fraud often goes unreported and undiscovered for extended periods of time. The fundamental procedure of most synthetic identity fraud schemes is as follows:
Creating a Forged Identity
Scammers who use synthetic identity theft often target children and the homeless, from whom they can obtain social security numbers. In another sense, Frankenstein IDs are fake identities made up of bits and pieces of information acquired from numerous victims. Synthetic identities can be created from various sources, including social security numbers, bank account numbers, and email addresses. Data breaches, stolen records, and the dark web all make it easy for fraudsters to get their hands on personal information.
Applications for Loans
Criminals are submitting online loan applications utilising fraudulent identities. The initial application is typically denied because the synthetic ID needs a credit history. Establishing a credit history marks the beginning of the job as a whole. The con artist applies for the loan after loan until one is granted, albeit a modest one from a high-risk lender.
Improving Credit History
To raise credit scores and establish a good payment history, they begin using the credit and make payments on a regular basis. They could eventually qualify for a better rate or borrow from a different institution. After a period of time, the fraudster will blend in with legitimate credit users. For more compensation, sophisticated criminal organisations can build fictional companies by taking advantage of publicly available addresses.
Disappearance
Cons use false promises of increased credit limits to run off with the money. Some fraudsters use only one phoney ID at a time, while others rotate through several. Scammers who vanish without a trace are notoriously tough to track down. The only evidence is the victim whose Social Security number was stolen, and proving innocence can be difficult.
Risks of Synthetic Identity Fraud
Since synthetic identity fraud (SIF) perpetrators create a false identity rather than use a stolen one, they are much harder to catch than those who exploit stolen identities. There are a couple of problems that arise from this:
- Definable evidence of fraud cannot be established with SIF. This makes it hard to recognise a fraud issue and much harder to tell if the new safeguards are effective.
- Traditional forms of identity theft are more accessible to spot than SIF. Any time there is suspicious activity on a customer’s account, such as a login from an unfamiliar IP address, the financial institution is obligated to contact the customer.
However, con artists can use stolen identities to keep up appearances for weeks, months, or even years, all the while increasing credit scores and accessing ever-larger lines of credit before finally maxing out all of their accounts and disappearing.
Since it could be years before the victim realises they have been a victim of synthetic identity theft, it is most prevalent among children. Young people are disproportionately affected since they cannot access credit reports. When deciding whether or not to grant a credit card or other kind of credit, the lender will look at the applicant’s credit history in the databases of the three credit reporting bureaus. Similar to SIF, a new one will be created if no matching file is located.
Synthetic Identity Fraud Detection
There is currently no easy way to spot fake ID schemes, including synthetic documents. Businesses need an approach with multiple moving parts, ideally using several technologies working in tandem, such as data enrichment, digital footprint analysis, and accurate device fingerprinting. Nonetheless, consider these three suggestions for spotting synthetic fraud in financial institutions:
Cross-Check Data
A loan application may look legitimate at first glance. However, there are better ways to go than using a horizontal approach in which individuals only look at the information offered in the application. Looking at other data sources for a more holistic view of the candidate is worthwhile. It’s possible that the applicant’s name has already been used for another account or that the phone number provided belongs to someone who lives outside the nation.
Rethink Proof Burden
The fraudster community heavily relies on automated bank onboarding and application processes. A reasonable level of friction added to the application process, such as requiring candidates to provide proof of identity and income, could be a good idea. For instance, financial institutions can use step-up levels and friction layers to make it more difficult for fraudsters to execute more lucrative transactions while ensuring a seamless experience for most loyal customers.
Find Anomalies
Be on the lookout for any strange or unexpected shifts in behaviour. A borrower from a specific area code with good credit is sometimes out of the ordinary. A red flag would be raised, though, if applications from the same area went from a few hundred to several thousand in the span of a year.
In addition, the information may be deciphered to reveal whether many programmes with various names all originate from the same electronic device. Control reporting allows banks to monitor application rates to determine if they are under attack by comparing activity to normal default rates.
Methods to Prevent Synthetic Identity Theft
Every year, synthetic identity fraud becomes more of a problem, highlighting the need for a more streamlined user verification method. Social Security numbers and credit reporting agencies aren’t sufficient anymore because of the prevalence of data breaches, exposed PII, and the anonymity of the dark web. Standard methods of preventing identity theft often miss cases of synthetic identity theft.
Companies should spend money on cutting-edge identity verification techniques like document and biometric verification systems driven by AI algorithms. A synthetic identity that uses a legitimate Social Security number in conjunction with bogus information can get around a credit bureau check. Still, it has a lower chance of passing a document check. Furthermore, a con artist will probably not risk revealing their true identity via biometric verification.
Documents can be examined for authenticity with Shufti, which allows users to scan documents from any device. Shufti’s biometric verification makes it easy for a company to verify and link a customer’s identification to an account. Shufti’s hybrid algorithm quickly determines if an ID photo and a selfie are a match after the user snaps both images.
Role of AML/KYC Compliance in Synthetic Identity Fraud
Using the fake identities they’ve created, con artists can open new bank accounts, deposit unlawful sums, or even buy and ship things without raising suspicion about where the money came from.
The Know Your Customer (KYC) process helps identify suspicious actions by gathering and analysing customer data. Institutions should have a complete picture of customers. In this manner, it’s possible to tell if a transaction was obtained from a legitimate consumer or a scammer. On the other hand, it is possible to learn whether or not the identification is artificial.
Banks must follow Know Your Customer and Anti-Money Laundering rules to combat financial crime. Using synthetic identities, fraudsters can quickly launder money from financial institutions while evading detection. Financial organisations and banks are responsible for doing due diligence even while fraud is not at fault. Institutions risk steep AML/KYC compliance fines if the government determines they have not taken adequate steps to prevent fraud.
Shufti AML solutions include Know Your Customers (KYC), Transaction Screening, Customer Due Diligence (CDD), and Transaction Monitoring to help financial institutions in the fight against fraud.
How Can Shufti Help
Shufti is a formidable ally in the fight against Synthetic Identity Fraud. With a global presence spanning 230+ countries, an efficient 2+2 verification approach, multilingual OCR extraction covering 150+ languages, and robust synthetic fraud detection, Shufti’s KYC solutions ensure that customer identities are verified precisely. Our impregnable facial authentication adds an extra layer of security, while our intuitive No-Code Verification Journey Builder streamlines the verification process.
On the AML front, Shufti’s comprehensive screening checks against 1700+ data sources, including those from FATF, Interpol, UN HMT, and more, ensure you’re well informed about potential risks associated with your customers. Our real-time watchlist updates every 15 minutes, covering sanctions, PEPs, and adverse media, providing a comprehensive view of potential risks. Our ongoing AML monitoring keeps your business continuously vigilant against emerging threats. Shufti empowers financial institutions to stay ahead in the battle against synthetic identity fraud while maintaining compliance and safeguarding reputation.
Contact us if you want to learn more about synthetic identity fraud and how Shufti helps in identify fake identities for criminal activity.












