The 10 Biggest DeFi Hacks of 2022 and How Can KYC/AML Compliance Help
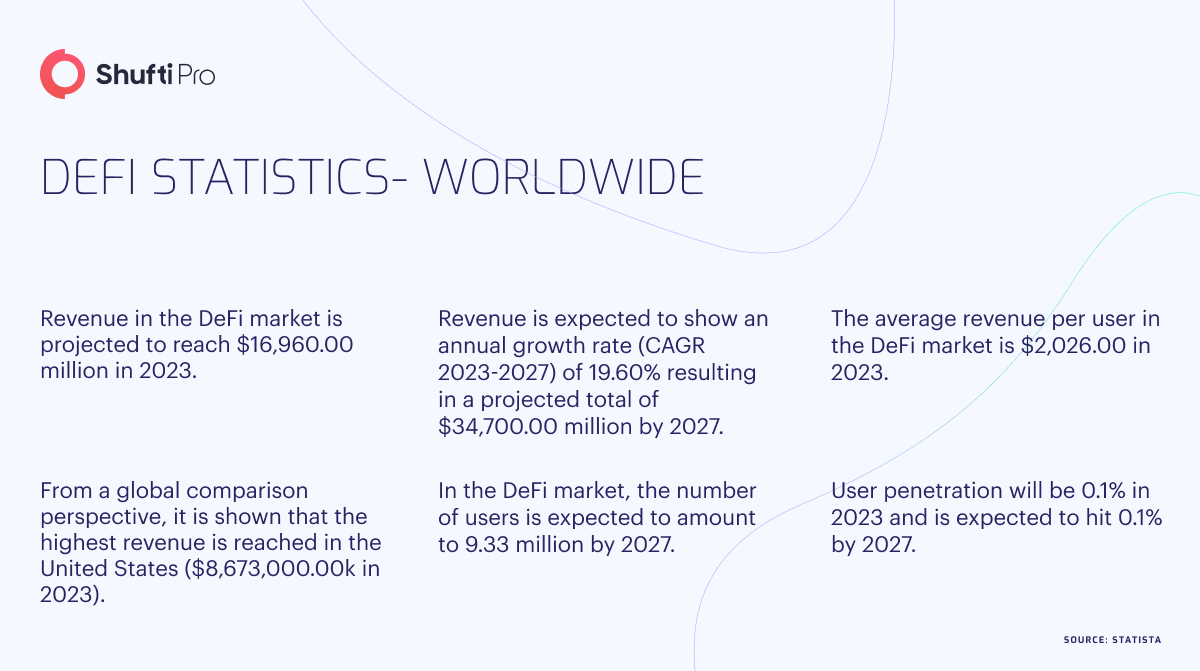
The crypto industry witnessed a challenging year in 2022, marked by numerous hacks and scams, highlighting once again the risks associated with Centralised Exchanges (CEX) and custody. FTX and other entities like 3 Arrows Capital, BlockFi, and Voyager suffered significant setbacks, intensifying the industry’s struggles. As Terra (LUNA), 3AC, and Celsius collapsed, the FTX incident hit the industry hard. Meanwhile, the Decentralised Finance (DeFi) sector is facing a growing crisis characterised by frequent hacks and exploits, albeit with less public attention. The surge in DeFi-related thefts in 2022 has made investing in this sector increasingly risky. The industry must find practical solutions to address these vulnerabilities within DeFi. Failure to do so may result in a collapse of trust among serious crypto users and the wider crypto community.
Top 10 DeFi Hacks (2022)
Like all other sectors, DeFi is also vulnerable to hacks. The year 2022 witnessed a significant number of DeFi hacks, as under:
1. Qubit Finance
In January 2022, a cybercriminal successfully stole over $80M from Qubit Finance, a protocol operating on the Binance Smart Chain. The hacker exploited a deposit feature within Qubit’s QBridge contract. Upon investigation, CertiK, a security firm, discovered that the hacker utilised the deposit feature to generate 77,162 qXETH tokens, representing Ether. These tokens were then employed to drain all BNB funds from QBridge. The company tried to persuade the hacker to return the funds to rectify the situation, proposing a smaller sum as a legal bug bounty. Unfortunately, these attempts were unsuccessful.
2. Wormhole Bridge
In February 2022, a significant security breach occurred within the Wormhole Bridge, leading to the loss of 120,000 Wrapped Ether (WETH) tokens. These tokens were valued at around $325M during that period.
The perpetrator successfully bypassed the bridge’s verification protocols and proceeded to mint the wrapped tokens. Subsequently, they exchanged these tokens for ETH on the Ethereum network and various alternative cryptocurrencies on Solana.
To rectify the situation, the Wormhole team offered a bug bounty of $10M to recover the stolen crypto. However, no individual came forward with information or assistance. Wormhole’s venture capital backer, Jump Crypto, replenished the missing cryptocurrency to avert potential inflation risks and maintain user confidence in the bridge.
3. Ronin Bridge
In March 2022, an individual stole 173,600 Ether and 25.5M USDC, which amounted to approximately $625M, from the Ronin Network. The attacker employed compromised private keys to transfer the funds away from the network swiftly.
Ronin, a side chain of the Ethereum network that facilitates the Axie Infinity P2E game, had nine validators at the time of the attack. To authorize withdrawals, a majority of signatures were required. However, the attacker exploited a backdoor and accessed five private keys.
Subsequently, Sky Mavis, the company behind Axie Infinity, announced that they had raised $150M in collaboration with Binance to compensate affected users partially. Concurrently, United States officials linked the North Korean Lazarus group to criminal activity.
4. Beanstalk Farms
In April 2022, the governance system of Beanstalk Farms, an Ethereum-based stablecoin protocol, witnessed the complete loss of its Total Value Locked (TVL), amounting to $182M.
During the investigation conducted by blockchain security firm PeckShield, it was discovered that the attacker leveraged a flash loan to obtain a substantial quantity of Beanstalk’s native governance token, STALK. With this significant ownership, the individual could propose and pass measures related to donations for Ukraine.
The attacker managed to steal approximately $80M in various cryptocurrencies, causing the BEAN stablecoin to deviate from its peg of $1, resulting in the complete depletion of Beanstalk Farms’ $182M TVL. Ultimately, the stolen cryptocurrency was laundered using Tornado Cash.
5. Maiar Exchange
In June 2022, Maiar Exchange, a decentralised exchange on the Elrond blockchain, witnessed a significant security breach. The attacker took advantage of the vulnerability in the exchange’s smart contract, enabling them to withdraw Elrond eGold (EGLD) tokens valued at around $113M. Promptly after the breach, the hacker initiated the sale of the stolen EGLD tokens on the Maiar Exchange. This action resulted in a temporary 92% drop in the value of EGLD. Subsequently, the attacker converted the EGLD to ETH and sold it on other exchanges.
6. Horizon Bridge
In June 2022, a hacking group known as the Lazarus Group, affiliated with the North Korean government, successfully breached the Horizon Bridge.
This cyberattack resulted in the theft of approximately $100M worth of various cryptocurrencies, including Ether, Tether, and wrapped Bitcoin. After conducting an investigation, blockchain analysts at Elliptic were able to trace the origin of the attack and discovered that some of the stolen assets were routed through Tornado Cash, a coin-mixing service.
Based on their analysis, the Elliptic analysts noted that the method used by the hackers to automate deposits into Tornado Cash bore similarities to previous hacks attributed to the Lazarus Group, such as the Ronin Bridge hack that occurred in March 2022.
7. Nomad Bridge
In August 2022, hackers targeted the Nomad cross-chain bridge, stealing over $190M from the platform. The attack involved many addresses and commenced with a suspicious transaction that drained 100 wrapped Bitcoin tokens.
Subsequently, a series of transactions systematically depleted all digital assets within the Nomad platform. The exploitation was made possible by a flaw in the Replica contract utilized on the bridge. This flaw allowed anyone to identify a transaction, replace their address, and broadcast it anew.
The attack persisted for three hours and was facilitated by an update introducing the vulnerability. In response, Nomad initiated a bug bounty program and managed to recover $20M in stolen cryptocurrency by offering assurances that charges would not be pursued against those who returned the funds.
8. Wintermute
In September 2022, Wintermute, a crypto market maker, fell victim to a DeFi hack, resulting in a substantial loss of approximately $162M. Following a thorough investigation, Certik, a blockchain security firm, determined that the hack was not a result of a vulnerability within the smart contract itself. Instead, it was traced back to a vulnerable private key. It is suspected that the private key may have been compromised either through a leak or obtained through brute force. Additionally, Certik highlighted a potential flaw in the Profanity vanity address generator as a contributing factor to the incident. At the time of the hack, Wintermute had a significant outstanding DeFi debt totalling around $200M across various platforms, with TrueFi being the largest creditor holding a deficit of $92M. Despite the hack, Wintermute honoured its obligations and successfully repaid its loan to TrueFi.
9. Mango Markets
In October 2022, Mango Markets, a DeFi platform built on the Solana blockchain, experienced a loss of approximately $114M due to an attack in which the perpetrator manipulated price oracle data. This manipulation allowed them to obtain significant loans without providing sufficient collateral.
The attacker initially deposited $5M into the platform to execute the attack, using it to open a significant long position in MNGO-PERP. This action caused the price of MNGO to surge, thereby increasing the value of the collateral held by the attacker. These raised funds were subsequently utilised to acquire additional debt positions on Mango.
Ultimately, the protocol permitted the attacker to return $67M worth of the stolen tokens while allowing them to retain the remaining $47M as a bug bounty reward. The attacker was later identified, who defended his actions by claiming they were “legal” and characterized it as a “highly profitable trading strategy.”
10. BNB Chain
In October 2022, an incident occurred on the cross-chain bridge of Binance’s BNB Chain, creating additional BNB tokens within the network. A developer associated with BNB Chain shared details on Reddit, disclosing that the attacker had withdrawn between $100M and $110M. This amount was considerably lower than the initial estimation of $600M.
According to the developer, the exploit occurred on the BSC Token Hub, which acts as a bridge connecting the BNB Beacon Chain and the BNB Chain. The vulnerability stemmed from a bug in the bridge’s smart contract, enabling the execution of forged transactions responsible for the exploit.
KYC and AML Compliance to the Rescue
Know Your Customer (KYC) and Anti-Money Laundering (AML) compliance plays a crucial role in preventing DeFi hacks through several measures:
- Strengthen Security Measures: KYC and AML compliance solutions implement rigorous identity verification procedures to authenticate user identities. This helps mitigate the risk of fraudulent activities by ensuring that participants are accurately identified within DeFi platforms.
- Smart Contract Audits: KYC and AML solution conducts thorough audits of smart contracts utilised in DeFi protocols. This meticulous code review helps identify and address potential vulnerabilities or loopholes, minimising the risk of exploits and unauthorised access.
- Transaction Monitoring and Analysis: KYC and AML solution help in advanced transaction monitoring systems that analyze patterns and detect suspicious or abnormal activities. These systems can promptly identify potential money laundering or illicit transactions, protecting the platform from penalties for non-compliance.
How Can Shufti Help?
Shufti offers AI-powered KYC and AML compliance solutions to 230+ countries and territories, supporting 150+ languages to verify identities. Our robust IDV suite verifies identities within seconds and mitigates the risk of fraudulent activity in the DeFi platforms. Not only this, but our IDV solution does help the sector comply with regulations and avoid heavy fines.
Still confused about how KYC and AML compliance solutions protect DeFi platforms from hacks?












