What is eKYC: Meaning, Process & Digital KYC Benefits?

Governments have mandated various businesses, including financial institutions, to thoroughly understand their clientele worldwide to comply with regulations. These regulations, called Know Your Customer (KYC), aim to detect and prevent financial crimes such as money laundering.
The fundamental requirement of KYC is identity verification, which entails ensuring that customers are genuinely who they claim to be. In the past, IDV involved scrutinising information provided through physical forms and documents. However, with the increasing digitisation of the world, KYC policies and practices have had to adapt to meet customer expectations and address risks associated with digital interactions. Thus, electronic KYC (eKYC) came to the rescue; here, eKYC full form is electronic know your customer.
What is eKYC?
Electronic KYC is the digital method of verifying identity and other necessary KYC obligations. The approach may vary based on industry, business requirements, and customer preferences. However, it generally encompasses using electronic forms, digital records, and different levels of automation. Similar to conventional KYC procedures, eKYC is typically carried out during the initial account opening process and is subsequently maintained on an ongoing basis.
Difference Between KYC and eKYC
KYC is the traditional way of verifying a customer’s identity. It usually requires physical documents, paper forms, and sometimes an in-person visit to a branch. The process can take time because employees manually review the information.
eKYC, on the other hand, completes the same verification process digitally. Customers can upload documents online, use biometric checks, and get verified within minutes. While both methods aim to prevent fraud and meet regulatory requirements, eKYC makes the process faster, simpler, and more convenient in today’s digital world.
Why is eKYC verification important?
In an era where digital fraud is becoming increasingly sophisticated, eKYC verification has emerged as a critical safeguard for businesses and their customers alike. Whether you are a bank, a fintech startup, or an online marketplace, deploying a reliable eKYC service is no longer optional, it is a fundamental requirement for sustainable growth.
- Regulatory compliance: Businesses across sectors must meet strict ekyc compliance requirements set by regulators such as FATF, FinCEN, and local financial authorities. Failure to verify customer identities adequately can result in significant penalties, licence revocations, and reputational damage.
- Fraud prevention: Modern eKYC systems cross-reference identity data against government databases, sanctions lists, and behavioural signals in real time. This multi-layered approach makes it substantially harder for fraudsters, money launderers, and identity thieves to slip through undetected.
- Faster customer onboarding: Traditional, paper-based verification can take days. eKYC software automates identity checks so businesses can onboard verified customers in seconds, dramatically reducing drop-off rates and improving conversion.
- Cost efficiency: Automating verification reduces dependency on manual review teams, lowering operational costs while maintaining the rigorous ekyc compliance standards demanded by regulators.
- Global scalability: A trusted eKYC service supports multi-jurisdictional compliance, enabling businesses to verify customers from different countries without manual intervention and without compromising on local regulatory requirements.
- Customer trust: Consumers increasingly expect secure, seamless digital experiences. A robust eKYC process signals that a business takes data protection and identity security seriously, building long-term customer confidence.
How eKYC process work?
Today’s eKYC systems have the potential to provide businesses with a more comprehensive understanding of their customers’ identities. This is due to the broader range of data and indicators that eKYC can leverage, surpassing what is typically available in traditional KYC procedures. Conventional KYC relies on active indicators, such as Personally Identifiable Information (PII) the user provides and third-party data from watchlist reports. In simple terms, eKYC meaning involves blending active data with passive and behavioural signals that manual checks of paper documents often fail to capture.
Active Signals
Active indicators comprise information directly provided by the individual, including but not limited to:
- Name
- Address
- Date of birth
- Social Security number
- Employment information/source of funds
Furthermore, active indicators encompass any submitted ekyc documents and photos, such as government-issued IDs, bank statements, selfies, etc. In addition to the transition towards ectronic know your customer, governments like India and Estonia have introduced electronic identification forms, serving the same purpose as physical IDs. Although the concept of eID has yet to gain widespread acceptance at the federal level in the United States, several states have embraced it. States such as Arizona, Colorado, Georgia, and Hawaii accept digital driver’s licences, which can be securely stored in an app or even an Apple wallet, depending on the state’s provisions.
Third-party Data
Third-party data refers to signals not directly or indirectly provided by the individual but rather obtained from external sources such as government entities, private enterprises, and authoritative databases. These datasets encompass various types, including:
- Government watchlists
- Sanctions lists
- Lists of Politically Exposed Persons (PEPs)
- Phone risk reports
- Email risk reports
- Adverse media reports
During the account opening process, third-party data is typically collected in the background, allowing businesses to enhance their understanding of customers without creating additional obstacles to the KYC process. Furthermore, many companies regularly cross-reference customer profiles with these sources to ensure the individual’s status remains unchanged.
Passive Signals
Passive signals, also known as device signals, are derived from the device that individuals use to undergo the KYC process. These signals are typically obtained in the background without the individual’s awareness. They encompass various data points, including:
- IP address
- Location data
- Device fingerprint
- Browser fingerprint
- Metadata
- Use of a VPN
Passive signals play a crucial role in online Know Your Customer as they enable digital verification and cross-referencing of the information provided actively by the individual with the data passively provided by the device. For instance, if someone claims to be in California, but their IP address indicates they are currently in Florida, further investigation may be warranted to ensure their authenticity.
Behavioural Signals
Behavioural signals are derived directly from the actions of individuals as they engage with online forms or applications. Generally, individuals are unaware that their behavioural signals are being monitored, assessed, and analysed. Examples of behavioural signs encompass:
- Detection of hesitations
- Identification of distraction events
- Tracking of mouse clicks and keyboard strokes
- Usage of developer tools
- Implementation of copy-and-paste operations
- The use of autofill functionality
Behavioural signals serve a range of purposes; for example, analysing behavioural data can assist in distinguishing between genuine human users and automated bots when completing a form or application. Similarly, it can contribute to detecting potential identity theft cases, such as when a form is completed suspiciously. Consequently, behavioural signals, like passive signals, hold significant importance within the domain of eKYC.
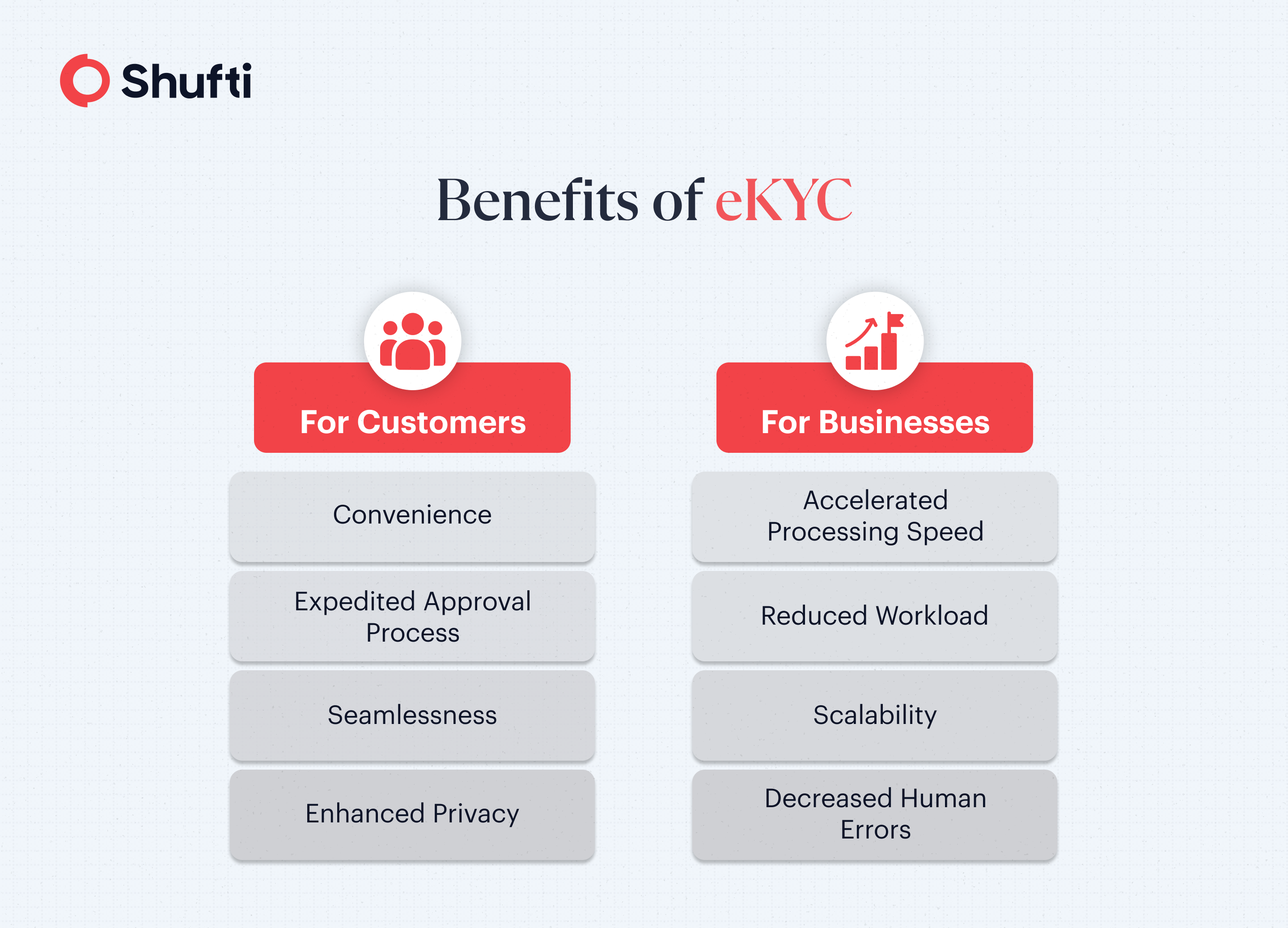
What are the Benefits of eKYC?
eKYC offers numerous advantages, primarily due to its ability to leverage automation more than manual identity verification processes by human personnel.
For customers, the benefits include:
- Convenience: Individuals and businesses can complete forms and applications without the need to scan physical documents, print paper forms, or visit physical branches.
- Expedited Approval Process: Automatic review of electronic data enables customers to enjoy faster approvals for account opening.
- Enhanced Privacy: Embracing eKYC typically entails fewer human individuals reviewing sensitive data as it is processed automatically by the system. This translates into improved overall privacy for customers.
For companies, these benefits include:
- Accelerated Processing Speed: Upon submission of customer information, identity verification can be completed within seconds by advanced eKYC platform, significantly faster than manual review. This expedites the process, reducing drop-offs and enhancing conversion rates.
- Reduced Workload: With diminished reliance on manual review, financial institutions require fewer employees dedicated to KYC, enabling the reallocation of resources to other areas.
- Scalability: By minimising the need for hiring and training manual reviewers, eKYC processes facilitate business growth and scalability. Furthermore, the availability of electronic KYC services around the clock ensures continuous business operations beyond regular working hours.
- Decreased Human Errors: The reduced involvement of humans minimises the risk of errors, resulting in more efficient workflows.
How Can Shufti Help?
Shufti offers eKYC solutions to 230+ countries and territories and supports 150+ languages, helping businesses keep scammers away and comply with regulations.
Here’s what makes Shufti’s eKYC service stand out:
- No document uploading
- Fast customer onboarding
- 99.3% accuracy rate and verifies clients within seconds
- Real-time authentication from government databases
Want to know more about how eKYC helps businesses keep scammers away?
Frequently Asked Questions
What is eKYC verification?
eKYC verification is the digital process of confirming a customer’s identity. It uses online document checks, biometric verification, and database cross-referencing to complete KYC requirements quickly and securely.
What does eKYC mean?
eKYC meaning stands for Electronic Know Your Customer. It refers to the fully digital process of verifying a customer's identity using electronic methods such as document scanning, biometric checks, and real-time database lookups. eKYC is the digital evolution of traditional KYC, designed to make regulatory compliance faster, more accurate, and accessible in today's interconnected world.
Which documents are needed to complete eKYC verification?
eKYC usually requires a government-issued ID, such as a passport, national ID card, or driver’s license. With Shufti, users can upload their ID and complete a quick selfie verification, allowing the system to verify identities in seconds while ensuring KYC and AML compliance.
How can I do eKYC online?
To complete eKYC online, visit your bank's or service provider's website or mobile app and navigate to the identity verification section. You will typically need to upload ekyc documents such as a government-issued ID and a recent selfie, or complete a short live video check. The eKYC software processes your documents and biometric data automatically, with most verifications completing within seconds. Some providers also offer OTP-based verification linked to your registered mobile number for an even faster experience.
Is eKYC legit?
Yes, eKYC is a fully legitimate and legally recognised identity verification process. It is used by banks, fintech companies, insurance providers, and regulated businesses worldwide. eKYC systems operate within established regulatory frameworks, including FATF guidelines and local KYC/AML laws, and are built to strict data security and privacy standards. If a service asks you to complete eKYC, it is a standard compliance requirement, not a red flag.
How do I check my eKYC status?
You can check your eKYC status by logging into your bank's or financial service provider's app or portal and navigating to the profile or account settings section. Most platforms display whether your verification is approved, pending, or if additional ekyc documents are required. If you are unsure of your status, contact your provider's customer support team with your account details and they can confirm it directly.
What is the difference between CKYC and eKYC?
CKYC (Central KYC) is a centralised system that stores customer KYC records in a single government-managed registry. On the other hand, eKYC is the digital method used to verify identity online, while CKYC focuses on maintaining and sharing verified KYC data across institutions.












