AML Compliance in the UK’s Financial Sector – What Shufti Offers

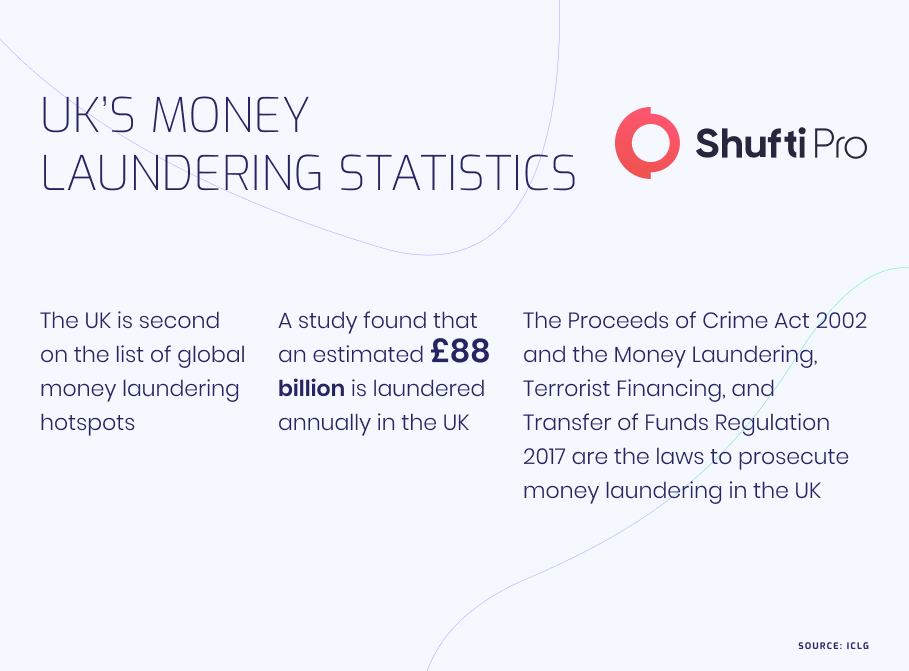
The UK is known in the global financial paradigm for being both a financial hub and the dirty money capital of the world. Considering the challenges faced by the region in the form of money laundering and terrorist financing, the UK has demonstrated significant progress in strengthening its KYC/AML regime.
That being said, the numbers don’t speak in the favor of the UK as the National Crime Agency has stated that financial crimes cost the major financial centre a whopping £100 billion annually. Identity fraud and money laundering are the two major areas of concern for businesses and financial institutions operating in the UK.
KYC/AML Requirements in the UK
In order to clamp down on financial crimes like money laundering, the UK constantly updates and strengthens its Anti-Money Laundering (AML) measures. For financial institutions and FinTech firms operating in the UK, AML compliance is not only a matter of fulfilling a legal obligation. Apart from compliance with the regulations set forth by regulators, businesses need to secure their operations, and most importantly, their reputation.
Incorporating robust measures for identity verification and background screening of customers allows banks and FinTech firms to prevent their financial processes and accounts from being affected by illicit activities.
The UK has more than one law and legal act to ensure AML compliance in its financial sector. The first and oldest law is the Proceeds of Crime Act of 2002, which lists three main money laundering offences:
- Concealing, disguising, converting, transferring, or removing criminal property from England and Wales or from Scotland or Northern Ireland (Section 327).
- Entering into or becoming involved in an arrangement, and knowing or suspecting that it facilitates (by whatever means) the acquisition, retention, use or control of the criminal property by or on behalf of another person (Section 328).
- Acquiring, using, or possessing criminal property (Section 329).
Moreover, the UK introduced the Money Laundering, Terrorist Financing and Transfer of Funds (Information on the Payer) Regulations in 2017. Apart from these two regulations, the Electronic Identification and Trust Services for Electronic Transactions Regulations (2019) also help monitor AML processes. The Financial Conduct Authority (FCA) is the government regulator that ensures compliance in both financial firms and the FinTech industry.
The FCA is considered one of the most progressive and innovative regulatory authorities in the world. It directs its efforts to ensure that the UK’s financial firms adhere to the standard global AML requirements, procedures, and adoption. Most of the global AML regulations are issued by the Paris-based financial watchdog Financial Action Task Force (FATF). Furthermore, the UK has also come up with concepts of its own to regulate different industries. These include developments in RegTech and a broadened regulatory scope to include the crypto sector through new and improved automated processes.
UK’s AML framework After Brexit
In January 2020, the UK was no more a part of the European Union, which did not have a significant effect on the country’s AML regulations. This is because most of the prominent laws were already introduced before Brexit. Even the regulations stated in the European Union’s Anti-Money Laundering Directives 5AMLD and 6AMLD are covered by UK law. That being said, the UK law did see some smaller changes through the years.
For instance, the UK law now considers EU member states for the list of high-risk “third countries” and treats them with different risk factors. This is quite ironic as the list of third countries was previously overseen by the EU. Although there is only one EU country (Malta) that is considered high-risk, the list is now managed by the UK. The other small change to UK law came in the form of the Trade and Cooperation Agreement (TCA), which regulates the EU-UK relationship and sets several conditions for the transfer of information and AML standards. This also involves the updating and maintenance of centralized beneficial ownership registers.
How Businesses and FinTech Firms Can Comply
Even though the UK’s AML regulations do not state a set procedure for the use of specific techniques for ensuring KYC compliance, they do stress its importance. The process of ensuring KYC compliance in businesses, banks, and FinTech firms requires three key measures:
Identity Verification
The initial stage in securing any financial operation is to ensure that the institution onboards legitimate customers only. As most financial operations are now moving online, there is an increasing demand for robust online identity verification solutions. Online identity verification allows businesses to authenticate their customers’ identities in real-time and eliminate the risks of financial crimes.
CDD and EDD
Customer Due Diligence (CDD) is a basic requirement for banks and other institutions that process payments and deal with transactions. It allows the company to establish trust by identifying the customer’s risk factors. For high-risk customers, the UK regulations advise financial institutions to adopt Enhanced Due Diligence (EDD) measures. Due diligence measures include processes to perform AML Screening to verify whether the customer is present on global watchlists or lists of Politically Exposed Persons (PEPs).
Ongoing Transaction Monitoring
In many cases, it is not enough for businesses and banks to perform KYC verification during the onboarding stage only. It is of equal importance to perform ongoing monitoring in case a customer is legitimate but their transactions are linked to illicit crime networks.
Perks of Automated Verification Solutions
In recent times, financial institutions have demonstrated fast-paced adoption of automated processes for KYC compliance. According to surveys from companies throughout the world, firms believe that automated solutions have taken them years ahead in their digital transformation, especially during the Covid pandemic.
Moreover, there have been significant developments in the areas of KYC and AML. The evolution of eKYC measures, which automate the whole process of KYC verification began with the transition of these services to online platforms. Currently, KYC processes involve the use of Video KYC (video-based verification) for secure digital onboarding.
What Shufti Offers
FinTech firms like any other financial institution are required to comply with international and local regulations. Compliance for banks is becoming easier as they standardize their operations. However, FinTechs still need to catch up and develop the same level of compliance.
Shufti’s Anti-Money Laundering (AML) screening allows banks and FinTech firms to stay compliant with regulatory standards as well as prevent money laundering. Powered by thousands of AI algorithms, Shufti’s AML screening solution also screens customers against 1700+ global watchlists in less than a second with 98.67% accuracy.
Want to learn more about our AML Screening solution for your financial institution?












