Anti-Smurfing Solutions | Safeguard Your Business Against Money Laundering Risks

Businesses are under constant threat of financial damage. This is primarily because cybercriminals and fraudsters are constantly utilizing different tactics to infiltrate business processes. This allows illegal entities to commit crimes like money laundering undetected by businesses, which ultimately raises security concerns.
In most cases, money laundering is carried out when a criminal gains access to a business’s general processes, this can be as a customer or as an employee. Once an entity gains access, it can create backdoors and access crucial information. This poses a financial threat to a company, and a data breach exposes it to identity theft. These criminals can also use the stolen identity data of users to commit further crimes. The United Nations Office on Drugs and Crime (UNODC) study reveals that the volume of money laundered annually may be as much as 5% of global GDP. That’s a staggering figure, equating to roughly $2 trillion.
Structuring and Smurfing: Money Laundering Methods
Companies usually have doubts about what is smurfing in money laundering. Smurfing splits illegal funds into small sums to create a streamlined money-washing mechanism, ultimately helping the business avoid regulatory scrutiny. A similar and more widely used term is “structuring.” Both of these are money laundering mechanisms primarily used to wash money, but both differ in their end goals. Structuring primarily involves concealing assets into smaller packets that make the reporting process look normal. In most cases, money laundering is caught because of the reporting process. If a regulatory authority finds something lacking in funds and records in a report, it conducts further checks on the entity. This is primarily why criminals use fund structuring.
The primary purpose of smurfing is to help criminals avoid regulatory checks overall. Its primary aim is to disguise funds so well that regulatory authorities look over them even after conducting detailed checks.
Smurfing is a criminal offense because it facilitates criminals to launder the proceeds of illegal activities, such as drug trafficking, terrorism, and fraud. This ultimately allows them to finance their criminal operations and avoid law enforcement. Global regulatory authorities have also introduced strict AML/CFT regulations for companies to prevent this activity. A business that fails to comply with these rules and regulations is subject to heavy penalties and fines.
The Mechanics of Smurfing: How Does it Work?
What is smurfing? Smurfing is highly variable and depends on the amount of money being laundered. It is also significantly affected by the activity from which the finances have been extracted. Moreover, the gateway being utilized for this act contributes a lot to the smurfing mechanism.
-
Depositing Finances
The most crucial part of the smurfing process is getting the illegal cash into the legal cash flow. This is where legitimate businesses are utilized because of their legal presence. A criminal establishes relationships with this business as a customer or a company. These businesses cannot differentiate between what a Smurf account is.
These criminals act as investors or customers, buying a service in massive quantities. This process washes away the black money without raising security concerns. Surfers may also deposit small amounts of cash, often just below the reporting threshold set by financial institutions, at multiple banks or branches over some time.
-
Micro-Structuring
A Smurf account is then used to micro-structure the funds. The deposited funds are wired to legitimate accounts in small packages under the reporting threshold. A complete cycle from the legal cash flow is needed to make black money eligible for use. Once these funds make a round from Smurf accounts into legit accounts in small packets, they are eligible for standard transactions.
Regulatory authorities can still trace this if the transaction’s origin is traced. The catch is that the criminals keep the amounts just below the reporting values. Numerous transactions of this sort are being conducted daily, and a business cannot possibly carry out detailed checks on all of them. Companies need a robust AML system for this.
-
Purchasing Goods and Services
Now that the criminals have the smurfed funds in legitimate accounts and money smurfing has been carried out successfully, they can use it to wash them for the final time. This step makes the funds legitimate, and they can be used for whatever purpose the criminals intended.
In most cases, surfers may use illicit cash to purchase goods and services, such as prepaid cards or gift certificates, which can be easily converted into cash or used to make online purchases. Once the smurfed funds are all individually washed, the last step is to gather those finances into the initial criminal’s account. For this purpose, these criminals can utilize different investment opportunities or cash-return schemes that direct the funds into the recipient’s account.
The Impact of Smurfing on Businesses
The most prominent damage smurfing money laundering deals to businesses is reputational damage. Establishing relationships with such illegal entities is a gamble for businesses, as it can lead to heavy fines and potential bankruptcy. These criminals can even damage businesses directly by selling the information to criminals who rely on ripping businesses off.
Moreover, the company loses the trust of its shareholders and investors, as the financial loss also directly impacts them. This will create a negative image of the business in the market, preventing future investors and partners from engaging. Regulatory scrutiny is also a significant concern, as a business can be put on regulatory blocklists, significantly impacting its scale and scope.
Operational disruptions that delay other business processes are bound to occur. Repairing the damage dealt by money smurfing is also a resource-intensive task, and small businesses might need help to afford it. Moreover, compliance costs after the damage are also massive and unaffordable for standard companies.
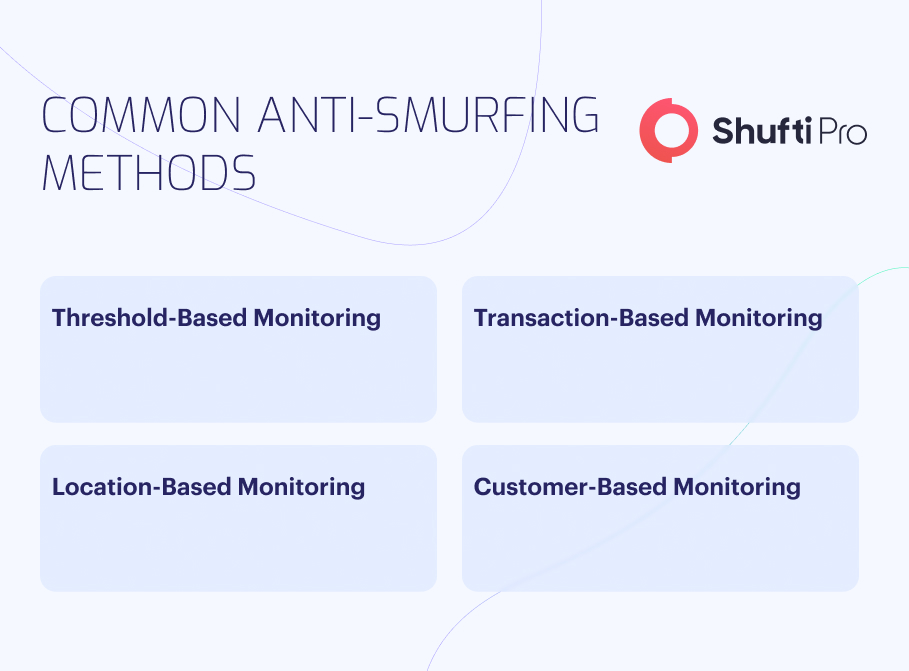
Anti-Smurfing Solutions: Preventing Laundering
The first and foremost preventive measure against smurfing money laundering is the regulatory compliance acts imposed by global authorities. These regulations require businesses to maintain proper records, implement anti-crime security protocols, and report suspicious activities promptly.
-
Transaction Monitoring
This is a process that financial institutions require the most, but it is now essential for regular small-scale businesses to implement it as well. This process has the ability to identify illegal transactions and then trace them thoroughly. Loopholes are identified by effectively tracing the transactions, which helps businesses prevent illegal transactions from flowing. A standard transaction monitoring system monitors all aspects of a transaction, ranging from its origin to its intent.
-
Customer Due Diligence (CDD)
Customer due diligence (CDD) allows businesses to identify shell companies and non-existent entities. AML smurfing uses fake information and stolen identities because accurate information can expose criminals. A customer due diligence process conducts a thorough verification check on an entity and creates a whole customer journey. By effectively mapping its past digital footprint, the CDD check determines whether it is a fake entity posing to be accurate or a legitimate customer. Smurfing is prevented before it starts.
-
Know Your Customer (KYC)
Know Your Customer (KYC) is a due diligence process that addresses a business’s security concerns regarding customer fraud and crime. These due diligence solutions keep a close eye on an entity as soon as it establishes relationships with a company. Data is gathered on an entity and cross-checked against global databases for records. A risk profile is established, which allows businesses to make informed decisions. From proof of finances to an entity’s ability to comply with rules and regulations, KYC maps all aspects accurately and gives detailed results.
Shufti’s AML Solution Arming Organisations Against Smurfing
Shufti is an IDV service provider that provides businesses with a suite of identity verification (IDV) solutions, aiding robust verification for safe business processes. Our AML solution safeguards businesses from smurfing by providing comprehensive transaction monitoring and analysis. Our robust AML solution helps detect unusual patterns within seconds, identify potential smurfing activities, and enable enterprises to prevent money laundering and financial crime.
Still unsure about protection against money laundering and smurfing attacks?












