Facial Recognition | The Principles of Responsible Use and the Legal Landscape

One of the most popular uses of AI nowadays is facial recognition. In all likelihood, it’s the most divisive. With the advent of ubiquitous computer vision algorithms and smart cameras, facial recognition has become the ultimate double-edged option of artificial intelligence. While it’s every privacy advocate’s worst nightmare, using it on mobile devices would allow for faster, more reliable, and more personalised face verification and customer service. It’s the best resource for tracking criminals and the ultimate control tool for dictatorships.
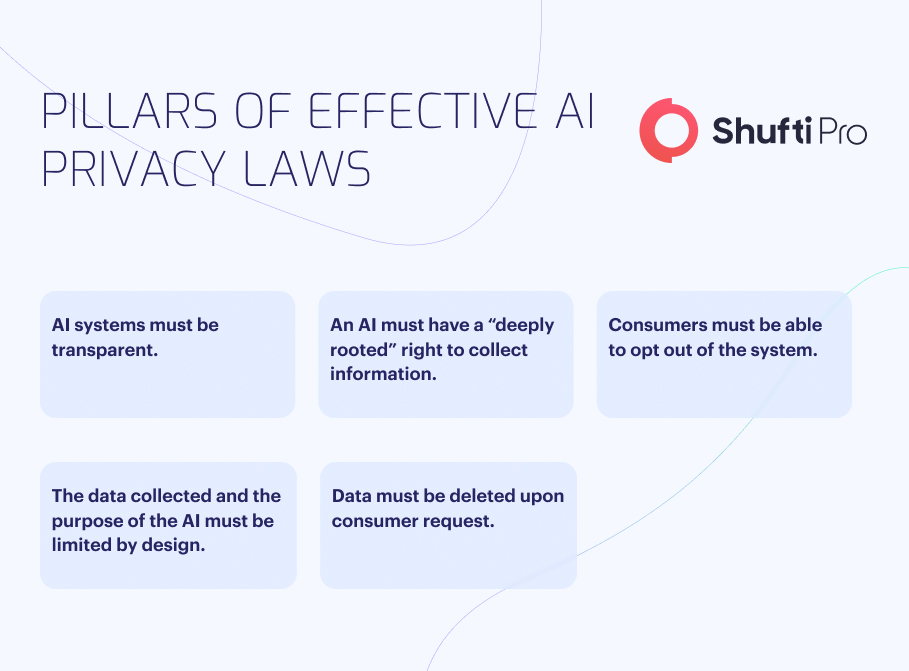
As the use of AI is scrutinised in various countries, there will be requests for more stringent regulation of facial recognition technology (FRT). Some new rules may generally apply to all forms of facial control. Some could be implemented gradually within pre-existing laws and policies concerning law enforcement, healthcare, e-commerce, social media, and autonomous vehicles.
Understanding the Regulatory Landscape
To protect people’s privacy, many proposed laws would allow them to opt out of facial recognition systems. How it is being utilised to target people specifically may now be seen. Allowing individuals to request that their face data be deleted from company files and providing a full accounting of how it is used. Since the General Data Protection Regulation of the European Union and equivalent mandates have been enacted in several jurisdictions, such restrictions may already be in effect there.
Several international regulations have been enacted to restrict and monitor the application of FRT. The private sector is no longer the focal point of new legislation and plans. Whilst some initiatives are solely concerned with policing, others seek to control the public sector. A legislative greenlight is needed to implement FRT in Pittsburgh, Philadelphia, and Virginia in the United States. For example, in the US states of Massachusetts and Utah, authorities must first submit a formal request to the state agency in charge of the database before executing a face recognition search. South Australia also has a law prohibiting some types of surveillance technology (2016). Knowingly installing, maintaining, or using optical surveillance equipment on premises that visually captures or observes private conduct is illegal unless all relevant parties provide their consent, either explicitly or implicitly. The legislation likewise prohibits knowingly using, communicating, or publishing information or material obtained through optical surveillance equipment.
Read More About: Biometric Identification Analysis And Facial Recognition Technology
New Regulatory Structure for Face Recognition Technology
New regulatory structures aimed squarely at face recognition technology are almost inevitably being implemented in light of the complicated challenges this technology raises and its reliance on AI. It is expected that the following new regulatory frameworks will be implemented during the next several years:
Prior Consent
More and more countries are passing legislation requiring businesses to get people’s permission before collecting photographs for facial recognition and this trend is expected to spread to relationship-focused industries like e-commerce, smartphone apps, and social networking. The rules will specify the circumstances under which consent is necessary and the methods, forms, and sharing channels through which customers must express support (decline, modify, or withdraw).
Visible Notifications
Public and commercial establishments must disclose the use of AI face recognition technology with clear signage and, in some cases, push notifications to mobile devices nearby. More individuals will provide agreement to facial recognition — or withdraw it — just by entering a venue equipped with the necessary signage rather than going through the time-consuming process of acquiring previous approval through online forms. There must be clear on-screen notifications in web and mobile apps when face recognition is used, especially for more covert online face recognition methods like browser-based machine learning technology.
Ad Hor Opt-Outs
Countries concerned with citizens’ right to privacy may pass laws to shield those who opt out of routine facial recognition systems. To avoid identification by algorithms in real-time, some persons may choose to use adversarial masking strategies such as covering faces, wearing glasses, changing skin tone, or other similar measures. In some jurisdictions, the law may hold that persons may engage in selective post-hoc masking of images stored in non-sensitive public and commercial databases. This is an emotionally charged issue since several countries have banned face masks and other cloaking technology for fear that terrorists and other criminals could use them to avoid being identified.
Subject Sovereignty
In response to the GDPR and similar mandates, many jurisdictions will enact regulations to protect the privacy of individuals who are the subjects of facial recognition by providing them with the information they need to make informed decisions about the collection, storage, and use of their likeness. If a facial recognition system mistakes a person or if they believe an accurate facial recognition is being utilised for an illegal or inappropriate purpose, the legislation in many countries will be tightened to allow for an appeal. Similarly crucial is the likelihood of legislation establishing when and under what conditions facial recognition evidence is inadmissible in criminal and civil trials.
Debiasing Requirements
Given the widespread fear of discrimination based on race, sexual orientation, and other protected characteristics, many jurisdictions will require businesses to demonstrate that algorithms have been debiased to these factors regularly. Facial recognition algorithms must be retrained and recertified periodically to ensure that the rates of false positives and negatives remain stable across all these characteristics. There will also be regulations to prevent innocent people from being wrongly labelled as criminals, animals, or anything else that could hurt their reputation.
Embedded Technological Safeguards
It may one day be possible to programmatically or automatically turn off facial recognition algorithms in AI accelerator chipsets based on various temporal, geospatial, and other environmental factors. Alternately, these protections could eventually be included in picture-capturing systems at the chip level. As these technology possibilities develop, authorities will demand incorporation into commercially available computer vision systems and other facial recognition devices.
FRT’s Privacy and Security Risks
The growth and application of FRT in recent years has been meteoric. FRT is becoming increasingly popular as businesses use it for various purposes, such as authenticating users for access to restricted resources, processing payments, keeping tabs on employees, narrowing in on potential customers, etc. From a projected US$5.01 billion in 2021, the face recognition technology market is expected to grow to US$12.67 billion by 2028. Government and law enforcement organisations’ increasing need for technology to help in criminal investigations, surveillance, and other security-related purposes is also a driving factor.
However, there are possible drawbacks to employing FRT, such as the numerous privacy and security concerns, as there are with any technology.
- Lack of consent— By the requirements of applicable data privacy regulations, businesses must obtain their customers’ explicit permission before collecting biometric information. FRT’s most severe privacy risk arises when it tracks and identifies people without their knowledge or permission. Real-time public surveillance and the illegal compilation of databases fall within this category.
- Unencrypted faces— The cost of capturing and storing facial images decreases as technology improves. Faces are unencryptable, unlike many other types of data. Because of the immutability of a person’s appearance, data breaches involving facial recognition data enhance the risk of identity theft, stalking, and harassment.
- Lack of transparency— Since each person’s biometrics are distinct, using FRT to identify people without their knowledge or consent presents privacy problems. Unlike other biometrics (such as fingerprints), facial scans can be recorded simply, remotely, and discreetly, raising additional security problems.
- Technological holes — Spoofing a system (or pretending to be a victim) may be possible with FRT by employing photos or 3D masks made from victim-specific data. FRT is also vulnerable to presentation attacks and other forms of spoofing, such as masks and deepfakes, which can be used in the physical and digital realms.
- Inaccuracy— Another major argument against FRT is that it is inaccurate. If a captured facial scan incorrectly identifies an individual, it might have serious long-term ramifications. Accuracy also varies by ethnicity, with women and persons of colour being more likely to experience false positives, which can lead to wrongful arrests.
How Might Technology Step in and Help?
According to a study, the average cost of a data breach was estimated to be $3.86 million in 2018. The price of a privacy blunder is minimal for significant corporations with annual revenues between $100 million and $25 billion. However, stock prices might drop, and customer trust can be lost if corporations experience privacy breaches. It’s safe to suppose that, at some point, these issues will grow severe enough to have a noticeable effect on the company’s bottom line.
How could modern technology be of assistance? Differential privacy and homomorphic encryption are two examples of cutting-edge technologies that point to promising new directions. Homomorphic encryption provides an extra layer of protection by enabling facial recognition machine learning algorithms to work on data without decrypting it, and differential privacy systems infuse unpredictability into user data to thwart de-anonymisation strategies. Tests of these and similar approaches are only getting started.
The AI Now Institute, a prominent New York-based research organisation, has released a report highlighting facial recognition as a primary concern for society and governments. The rapid advancement of a subfield of machine learning known as deep learning is mainly responsible for the meteoric rise of facial recognition. To find patterns in data, deep learning employs complex networks of calculations that approximately mimic the neural circuitry of the human brain. It has improved to the point that it can perform pattern recognition with mind-blowing precision.
To Sum Up
The worldwide spread of FRT is now a significant discussion topic. While FRT holds great promise, it also raises serious privacy problems. The future of regulation in this burgeoning field appears to be focused on putting in place sufficient protections to avoid abuse of FRT and protect privacy, but this is still to be determined. Even if FRT is not employed, knowing the difference between a real and fake face is essential for security and privacy in a world where faces are used to establish identity in-person or via video conference.
However, Shufti provides advanced facial recognition technology that may be used in various settings. Our authentication system uses AI-powered algorithms to quickly and accurately verify user identities, reducing the likelihood of fraud and other criminal activity. Additionally, it helps businesses in meeting international standards and avoids hefty fines. Our face recognition technology is used by various industries throughout 230+ nations and territories, from the hospitality industry to the in-home care industry.
Shufti has compliance officers and other industry specialists strategically located worldwide. This global reach offers specialised services for companies in all areas. To help businesses succeed in international markets while protecting customers’ personal information and adhering to all applicable laws, we employ local experts to ensure our identity verification and facial recognition solutions comply with each country’s specific requirements.
Want to know more about facial recognition principles and the legal landscape?












