Rising Social Media Scams in 2020 Calling for Digital Identity Verification

Social media was a simple place for interaction a few years back. People valued it for its security and anonymity, but unfortunately, 2020 faced the opposite side of what was expected from it. Social media is not just a place to keep children busy with cartoon videos now.
Social media is a big industry that provides a smooth networking space for everyone. On the other hand, it is also unknowingly facilitating the proliferation of spams and trolls. Harassment cases and scams are significantly increasing. But why are scams on social networking platforms drastically increasing? A freehand and lack of a robust verification system is the main reason. Everybody can join these platforms with fake social media identities.
According to 2020 statistics, there are 3.5 billion social media users and a significant number of profiles are created with fake names and documents. These accounts threaten other users with hacking, social media identity theft, and other cybersecurity issues. Spammers have thousands of fake profiles that become an obstacle for legitimate users to interact and expand networks. Furthermore, fake posts and junk advertisements do nothing more than diverting attention and manipulating the thoughts of innocent users.
Professional networking sites like LinkedIn are also not secure since fraudsters post fake job ads to attract desperate job seekers. The increasing scams on social media have led to plenty of government regulations for the security of the users and their identities. However, the authorities cannot blame someone without getting their social media identities verified in the first place.
Some Facts and Figures
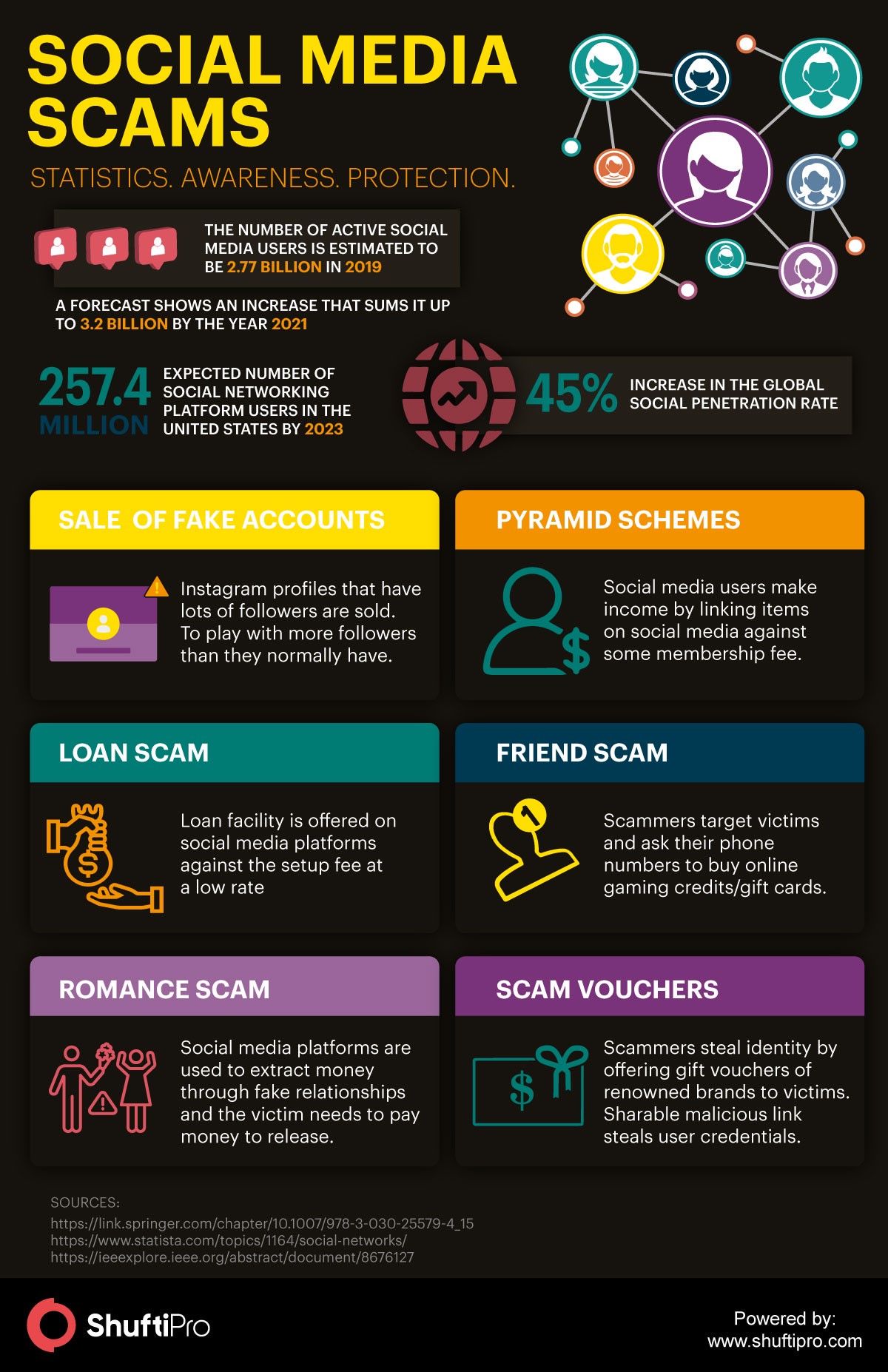
This section gives an overview of social media usage and its penetration at a global level. In recent years, social networking applications have shown a clear shift towards handy devices such as mobile phones and tablets. Easy access to these platforms, therefore, have increased the usage via mobile devices. Social media is one of the most defining phenomena of the present environment that is reshaping the entire world. Statista shows that the global social penetration rate has reached about 45%. Among these, North America and East Asia have the highest penetration rate i.e. 70% and Northern Europe with 67%. Also, in the future, this percentage does not seem to go down anyhow because the survey shows that the number of expected social networking platform users in the United States would be 257.4 million by 2023.
According to a research paper by IEEE published in 2019 named “Cyber Security in Social Media: Challenges and the Way Forward”, the number of active social media users in 2019 is estimated to be 2.77 billion and a forecast shows an increase that sums it up to 3.2 billion by the year 2021. The same paper highlights the threats in social media platforms that correspond to the impersonation of friends and celebrities, cyberbullying, and phishing scams. This increasing trend and penetration of the population into it shows a tremendous increase in social platforms’ security flaws. Lax rules of these platforms are inviting fraudsters to poison the cybersecurity triad i.e. confidentiality, integrity, and availability. Lack of security measures gives birth to attacks such as CSRF or XSS that lead to data breaches.
Know more about Identity verification
Frauds in the Social Media World
The section covers some major frauds in the social media world that every user must beware of. Social media has penetrated every corner of the world, and it is now a fundamental source of communication. Here are some of the common frauds on social media platforms.
Hidden URLs
Short URLs may not be suspicious for anyone, but they are now a threat to social media users. Beware of URLs that have hidden locations. They are common on twitter and LinkedIn, and they can innocently redirect you to the relevant web page. However, other social media platforms may not always look out for such issues. Fraudsters can post a trending news headline and redirect you to a scam page. Acquiring your social media identity and other personal information will not be a problem.
Phishing Attacks
Phishing attacks are a new form of social media identity theft. These attacks were common in emails, but advancements in technology has allowed scammers to perform phishing attacks on social media as well. “Someone just uploaded weird photos of you from the party last night.” What will you do now? As a reflex, you will immediately click on the link, and it will redirect you to some other platform. It can be a twitter page that will ask for credentials. As soon as you enter your account details, the spammer can use your social media identity and other personal information for fraud.
Catfishing
Catfishing is a kind of online harassment where spammers search for people desperately looking for their special one on social networking sites. Spammers create fake accounts with an eye-catching picture and false social media identity to begin a relationship. They earn the trust of the other person and ask for money after some time.
“Who Visited Your Profile” Scam
It is always good to know who visited your profile. Someone might call you for a job or just become good virtual friends in a while. Fraudsters take complete advantage of this curiosity and create ads, for example, ‘click on this link to find out who viewed your profile today’ or ‘visit this link to know your secret admirers.’ As soon as you click the link, you are redirected to a new page that asks for your personal information or credentials of the platform. Stealing your identity is not a problem then.
Know about the top five key identity verification market trends here.
Digital Identity Verification: An Effective Measure for Social Media Security
Individuals alone cannot always figure out these scams, however, social media platforms can restrict fraudsters from creating fake accounts for harassment and illegal use. Social media platforms that assume personal identification an overkill for social users would now be realizing that how many spammers are facilitated through these platforms, and how they are disrupting the integrity and privacy of online users. Again, spammers are not only posting junk information but exploit weaknesses of the system to damage in the best possible way among which phishing attacks and malware/malicious executables injection is the one.
Lack of social media identity verification service on age-restricted websites affects both the social media platforms and their users. Online users below an adult age are not verified and use the applications without any restriction. Or some websites do apply age affirmation pages or checkboxes for age verification that actually does not serve the purpose of age verification and can easily be deceived by minors.
Online Age Verification
In the past few years, age verification has become a regulatory requirement that is necessary for social media platforms to consider. Taking advantage of technological advancements, social media firms can take in place various solutions that could help in identifying the individuals and restrict services if they are not for children.
Current verification methods can easily be falsified which require obvious changes in digital practices of verification. Many social networking platforms are now using age verification services that verify using document verification if the online user has misstated their age. Those social media identities would immediately be flagged with the status of unverified as they do not lie under the age limit that could access the networking platform.
Ideally, social media platforms are required to collect minimized data from customers. For instance, if they want to make sure whether someone is above 18 years, then the individual would have to share a proof of their social media identity in the form of an official ID document, etc. The company should ensure that the individual is above the defined age and avoid collecting much of the information from the user’s uploaded document.
Know more about age verification at Age Verification – Does Your Business Need It?
Video KYC
Technological advancements have made everybody’s life convenient, including fraudsters. Dodging verification checks may not be a challenge anymore. Moreover, the young ones can provide wrong information to skip age verification. Video KYC allows socializing sites to verify all the clients on a live video call. Verifying social media identities through video-based KYC can enhance the result of social media verification service.
Digital Social Media Identity Verification
In social media platforms, it is quite easy to create a fake account/profile to impersonate a social media identity online. Whether it is Facebook, Twitter, Linkedin or some dating sites, fraudsters find all of these a hot target and conduct malevolent activities there. With single digital identity verification, misuse of social platforms can be crushed.
Focusing on just collecting data whether it is true or false should not be the goal of social networking platforms. Allowing legitimate traffic can help provide better search results. Stuffing fake social media identities affect the huge population and hence the platform reputation. Using artificial intelligence and machine learning algorithms as the underlying technology, facial recognition systems, and online document verification for social media verification service can help maintain an honest community with much more healthy working and networking opportunities.
What’s the big deal, if a social media identity can be verified within seconds? But it would really be one if your platform is in the spotlight due to data breach that compromises the security of millions…
Have questions about how Shufti can help you secure your social media platform?












