Top 10 Biometric Technology Trends to Watch For in 2022

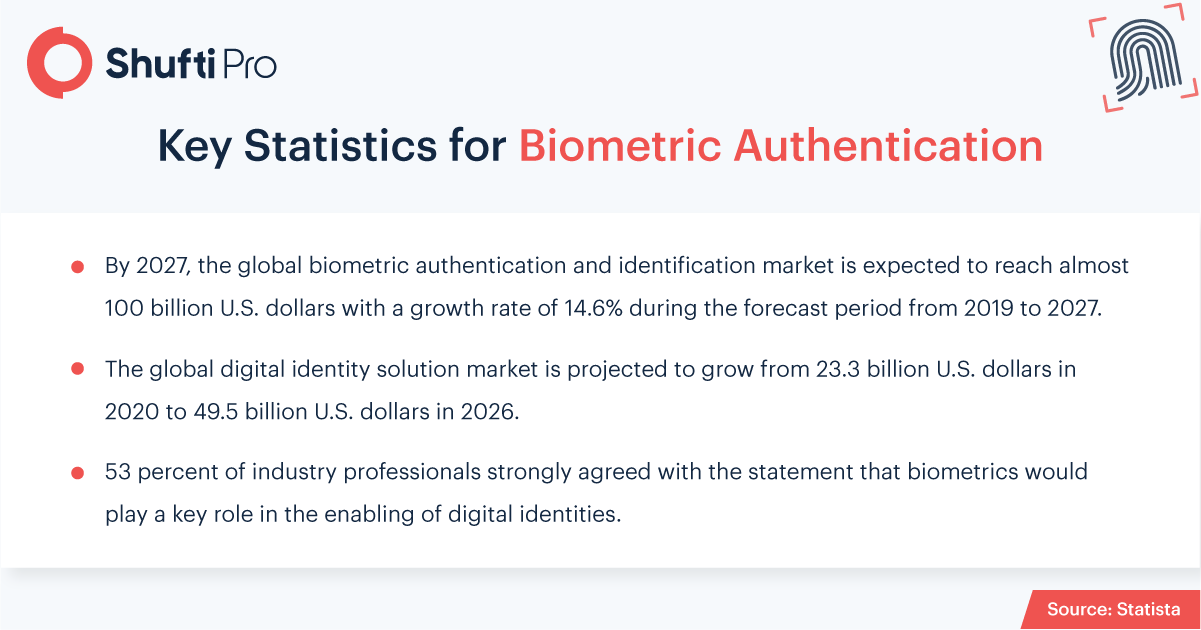
Biometric innovations in present times have manifested various technological advancements and their effects are all set to influence businesses’ everyday tasks. Keeping tabs on changing technological trends every year is essential for businesses. The future of biometric technology in terms of application is immeasurable and set’s one side on enhanced security and data protection.
Regulatory changes make it equally essential to move towards advanced technologies that assist businesses in streamlining their workflow. Fingerprints, voice recognition, and facial recognition have widened the paths towards secured connections and privacy at a personal level. Biometric innovative solutions make it easier to tackle money laundering, tax evasion, and combating fraudulent activities.
Coronavirus Pandemic Skyrocketing Biometric Adoption
Considering the challenges that businesses face as they attempt to safely reinstate their services after the Covid pandemic, biometric technology is proving to be the most convenient security solution. Due to the severity of the virus, governments all around the globe imposed lockdowns and legislated numerous other standards for individuals and businesses. However, due to newly introduced norms, business operations were adversely affected, especially those that lacked the facilities or resources to get digitized.
Identifying, managing, and deploying all of the technology required to accomplish digitization may appear daunting to businesses. However, companies can now use biometric technology systems to move things forward safely.
Top 10 Trends for Digital Identity and Biometrics
Here are the top 10 trends of biometric technology businesses need to watch for in 2022:
1. Cyberattacks Adapt to the Age of AI
Cybercriminals have become more refined, both in terms of identifying target systems and tech-driven tools they employ as Machine Learning (ML) and Artificial Intelligence (AI) capabilities become more common in our daily lives. As artificial intelligence is refining criminals’ techniques, they’re now ruthlessly and consistently attacking systems every day, focusing on the weak areas. An example of an AI-based cyber-attack is deepfake that is used to exploit the identification systems by impersonating victims’ facial traits. Therefore, the rate at which these complicated threats are evolving will accelerate in 2022.
2. Identity Verification Systems Continue to Make Sharing Economy Trustworthy
Sharing economy platforms like Uber, Airbnb, and various other companies are used to connect individuals through P2P services and are looking for innovative ways to prove their credibility. In 2022, people can hope to see wider use of ID verification with an unshareable credential in this sector, allowing companies to provide services that can make them trustworthy along with improving the customer experience.
3. The Unshareable Credential Will Grow in Importance
Limiting authentication to a certain person is a crucial challenge in various businesses, ranging from financial institutions to education centers and the sharing economy. Considering ride-sharing companies, it is hard to verify the legitimacy of drivers as well as the customers. That being said, it’s quite challenging for companies to keep check and balance of the driver to know whether registered entities are performing a duty or not. As credentials and gadgets can be freely exchanged or forcibly taken, biometric authentication will take the lead in this field.
4. European Regulation to Spark Innovation
It is expected that the standard of Electronic IDentification Authentication and Trust Services (eIDAS) in the UK will evolve in 2022. This is an automated framework that permits companies to authenticate customers’ identities and government-issued documents. eIDAS will create more inclusion by allowing people to engage online, minimizing the environmental impact of travel, enhancing efficiency, and promoting a cost-effective option to support international trade for economic growth.
Businesses, as well as individuals, may anticipate a major effort in Europe in 2022 to ensure confidence and authenticate the legitimacy of electronic transactions and secure access to services. SaaS providers will come up with innovations as Europe embraces new ideas like citizen wallets and verifiable credentials to make compliance with new standards easier and to speed up the delivery of digital trust.
5. Staffless Stores
The concept of staffless stores emerged right after the coronavirus pandemic disrupted the world’s order. In these stores, the customers are required to download the mobile application that needs to be scanned before entering the store. Apart from this, AI-backed facial biometric recognition devices are also implanted that verify clients.
A set of digital cameras have also been installed that track the consumers in the shop and record every bit of clients’ activities including the items they place in bags. Many pilot staffless stores are inaugurated but are still in the testing phase. However, the year 2022 will be the year when such stores will become common.
6. Travel Industry Adopting NFC-Powered Solutions
Contactless solutions are being used by transit networks all over the world to create a safer travel environment for passengers on buses, trains, and airports. Due to COVID-19, public transportation and activities have become a potential risk for individuals, while service providers are well-aware that they must face new hurdles in order to maintain and create confidence, as well as grow ridership.
Biometric technology solutions are being used by businesses to create a safer travel environment, from mask compliance to disinfection efforts. In addition to this, NFC-based payments will also allow customers to simply tap their chip-based identity card on the NFC-based device placed at the terminal.
7. Continuous Biometric Authentication will Continue to Gain Traction
This provides authentication in real-time and deters the risk of criminal activities like hacking or database breaches. As the concept of zero-trust is becoming a standard in the cyber security sector, many technology analysts forecast that biometric technology will be frequently incorporated in the continuous authentication process. Having high-security options, both businesses and individuals prefer biometric verification solutions rather than relying on conventional passwords.
For instance, in today’s tech-driven cars doors are automatically local and the car will not start if individuals walk away from the specific car with the key in their pocket. However, once the user returns, the car will unlock. Yet this innovation holds loopholes that can easily be manipulated. However, Incorporating biometric technology such as facial recognition can be placed into the key to make it secure.
8. Behavioral Biometrics
This type of biometrics includes human behavior like voice recognition, keystroke dynamic, and facial analysis. However, this biometric technology field is still in the development phase. This necessitates the use of other biometric modalities for authentications and is credibly is much greater than other forms.
9. Cloud-Based Biometrics
The development of cloud technology is parallel to the evolution of biometric identification. Cloud-based biometric solutions aim to embed several segments into systems that can satisfy the customers’ requirements, not only restricted to security concerns. Thereby, by combining cloud services with biometric technology, SaaS will come up with multi-factor authentication solutions that will effectively prevent identity thefts and data breaches in the coming years.
10. Multimodal Authentication
With time, biometric solutions are becoming more sophisticated as advanced technologies are emerging. Multimodal biometric verification can provide an extra layer of security to digital businesses. However, with the rise in spoof attacks, biometric-enabled anti-spoofing technologies are developed that are quite beneficial to identify fraudulent activities.
Final Thoughts
Biometric technology is significantly taking over the conventional means of identity verification that were full of shortcomings, highly vulnerable to cyberattacks. Biometrics offers an ideal balance of security as well as convenience.
Shufti’s robust facial biometric recognition services are powered with thousands of AI models to verify customers’ real identities and validate the live presence of the customer. With 98.67% accuracy, Shufti’s identity verification solutions ensure that the companies stay safe from facial spoof attacks.
Want to learn more about facial biometric recognition solution?












