Top Applications of Facial Recognition Technology in the Digital Age

Facial recognition technology is biometric security in which an individual’s physical traits are their unique “password” or identifier. This technology has gained widespread popularity among consumers over the years, with various popular smartphone manufacturers offering it as a screen unlocking option. Despite its ongoing development and ethical concerns, governments and industries have already begun using facial recognition technology for various purposes.
How Does Facial Recognition Technology Work?
Facial recognition technology recognises one person as the legitimate device owner whilst restricting access to others.
Here’s how facial verification technology works:
- Face Detection: The camera locates and detects a face image, whether it’s an individual alone or amidst a crowd, facing forward or in profile.
- Face Analysis: Following that, the captured face image undergoes analysis. Most facial recognition systems rely on 2D images as they can conveniently match them with public or database photos. The technology reads facial geometry, considering eye distance, eye socket depth, forehead-to-chin distance, cheekbone shape, and lip, ear, and chin contours. The goal is to identify critical facial landmarks crucial for distinguishing a person’s face.
- Converting the Image to Data: During the face capture, facial information becomes digital data based on the individual’s facial features. This analysis is translated into a mathematical formula known as a faceprint. Similar to unique thumbprints, each person possesses their distinctive faceprint.
- Finding a Match: The individual’s faceprint is compared with a database of known faces. For instance, the FBI accesses up to 650 million photos from various state databases. Additionally, Facebook’s database includes pictures tagged with people’s names, which can also be used for facial recognition. If the faceprint matches an image in the facial recognition database, a judgement is made.
Applications of Facial Recognition Technology
The face verification technology finds its applications in various areas which are as under:

1. Citizen Services
Citizen services are leveraging Facial Recognition Technology (FRT) in this age of digitisation. From security concerns to convenience, FRT recognises individual characteristics and conditions and offers appropriate services. This will necessitate substantial edge infrastructure, analytics, and the establishment of new privacy regulations.
2. Financial Services
Face verification technology will disrupt the payment landscape of the financial services sector. Major banks are expected to adopt this technology for ATM withdrawals within five to ten years.
3. Livestock Farming
Facial recognition revolutionises livestock farming, particularly in challenging sectors like dairy farming with complex and harsh conditions. Farmers will no longer be confined to relying solely on their observations and inherited knowledge. Whilst implementing FRT in this context is no easy feat, it can potentially drive significant changes in an industry that has remained unchanged for millennia.
4. Retail Recommendations/Purchases
Retail is considering adopting facial recognition technology to provide personalised recommendations and create a seamless online/offline shopping experience. Sometimes, a shopper checks for skinny jeans in a brick-and-mortar store but doesn’t purchase them. The store will later target them online with personalised ads and recommendations for similar products based on their interests displayed in-store.
5. Managing Office Spaces
Modern smart buildings are likely to embrace facial recognition extensively. Office space managers promote mobile applications for space reservation, but soon conference rooms may recognise individuals’ faces and adapt to their preferences. This includes adjusting temperature and lighting and even ordering their preferred mineral water.
6. Multifactor Authentication
Facial recognition technology integrated into a multifactor authentication process has the potential to enhance various interactions, like purchases and building access, offering significant value to the public. These benefits can help foster public acceptance of the technology, which might otherwise be viewed with concerns about intrusive surveillance or “Big Brother” implications by law enforcement.
7. In-Home Care
In-home delivery services and home health care providers use AI facial recognition technology. It allows individuals with physical challenges to receive visitors and assistance without the need to answer the door physically. By verifying the identity of expected delivery personnel or medical professionals, facial recognition grants them entry into the home.
8. Campus Safety
Facial recognition technology is witnessing widespread implementation in educational institutions to enhance campus safety. It will play a key role in authorising entry for students, teachers, and faculty, improving tracking capabilities and overall security of facilities and campuses.
9. Age-Gating Online Content
Current age-gating measures for online content prove largely ineffective. New regulations like California’s AB 2273 aim to address this issue. However, compliance with such regulations may require companies with age-inappropriate scope to implement tools like face-based age-estimation solutions, which visitors must use to access the content on their websites. Such laws raise potential privacy concerns among users.
10. International Travel
Facial recognition is becoming a standard feature at airports and border checkpoints worldwide. With an increasing number of passengers carrying biometric passports, they can bypass long lines and utilise automated ePassport control at the gate. Airports can leverage facial recognition technology to expedite check-in procedures and enhance security.
11. Hospitality Services
In the hospitality industry, particularly hotels, FRT is used to recognise guests, retrieve their reservations, facilitate check-in, understand their preferences, and provide personalised services. Hotel staff will efficiently add charges for services availed during the stay to the guest’s bill, enhancing the overall guest experience.
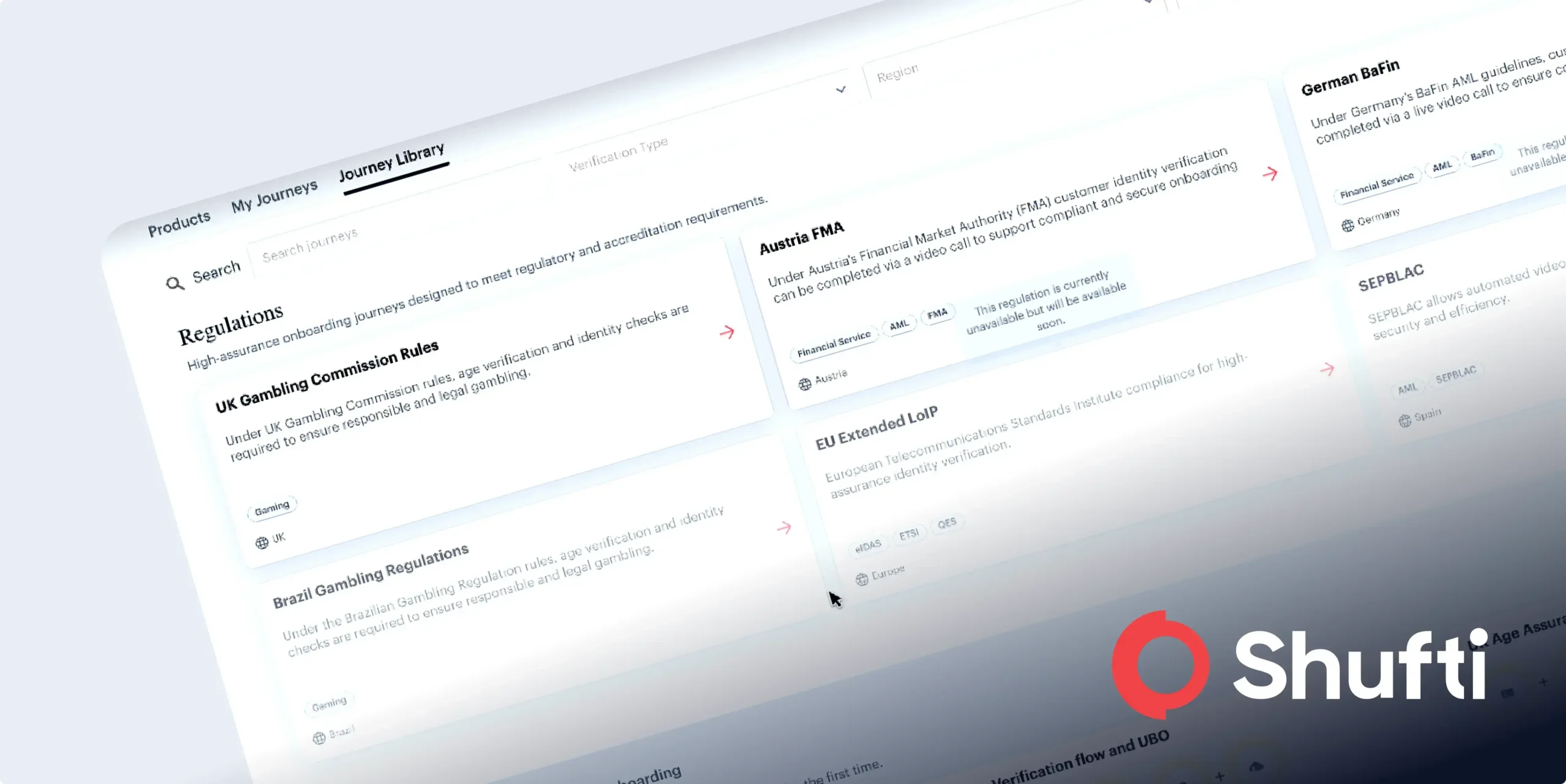
How Can Shufti Help?
Shufti offers robust face recognition technology helping businesses in different areas. Our verification technology uses artificial intelligence algorithms to authenticate individuals within seconds, mitigating the risk of fraud and other crimes. Not only this, but it helps businesses comply with global regulations and avoid heavy fines. From hospitality services to in-home care service providers, our face recognition technology serves every sector in 230+ countries and territories.
Still confused about how facial recognition technology is helping in different areas?

 Explore Now
Explore Now