10 Ways to Eliminate Business Fraud with Robotic Process Automation (RPA)

- 01 Revamp Current Processes
- 02 Expedite Fraud Investigations
- 03 Minimize Human Interactions
- 04 Look-out For Anomalies
- 05 Update Watch Lists
- 06 Implement Compliance
- 07 Automate Report Generation
- 08 Review High-Risk Accounts
- 09 Automate Temporary Block and Removal
- 10 Integrate with Machine Learning
- 11 Is RPA the Best Solution For Fraud Detection?
One of the prime concerns of businesses today is detecting and mitigating the risk of fraud. This is because the consequences of fraud can be considerably detrimental, from financial repercussions to legal penalties. Companies are seeking Robotic Process Automation (RPA) technology to completely eliminate this threat from occurring in the first place.
With the help of RPA technology, businesses can weed out identity and financial frauds in a number of ways. Here’s how your company can enhance legacy fraud prevention mechanisms with the help of RPA.
What is Robotic Process Automation?
Robotic Process Automation is an automated technology that has the ability to record tasks performed by humans on computers, and then perform the same task without human intervention. In simple terms, it is a virtual robot that automates repetitive human actions. Common business processes performed by RPA technology include website scraping, payroll processing, and order processing.
Revamp Current Processes
To implement RPA, companies are required to reevaluate the current processes that are associated with a high financial risk. For instance, financial transactions that are indicative of fraudulent behaviour are thoroughly analysed on a timely basis. This evaluation helps in revamping the current processes through RPA technology, enabling the company to better detect and monitor vulnerabilities within the business processes.
Expedite Fraud Investigations
To begin a fraud investigation, a large sum of relevant data is required. The longer it takes to resolve an investigation, the more challenging it becomes to recover the funds. Since RPA technology works well with structured data, it speeds up fraud investigations by efficiently pulling out necessary data when needed. As a result, investigators are able to focus on the qualitative aspects of the case, while RPA-based technologies focus on providing required quantitative data.
Suggested Read: The Power of Robotic Process Automation in the Banking Industry
Minimize Human Interactions
It is a common notion that “fraud is a crime of opportunity”. For that opportunity to arise, human interaction with the data is required. In a traditional business setting, employees are constantly dealing with financial data, providing them with an opportunity to manipulate it for illegal gains. With RPA implementation, the processes become automated, thus substantially diminishing human interaction. Another added bonus of Robotic Process Automation is automated document extraction. However, by combining it with the powers of AI, Optical Character Recognition (OCR) technology can be utilized to obtain highly accurate results.
Download Report: Fully Embracing Digital Transformation with Automated AI OCR Engine
Look-out For Anomalies
Banks and other financial institutions deal with hundreds of financial transactions on a daily basis. This makes it challenging for the employees to keep an eye out for irregularities and fraudulent behaviours. However, RPA has the ability to process high-volume transactions within seconds. By pairing up this technology with Artificial Intelligence and Machine Learning, the monitoring process can be further enhanced. Payrolls and accounts receivables/payables are examples of processes where RPA implementation can be used as a fraud prevention tool.
Update Watch Lists
Financial institutions have the crucial task of maintaining a clean customer base. This step is essential to prevent fraudulent activities such as money laundering and terrorist financing. For this purpose, every customer that is onboarded is scanned against criminal watch lists, Politically Exposed Person (PEP) lists, global sanctions and other lists that have been compiled by global regulatory bodies. With RPA technology, these lists can be automatically updated, making the obligatory AML (Anti-Money Laundering) screening process more streamlined and effective.
Implement Compliance
RPA technology has proven itself to be useful for staying compliant with Know Your Customer (KYC) and Anti-Money Laundering (AML) regulations. These regulations require businesses to collect each customer’s Personally Identifiable Information (PII) for the purpose of identity verification. RPA-based solutions keep a record of all the data actions taken by the employees and customers, leading to a complete audit trail. This makes it easy for the business to extract data when required for KYC or AML verification.
Suggested Read: The Changing Landscape of KYC/AML Regulations in 2021
Automate Report Generation
In a traditional setup, compliance officers and their dedicated teams manually file a Suspicious Transactions Report (SAR) in the case a fraudulent transaction has been detected within a business. This step is unavoidable, as it has been mandated under global AML regulations. RPA solutions based on AI technology eliminate the need for manual processes by generating reports in real-time within a few seconds. This allows a company to save its resources, in terms of both time and money.
Suggested Read: Winter is Coming: With a Storm of KYC and AML Regulations
Review High-Risk Accounts
RPA implementation also provides benefits in the high-risk transaction review process. How? By automatically pulling in additional information about the customer, such as their transaction history and prior business activity details. Using RPA, these details can also be sent to company stakeholders through RPA-generated communication templates. This enables businesses to swiftly review and create communication with the necessary parties, expediting the action-plan for catching the culprits.
Automate Temporary Block and Removal
Have you ever been in a situation where your credit card got stuck in an ATM over an “unusual behaviour” claim? That process is driven by RPA technology. An RPA-based access control system has the ability to block accounts that are indicative of suspicious behaviours while simultaneously informing the end-users. Often, companies combine RPA and Artificial Intelligence capabilities to deal with compromised accounts that may pose a high-risk of financial crimes.
Another feature of RPA in this regard is that it also has the ability to detect temporarily blocked accounts, access the transactions they performed, and then remove the restrictions based on a pre-defined criterion set by the company.
Suggested Read: Artificial Intelligence – What is it and Why it Matters
Integrate with Machine Learning
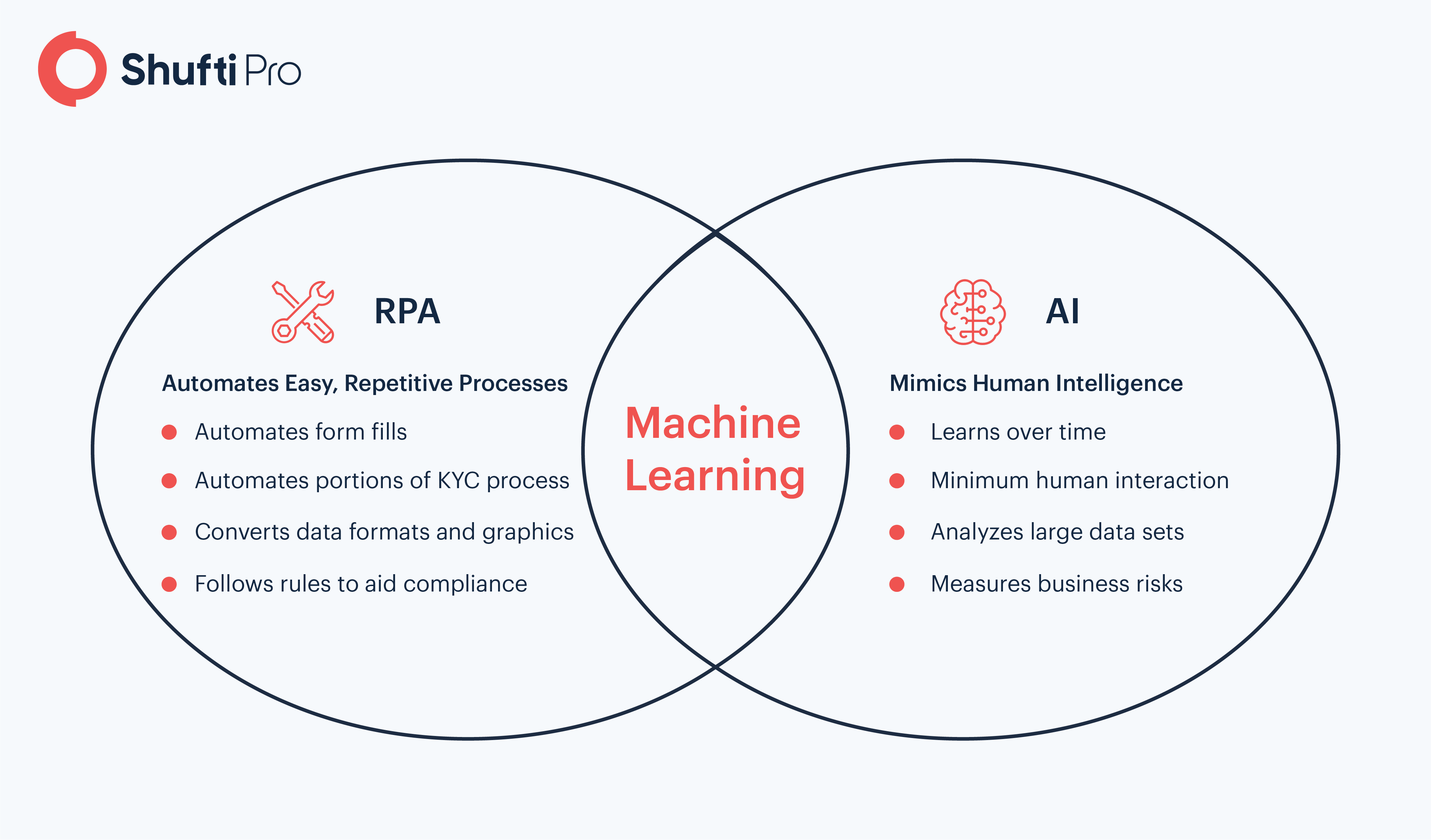
The best fraud prevention method relies on the use of the latest technologies available in the market, and understandably so. By integrating the capabilities of Robotic Process Automation with Machine Learning, its cognitive capabilities can be enhanced. This allows a company to smartly decipher and report financial anomalies by filtering out fraudulent transactions from large datasets. If the RPA, ML, and AI technologies are combined, a self-learning model is created for the analyses of newer fraud patterns. Thus, such a solution can provide decline reasons for rejected transactions and verification results, while simultaneously maintaining audit logs for compliance reasons.
Is RPA the Best Solution For Fraud Detection?
Amongst the countless fraud prevention technologies available today, Robotic Process Automation definitely stands ahead of the game. However, whether this is the perfect solution for mitigating fraud risk in your company, depends on the needs of your business. If your business operations merely require fraud prevention through automation, then RPA technology is your go-to option. On the other hand, if your business wishes to stay compliant, mitigate the risk of fraud, and screen identities of customers through a single solution, then an AI-based identity verification (IDV) solution is exactly what you are looking for. These solutions combine the power of AI, automation, and ML to provide businesses with the ultimate fraud detection and prevention suite.
Suggested Read: Top 10 Real-World Scenarios Where Shufti’s IDV Can Help
Want to learn more? Try out our 7-day free trial or talk to our experts!












