All You Need to Know About Facial Recognition

Rapid digitisation over the past few years has led to the adoption of facial recognition for many purposes. Be it an attendance marking system at the office or fighting fraud, face recognition online comes in handy. Today, thousands of Artificial Intelligence models are deployed that make face recognition an effective measure for fighting fraud. According to Mordor Intelligence, the global facial recognition market was valued at USD 8.58 billion in 2025 and is projected to reach USD 20.88 billion by 2031. Nowadays, this technology is being widely used in identity verification systems.
What is Facial Recognition?
Facial recognition is an AI-powered technology that authenticates the face of the end-users against the image on any government-issued ID documents. It makes identity verification easier and the chances of spoof attacks, deep fakes, 2D and 3D face masks, and replay attacks are significantly reduced during customer onboarding.
At its core, the system maps the geometry of a face (such as the distance between eyes, the shape of the jawline, the depth of the nose) and generates a mathematical signature that can be compared against a stored reference. Modern systems use convolutional neural networks trained on millions of face images to achieve this at speeds and accuracy levels which can’t be achieved by manual comparisons. The FBI’s IC3 recorded AI-enabled fraud totalling $893 million in 22,364 complaints in 2025 (this is the first time IC3 dedicated a section to AI-driven crime) this clearly signals that passive document checks are no more sufficent.
How Does Facial Recognition Work?
Facial recognition deploys various Artificial Intelligence algorithms to enhance the efficiency of the process. Within a few seconds, Shufti performs facial recognition checks and helps businesses deter frauds.
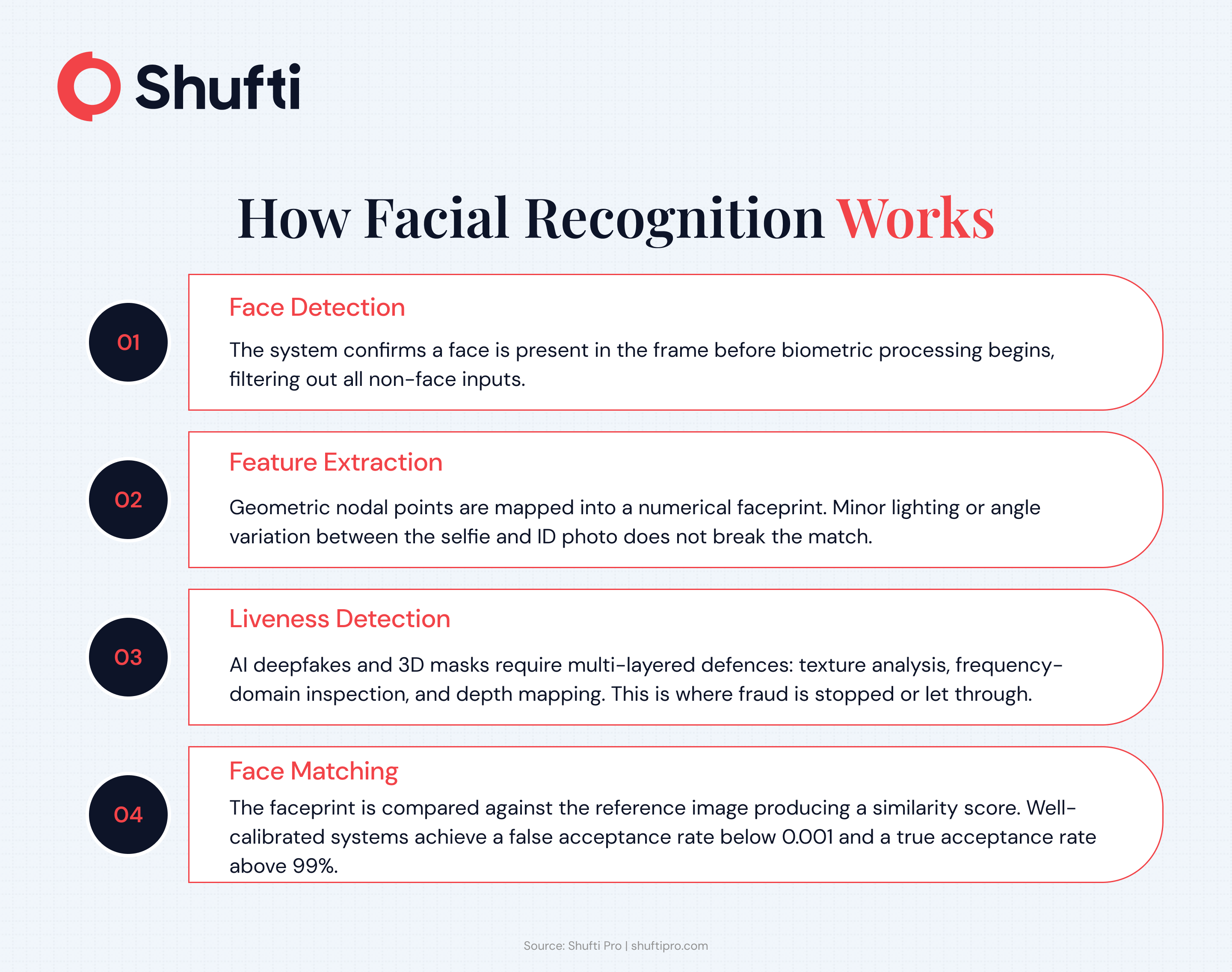
The process runs through four stages on every submission:
Face Detection. The system identifies the face region in the image or video frame using a detection model. Poor lighting, angled shots, or obstructions are normalised at this step.
Facial Landmark Mapping. Key anchor points eyes, nose tip, mouth corners, jawline are located and used to align and normalise the face regardless of tilt or rotation.
Feature Extraction. A deep learning model converts the aligned face into a numerical vector a unique facial signature specific to that individual.
Matching and Decision. The extracted vector is compared against a reference image (typically the photo on a submitted ID document). If the similarity score exceeds the defined threshold, the check passes. Liveness detection runs concurrently to confirm the submission is from a live person, not a photograph, video, or mask.
Benefits of Facial Recognition
Every year, thousands of cases are reported for identity theft and with continuously advancing technology, fraudsters are becoming experts in their job. Simple mechanisms for fraud detection and prevention are no longer useful for the corporate world so digital means of identity verification are crucial. Facial recognition technology is, therefore, a vital part of business operations. Different sectors across the world have benefited from it. Let’s jump into a few benefits of facial recognition.
Seamless Customer Onboarding
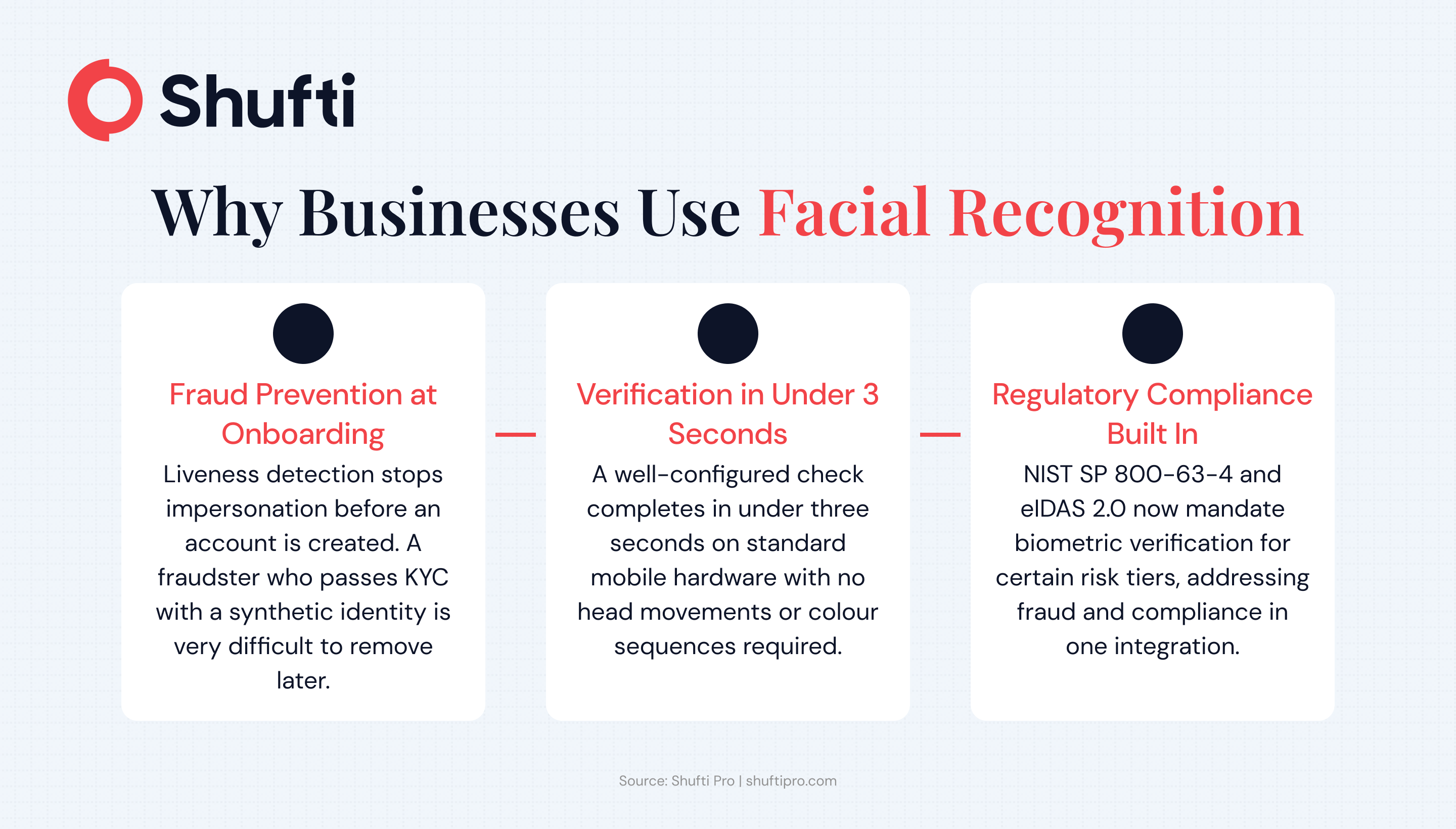
Today’s customers need a highly efficient process for onboarding them that takes only a minute for completion. Considering the tedious manual procedures, businesses might lose customers without automation. Did you know that 74% of customers abandon businesses during the onboarding process because it’s too complex? That’s a lot of customers. Using an online facial recognition system allows businesses to provide a state-of-the-art customer onboarding experience. Identities are verified, customers are effortlessly onboarded, and that too within seconds.
Robust Identity Verification Mechanism
Enhancing the efficacy of the identity verification process requires a system that can not only improve the mechanism but also increase the robustness. Employing face recognition increases the authenticity of the procedure. In case a fraudster has submitted a forged ID document or it has been altered, facial recognition will identify the issue in no time.
Age Verification for Minor Protection
Protecting minors from the perils of the digital world is important and usual “I’m above 18” checkboxes do not suffice. The young ones can easily submit their elders’ ID documents for verification and enter a fake date of birth to dodge identity verification. With facial recognition technology, companies can verify the live presence of the person whose identity documents have been submitted. Minors can easily be prevented from entering the business.
Features of Facial Recognition for Identity Verification
Facial biometric identity verification offers many features that ensure business security and prevent fraudsters from causing any trouble. Here are some of the features that Shufti’s facial recognition software offers:
Liveness Detection
With liveness detection, the chances of spoof attacks are eliminated and the live presence of the end-user at the time of verification. Unfortunately, fraudsters try to bypass biometrics as well, and liveness detection checks enable you to fight them.
3D Depth Detection
To ensure that images haven’t been tampered with, 3D depth detection checks are important. Different points on the image are captured and compared to the ones on the previously digitised image (the unique code generated for the selfie). 3D recognition, skin texture analysis and human intelligence are collectively used for this check.
Deep Fake Identification
If the merchant has opted for videos for identity verification or video KYC, the system performs different AI-based checks like skin texture analysis, image distortion analysis and 3D depth detection to detect any deepfakes.
Use Cases of Facial Recognition
Facial Recognition can be employed in many industries to prevent fraudsters from hindering identity verification systems. Here are some use cases of facial recognition technology:
Facial Recognition for Banking and Finance
The banking and finance sector is a goldmine for criminals. Creating fake bank accounts, account takeover (ATO) fraud, identity theft, money laundering, and terrorist financing are some of the fraudulent activities that are on the rise. So, the banking and finance sector must employ facial recognition biometrics for verifying identities.
Facial Recognition in Safety and Security
The overall security and safety of the corporate world require the utmost attention and a facial recognition security system is what businesses need. From border checks to security clearance at airports, the vitality of facial authentication technology cannot be doubted.
Facial Recognition for Law Enforcement Agencies
Law enforcement agencies use facial recognition to identify criminals. Using this system at check-ins and security checkpoints can help law enforcement agencies know if any criminal is residing within the system, undetected. The face recognised can be matched with the images in the database for this purpose.
Facial Recognition for the E-Commerce Industry
Facial recognition in the e-commerce industry has made payment systems seamless. All it takes is your face to verify and book your order. It reduces the chances of chargebacks and other fraud. Furthermore, merchants can enhance the customer experience as well.
Facial Recognition for Gaming Industry
The gaming industry is the second biggest target of financial criminals for achieving their illicit goals. To combat them, all online gaming platforms can use face detection and onboard legitimate players in real-time. Moreover, minors have easy access to these gaming sites, but facial authentication can prevent them from accessing adult-oriented games.
Facial Recognition for Cryptocurrencies
Cryptocurrencies are anonymous and have become a viable option for fraudsters to launder illegally earned money. So, cryptocurrencies need a better option for identity verification to comply with the regulations and prevent fraudsters from achieving their malicious goals. AI-based facial recognition software is what the crypto market can adopt.
Facial Recognition for the Healthcare Sector
With facial recognition, the healthcare sector can onboard patients without any delays. This system can help in restricting unauthorised access, and patient records can be kept safe. Moreover, fraudsters cannot avail patient benefits or acquire prescription-only drugs if face verification is added as a mandatory requirement.
Book a free demo and test it against your use case.
Facial Recognition and Global Regulations
Governments and regulators throughout the world are drawing boundaries around how and where facial recognition can be deployed. Businesses using biometric verification need to understand three frameworks in particular.
EU AI Act (high-risk compliance track: August 2026). The EU AI Act prohibits the creation of facial recognition databases through untargeted scraping. Identity verification for the sole purpose of confirming a specific person is who they claim to be is explicitly exempted, but systems deployed in this context still fall under the high-risk category and must meet transparency, accuracy, and human oversight requirements before August 2026.
GDPR Article 9. Biometric data used to identify a natural person qualifies as special category data under GDPR. ICO guidance updated in 2025 states that explicit consent is the most appropriate lawful basis for most biometric recognition use cases, meaning businesses must obtain a clear, specific opt-in before running facial recognition on their users.
NIST SP 800-63-4 (finalised July 2025). NIST’s revised digital identity guidelines mandate Presentation Attack Detection (PAD) for all Identity Assurance Level 2 (IAL2) and above remote biometric verification. For businesses targeting regulated use cases in financial services, healthcare, or government, compliance with NIST SP 800-63-4 is no longer optional.
How Can Shufti Facial Recognition Help?
Shufti is among the fastest facial recognition software providers and employs thousands of artificial intelligence models to authenticate the live presence of the end-users. Furthermore, it detects spoof attacks and deepfakes to enhance security. The identity verification system has multiple layers and the process begins with document verification. Next is the face verification step that works in two simple steps.
A selfie or video is required from the end-user, which is authenticated using AI. A unique signature is created for the photo, which is used in step two for verification.
The end user’s image in the government-issued ID document is verified against the unique image code generated as mentioned above. In case the image of the document does not match the photo, the verification is declined.
Facial recognition technology has been in action since the 1960s, and today, it is one of the most powerful tools to enhance security. The corporate world can seamlessly onboard customers, comply with the CDD requirements and enhance the overall security of the enterprise. Face recognition software is also a great way of identifying criminals at border checks and airports. By using thousands of AI models, all it takes is a few seconds for Shufti’s facial recognition software to detect spoof attacks and deep fakes. There is no end to the uses and benefits of this technology. All you have to do is get in touch with us.
Frequently Asked Questions
Why is facial recognition important?
Facial recognition adds a layer of identity assurance that documents alone cannot provide. A stolen or forged ID can pass a document check, but it cannot pass a live biometric match. For regulated businesses, it also satisfies the biometric verification requirements of KYC/AML frameworks and reduces manual review workload significantly.
Is facial recognition safe?
When deployed with liveness detection, presentation attack detection, and encryption in transit and at rest, facial recognition is considered a secure form of identity verification. Modern systems, including Shufti’s, cover 56+ anti-spoofing attack vectors and process biometric data under GDPR and ISO 27001 controls.
How accurate is facial recognition?
Accuracy depends on the system. Shufti’s facial biometrics achieve 98.72% accuracy (iBeta Level 1 and Level 2 certified), with a False Acceptance Rate below 0.001. DHS RIVR 2025 independently validated Shufti as a top performer, distinguishing independently tested accuracy from vendor-reported figures.
How do facial recognition systems ensure real-time verification?
Real-time verification requires fast face detection, a GPU-accelerated matching engine, and concurrent liveness detection. Shufti completes the full face verification check in under 3 seconds. Liveness detection runs simultaneously (not sequentially), so the total time to decision does not increase.
Does facial recognition work on all devices and cameras?
Modern facial recognition systems are designed to work across mobile cameras, webcams, and dedicated capture hardware. Image quality, lighting, and camera resolution affect accuracy. Shufti’s SDK-based capture with guided UX achieves a 95% first-attempt success rate across device types.
Can facial recognition identify people with facial disabilities or changes?
Modern AI models are trained to handle natural variation, such as ageing, facial hair, glasses, minor scarring, and skin tone diversity. Significant facial changes can affect match accuracy. Reputable providers offer alternative verification pathways or human review escalation so no customer is unfairly rejected.