Elevating Payment Security: The Crucial Role of Biometric Authentication

There has been a considerable rise in digital payment methods in recent years. People now prefer using digital payment methods over cash, as it is inconvenient and comparatively less reliable than digital payments. They provide users with more security and reliability, as these transactions serve as proof. Moreover, modern digital payment service providers allow users to leverage safety mechanisms such as instant financial statements and payment reversals, which can save them from financial losses. Biometric authentication provides individuals with a further improved layer of security, allowing them to stay safe in our evolving digital ecosystem.
Fraud is also a prevalent issue with today’s online payment methods. This year, Card-not-Present (CNP) fraud will account for $9.49 billion in losses, up 8.5% over last year, according to our data. CNP will make up 73.0% of card payment fraud losses this year, up from 57.0% in 2019. Moreover, e-commerce losses due to online payment fraud are estimated to reach $48 billion globally, up from $41 billion in 2022.
Hence, traditional protection methods like PINs and passwords are insufficient to protect users from cyber threats while making online payments. A robust biometric authentication system can help businesses and individuals avoid heavy financial losses and complications due to low levels of security. These security methods are vulnerable to breaches, and cybercriminals can exploit the stolen data. The majority of identity theft cases include stolen credit cards and financial information used to commit crimes under the name of a legal citizen.
The Basics of Biometric Verification
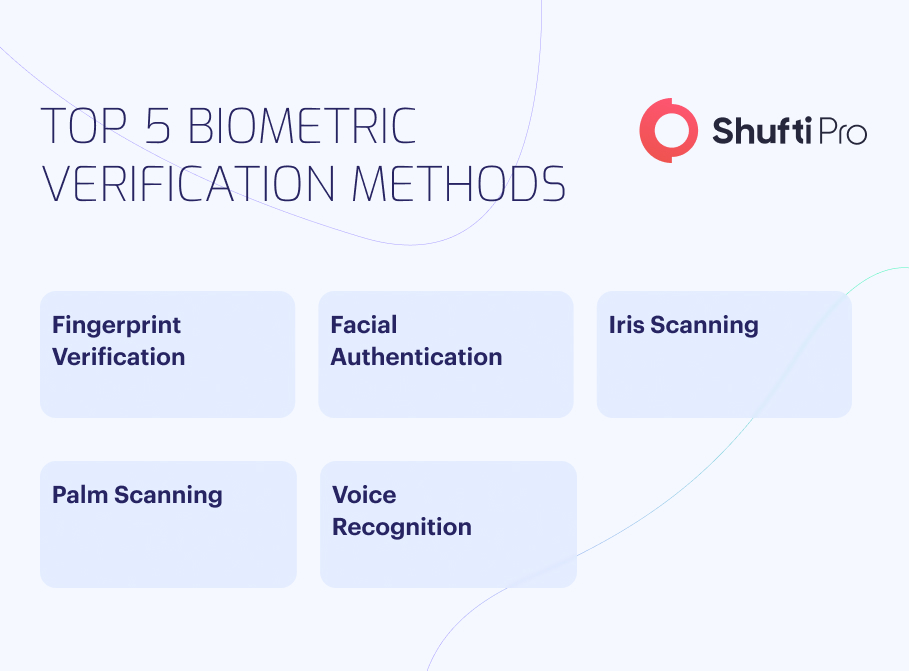
Biometric authentication is a crucial user verification method that can be used to verify whether a user is legitimate. What makes this verification method stand out from the rest is its capability to identify user-specific characters ranging from facial and fingerprint patterns to iris verification that uses infrared light to reveal the specific patterns of a user’s iris. These characteristics cannot be forged, or fake copies can’t be made, as they exist at a micro level and cannot be replicated. Cybercriminals can generate fake rip-offs of these characteristics, but a robust biometric authentication system can always spot the difference between users’ actual and simulated biometric characters.
However, the most commonly used example of biometric authentication is fingerprint verification, which uses a user’s fingerprint patterns for verification. Fingerprint verification can be used during user onboarding and as a security firewall at checkpoints during a customer’s journey. A survey shows that 75% of Americans feel comfortable using fingerprint recognition technology. Using fingerprint verification by mobile banking service providers establishes a more robust mechanism for user authentication, ensuring no illegal entity accesses the digital bank accounts of a legitimate user. Fingerprint verification in the digital banking sector also boosts convenience by allowing users to access their bank accounts from the comfort of their homes without worrying about security risks. This process is also relatively convenient for businesses in the banking sector because it can eliminate manual verification processes and data-keeping. This saves them significant resources and time, which can be utilized elsewhere.
Adapting to Change: Biometric Facial Recognition
Our current digital system has been evolving at an incredible pace. Cybercriminals and fraudsters have been using technologies such as AI and ML to create new methods to commit criminal activities. A clear example of this is identity theft. From phishing attacks to creating data breaches and backdoors in a system, cybercriminals have not left a single data system unchecked. With these breaches, criminals can access users’ crucial financial information, which is then used to disrupt their financial processes.
Another primary concern in this instance is that of deepfakes. Deepfake technology uses a user’s biometric data to create a video or real-time deepfake of a specific user. This is one of the latest and most prevalent threats in the current digital age. If a company does not have proper biometric authentication incorporated into its processes, it might be unable to differentiate modern deepfakes from real users. This way, these companies can fall victim to scams and fraud. Biometric verification online helps companies avoid deep fakes while onboarding remote users or conducting business online.
The technology utilized in this process is known as liveness detection. It is the most advanced facial biometric authentication method available. It uses a challenge-response mechanism that requires the user to perform specific actions. Since a deepfake is programmed before an attack, it fails to perform the specified tasks. 3-D depth analysis allows these verification solutions to combat deep fakes more effectively. 3-D depth perception allows biometric identification solutions to capture depth information, allowing them to differentiate between a flat image and a three-dimensional face. Apart from that, artificial intelligence (AI) and machine learning (ML) help these software solutions conduct accurate behavioral analysis based on pattern recognition, further solidifying their efforts to verify the user.
Biometric Payment Solutions: A Brief Overview
Almost all primary payment methods now support biometric authentication. In a typical case, a service provider usually adopts a biometric authentication system from an external provider that integrates the verification process into the company’s general processes.
-
Mobile Payments
General mobile payments, such as Google Pay and Apple Pay, use online biometric verification to carry out payments. An Apple user can simply put their iPhone before the contactless reader, using face ID recognition or fingerprint biome
tric verification to authenticate the transaction. Similarly, Android users can tap their phones against an NFC terminal, using a face ID or fingerprint to authenticate the payment. A biometric authentication solution is used to verify the transactions on the company’s end.
-
Biometric Cards and Wearable Devices
To further facilitate consumers and companies, biometric cards and wearable devices are now also used to make payments worldwide. Users can use the fingerprint sensor embedded in the biometric card to authenticate the transaction, and in the case of wearable devices, users can use fingerprint verification or wrist-based authentication that uses the veins on the wrist to verify the user. Biometric solutions integrated into the business’s processes can validate these transactions, making payments convenient.
-
Mobile Banking Apps & Online Payment Platforms
Mobile banking apps and online payment platforms with integrated biometric services can aid user convenience by enabling them to use biometric logins. Instead of PINs and passwords, users can use biometric features such as face verification and fingerprints to validate transactions. This way, users can easily make payments and transfer assets without the hassle of extensive verification processes.
-
Biometric-Enabled ATMs and POS Systems
Apart from fintechs and online payment platforms, physical banks and businesses can also use biometric technologies to make their payments more convenient. ATMs enabled with real-time biometric identification can allow users to withdraw cash with more convenience, and it also helps prevent theft. Besides, biometric-enabled POS machines can make daily payments seamless, saving users and businesses significant resources.
-
Blockchain and Cryptocurrency Payments
Crypto and blockchain assets are usually well protected and have a decentralized system, with each asset having its place in the blockchain, making replication and theft impossible. Still, there is a risk of fraud and scams. This is because most cryptocurrency wallets rely on user-specified seeds. Each user has a specific seed; if someone gets access to that combination, they can access the crypto wallet. Online biometric verification allows users to add an additional layer of security to their crypto wallets, ensuring only they get access to their wallet.
Biometric Authentication With Shufti
Biometric authentication is becoming more common among digital providers, so they must choose the latest biometric solutions.
Shufti is determined to provide leading digital providers worldwide with top-of-the-line biometric solutions. Our biometric recognition offers businesses verification against a range of biometric features. Users can experience a secure, reliable, easy-to-use authentication system renowned for its accuracy, scalability, and affordability. Businesses can easily onboard and verify users across 240+ countries and territories using our solutions within seconds. With the support of 10,000+ identity documents and records in over 150+ languages, companies can confirm users’ identities with 99% accuracy.
We provide businesses with easy access to 17+ identity verification services, including facial biometric authentication, through a single API integration for ready-to-use, streamlined verification processes.