Your KYC Has Already Approved AI-Generated IDs
Shufti Exposes What Your IDV Missed
Fraudsters do not need to create a fake document from scratch, they take a genuine issued document, alter a name, date, or number, and submit it. Audit 2025-approved IDs in your cloud and expose altered documents, before your regulators do. Run document originality check now!
Runs Entirely
in your cloud
No PII
Ever leaves
No Integration
or coding
50K Identity Pilot
In 30 days

Forgery Is Everywhere
Have your originality checks kept up?
Trusted by 2,000+ Clients Worldwide
Detection Technology
Four Forensic Checks That
Go Beyond Template Matching
Pixel-level Forensic Analysis
Shufti examines document images at the frequency domain level. Detects clone-stamp edits, compression inconsistencies, and selective field manipulations — including altered names, dates, and numbers — that produce no visible anomaly at standard resolution.
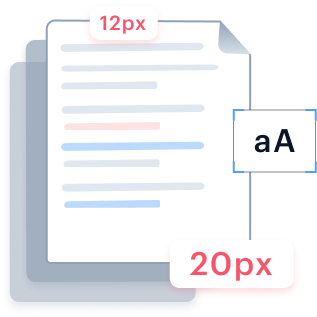
Learn moreTypography and Font Rendering Verification
Shufti compares character spacing, kerning, and font rendering against a reference library of authentic issuing-authority templates. Flags documents where individual characters pass visual inspection but fail statistical comparison against genuine issuing standards.
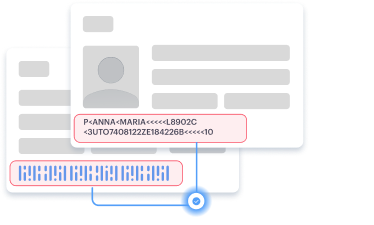
Learn moreMRZ and Barcode Cross-Validation
Shufti cross-validates machine-readable zone data and 2D barcode content against every visible field on the document. Detects discrepancies that appear when visible data is altered but the machine-readable layer underneath is not.
Learn moreDocument Reuse Detection
Shufti identifies matching document signatures across multiple applicant records. Flags instances where the same base document was submitted under different claimed identities, a pattern characteristic of organised fraud operations.
Learn moreRun Shufti Inside Your Environment
Run Shufti within your own infrastructure for maximum data control and privacy.
- Keep all sensitive information in-house to meet strict governance and residency requirements.
- Keep sensitive information fully private and secure in-house.
- Deploy in highly regulated sectors without compromising compliance.
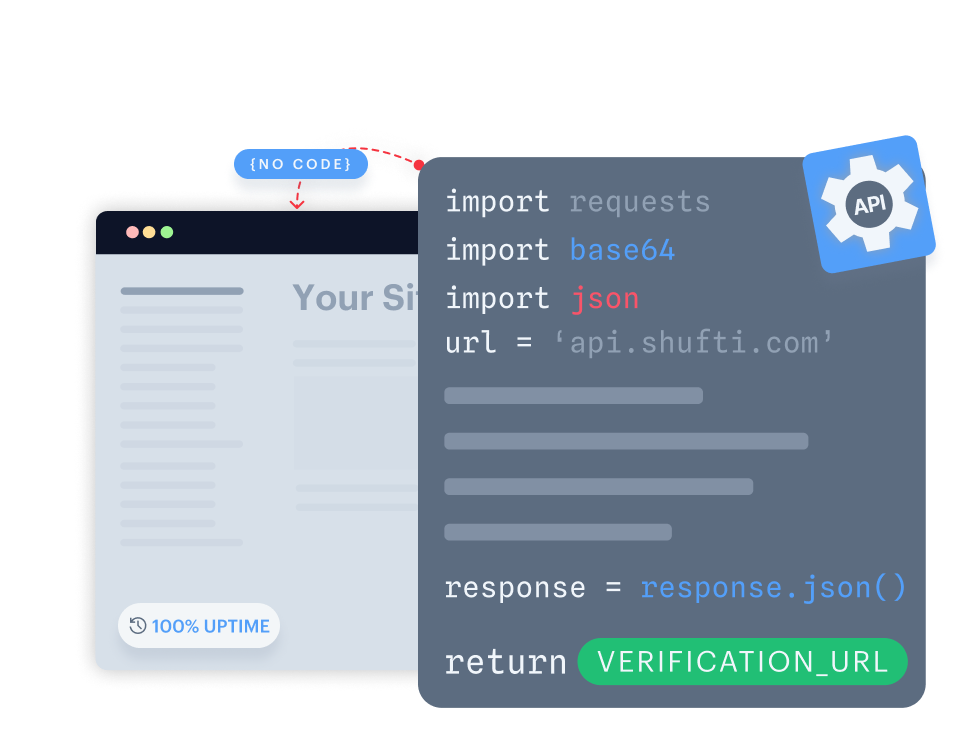
Build fully customizable verification flows with seamless backend integration.
- Gain full control by customising verification flows end-to-end.
- Integrate seamlessly with your backend for quick implementation.
- Design flexible verification journeys tailored to your users.
Launch a native verification experience in your mobile app within minutes.
- Launch native verification within minutes on iOS or Android.
- Use ready-made UI with camera, capture, and real-time feedback.
- Customize flows to fit seamlessly into your mobile app.
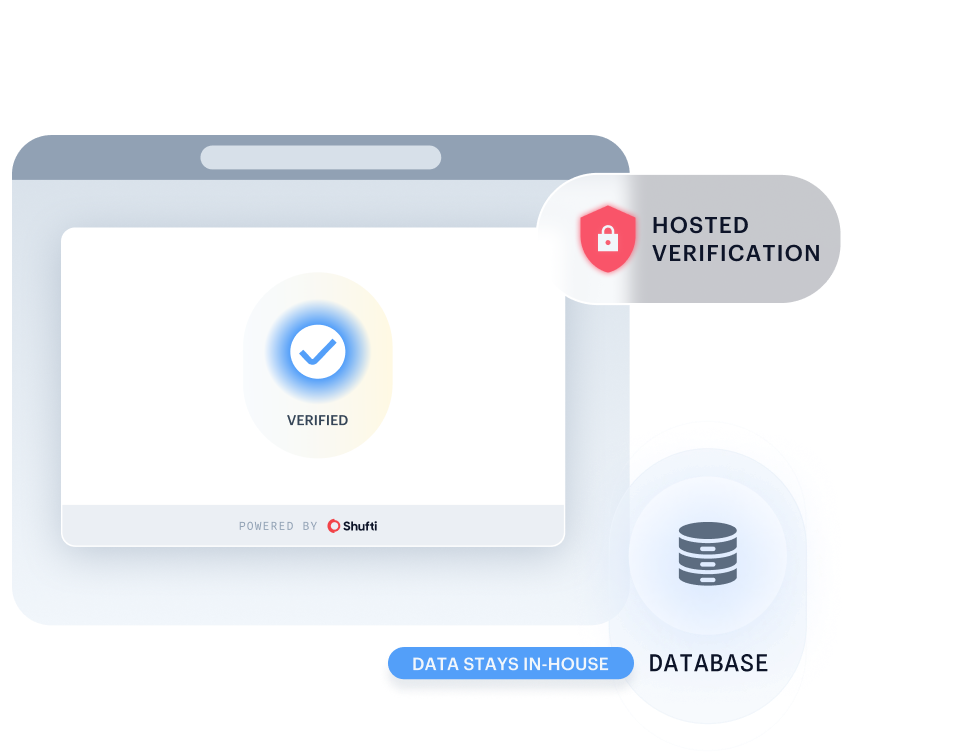
Quickly launch identity verification through a secure, customisable web link, no code required.
- Start verifying users instantly with a no-code setup.
- Deliver a consistent identity experience via a link or embedded iframe.
- Deploy quickly via a secure link or embedded iframe.
Start My Document Originality Audit Now
Launch Shufti’s Document Originality Detector from your preferred cloud marketplace, upload your highest-risk IDs and business documents, and see where AI-forged layouts are being approved by your current checks.
- Easy deployment
- No Integration
- No new contracts
Built for the
Teams That
Own
Fraud and
Compliance
Compliance Officers
Manipulated identity documents are a primary onboarding fraud vector. The audit produces timestamped forensic evidence for each flagged document, supporting SAR filings, EDD decisions, and regulatory examination responses without requiring technical interpretation from the compliance team.
Fraud & Risk
Document manipulation is rarely isolated. A single flagged record often reveals the same base document used across multiple accounts. Audit results feed into case management with risk scores for prioritised investigation, turning one find into a full ring.
Product & Engineering
The audit processes stored document images with no changes to the live pipeline. Integration via API or batch CSV upload. Results return structured JSON with field-level signal breakdowns and confidence scores, compatible with existing case management systems.
Run a Blind Spot Audit Where Failure Hurts Most
Where Document Manipulation Causes the Most Damage
Digital Banks & Fintech
Manipulated date-of-birth documents enable underage account opening and synthetic age fraud. Audit flags altered fields before they become regulatory liability.
PSPs & Remittance
Forged address and identity fields allow money mules to pass KYC. Document originality checks identify altered submissions in historical transaction accounts.
Crypto & Web3
Reused and modified national IDs enable multi-account fraud across exchanges. Audit identifies document reuse rings in your onboarded base.
Online Lending & BNPL
Modified income and identity documents enable fraudulent credit applications. Audit surfaces manipulated submissions before defaults escalate.
Gaming & iGaming
Altered age documents bypass responsible gaming controls. Audit identifies historical approvals where fields were changed post-issuance.
Marketplace & Gig Economy
Seller identity fraud relies on modified documents to pass verification. Audit identifies compromised seller accounts before platform abuse escalates.
EVERYTHING YOU NEED TO KNOW IN ONE PLACE
Frequently Asked Questions
What does a document originality audit check?
It re-analyses stored identity document images for field-level manipulation, altered names, dates, and numbers, using pixel forensics, typography analysis, MRZ cross-validation, and reuse detection. It operates on documents already approved by your original verification system.
How is this different from standard document verification?
Standard verification checks that a document matches a known template and that fields are correctly formatted. Document originality detection checks whether fields were modified after the document was issued, using frequency-domain analysis that template matching cannot perform.
Does the audit require customers to resubmit documents?
No. It re-analyses document images already stored from original verification. No customer contact is triggered.
What does a flagged result include?
Each flagged document returns a status classification, confidence score, signal breakdown, and visual annotation showing the affected image region. The evidence package is formatted for direct use in compliance workflows.
Does data leave our environment?
No. Document images are analysed inside your cloud environment. Nothing is transmitted to external systems.
Secure Your Entire System
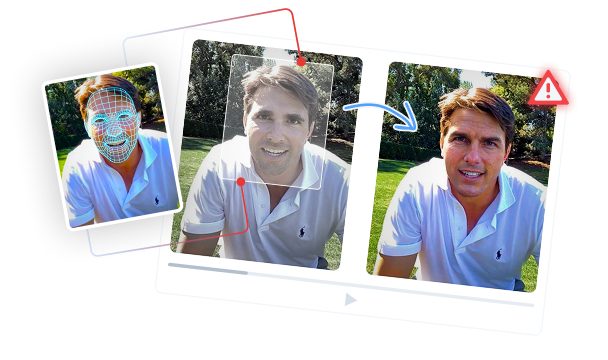
Deepfake Detector
Block all the forged AI-generated faces and fake identities with Shufti's Deepfake Detector.
Learn moreDocument Deepfake Intelligence
Re-scan approved IDs to expose AI-generated and forged documents without sharing PII data.
Learn moreFace Liveness
Find deepfakes, replays, and spoofs hiding in passed liveness sessions, all inside your cloud.
Learn more