Journey Builder Library: One Platform, Tailored Compliance Flows for Every Market
Every regulated business has its own AML compliance program. The regulatory requirements vary by market, the risk appetite differs by industry, and the customer due diligence expectations shift depending on the customer segments being served.
Yet, when it comes to identity verification, most businesses are stuck with the same rigid, pre-packaged workflow regardless of whether they’re onboarding retail traders in Germany or marketplace sellers in Southeast Asia.
For crypto exchanges, fintechs, iGaming platforms, and social media marketplaces, this mismatch creates a very real problem. The verification platform they rely on doesn’t give them the flexibility to build user journeys that reflect the specific requirements of their AML compliance program or the regulatory framework of each market they operate in.
The end result is often predictable; users posing low risk face unnecessary friction during the onboarding process (which hurts conversion rates). On the other hand, high-risk users can pass through checks that were not designed to flag or identify the signals that could matter for that particular business.
In order to fully cater to the gap that persisted between what compliance programs truly require and what the majority of verification tools are actually fully able to deliver, Shufti essentially the exact reason why Shufti built the Journey Builder Library.
Why do most Verification flows look alike when that is not the case with Two Compliance Programs?
The primary issue is pretty self-explanatory, which is that two businesses do not share the same AML compliance programs. For example, a neobank regulated by BaFin that is based in Germany has document verification, video identification, and AML screening all gelled into its compliance program. Similarly, an iGaming operator based in the UK would require age verification along with enhanced due diligence. A peer-to-peer marketplace, on the other hand, may only require some basic identity proofing once a certain transaction volume is crossed by sellers.
All of these businesses have their own recognized and defined risk thresholds along with CDD requirements, as well as onboarding logic based on whichever regulations they operate under.
However, most identity verification platforms fail to reflect on this reality. They work with a handful of preset workflows. It limits businesses to pick the closest match and make the relevant adjustments within it, where necessary. This eventually becomes the onboarding flow for every customer in every market. There’s no way to build distinct verification journeys for different regulatory contexts or risk tiers, at least not without heavy engineering involvement.
Pushing every customer through the same verification process results in two things:
- Abandonment rate at onboarding rises; this is because low-risk users are subjected to unnecessary checks.
- Surge in compliance gaps because the flow was not configured to put the correct level of scrutiny when actually needed.
Making Compliance Cost-Effective through Risk-Based Verification
Customizable verification workflows no longer remain just a “nice-to-have” option. They have become one of the most practical ways of implementing a risk-based approach in order for compliance to become truly customizable. Verification workflows are not just a “nice-to-have” option. They are one of the most practical ways of implementing a risk-based approach so that compliance can truly become cost-effective.
FATF’s updated 2025 guidance reiterates this point, which is that AML controls should be in proportion to the extent of the assessed risk. FinCEN’s 2025 regulatory overhaul made it even more direct and explicit that AML programs must be “effective, risk-based, and reasonably designed.” The keyword over here is “reasonably designed” for the business, its customer base, and the jurisdiction it serves.
The FATF guidance also specifically urges institutions to “embrace the inherent flexibility in the risk-based approach,” which includes simplified measures for lower-risk scenarios.
The logic behind this is sound, which is that applying the same level of scrutiny to every user regardless of risk doesn’t just result in creating friction; it also results in wasting compliance resources upon checks that are not needed and do not necessarily add value for low-risk segments, while also under-resourcing the reviews that matter most.
By configuring verification journeys according to the regulatory requirements of each market, businesses can ensure a smooth customer experience without subjecting every user to the same compliance flow. A first-time retail user opening a basic account doesn’t need the same verification depth as a high-net-worth individual being onboarded for private banking services. When the verification journey reflects that distinction, businesses reduce drop-offs, allocate compliance resources more efficiently, and still meet every regulatory obligation.
This is the operating principle behind the Journey Library. Low-risk customers get a faster, lighter verification experience. High-risk customers go through the appropriate level of scrutiny. And your compliance team can configure and manage both from the same platform, without writing a single line of code.
What is the Journey Builder Library’s Actual Approach?
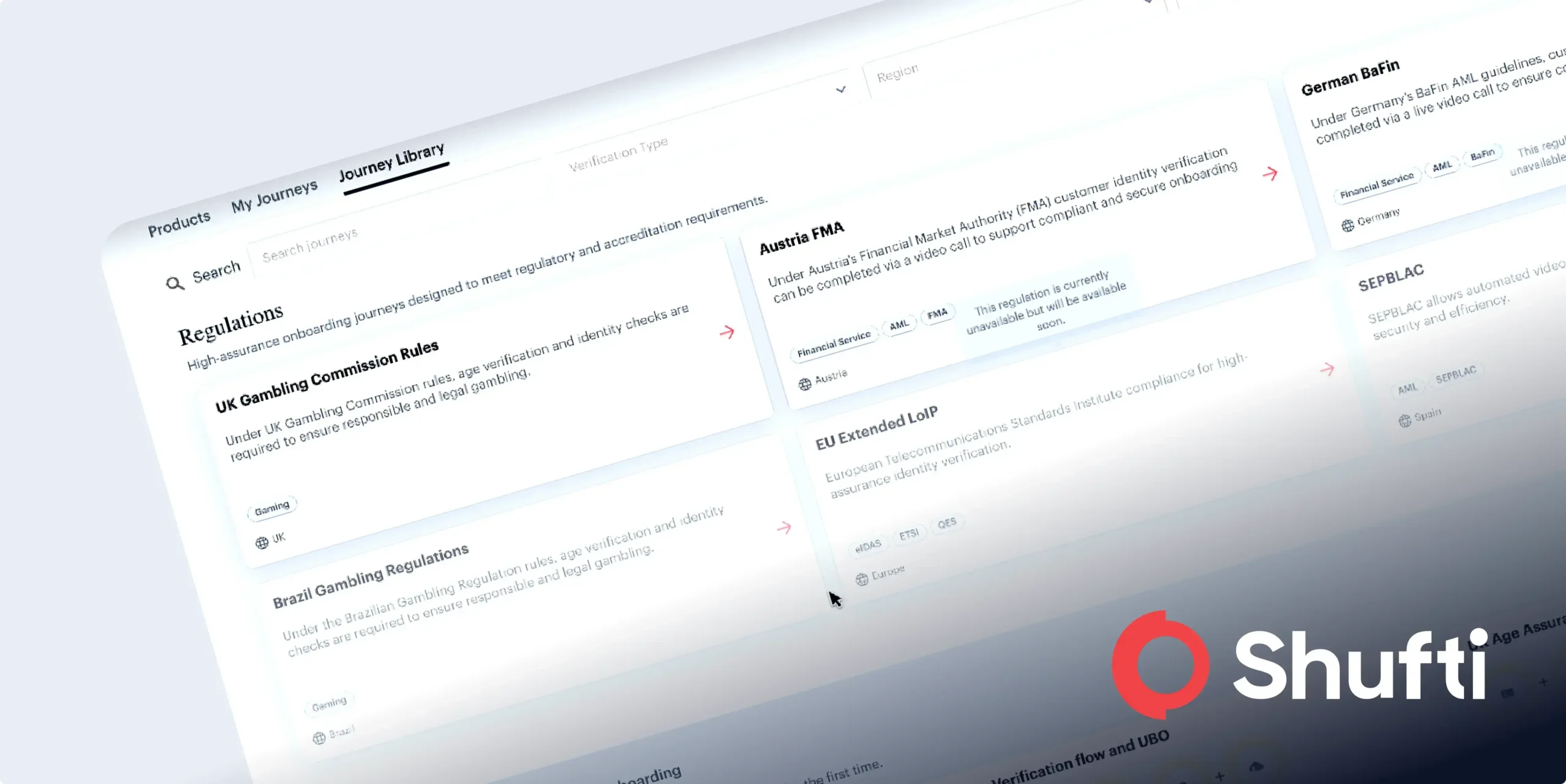
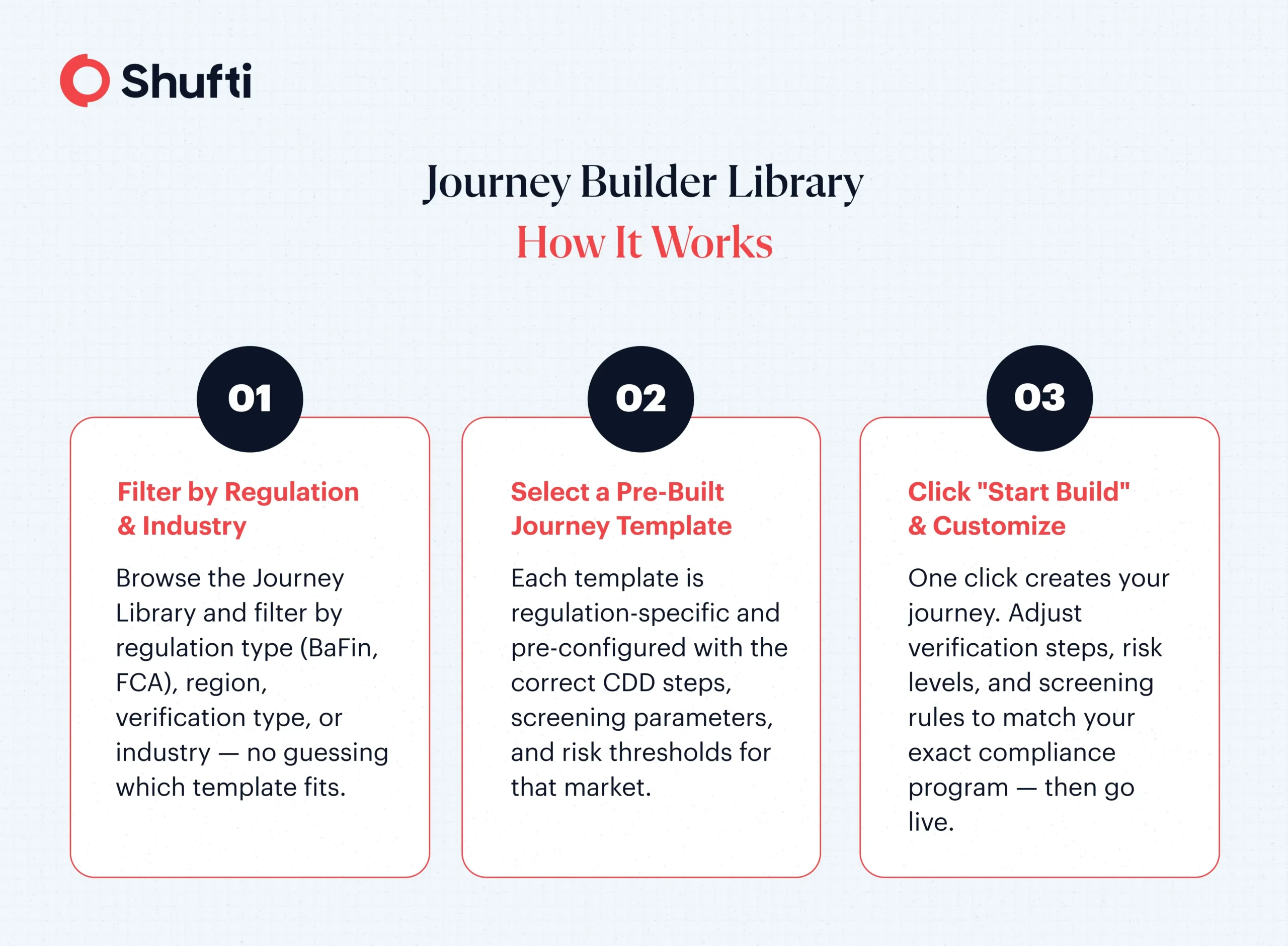
Shufti’s Journey Builder Library adopts a relatively unique approach from the many rigid workflows that most platforms have to offer. Instead of providing businesses with a rigid template or a blank, confusing canvas, the Journey Builder Library offers pre-built, regulation-specific journey templates that can easily be browsed, filtered accordingly, and are ready to be deployed in a matter of only minutes.
Practically, businesses are to log into Shufti Backoffice, navigate their way to the Products page and open the Journey Library. From this step, they filter by regulation type (like BaFin, FCA, non-regulated, and others are also supported) and by journey type, whether a business needs an onboarding flow, an authentication flow, or a pre-onboarding check.
Once a template is selected, a single click on “Start Build” creates an entirely new journey and just redirects the businesses into a configuration flow to finalize the setup.
It ultimately helps the businesses in enhancing customer experience for them.
These aren’t static templates with hardcoded values. Each journey is powered by configurable data, so businesses can adjust verification steps, risk thresholds, and screening parameters to match their specific compliance program. A crypto exchange can combine document verification with AML screening and enhanced due diligence. An iGaming operator can start from an age verification template and layer on identity proofing and ongoing monitoring.
The library also handles the technical details that cause configuration errors on most platforms—linking templates to their correct IDs and UUIDs, validating configurations across account types, and applying the right compliance settings automatically based on the regulation selected.
Why is this Important for Compliance and Product Teams?
There are three practical benefits that typically stand out for compliance and product teams.
- Speed: Building verification flows from scratch or reverse-engineering a preset template eats up engineering and compliance hours. The Journey Library cuts that setup time down. This way, compliance teams can browse, select, and launch a regulation-ready flow without filing a ticket with engineering.
- Accuracy: When configurations live in a centralized library linked to validated templates, the risk of misconfiguration drops. No accidentally skipping a required screening step for a BaFin-regulated account. No, deploying a non-compliant flow because someone copied the wrong settings from a staging environment.
- Scalability: As a business expands into new markets or adds new product lines, it needs new verification journeys for each regulatory context. The Journey Library’s data model is built for this, adding support for new regulations, templates, and services without requiring a platform overhaul. Compliance infrastructure can grow alongside the business, not behind it.
The UI has also been refined with updated filters, tabs, and clearer messaging for unavailable journeys. If a template isn’t available for a particular account type, the platform provides a clear explanation instead of a confusing error.
More journey templates are being added to the library in the coming weeks, expanding coverage across additional regulations and onboarding scenarios.
For businesses whose current verification setup forces the same flow on every market regardless of risk, it might be worth exploring a different approach. Request a demo to see how Shufti’s Journey Builder Library works with different compliance programs.
Frequently Asked Questions
What is the Shufti Journey Builder Library?
The Journey Builder Library is a centralized collection of pre-built, regulation-specific verification journey templates available in Shufti’s Backoffice. Authorized users can browse, filter by regulation and journey type, and deploy onboarding, authentication, or pre-onboarding flows without engineering support.
Can businesses customize the pre-built journey templates?
Yes. Each template is powered by configurable data, allowing businesses to adjust verification steps, risk thresholds, and screening parameters to match their specific compliance requirements. Templates are starting points, not rigid workflows.
Which regulations does the Journey Builder Library support?
The library currently supports multiple regulation configurations, including BaFin and non-regulated handling, with more regulation options being added regularly. Each template applies the correct compliance settings automatically based on the selected regulation.
Who can access the Journey Builder Library?
The library is available to authorized users under the Products page in the Shufti Backoffice. Role-based access ensures that only team members with the appropriate permissions can create or modify verification journeys.

 Explore Now
Explore Now