eIDAS 2.0 and the EUDI Wallet: What It Means for Address Verification

By December 2026, every EU member state must provide a government-issued/approved digital identity wallet for its citizens. By December 2027, regulated businesses (banks, fintechs, and payment providers) must accept it.
The architecture decisions compliance teams make today will determine whether they lead that transition or scramble to catch up.
What is the EUDI Wallet?
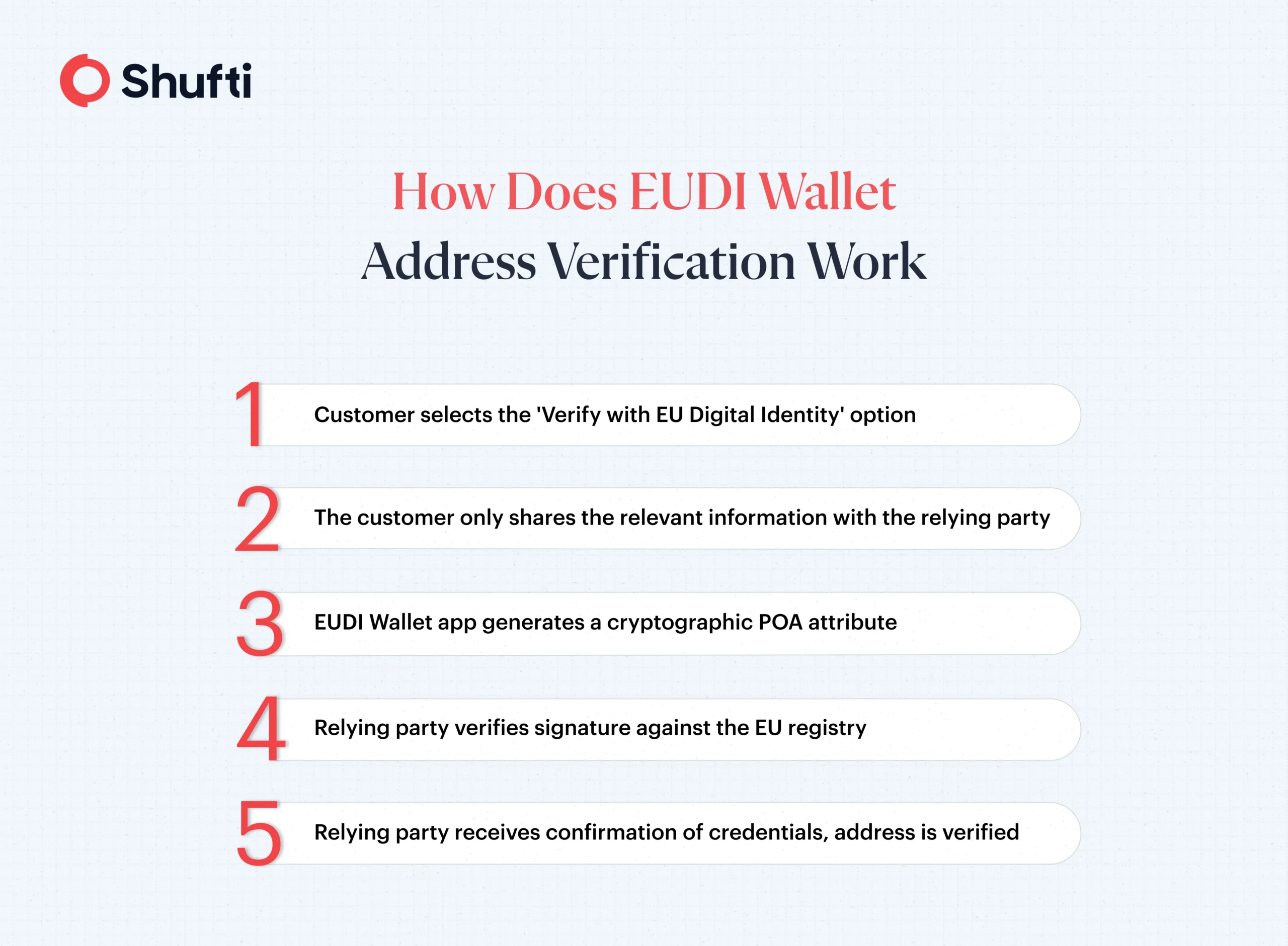
The European Digital Identity Wallet (EUDI Wallet) is a government-issued mobile application that stores cryptographically signed attributes about a person (name, date of birth, nationality, and other credentials), including a verified residential address.
Every EU member state is legally required, under Regulation (EU) 2024/1183 (eIDAS 2.0), to provide citizens with digital wallets free of charge. The wallet itself does not store a photo of a passport, for example, or a scan of a utility bill. It holds verified data fields, signed by trusted public authorities. When a customer shares their address with a third party, they provide cryptographic proof of address (POA) that is verified by a trusted authority.
This distinction matters for anyone who has spent years building document-based POA pipelines.
Why Existing Address Verification Pipelines Struggle under eIDAS 2.0?
Most address verification flows today share the same fundamental weakness: trust is placed in a document that a customer has supplied, rather than in a verified data source. A utility bill demonstrates that someone once received mail at an address. It does not confirm they live there now, and it offers no technical guarantee against tampering.
There can be operational consequences:
- OCR extraction fails on low-quality uploads.
- Human review queues create delays that result in low conversion rates.
- Fraud teams flag false positives that reject legitimate customers.
These challenges are made worse by the fact that across the 27 EU member states, document standards are inconsistent. A French relevé de compte (French bank statement) looks nothing like a German Kontoauszug (German bank statement). Address verification frameworks must accommodate different formats across jurisdictions.
eIDAS 2.0 replaces this model entirely. Under the new framework, regulated institutions that are required by law or contractual obligation to conduct strong customer authentication for online identification must accept EUDI Wallet credentials when a customer presents them. Each member state’s wallet version will be interoperable with other wallets across the EU. Article 5f(2) of the regulation sets the compliance deadline for financial institutions at December 2027:
Thus, continued reliance on document upload as the primary POA method across the EU is no longer a sustainable practice, especially not after the 2027 deadline.
How Docless POA Verification Solves This Problem:
EUDI Wallet adoption will not be universal from day one. ABI Research forecasts 169 million digital identity wallets in circulation by 2026, a significant number, but short of the EU’s own 80% adoption target set for 2030. During the multi-year transition window, onboarding flows will serve two distinct user populations simultaneously. Banks and other regulated entities are likely to encounter two types of customers between 2026 and 2029:
- Those with an EUDI Wallet can instantly share verified addresses.
- Everyone else will still need an alternative path (i.e., physical uploads).
Wallet users can provide verified address attributes in seconds. Non-wallet users still need an address verification path that does not rely on document uploads.
The critical mistake to avoid is treating the non-wallet path as a legacy fallback, keeping the utility bill upload flow alive indefinitely while bolting on wallet support. That approach creates two quality tiers in a compliance stack, and the lower tier is exactly where fraud concentrates.
The right architecture runs both tracks at the same assurance standard. For customers without a wallet, this means docless POA verification: cross-referencing verified data signals to confirm an address without requiring the user to supply a document.
The transition window is not a reason to delay. It is the reason to build the right foundation now, before EUDI adoption makes document-based fallbacks the obvious target for fraud.
What EUDI-Ready Address Verification Requires From the Verification Stack?
Five capabilities determine whether a verification stack can operate effectively across both wallet-native and non-wallet populations:
1. Protocol support:
Third-party integrations must support OpenID4VP and OpenID4VCI (the protocols the EUDI Wallet uses to present and verify credentials). These are not optional extensions; they are the communication layer on which the entire ecosystem operates.
2. Selective disclosure handling:
The wallet allows users to share individual attributes without exposing their full identity. Identity verification systems need to request and process only the address field, not the entire PID (Person Identification Data), to satisfy GDPR data minimisation requirements.
3. Cross-member-state compatibility:
There are 27 national wallet implementations. A German wallet and a Spanish wallet both comply with the Architecture and Reference Framework (ARF), and the integration must support all wallet variants.
4. Audit-ready verification logs:
eIDAS 2.0 compliance requires demonstrable records of verification events. Systems must log the verification result, the attribute source, and the timestamp, without storing the raw credential content, thereby eliminating unnecessary data retention risk.
5. A docless fallback at equivalent assurance:
For non-wallet users, the fallback must match the fraud-resistance standard of the wallet path.
The December 2027 deadline for financial institutions is 21 months away. Typical enterprise identity infrastructure changes take 9 to 18 months end-to-end, including architecture review, vendor selection, integration, testing, and compliance sign-off. Organisations that start now will complete on time. While those who wait for the 2026 wallet rollout before beginning will not.
How Shufti Supports the EUDI Transition?
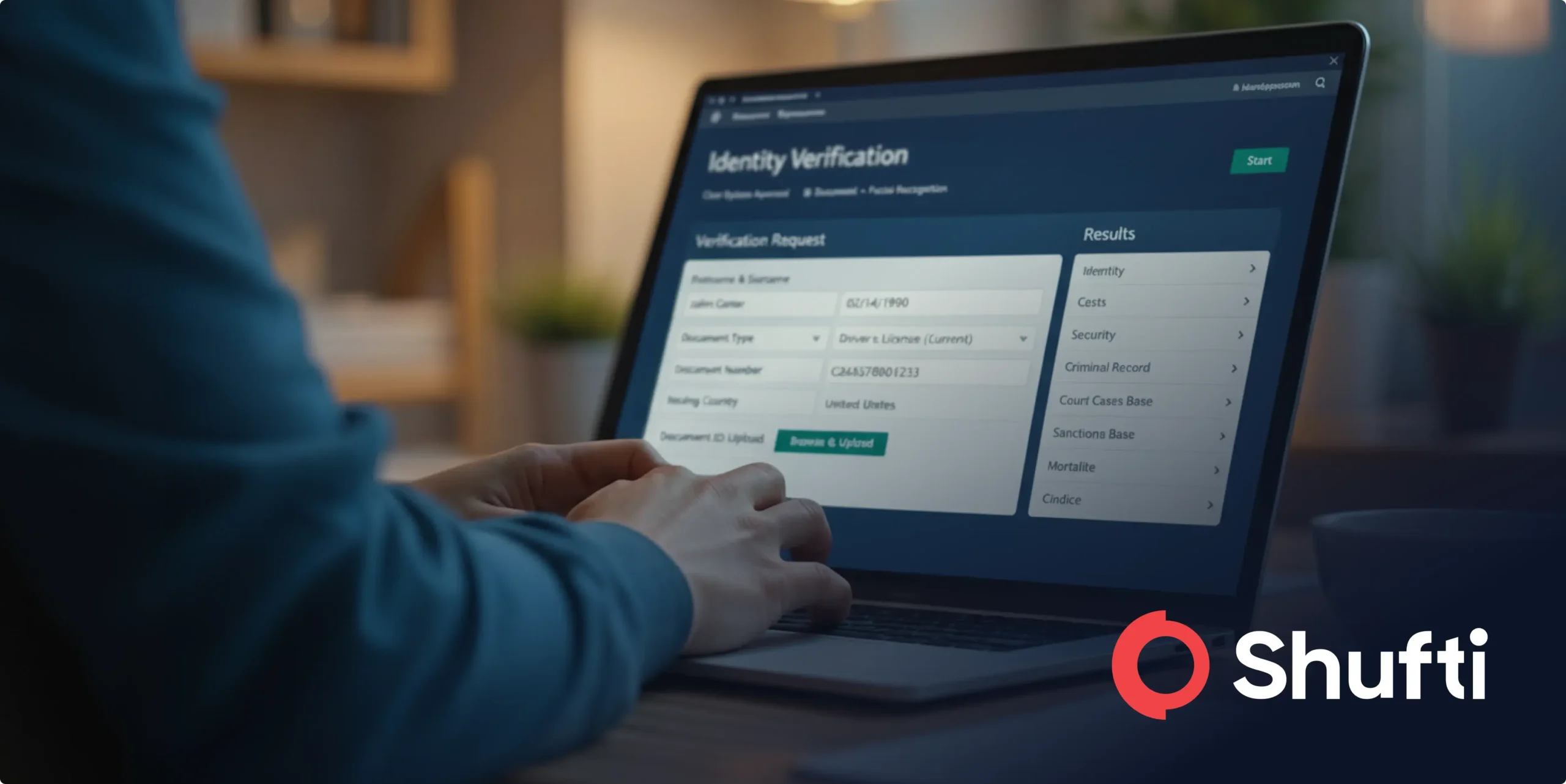
Shufti address verification is built for exactly this moment, the period where wallet-based attributes and non-wallet verification paths must operate in parallel, at the same assurance level, across all 27 EU member states.
Our docless POA solution handles non-wallet users via cross-referenced data signals (telco, credit bureau, open banking) without document upload, manual review, or the fraud exposure of static PDF checks.
Shufti is currently integrating with EUDI Wallet sandboxes, starting with France, and will register as an intermediary relying party before wallets become operational to connect relying parties (banks, fintechs, health, transport, and energy) with EUDI Wallet infrastructure across all EU member states.
Book a demo today to upgrade your POA stack for the future of address verification in the EU.

 Explore Now
Explore Now