DEVICE FINGERPRINTING
Stop Fraudsters From Resetting Their Risk History
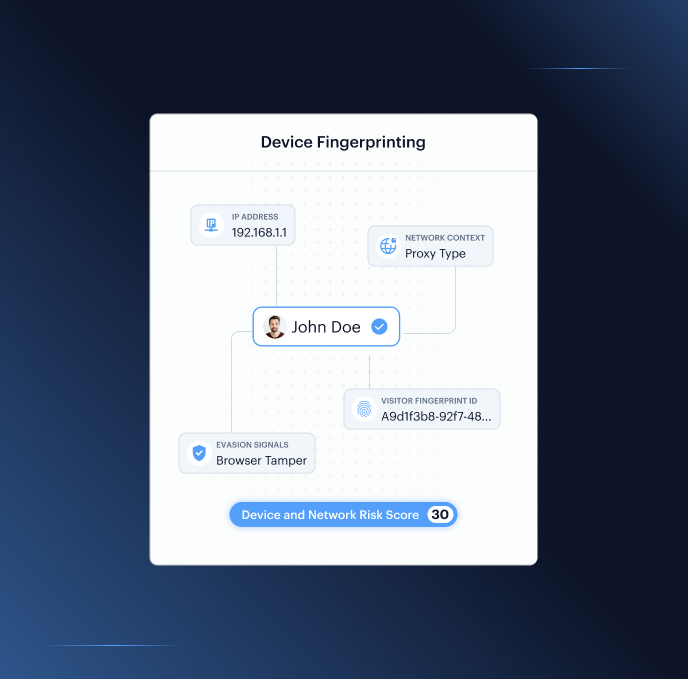
Returns a persistent Visitor Fingerprint ID, composite Threat Level, and signals across network routing, device integrity, and evasion detection, per verification event.
Faster Fraud Decisions Stronger Detection
Four Layers Standard Fingerprinting Doesn't Reach
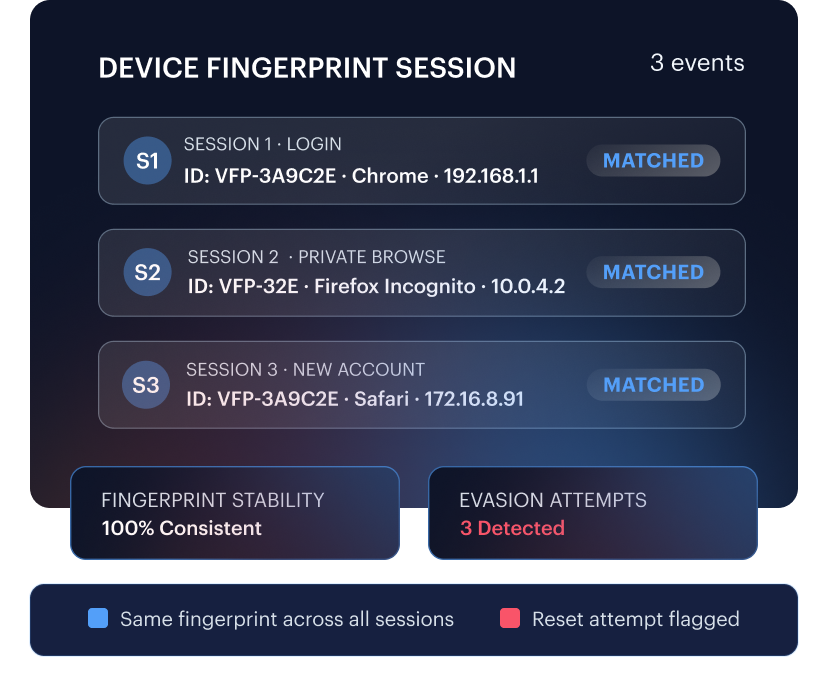
Persistent Identity Across Sessions
Fraudsters clear cookies or use private browsing to appear as a new user. Shufti's Visitor Fingerprint ID stays consistent across cookie clears and private browsing.
Fraudsters change IPs or switch networks to break the tracking trail. Shufti's fingerprint remains consistent across network changes, same device, same history.
Fraudsters create new accounts expecting each to look new to the platform. Shufti keeps device history connected even across new account registrations and different sessions.
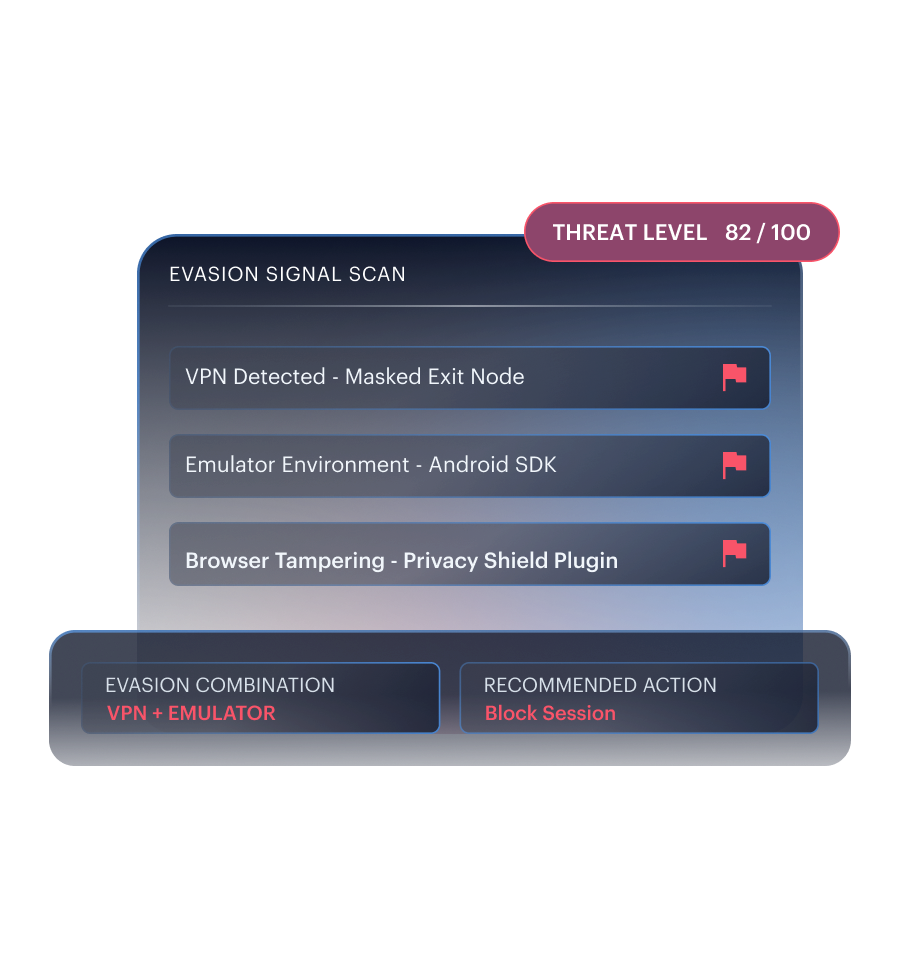
Evasion Attempts Become Risk Signals
Fraudsters mask their location using VPNs, proxies, and TOR. Shufti detects each and returns them as evasion signals.
Fraudsters manipulate their device environment to avoid detection. Shufti detects emulators, virtual machines, jailbroken devices, browser tampering, and unusual privacy settings.
Reviewing evasion signals separately misses coordinated fraud patterns. Shufti combines all signals into a single Threat Level that reflects the full risk pattern.
Network Context Behind Every Action
An IP address alone doesn't reveal whether traffic comes from fraud infrastructure. Shufti returns detailed IP, ASN, routing, and proxy context for each device event.
Sessions through datacenters or masked networks look like genuine users without deeper context. Shufti helps fraud teams distinguish genuine users from sessions routed through datacenters and masked networks.
Infrastructure commonly used in organised fraud is invisible without ASN-level analysis. Shufti surfaces suspicious ASNs and proxy contexts so teams can act on the full network picture.

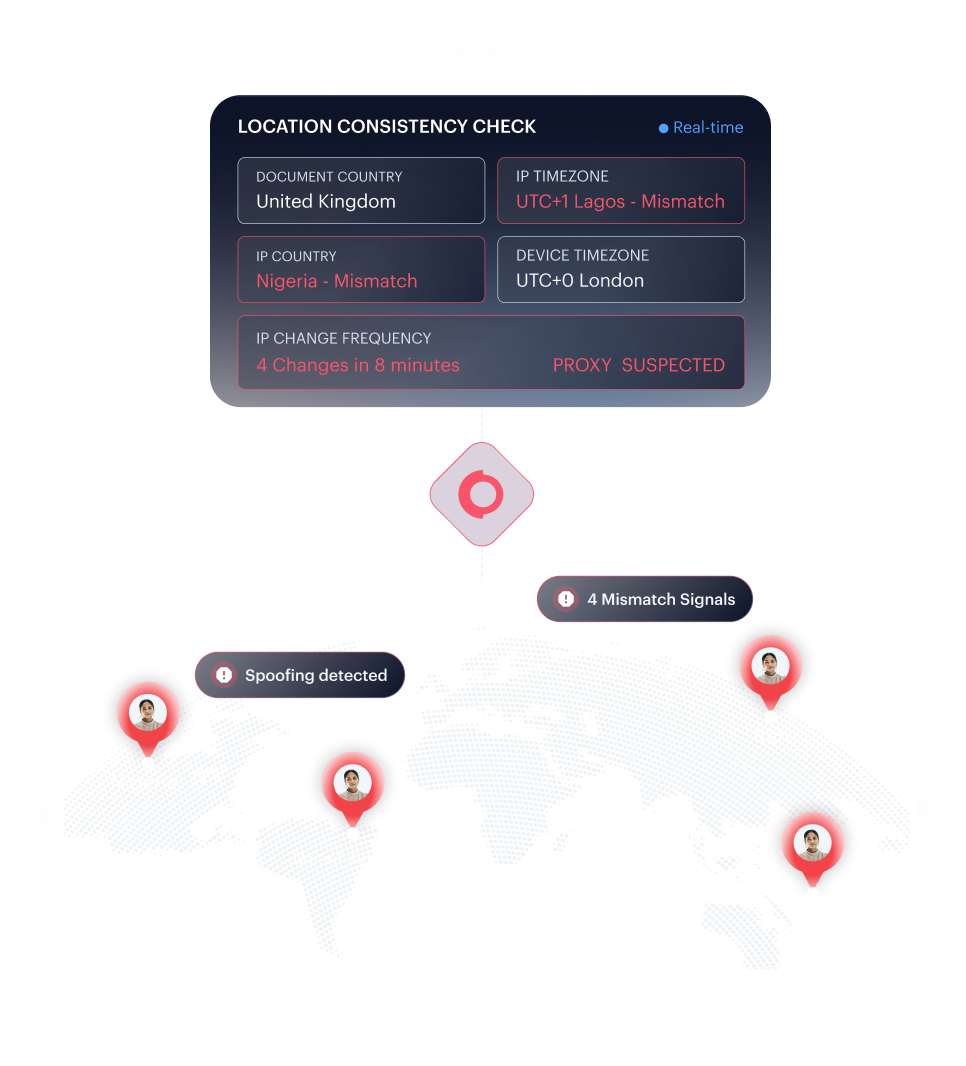
Location and Behaviour Consistency Checks
A document claiming one country with an IP from another signals location spoofing. Shufti compares document country against IP country to identify mismatch patterns.
Timezone inconsistency and rapid IP changes indicate proxy rotation and session manipulation. Shufti checks timezone against IP and monitors IP change frequency as consistency signals.
Blanket rules that flag location changes block users who are simply travelling or switching networks. Shufti's consistency checks detect spoofing and manipulation without blocking genuine users.
INDUSTRY COVERAGE
Device Intelligence for Every Industry Fraud Targets
Banned Sellers Returning Behind New Accounts
Banned sellers re-register new accounts from the same device to continue operating. Shufti keeps device history connected across new account registrations, exposing repeat offenders before they re-enter the marketplace.

Frequently Asked Questions
What does device fingerprinting return in the API response?
Five things: a Visitor Fingerprint ID (a stable ID for the device), a Threat Level (an overall risk score), network and location details (IP, ASN, routing), evasion signals (VPN, TOR, emulator, jailbreak, browser tampering), and stability signals (IP changes, country and timezone mismatches).
How does device fingerprinting differ from cookie-based tracking?
Cookies are stored on the user's device and can be deleted. Device fingerprints are stored on Shufti's servers and cannot be cleared by the user. The fingerprint stays the same even after cookies are wiped, private browsing is used, or the network changes.
What is the difference between device fingerprinting and behavioural biometrics?
Device fingerprinting asks: is this a trusted device and connection? Behavioural biometrics asks: is the person behind it acting like a real user? One checks the device. The other checks the behaviour. Both together give a more complete picture.
Where in a verification flow does device fingerprinting apply?
At login, account recovery, payouts, withdrawals, sign-up, and marketplace onboarding. Anywhere device consistency and network integrity matter to the risk decision.
What do teams typically do with the signals?
Three actions. Allow when everything looks normal and the Threat Level is low. Step up authentication when risk rises — VPN detected, new device, IP mismatch. Block or review when strong evasion combinations appear, such as TOR with an emulator or a datacenter IP with automation signals.
Is device fingerprinting GDPR-compliant?
Yes. Fraud prevention qualifies as a legitimate interest under GDPR Article 6(1)(f), confirmed by Recital 47. Individual consent is not required. Businesses should document this basis and disclose it in their privacy policy.
How does device fingerprinting work alongside behavioural biometrics?
Device fingerprinting sets the risk context. Behavioural biometrics checks what the person is doing inside the session. A clean device with unusual behaviour triggers a biometric step-up. A flagged device with normal behaviour triggers a network review. Using both closes the gaps either misses alone.
Stop Fraudsters Before They Reset the Trail
Detect returning devices, masked networks, evasion tools, and high-risk sessions before they reach payouts, withdrawals, or repeat account creation.





