Fraud Network Detection
See the ring,
not just the account
Shufti’s AI-powered Fraud Network Detection exposes organised rings the moment they touch your platform, not after the loss lands. Biometric de-duplication, device clustering, and real-time AML surveillance work as one. Government-validated. Live in days.
Live
in days
Integration
Cloud, on-prem, or hybrid
10M+ face
de-duplication at scale
Seen Once Blocked Everywhere
Where Fraud Networks Strike

1. Onboarding
Rings seed dozens of accounts at once, AI-generated faces, fabricated documents, device farms. Invisible to per-account IDV.

2. Login
Stolen credentials and session cookies let nodes authenticate silently. Ring volume is invisibly checked account by account.

3. Action
Once trusted, the ring strikes simultaneously, bonus abuse, loan stacking, and APP fraud, before a single rule fires.

4. Monitoring
Proceeds layer through mule chains in hops. A newly listed ring member triggers no alert without continuous monitoring.
FOUR ATTACK CLASSES. FOUR PLAYS.
How Shufti Stops It
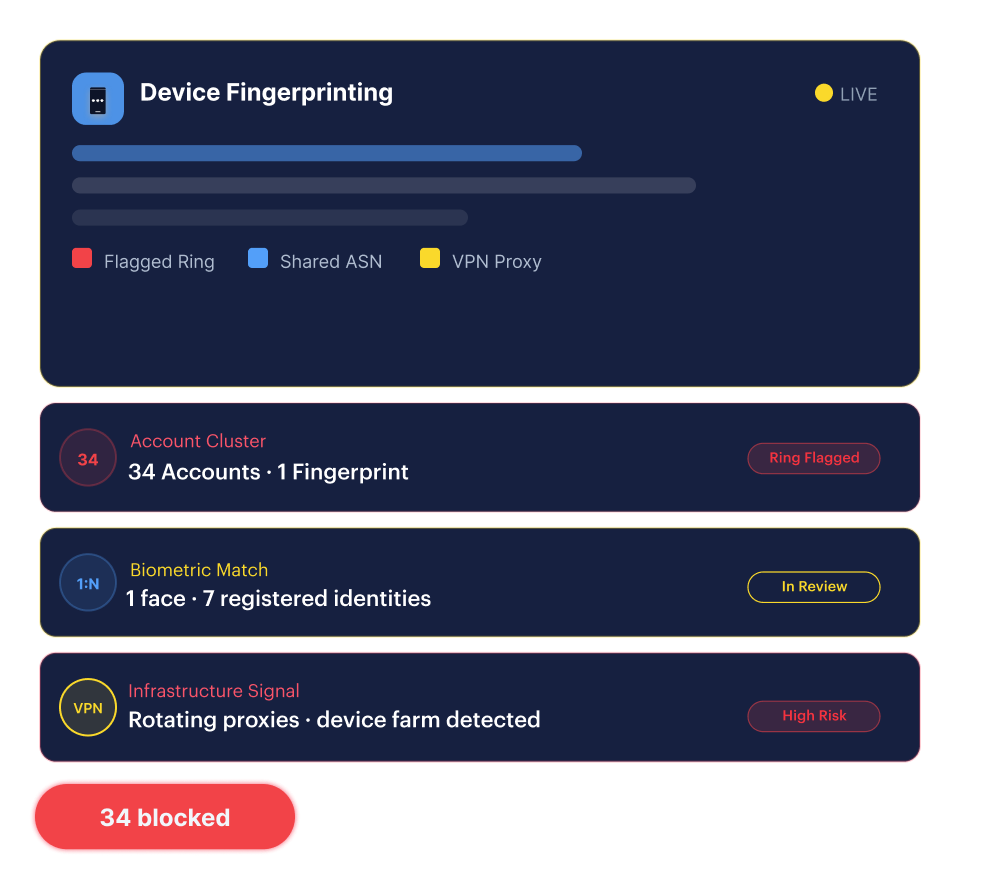
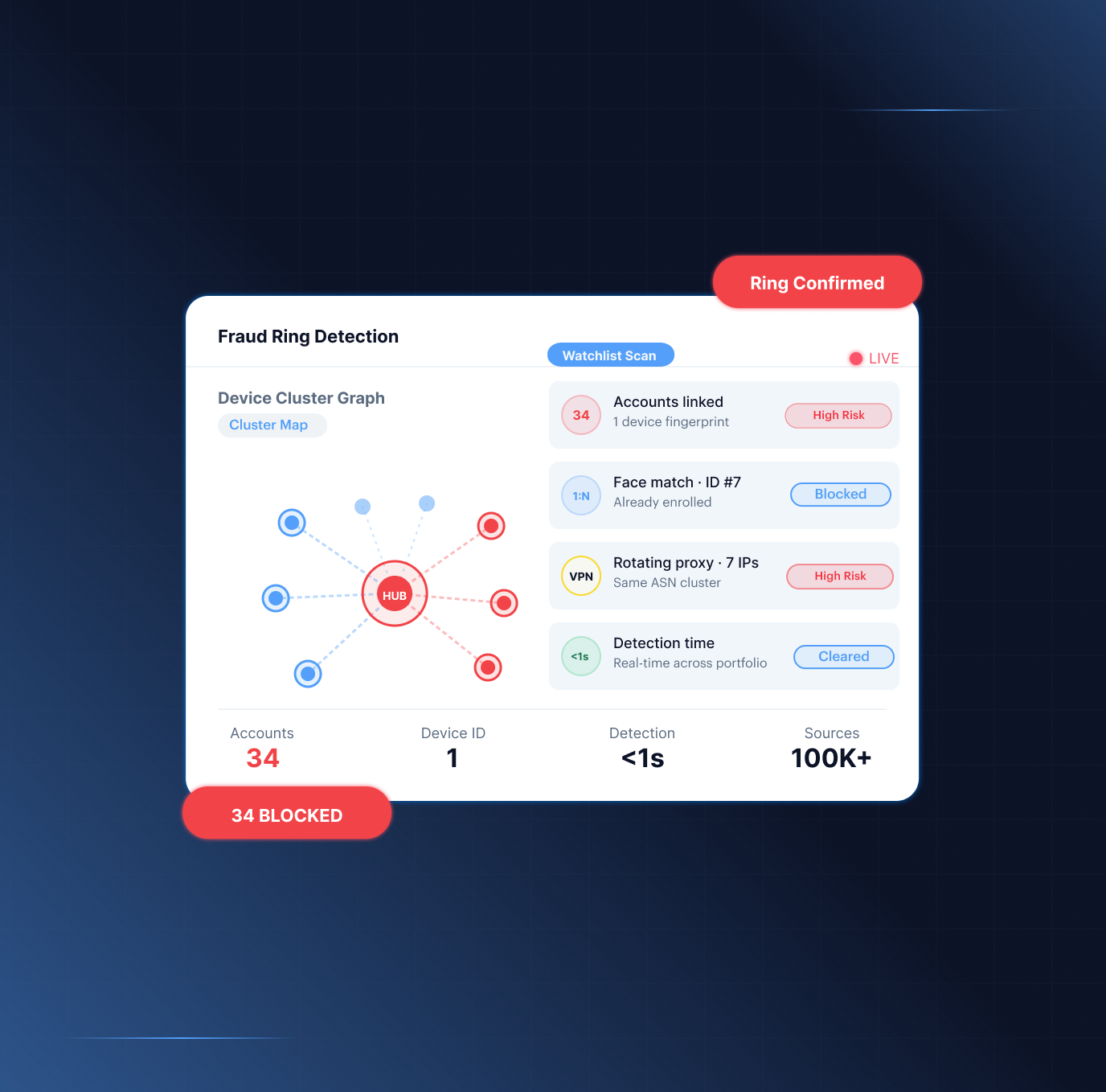
Multi-Account Rings
When a ring registers dozens of accounts using device farms, rotating proxies, and VPN infrastructure.
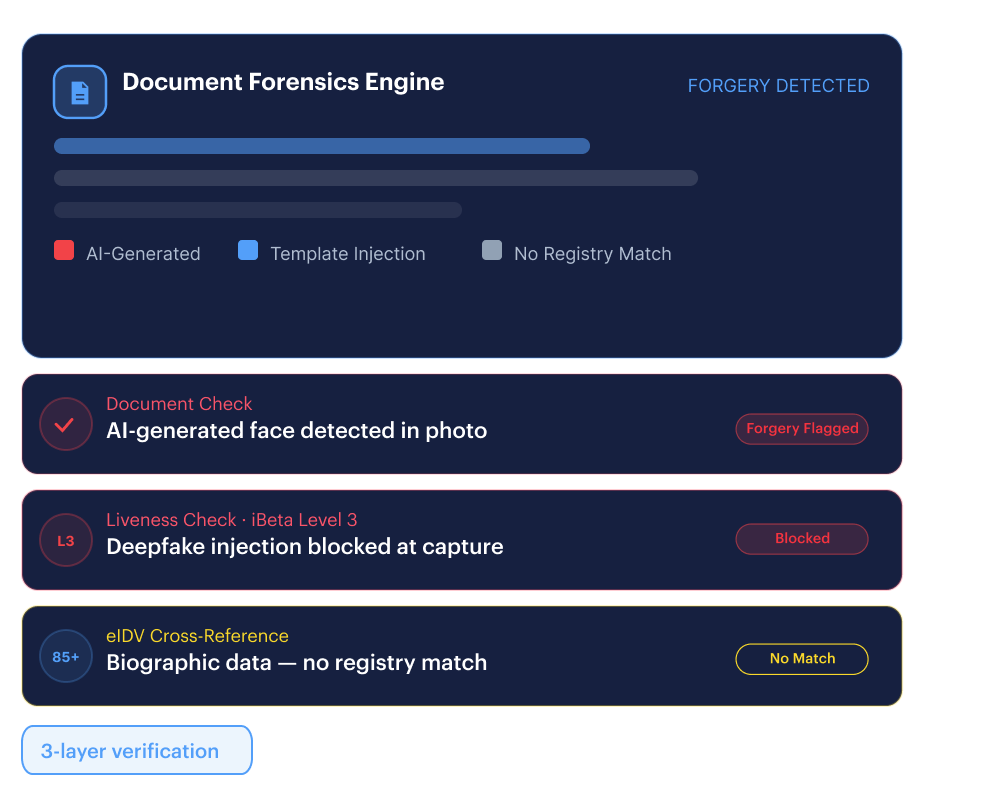
Synthetic Identity Networks
When rings deploy AI-generated faces and fabricated documents.
- Document Verification’s forensic stack catches AI-generated IDs and template-injection attacks before the document passes.
- Face Verification’s iBeta Level 3 liveness kills deepfake injection at capture, not after a decision.
- eIDV cross-references biographic data against authoritative registries in 85+ countries.
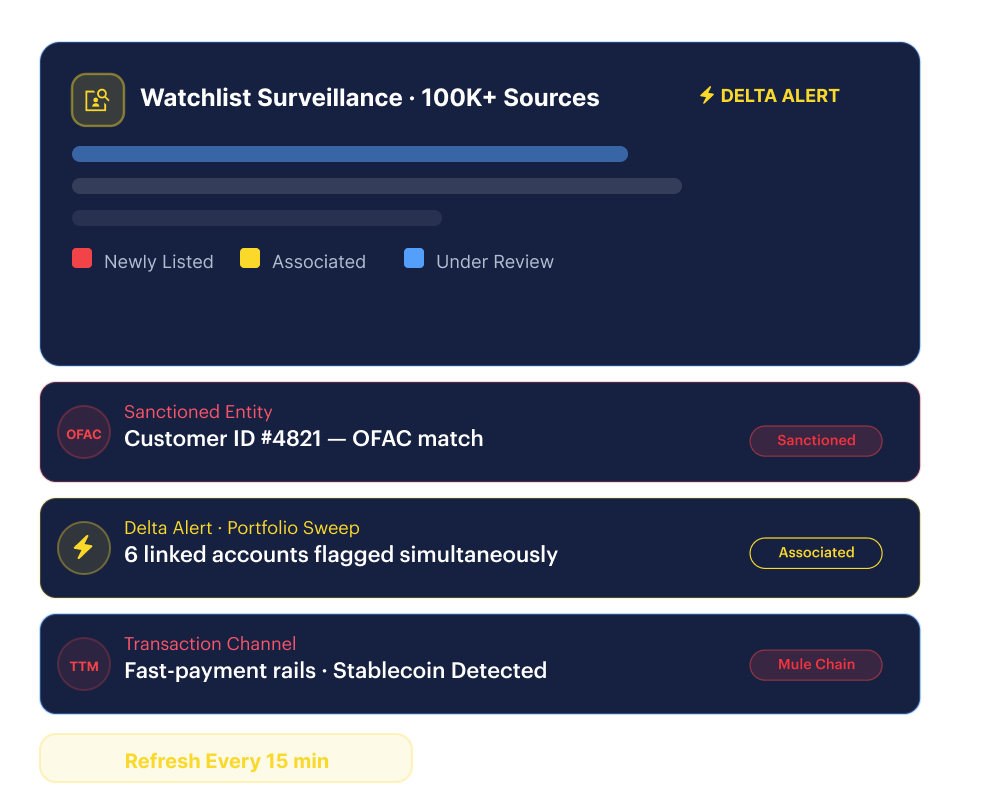
Money Mule Chains
When ring proceeds move through layered mule accounts on fast-payment rails and stable coin channels.
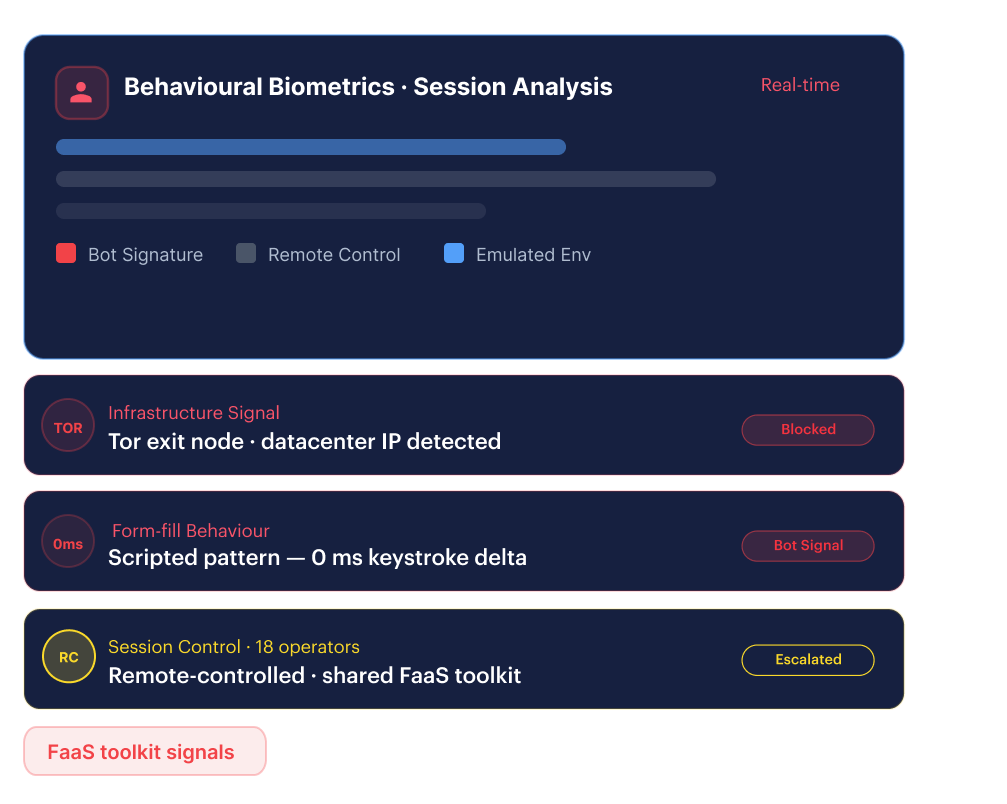
Fraud-as-a-Service Infrastructure
When criminal platforms sell phishing kits and ATO toolkits to distributed operators running coordinated attacks.
Industry Playbook
Fraud networks hit every sector differently
Mule chains are your liability
Stop APP fraud rings from using your platform as a layering hop, detect shared-device mule clusters in your portfolio, and fire AML delta alerts the moment a ring member is listed before the next transfer executes.
The Broader Platform
Shufti covers the full attack surface

What We Do
The core workflows Shufti delivers — verifying customers at onboarding and monitoring them throughout the full relationship.
-
Onboarding
AI-powered document forensics, biometric verification, and real-time AML screening in one adaptive flow, verifying genuine customers while blocking synthetic identities at the door.
-
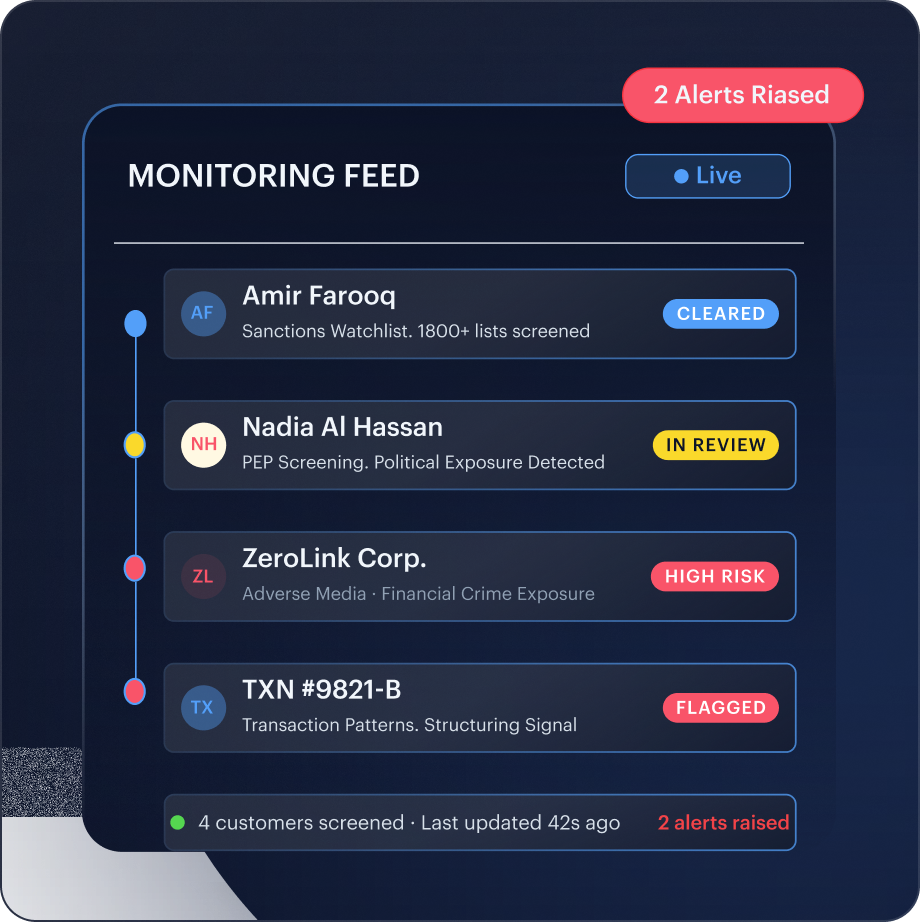
Ongoing Monitoring
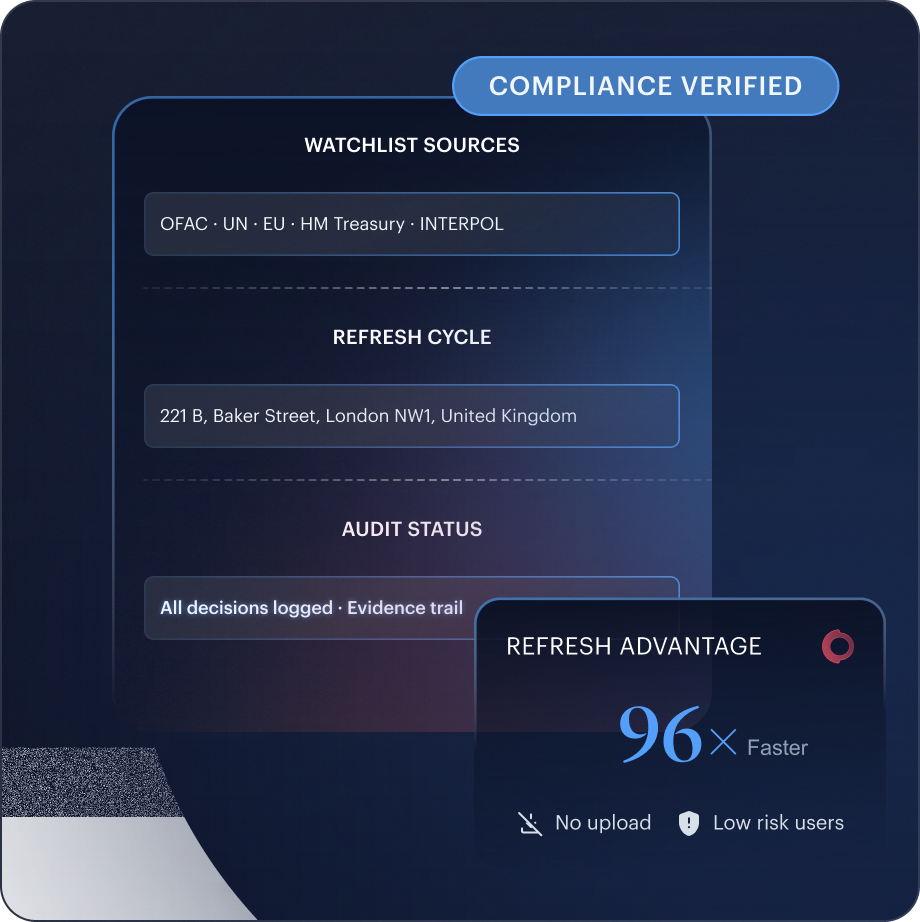
Continuous screening against 1,700+ sanctions, PEP, and adverse media sources. Customer records rechecked within minutes of a list update, not at the next periodic review.



What We Solve
The compliance and identity challenges regulated businesses face — KYC, KYB, fraud, age, workforce, and investor verification, resolved without stitching vendors together.
-
Identity Verification
Document forensics, iBeta-certified biometric liveness, NFC chip verification, and AML screening through one API. Authenticate customers across 250+ regions from a single integration.
-
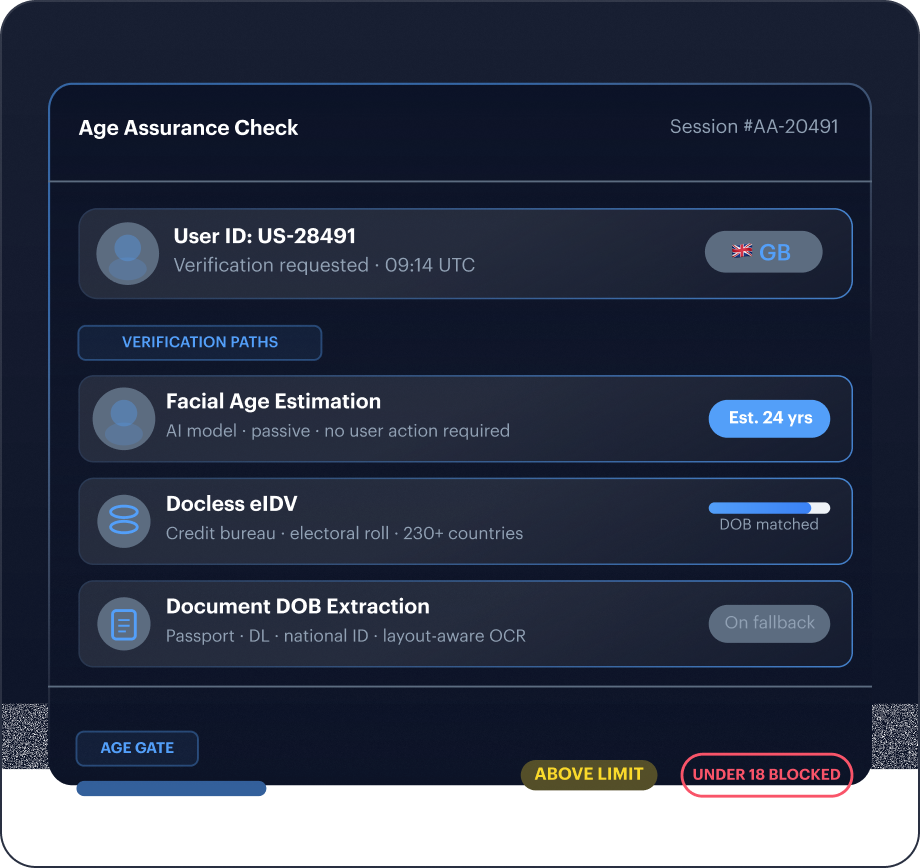
Age Assurance
Three verification paths, facial estimation, docless eIDV, and document DOB extraction, in one flow. Stop underage access without driving away legitimate users.
-
KYC
One configurable flow for document verification, face verification, eIDV, NFC, address verification, and AML screening. One integration, one audit trail, no vendor stitching.
-
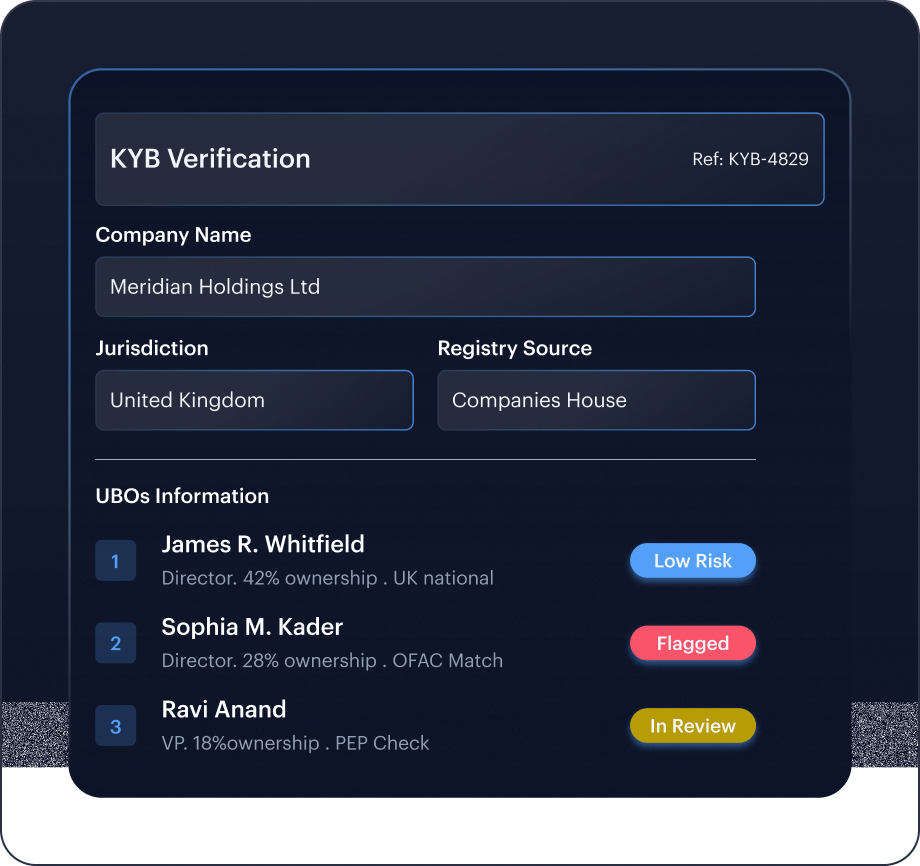
KYB
Live registry checks across 240+ official sources, complete UBO due diligence, and AML screening in one flow.
-
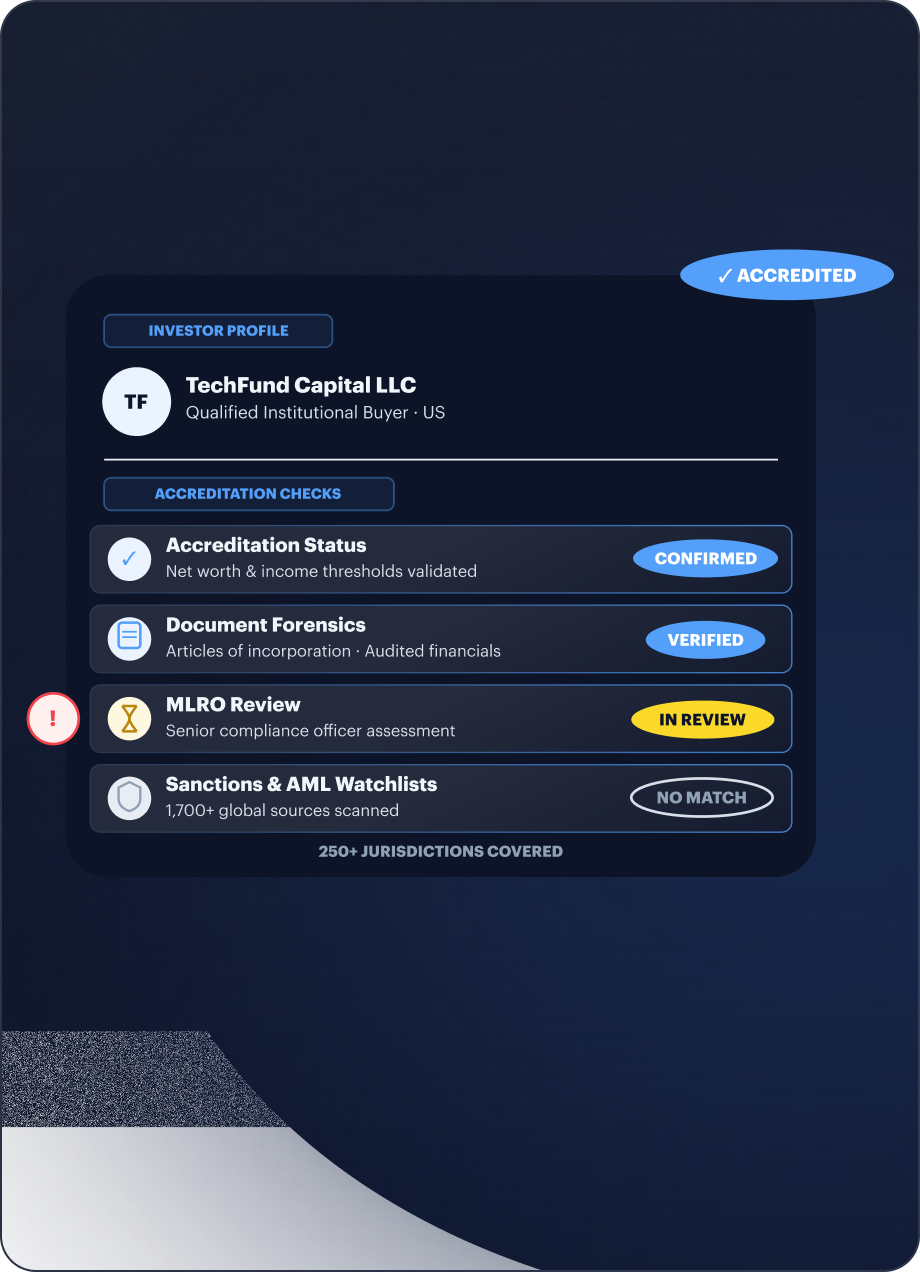
KYI
Accreditation validation, document forensics, and MLRO-backed review in one investor verification flow. Meet accredited-investor mandates across 250+ jurisdictions without additional vendors.
-
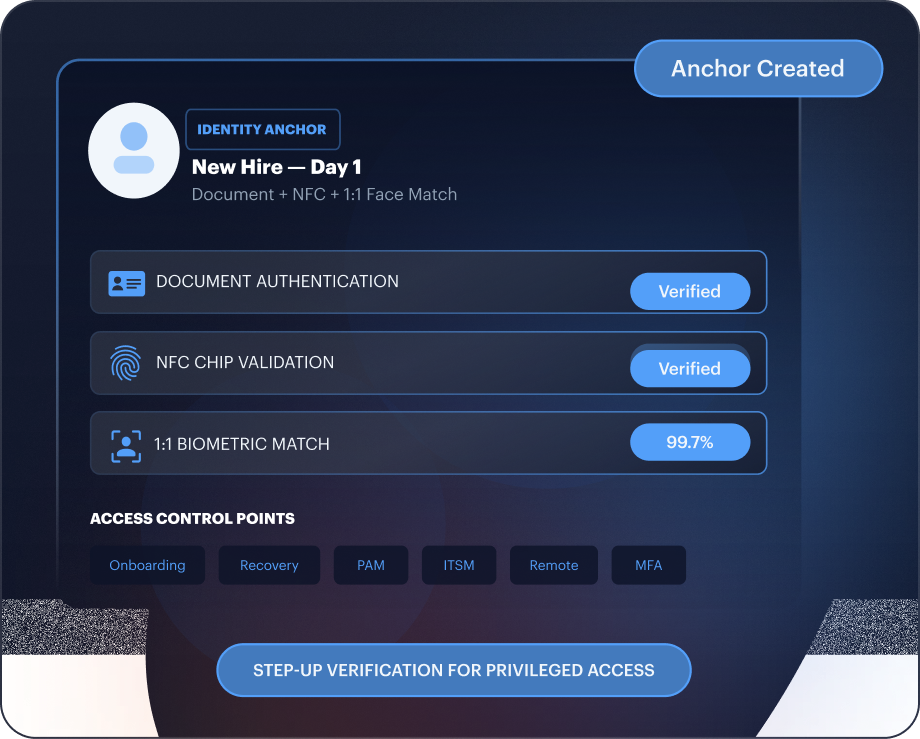
Workforce IAM
Verified identity at every access control point, onboarding, account recovery, privileged access, and MFA re-enrolment, without replacing your existing IAM stack.
-
Candidate Verification
Document forensics, biometric matching, and enhanced due diligence inside your hiring pipeline. Catch fraudulent applicants and AI-generated candidates at application stage, not after offer.



Business Outcome
The results Shufti delivers at scale, staying compliant, stopping fraud, building user trust, and expanding globally from a single integration.
-
Compliance
Automated KYC, KYB, and AML across 250+ regions. Audit-ready evidence trails for every decision. Sanctions refreshed every 15 minutes — 96x faster than industry standard.
-
Fraud Prevention
40+ ensemble AI models across the full customer lifecycle. Independent testing: 8 of 8 document forgeries detected where legacy stacks caught zero.
-
Trust & Safety
Verify users, sellers, workers, and businesses before risk reaches your platform. One trust layer across marketplaces, gaming, gig economy, fintech, and age-restricted services.
-
Global Expansion
230+ countries, 10,000+ document types, 150+ languages. One API with jurisdiction-configurable workflows and regional cloud infrastructure across EU, UK, US, APAC, and MENA.
BUILT FOR YOUR TEAM
One platform. Every stakeholder
Compliance Officer
Regulator-defensible audit trail at every account-change event.
Product Manager
0.75s passive biometric. Legitimate pass rates up, fraud acceptance down. Live in a sprint.
Developer
REST API, mobile SDKs, and sandbox access. First verification call within hours of integration start.
Fraud Analyst
Signal-level Risk Score with full breakdown. >70% fraud reduction without growing the review queue.

Shufti Is A Top Solution Serving Global Clients
Shufti delivers the widest global coverage with its own technology, ensuring flexibility, innovation, and stronger Extended IDV capabilities than regional or orchestrated competitors.
Download Full Report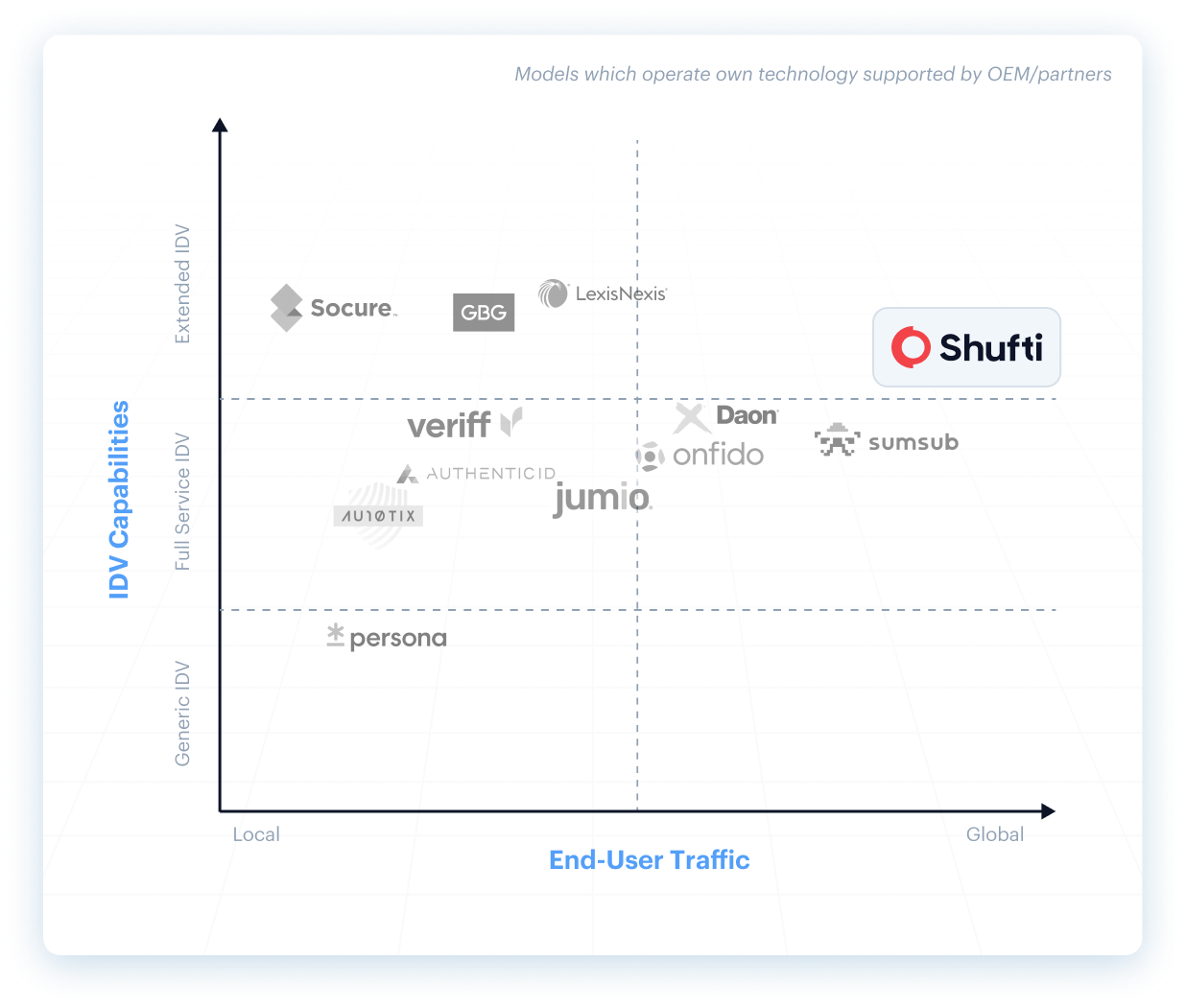
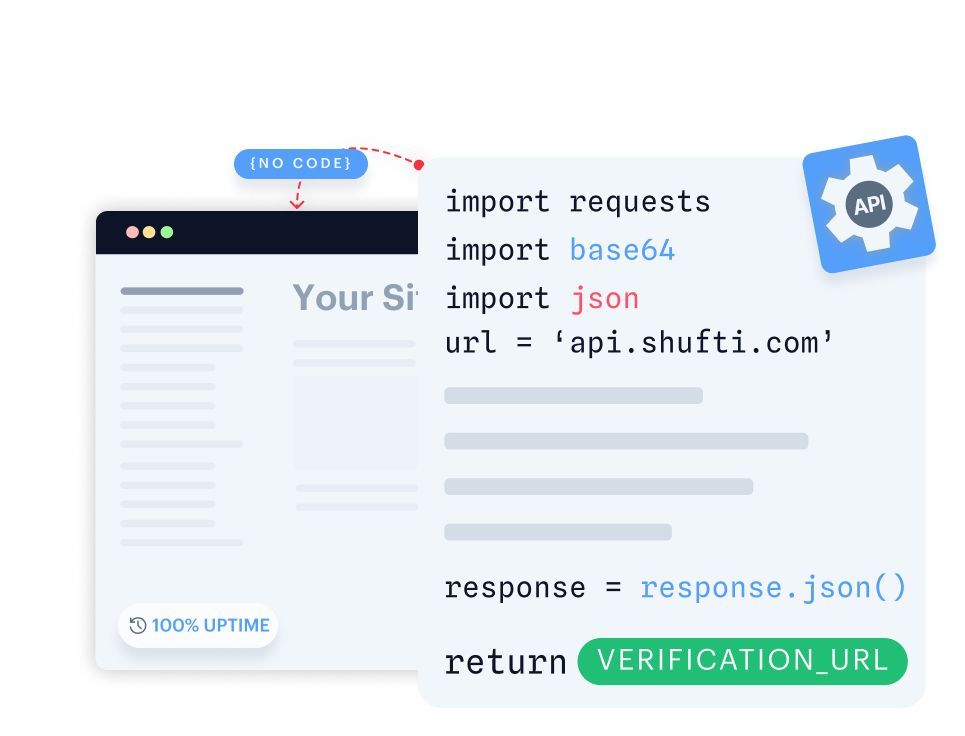
Single API, Seamless Integration
Build fully customisable verification flows with seamless backend integration.
- Gain full control by customising verification flows end-to-end.
- Integrate seamlessly with your backend for quick implementation.
- Design flexible verification journeys tailored to your users.
Launch a native verification experience in your mobile app within minutes.
- Launch native verification within minutes on iOS or Android.
- Use ready-made UI with camera, capture, and real-time feedback.
- Customise flows to fit seamlessly into your mobile app.

Run Shufti within your own identical-capability infrastructure for maximum data control and privacy.
- Keep all sensitive information in-house to meet strict governance and data residency requirements.
- Keep sensitive information fully private and secure in-house.
- Deploy in highly regulated sectors without compromising compliance.
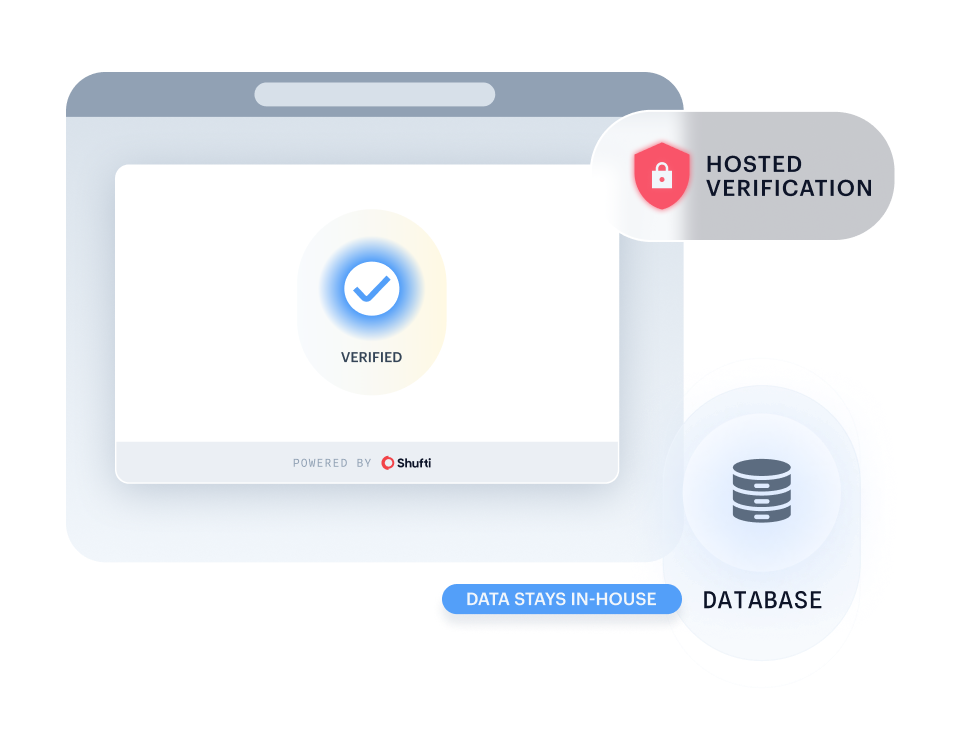
Quickly launch identity verification through a secure, customisable web link, no code required. Learn more.
- Start verifying users instantly with a no-code setup.
- Deliver a consistent identity experience via a link or embedded iframe.
- Deploy quickly via a secure link or embedded iframe.

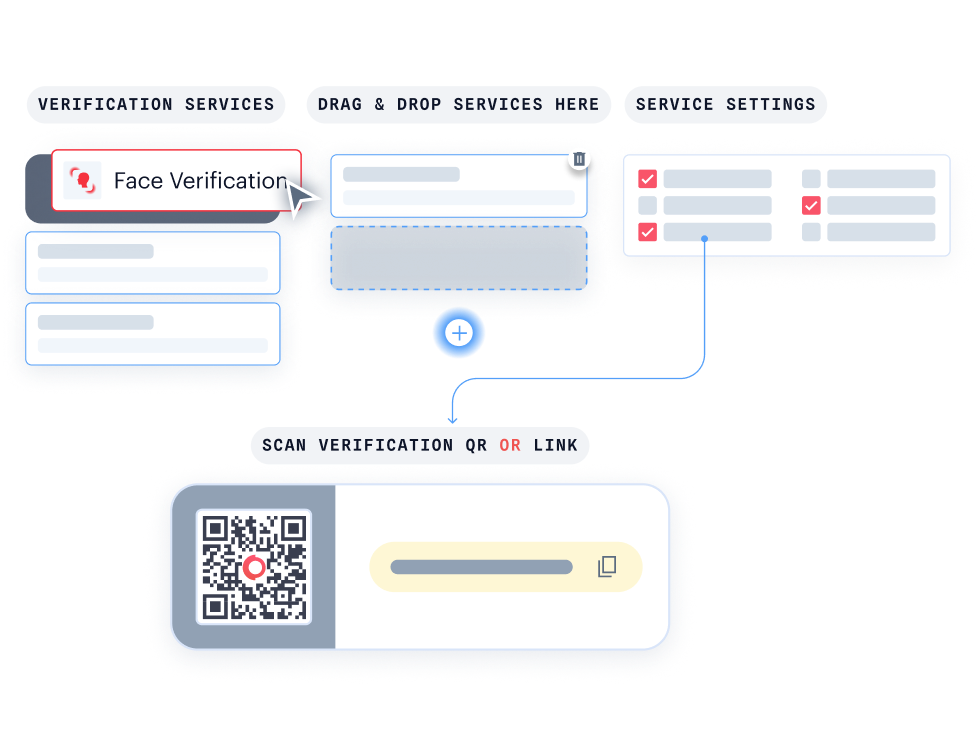
With KYC Journey Builder, create personalised verification journeys without writing a single line of code.
- Customise your journey effortlessly with drag-and-drop functionality.
- Instantly see how your verification flow looks for your users.
- Easily connect with Hosted Verification for a consistent, branded experience.
Your Go-To for KYC/AML & Fraud
Resources

18 September, 2025
7 minutes read
Shufti Overview: Duplicate Account Detection
Prevent duplicate accounts and fraud with AI-powered Face Mapping and FAST ID technology for streamlined user verification.
Case Study
Frequently Asked Questions
What is fraud network detection?
Fraud network detection is the discipline of identifying organised rings, not just individual bad actors, by analysing cross-account signals: shared device fingerprints, biometric re-use across multiple identities, common IP infrastructure, and co-ordinated transaction velocity. Single-account controls miss the ring. Network-level analysis catches it.
How does AI-powered Fraud Network Detection work differently from standard fraud screening?
Standard screening inspects each account in isolation. AI-powered Fraud Network Detection analyses signal patterns across your entire customer base simultaneously, biometric 1:N matching, device clustering, document template propagation, exposing the ring structure that per-account checks never see.
My existing fraud tools flag individual accounts. Why isn’t that enough?
Each node in a fraud ring is designed to look clean individually. Low velocity, plausible identity, fresh device. The pattern only surfaces at the network level. By the time a single account trips a rule, the ring has already executed across dozens of others.
How fast can Shufti deploy fraud network prevention?
Shufti’s fraud network prevention capabilities go live in days, not months. Pre-built APIs, SDKs, and a no-code Journey Builder integrate alongside your existing fraud stack, no rip-and-replace. Most clients have network detection active inside a single sprint.
Does Shufti’s fraud network detection work on existing customers, or only new onboarding?
Both. AML Screening’s continuous monitoring watches your live customer portfolio around the clock. The moment a network member appears on a sanctions list or watchlist, a delta alert fires across every associated account, including accounts onboarded months or years ago.
Where is biometric and identity data stored, and who owns it?
You own your customer data. Shufti supports cloud, on-prem, and hybrid deployments. Biometric templates stay in your jurisdiction or your own infrastructure where required. GDPR, CCPA, and SOC 2 Type II compliant by default.
See the ring,
not just the account
Fraud networks scale fast. So does Shufti. Deploy in days.