A Guide to Evaluating TRUST in Identity Verification Solutions

The TRUST Framework Compliance Teams Need Before Vendor Selection
Why “Compliant” Doesn’t Mean “Trusted”
Many compliance teams assume that meeting KYC requirements automatically makes an identity verification solution reliable. This assumption creates risk.
Fraud schemes today do not bypass compliant systems; they exploit gaps within them. A solution may comply with regulatory requirements yet still fail to detect sophisticated identity fraud.
So what does a rigorous evaluation actually look like? A stronger comparison rests on five pillars.
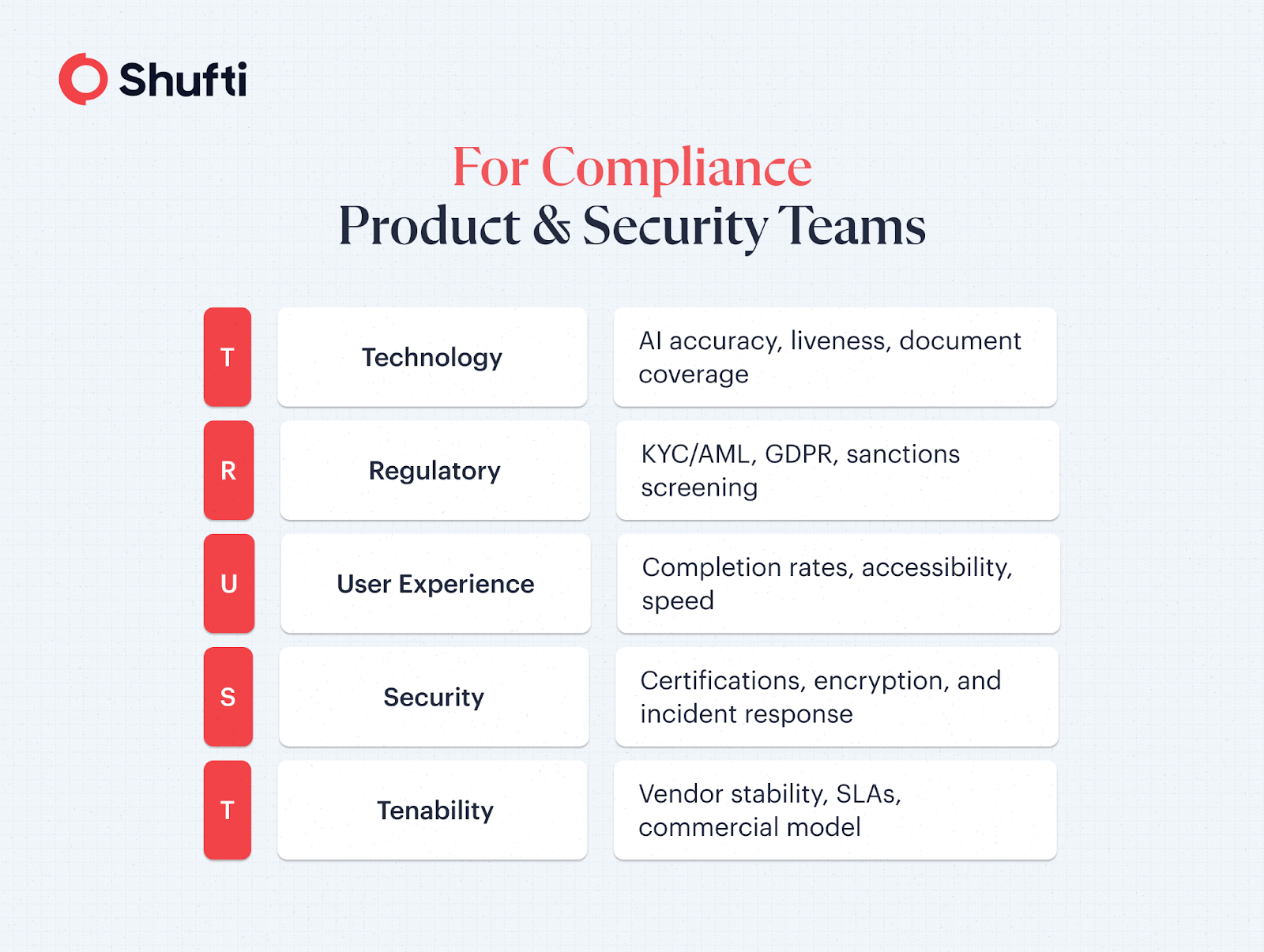
First Pillar — T: Technology
Can it actually verify people accurately?
The Technology pillar assesses the core AI and biometric capabilities of the solution and how accurately it recognises documents, detects presentation attacks, and matches faces. This is the main engine of the solution, and everything else depends on getting it right.
Vendor evaluations often rely on a single headline metric such as “98.5% accuracy.” Accuracy without context provides limited value. Vendors should specify the way accuracy should be determined, in which types of documents, and at what levels.
When these metrics lack clarity, it usually suggests a lack of transparency.
The False Accept Rate (FAR) and False Reject Rate (FRR) are the most important metrics to consider because they reveal the number of times the system is willing to admit the fraudsters and the number of times it refuses the right customer, respectively. These two metrics are closely linked and affect each other. When one is reduced, it often leads to an increase in the other. The right balance depends on the risk profile, and one needs to know where the vendor sits before deployment, not after.
What to evaluate:
- Document recognition accuracy and global coverage for national IDs, passports and DLs
- Active and passive liveness detection and presentation attack detection (iBETA PAD Level 2 certified)
- Third-party validated FAR and FRR benchmarks at operational thresholds
- OCR precision under varied lighting and document quality, and NFC chip reading
- Transparent AI models with advanced notification of decision-impacting updates
Second Pillar — R: Regulatory
Does it keep companies on the right side of the law, everywhere they operate?
A technically advanced solution that creates compliance gaps introduces regulatory risk. This aspect tends to depict the disjuncture between what providers claim and what can be proved.
The term “GDPR compliant” is one that almost all vendors advertise. But the question is, do their Data Processing Agreement, data residency practices, and right-to-erase practices really pass the test?
The consequences are substantial. Failure to comply with AML may result in fines of hundreds of millions, revocation of the licence, and, in severe instances, criminal responsibility on behalf of individual officers.
Key evaluation criteria:
- KYC/AML coverage mapped to the specific regulatory footprint, not a generic global figure
- Geographical restrictions can be imposed by contractually specified data residency controls, which require biometric templates to be stored outside a specific area
- Continuous real-time sanctions and politically exposed persons (PEPs) screening and monitoring, not only with the registration by a one-time check
- Identity Assurance Level (IAL) 2 and 3 under the NIST framework for regulated industries
- Audit trails that are tamper-proof, have a configurable retention time, and can be deleted on demand.
Third Pillar — U: User Experience
Will the customers actually complete it?
The most advanced verification technology is of no use if users give it up. And still, UX is never weighted up enough in the study where compliance and security teams prevail.
An operational measure of this impact is by conversion metrics. Any percentage of completion rate lost during onboarding becomes irreversible revenue leakage. A company making 100,000 verifications a year, with 80% completion rate with current vendors, can onboard 8,000 more customers with a vendor achieving 88% successful verifications, before accounting for the lifetime value of those customers.
Low-friction verification flows with 85% or above successful completion are considered the industry standard. High user dropoff during verification can be due to a poorly guided workflow and friction rather than genuine fraud.
Assessment factors:
- Verified completion rates by industry (not blended averages)
- Capability to handle mobile-led capture quality with entry-level devices, mixed lighting, and deteriorated documents with user-guided workflows and auto-capture to reduce shutter error
- The accessibility standards of WCAG 2.1 AA are mandatory in many markets; many are not merely a nice-to-have
- Multilingual and localisation support (UI and error messaging support in local language)
- The customer expects a shorter time for a decision. When onboarding is correctly automated, it can significantly reduce onboarding time from minutes to seconds
Fourth Pillar — S: Security
Vendors’ security posture is your exposure.
The businesses trust biometric information and identity documents of the customers for identity verification solutions. The regulatory liability directly depends on the security posture of the vendor. Such capabilities should be underpinned with separately verified security controls.
Biometric data is a special category according to GDPR and most similar laws. It is categorized as very sensitive personal information. Biometric data cannot be changed like passwords once it is compromised. The breach of solutions that reveal biometric templates has long-term effects on the lives of the people affected, as well as material effects on the affected population.
What to evaluate:
- Make sure businesses hold an up-to-date SOC 2 Type II certification, based on an audit conducted within the last 1 year. Make sure to read the exceptions section thoroughly, not just the executive summary.
- AES-256 encryption of data at rest and transmission using TLS 1.3 are used to protect data. Moreover, the biometric templates are registered in the form of mathematical vectors rather than raw images.
- Carry out third-party penetration testing on an annual basis, and consider sharing a summary of the results.
- Notification of contractual breach obligations, GDPR 72-hour deadline should be clearly stated in the Data Processing Agreement.
Fifth Pillar — T: Tenability
Will this partnership last?
Identity verification is infrastructure. Switching providers mid-scale is harmful, costly, and, when poorly timed, is a compliance risk in itself. The switching costs are so great that long-term fitness is worth as much examination as short-term ability.
The risk of tenability usually develops over time and cannot be perceived until dependency is created over a long period. This involves unpredictably scaling pricing, non-business need product roadmaps, and alterations to key account management. A key contact who leaves. At that stage, it is both operationally and financially challenging to change providers.
Key evaluation criteria:
- Uptime Service Level Agreement (SLA) of 99.9% or higher, with a multi-region failover and a well-tested disaster recovery plan that is not supported by mere promotional claims but supported by enforceable contractual penalties.
- The cost of ownership has been estimated at two, five, and ten times the current volume, including base verification, AML screening, continual monitoring, and manual review escalations.
- API versioning and deprecation policies with clear timelines for changes
- Significant customer success and compliance services with established response SLAs.
Shufti is Built to Support Growth, Not Just Immediate Verification Needs
Identity verification solutions that lack transparency, regulatory alignment, and long-term reliability often create more problems than they solve. Businesses operating across complex markets need a provider that supports accurate decisioning, defensible data control, and consistent performance at scale.
Shufti’s identity verification addresses these challenges through a unified identity, fraud, and compliance platform built on its TRUST framework, offering transparent decisioning, sovereign data control, and consistent global performance.
Businesses looking to improve verification outcomes and reduce multi-vendor friction can explore Shufti’s capabilities by requesting a demo.

 Explore Now
Explore Now