Identity Verification with Liveness Detection: The Key to Preventing Spoofing Attacks

Spoofing attacks are not limited to just emails and fake websites. Hackers and cybercriminals have now employed more advanced forms of technology, such as AI-generated deepfakes and system rats, to access users’ crucial information. A typical spoof attack involves messages and emails that are designed to look like they are sent from trusted and legitimate entities. The attackers try to trick users into clicking on a malicious link or providing confidential information. This type of attack is highly effective and challenging to detect, which is why companies need to harness the power of robust identity verification solutions.
According to a CAIDA study, between 2015-17, there were 21 million attacks on about 6.3 million users, accounting for almost 30,000 spoofing attacks daily. Spoofing attacks have seen a significant surge because of their easy accessibility.
What is Liveness Detection? A Brief Overview
Liveness detection is conducting a verification test on an individual to verify their identity and determine their real identity; the demand for these solutions has seen a massive surge in the past few years. The facial recognition market, worth approximately $4 billion in 2020, has seen continuous and steady year-on-year growth, which is forecasted to continue. 3D facial liveness detection helps companies detect fake representations and create a more secure online business environment.
-
Active Liveness Detection
Active liveness detection is the part that prompts an individual to perform specific actions like blinking, waving their hand, or tilting their head. This aids in liveness detection by detecting fake representations as a generated interface won’t be able to perform these actions unless it’s pre-programmed. A robust anti-spoofing solution has very uncertain active liveness detection requirements, making it nearly impossible for fraudsters to bypass them.
-
Passive Liveness Detection
Passive liveness detection is a verification process done in the background, without the user’s knowledge. This method has an advantage over active liveness detection, as it prevents fraudsters from preparing for the test. A passive detection test scans biometric features such as skin patterns, blink rate, blood flow, and other involuntary movements. Skin contours and shadows can sometimes also be crucial in detecting a deepfake.
3D Liveness detection is a technology that helps improve the accuracy of biometric facial recognition. The most effective application of these systems is during the onboarding process, which allows companies to easily conduct effective background checks. Additionally, significant high-volume transactions also require a verification process to be conducted. Primarily, this is because fake identities are often used during, money laundering and terrorist financing, which can be eliminated with the use of liveness detection.
Common Types of Facial Spoofing
A study on 2D liveness detection techniques found that non-rigid motion analysis resulted in an accuracy of 90%, face-background consistency analysis resulted in an accuracy of 97.50%, and image banding analysis also resulted in an accuracy of 97.50%. All the mechanisms that impersonate the real biometric features of a real human without their consent are examples of spoofing. Facial spoofing can be divided into the following representations:
- One of the most common types of face spoofing is a 2D static attack. These are high-quality facial impersonations on a flat canvas.
- 2D dynamic spoof attacks involve arranging multiple high-quality impersonated photos in a predetermined sequence. These can be used to recreate the basic challenge-response requirements.
- 3D digital duplicates and avatars are a more advanced form of face spoofing. They are primarily used to target high-ticket entities with advanced security protocols. They are primarily built on the principle of deep-learning.
- 3D static attacks comprise a major chunk of modern high-ticket deepfake attacks. These can involve 3D prints, wax heads, or digitally created high-resolution avatars.
- 3D dynamic attacks are primarily based on real-world applications. These utilize silicone masks, holograms, and micro-sculpted biometric facial masks.
Eliminating Facial Spoofing with Liveness Detection
Facial spoofing and deepfake fraud fall into the same category and fraudsters can utilize these methods to commit a variety of crimes by impersonating legitimate entities. When a facial spoof attack targets an individual posing as an actual entity, it can extract crucial financial, personal, and identity information. This information can then be used to construct more fake identities, ultimately creating a series of deepfakes just at the hands of a single individual. Facial spoofing detection, aided by liveness detection, can help companies prevent these attempts. Liveness detection technology can detect whether or not a person is real or fake by analyzing their behavior and facial expressions. This technology uses a multitude of techniques to help prevent face spoofing.
-
Challenge and Response
A robust 3D facial liveness detection system presents entities with a series of challenges they must complete. A pre-programmed deep fake of a deepfake video can be spotted this way, ultimately safeguarding business processes. The primary function of this aspect of liveness detection is to prevent low-level 2D deepfake representations that are primarily utilized by day-to-day scammers targeting laymen.
-
Depth and Motion Perception
This aspect of a 3D liveness check is used to combat more advanced deepfake technologies. These fraudsters mainly target businesses and enterprises that are functioning on a large scale. Their primary focus is infiltrating the company’s databases and committing crimes using the gathered data. Depth and motion perception are used to track the most subtle changes that aid businesses in detecting deepfakes.
-
AL and ML Algorithms
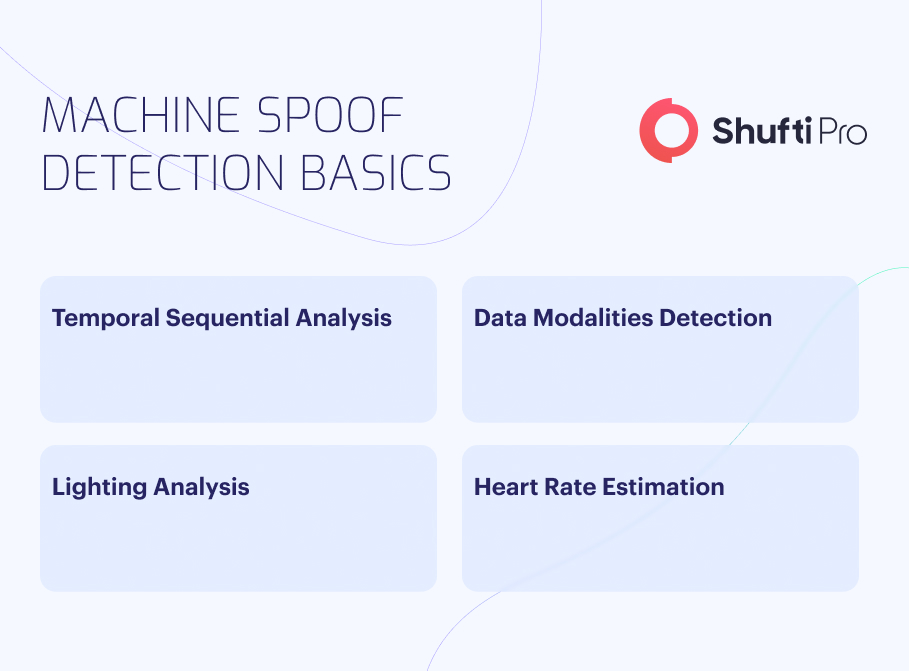
Artificial Intelligence (AI) and Machine Learning (ML) have been crucial in advancing the 3D liveness check ecosystem. These algorithms aid the liveness detection system in improving itself, ultimately improving efficiency. These algorithms keep track of the previously detected anomalies and use that data to prevent similar attacks in the future. Due to machine learning, facial recognition spoofing systems now have the advantage of detecting a multitude of facial spoofing attempts and eliminating them effectively.
Facial Anti-Spoofing with Shufti’s Liveness Detection
Shufti provides businesses with a suite of IDV solutions. Our biometric facial verification solutions are integrated with robust liveness detection measures that allow companies to effectively identify deepfakes of all types and eliminate them promptly. Our liveness detection features can detect the most subtle changes, such as shadow displacements and skin contour shifts, that can eliminate even the most high-quality deepfakes.
To ensure that no aspect is left unchecked, our liveness detection solution further equips companies with distortion analysis, 3D sensory techniques, and skin texture analysis. Companies can streamline their facial biometric verification journey with a vast array of security protocols. Our solutions make facial authentication convenient for both businesses and users by eliminating the need for physical presence and ensuring robust facial verification.
Our IDV experts are always available to aid businesses with their verification processes. By equipping robust facial recognition spoofing with expert human insight, we have created the perfect 3D liveness detection process. Expert human insight paired with the accuracy of AI-integrated solutions provides the top of line security to businesses.












