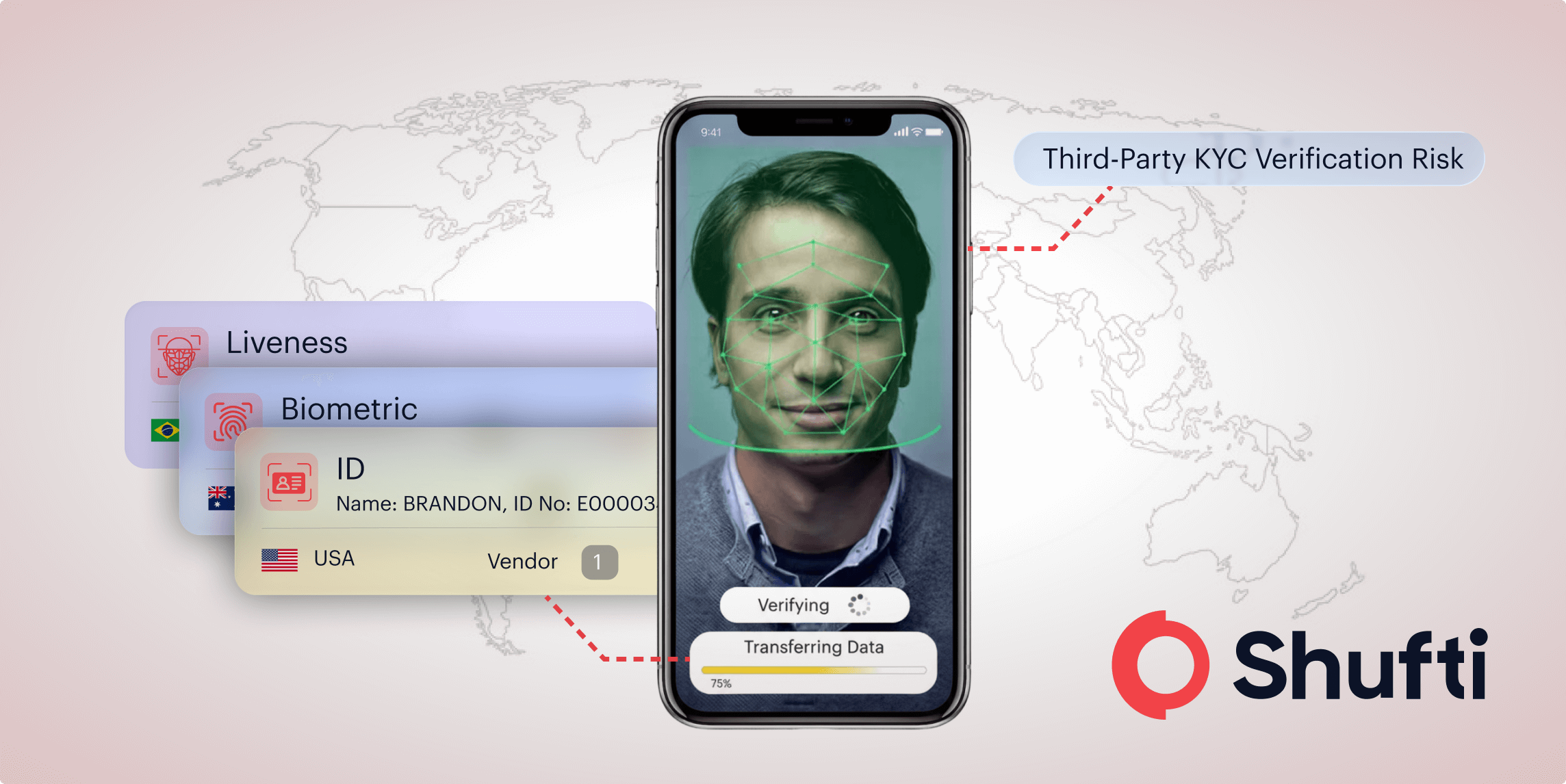
The Hidden Security Risk of Using a Third-Party KYC Verification Provider
- 01 Why KYC Data Breaches Keep Happening?
- 02 Third-Party KYC Verification Risks Nobody Discusses
- 03 How Proprietary KYC Verification Technology Changes the Equation?
- 04 Identity Verification Breach Prevention Through Architecture
- 05 Security Requirements for a Third-Party KYC Verification Provider
- 06 PII Verification Data Protection Through Ownership
- 07 What to Ask Your Identity Verification Provider?
- 08 The KYC Infrastructure Question That Actually Matters
If you’ve been following the news cycle for the past few years, you’ve likely noticed a consistent pattern. PII (Personally Identifiable Information) records exposed, systems compromised, and personal data floating around where it shouldn’t be are all too common.
What most coverage misses is the architecture underneath. The real vulnerability isn’t some sophisticated hacking operation. It’s how identity verification data moves through systems in the first place, and that’s a conversation most vendors would rather avoid.
Why KYC Data Breaches Keep Happening?
Most identity verification doesn’t actually happen inside the platform you’re interacting with. It happens somewhere else entirely, passed along through a chain of systems most people never think about.
What nobody tells you is that the company you’re dealing with probably isn’t the one actually verifying you. They take your documents and pass them to a verification vendor. That vendor might send your biometric data somewhere else; liveness detection gets handled by yet another party, and by the time your identity is confirmed, your data has touched three, four, maybe five different systems that you never agreed to share with directly.
Every one of those handoffs carries real risk. Your data is sitting somewhere, copied, stored, and potentially exposed at every stop along the way, and the frustrating part is that the company you originally trusted doesn’t fully control any of it. They’re essentially middlemen who passed your information down a chain and hoped everyone else was doing their job properly. Better encryption doesn’t fix that, and neither does a stronger firewall.
Third-Party KYC Verification Risks Nobody Discusses
Supply chain breaches roughly doubled between 2021 and 2025, and it had nothing to do with hackers suddenly getting smarter. The real reason is that verification infrastructure became more tangled over time, with more vendors, more dependencies, more places for something to quietly go wrong without anyone noticing.
Think about what happens when your data has to leave one system to reach a validation service somewhere else. You’re not just trusting the company you signed up with anymore; you’re trusting every single vendor in that chain, and all it takes is one misconfigured database or one vendor who treats security as an afterthought to put everything at risk.
The thing is, most providers won’t bring this up because their entire business is built around aggregation. They don’t actually own the verification technology, and what they do is stitch together third-party tools, routing your data between a handful of specialized vendors who each handle one small piece of the process. It moves fast, it scales well, and it works right up until it doesn’t.
What it also does is create a layer of exposure that sits outside their control, and no compliance framework currently on the market fully accounts for that kind of exposure.
How Proprietary KYC Verification Technology Changes the Equation?
There’s another way to build verification systems. Instead of routing data out to third parties, you keep everything internal and own the stack end-to-end.
Document analysis happens in-house using models your team developed. Biometric matching runs on your own infrastructure with algorithms you actually understand and can adjust. Fraud detection is trained on your own data rather than whatever a vendor decides to feed into a shared model. Nothing leaves your environment for verification work, which means you are not crossing your fingers and hoping the next vendor in the chain has their security in order.
This is not about being overly cautious or difficult to work with. It’s about controlling variables to actually guarantee security instead of hoping everyone else in your supply chain is doing their job correctly. When you own the full pipeline, you know exactly where data lives and who has access.
The operational benefits follow naturally from that. Verification is faster because nothing is waiting for an external API response. Accuracy improves because you are tuning your own models against the specific document types and fraud patterns you actually encounter. And compliance becomes considerably more straightforward because your data never crosses a boundary you can’t audit.
If you want to understand what true ownership of identity infrastructure looks like in practice, watch the breakdown here:
Here’s the full walkthrough: Stop the World Tour of PII Data
Identity Verification Breach Prevention Through Architecture
Most companies approach security backwards. They lock down their perimeter, implement access controls and encryption, get through their audits, and then assume their vendors are doing the same on their end. It feels like a strategy, but it is really just optimism with a compliance certificate attached to it.
Real prevention starts much earlier, at the architectural level, before a single line of code is written. The questions that actually matter are whether you own your verification technology or rent it from aggregators, whether your customer data stays within your infrastructure or travels to third-party systems, and whether you trace the full journey of a document through your pipeline.
If the answer is not immediately clear to you, you’re probably exposed.
The companies that consistently stay out of breach headlines did not get there by having better incident response plans. They built systems from the ground up where customer data simply never had to leave their controlled environment in the first place.
Security Requirements for a Third-Party KYC Verification Provider
Here’s what we built at Shufti. Full-stack proprietary verification where every component, from document capture to final decision, runs inside our infrastructure.
No third-party handoffs for verification work. No external APIs for biometric matching. No vendor dependencies for fraud detection, since we trained our own models on patterns we’ve observed.
The data enters our system, gets analyzed by our models, generates a decision, and stays contained throughout. Nothing depends on vendors who might have different security standards.
This means sub-second verification times because we’re not waiting on external services. It means accuracy tuned to specific document types and fraud patterns. It means on-premise deployment for organizations that can’t send identity data to the cloud.
Building this way required significantly more investment than licensing third-party tools, but when you look at where breaches actually originate and how consistently they trace back to vendor dependencies, it is difficult to argue for any other approach.
PII Verification Data Protection Through Ownership
Compliance doesn’t equal security. You can be fully compliant with GDPR, SOC 2, and ISO 27001 while still getting compromised if your architecture depends on external verification providers you don’t control.
Most regulatory frameworks focus on access controls, encryption, and data retention, which cover the basics but do not go nearly far enough. They don’t penalize aggregator models or require end-to-end ownership of verification pipelines.
Companies optimize for what gets measured in compliance audits instead of what keeps data safe. They pass assessments and then route customer data to vendors operating under different standards.
That space in between is where the risk lives.
What to Ask Your Identity Verification Provider?
If you’re evaluating KYC vendors or auditing your current provider, these questions will tell you more than any compliance certificate ever will.
- Do you own your verification stack or aggregate third-party services?
- When customer documents enter your system, where do they physically go?
- How many external systems interact with the data during verification?
- If one of your vendors gets compromised, are we exposed?
- Can you deploy entirely on-premise if we require it?
If a provider struggles to answer any of these clearly, that hesitation is your answer. A vendor who cannot walk you through their own data flow almost certainly does not have full visibility into it, which means you are taking on risk that neither of you can properly see.
The KYC Infrastructure Question That Actually Matters
Security failures in identity verification aren’t random bad luck. They’re predictable outcomes of architectural choices made years ago when companies were optimizing for speed to market rather than long-term security.
When you design systems that require data to travel outside your direct control for verification to happen, you inherit every vulnerability in that supply chain. When you use aggregators instead of building proprietary technology, you’re betting that vendors three layers deep remembered to configure their databases correctly.
The companies avoiding exposure didn’t get lucky. They built systems where customer data never has to leave controlled infrastructure for verification to happen, which eliminates entire categories of risk.
This is the fundamental decision that determines whether you’re actually secure or just compliant enough to pass audits.

 Explore Now
Explore Now